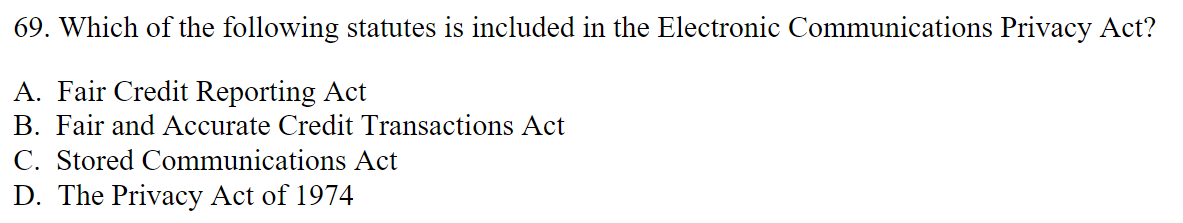
69. Which of the following statutes is included in the Electronic Communications Privacy Act? A. Fair Credit Reporting Act B. Fair and Accurate Credit Transactions Act C. Stored Communications Act D. The Privacy Act of 1974
Q: Create a logic circuit system for the following expressions. A'B'+ABC (XY)'Z X+Y+Z A'B'C AB'+CD…
A: 4. Given, The inputs of the logic circuit are A, B, and C. And the output of the logic circuit is…
Q: The issue that has to be answered is why these tendencies in cybercrime have evolved at this moment.…
A: Cybercrime refers to illegal activities committed via computers, networks, or other forms of digital…
Q: Why might reading a customer's inbox hurt an email provider?
A: Here is your solution -
Q: This is a computer science question related to cybersecurity.
A: Cybersecurity is an important field of computer science concerned with protecting computer systems,…
Q: 73. Which of the following describes the greatest challenge in regulating data security…
A: Data security is the process of preventing unauthorised access, theft, alteration, and destruction…
Q: 67. Which of the following constitutional protections is frequently a hurdle in passing laws and…
A: We have laws for the protection of regulations designed to restrict information shared or posted…
Q: Denial of service attacks may harm traditional email. Will you use this information to defend…
A: Denial of Service (DoS) attacks includes an attacker flooding a targeted system or network with…
Q: The options for b is 108,5001,78, 99- choose one The options for a is 99,78,120, none-choose one…
A: The definition of error correction codes communication protocols are designed error detection and…
Q: -lated to consumer privacy? . Federal Communication Commission ("FCC"). . Federal Trade Commission…
A: Answer is explained below in detail
Q: A- Describe the three steps in ElGamal cryptosystems. Encrypt the message m=5 for p=17 and a=6.
A: The ElGamal cryptosystem is a public-key cryptosystem that relies on the intractability of the…
Q: Q1-Vigenere cipher is a method of encrypting alphabetic text using a simple form of polyalphabetic…
A: The Vigenère cipher is a type of polyalphabetic substitution cipher that uses a keyword to encrypt…
Q: 40. The act of auditing your data to determine the level of financial and reputational and legal…
A: Dear student, I will provide you most correct answer with detailed explanation and I will also…
Q: What kinds of assumptions about the person who performed an illegal act on the internet are often…
A: Introduction : When unlawful conduct is committed on the internet, assumptions about the culprit are…
Q: a) Our task is to find the approximate frame error rate (FER) for FEC in percentage Answer: b)…
A: The error handling overhead in communication links can include: Error correction codes:…
Q: 13. Under the Electronic Communications Privacy Act ("ECPA"), when may a person lawfully monitor…
A: Under the Electronic Communications Privacy Act ECPA, a person may lawfully monitor another's…
Q: a) Our task is to find the bandwidth of each subcarrier. Answer b) Calc Answer 234 290 30 None Khz…
A: The definition of Orthogonal frequency division multiplexing is a digital modulation technique for…
Q: There are a few ways in which conventional email might be compromised by a denial of service attack.…
A: Denial of Service attack on email is a malicious attack that used to disrupt the normal functioning…
Q: A denial of service attack might harm conventional email in a number of different ways. Build a plan…
A: In order to answer this issue, we must comprehend and explore many ways in which a Denial of service…
Q: 39. Which of the following can be considered "personal data" as defined under GDPR? A. Avatar B.…
A: Correct answer is given below. Please note appropriate explanation for incorrect answers is given as…
Q: 65. Which of the following is least likely to be considered a covered entity under the Health…
A: Correct and incorrect options are explained below
Q: 1.What is the primary purpose of an audit trail? To provide evidence for legal or regulatory…
A: “Since you have posted multiple questions, we will provide the solution only to the first question…
Q: 8. What is the main purpose of the Fair Credit Reporting Act ("FCRA")? A. Increase the accuracy and…
A: The Fair Credit Reporting Act FCRA will govern access to consumer credit report records and promotes…
Q: 16. The Health Insurance Portability and Accountability Act ("HIPAA") can apply to whom? A.…
A: The question asks about the scope of the Health Insurance Portability and Accountability Act…
Q: Can you please help me find an applicable law/s for these three commandments, the specific violation…
A: As technology continues to advance and become an integral part of our daily lives, the need to…
Q: On this link: https://nca.gov.sa/legislation?item=182&slug=guidelines-list you can find different…
A: According to the information given:- We have to define Cloud Cybersecurity Controls Policy. Based…
Q: What fundamental beliefs and practices today underpin the vast majority of cybercrime? Include…
A: Cybercrime is the growing threat in this age of the digital technologies , there are various reasons…
Q: Cybercrime and society 2) Determine the best Internet-crime prevention methods.
A: Internet crime, otherwise called cybercrime, has turned into a huge danger to people, organizations,…
Q: USE MY SQL List all the data in your table movie_prod, sorted by the id of the movie (smallest…
A: MySQL is based on the SQL programming language and allows developers to store, organize, and…
Q: How does a data breach effect cloud security? What are some possible countermeasures?
A: According to the information given:- We have to define data breach effect cloud security? What are…
Q: Better and cheaper technology will allow it to be distributed across the global, this is known as…
A: The global technology revolution is defined as the revolution of materials, devices, and…
Q: For an Orthogonal frequency-division multiplexing data transmission with a cyclic prefix of 20 and…
A: Orthogonal Frequency Division Multiplexing (OFDM) is a digital modulation technique used in modern…
Q: Differentiate digital piracy from intellectual property infringement using examples.
A: In this question we need to explain the differences between intellectual property infringement and…
Q: 1. The Children's Online Privacy Protection Act ("COPPA") was enacted to primarily prevent which of…
A: In this question we need to choose the main purpose of Children's Online Privacy Protection Act…
Q: 78. Under the Fair Credit Reporting Act, Consumer Reporting Agencies must follow reasonable…
A: Consumer reporting agencies (CRAs) are required to adhere to reasonable processes under the Fair…
Q: Below is the Frequency hopping spread spectrum system (FHSS) for one Pseudo random noise period. Our…
A: To determine the resulting output frequency in order, using the information about the input data,…
Q: 3) Given that main memory is composed of only three page frames for public use and that a seven-page…
A: FIFO is a simple and easy-to-implement algorithm, but it may not always result in optimal…
Q: Carry out a quick risk management analysis on your laptop. Determine what you have, what you need to…
A: In the age of the digital era, most of our daily activities are done through computers and laptops.…
Q: 10. Which of the following strategies is a company's best bet to avoid having to notify residents of…
A: One of the best ways to safeguard personal data from unauthorised access in the event of a data…
Q: 75. Which of the following is not a term used to describe a method of acquiring personal identifying…
A: Cybercriminals utilise human engineering, often referred to as social engineering, as a strategy to…
Q: What actions would you take if a pathogen compromised your mobile device? Determine the type of…
A: Here is your solution -
Q: 72. Federal wiretap laws primarily protect what type of information? A. The identity of the sender…
A: The primary focus of federal wiretap laws is to protect the content of communications, which…
Q: Can you please help me find an applicable law/s for these three commandments, the specific violation…
A: As technology continues to advance and become an integral part of our daily lives, the need to…
Q: 2. If an information technology auditor working on behalf of a hospital with a valid business…
A: The hospital and auditor are required to comply with the Health Insurance Portability and…
Q: A Cyber Treaty can be paralleled to which treaties defined before it? Group of answer choices…
A: The world has become increasingly interconnected with the rapid development of technology,…
Q: 46. Which of the following is not a privacy/security law? A. TCPA B. HIPPA C. GLBA D. FCRA
A: The Telephone Consumer Protection Act (TCPA), which limits telemarketing calls and unsolicited…
Q: Could you perhaps elaborate on what you mean by the phrase "cybercrime"? Give an explanation of each…
A: What is cybercrime ? The cybercrime is about the criminal activities which are carries out online by…
Q: How different are network apps from other kinds of apps in terms of their layout?
A: A network application is defined as the application which is running on one host providing…
Q: Which widely held assumptions and behaviors characterize the bulk of today's cybercrime? If you want…
A: The bulk of today's cybercrime is characterized by a few widely held assumptions and behaviors,…
Q: 79. In some revenge porn cases, victims have been able to successfully recover damages from…
A: Copyright infringement occurs when someone uses someone else's copyrighted work without permission.…
Q: 41. The Computer Fraud and Abuse Act contains a potentially problematic definition of "protected…
A: A federal legislation known as the Computer Fraud and Abuse Act (CFAA) makes a number of…
please choose the most correct anwser.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps
