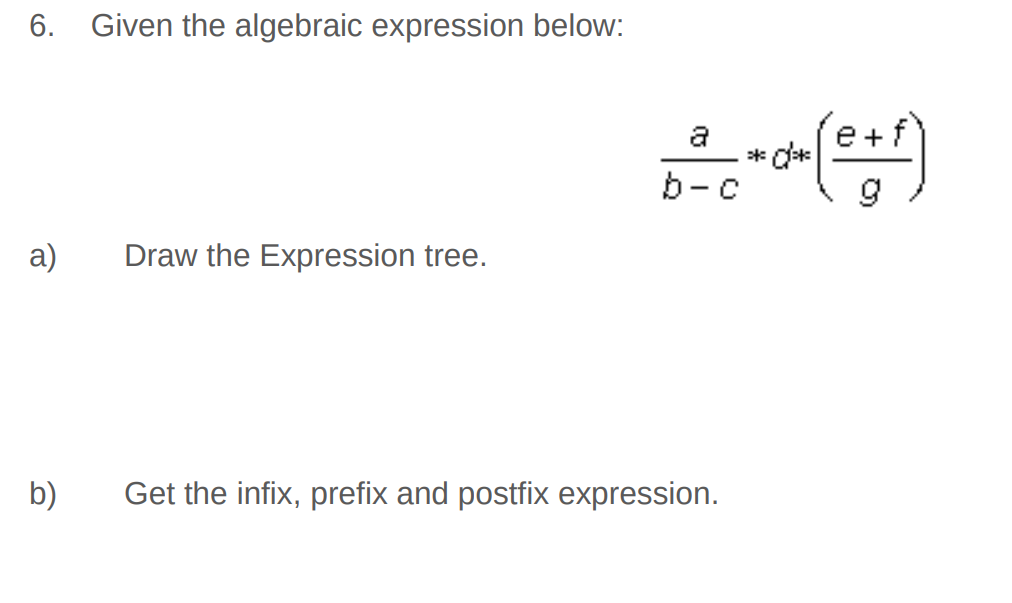
6. Given the algebraic expression below: a) b) Draw the Expression tree. a b-c Get the infix, prefix and postfix expression. (e+f) *d*
Q: Describe what is meant by a local variable's lifespan.
A: Introduction: When a variable has a flexible lifespan, it is still available while the system is…
Q: Problem Statement An intelligence agency has received reports about some threats. The reports…
A: Given question is asking for a program in c++ language for finding the possible ways to fill the…
Q: esis, evolution, and ongoing evolution?
A: SUMMARY: THE ORIGINS OF THE INTERNETThe origins of the internet are based on the USA of the 1950s.…
Q: Investigate the connections between utility computing, grid computing, and cloud computing.
A: Grid Computing, is a type of computing that combine resources from various administrative domains to…
Q: can you slove more 3 queries
A: As per guidelines I can answer only one. Thank You.
Q: Choose an information system for yourself and discuss the distinction between requirements that are…
A: Functional and Non-Functional: Both functional and non-functional requirements must be addressed.…
Q: Computerized information systems. On a typical client project, staff from Jobel Consultancy Company…
A: Management Information systems is referred as the informations systems that are used in the decision…
Q: Create a function check(s) that determines if its argument is a string in the format [i], where i is…
A: The Answer is
Q: Compare TDM, WDM, AND FDM
A: What is multiplexing? It is a technique which combines multiple signals into one signal. This makes…
Q: Given list: {28 30 53 58 73 74 92 94} Which list elements will be checked to find the value: 73…
A: Given We know about the binary search and linear search in cpp.
Q: SIX countermeasures employed by security managers to prevent the collection of data about your…
A: Start: Write down any SIX countermeasures security administrators have employed to prevent hackers…
Q: nsisting of 2100 livery across two an carry a maxim rame and the se um payload of 40 etwork…
A:
Q: An international round table conference will be held in india. Presidents from all over the world…
A: Since the programming language is not mentioned, I have done the code using Python 3. President and…
Q: Airport security officials have confiscated several item of the passengers at the security check…
A: Coded using C++.
Q: What are some of the advantages and disadvantages of using an operating system like Unix?
A: History of UNIX operating system The Multics operating system was created in the 1960s by the…
Q: The rise of Machine Learning has made Data Structures and Algorithms less relevant.
A: Introduction: Yes, algorithms, complexity, and data structures are still relevant in the age of…
Q: improvements of the given algorthims.
A: Operations can be executed on Leftist Heaps: 1. MakeHeap(Element e) 2. FindMin(Heap h) 3.…
Q: = Synaptic weights are w, 1.2, w -0.4, w, 0.7. Find the given input above (or) below the line?
A: The answer is
Q: What issues with your company's information system should you be aware of, and what steps should you…
A: What issues with your company's information system should you be aware of, and what steps should you…
Q: Hi really need help with this assignment Oracle 12c: SQL Chapter 8 Question 3 and 5. 3. List the…
A: The queries for the given questions are as follows.
Q: When designing a software system, list and explain all of the tasks that must be completed.
A: The question is "when designing a software system, list and explain all of the tasks that must be…
Q: What are the diffrent CMKs in AWS?
A: CMKs can be divided into two main types: AWS-managed and customer-managed. CMK managed by AWS was…
Q: Consider an IP packet with a data length of 4400 bytes. TCP header is of 40 bytes while that of IPv4…
A: Consider an IP packet with data of 4400 bytes. TCP header is 40 bytes while that of IPv4 reader is…
Q: Add 50 (18) (13) Part a: Draw AVL trees after applying the following operations: Remove 13 (18) (13)…
A: Below is the answer to above question . I hope this will be helpful for you...
Q: Consider the following instance of the Hamiltonian Cycle Decision Problem: b Generate the…
A: According to the information given:- we have to follow the instruction in order to generate the…
Q: An international round table conference will be held in india. Presidents from all over the world…
A: Since the programming language is not mentioned, I have done the code using Java.
Q: What type of DHCp packet does a device send once it has been offered an IP address by the DHCP…
A: Dynamic Host Configuration Protocol (DHCP): DHCP exchange involve four types of packets: Discover:…
Q: Which statement about this error handling function is correct? function handleErrors(message,…
A: Error Handling alludes to how Express gets and processes blunders that happen both simultaneously…
Q: Although Litecoin, Ether, and other cryptocurrencies are also used with blockchain, the great…
A: Introduction: Cryptocurrency The term "cryptocurrency" refers to an unofficial form of government…
Q: When designing a software system, list and explain all of the tasks that must be completed.
A: Different software development models are used in the software development service based on the…
Q: Defining a system model is a complex task. What are the most important considerations while…
A: The term 'system model' is used in a range of domains, application disciplines, and contexts with a…
Q: Code in python, take any 3D equation and solve it by gaussian elimination (you can’t use numpy…
A: Code is given below. ... Gaussian elimination is an algorithm that aims to find values for x₁,…
Q: Grid computing and cloud computing are different in how they are put together. I'm trying to figure…
A: The Answer start from step-2.
Q: Find the logic functions of A and D for the circuits shown in figure Q2 and prove it is working as…
A: Problem: Solution: 4X1 MUX output will be given by: And 2X1 MUX will be given by: These two…
Q: What type of storage is AWS S3 and also tell the maximum size of individual file for uploading?
A: Question is asking for the storage type and maximum size of file in AWS S3.
Q: Give three examples of instructional robots in action. For each case, describe what the robot is…
A: Due to this: Three examples of robots employed in teaching are the subject of the discussion.
Q: A software system may be needed to meet many sorts of Requirements.
A: Any software project must have a thorough list of criteria. High level business demands and purposes…
Q: You are working for a company that will be using the 192.168.1.0/24 private IP address space for IP…
A: Given IP address is, 192.168.1.0/24 Number of network bits=24 Number of host bits=8 Number of hosts…
Q: Report all books published after Jan. 1st, 2015, as well as all books published in 2014 that have…
A: SQL query will be: SELECT TITLE, PubID, RETAIL, PubDate FROM BOOKS WHERE (RETAIL<= 50 AND YEAR…
Q: Discuss the following four components of continuous event simulation in terms of their importance to…
A: CONTINUOUS EVENTS SIMULATION A continuous event simulation is one in which the variables change…
Q: An explanation of heuristic search: Compared to other search algorithms, what are the benefits and…
A: Heuristic search: In order to find the best solution to a problem, a class of methods known as…
Q: What is the difference between OCR and OMR (Optical mark recognition)?
A: The solution to the given question is: Basis for comparison OMR OCR Stands for Optical Mark…
Q: Within the limits of a wireless local area network, what kinds of communications are carried out?
A: Introduction: The introduction of several network types: A computer network is formed when two or…
Q: java Create a static method that: is called repeatAll returns ArrayList of Booleans takes in a…
A: I have provided JAVA CODE along with CODE SCREENSHOT and 2 OUTPUT…
Q: Admission to college is just beginning and Chef has also just finished his high school. There are N…
A: Input-Output Details: First line will contain TT, number of testcases. Then the testcases follow.…
Q: How were metrics of usability and user experience used and distributed throughout the evaluation
A: Introduction:…
Q: What does the networking term Ethernet mean?
A: Introduction: ETHERNET: Ethernet is essentially a method of linking numerous computer systems in any…
Q: 30. We have four sources, each creating 250 characters per second. If the i erleaved unit is a…
A: Given data, We have the four sources, each one creating the 250 characters per second, the…
Q: photo?
A:
Q: How do cloud computing advantages stack up against the competition? Users of the cloud should be…
A: Start: Organizations may assess the services provided by cloud technology in a number of ways, and…
Step by step
Solved in 3 steps with 2 images

- Draw an expression tree for the following, infix expression and find the prefix and postfix expression. (C+D+A*B)*(E+F)IMP:- Give correct And Detailed Answer if you know 100% sure thn Answer if get wrong we will downvotes Construct the syntax tree and draw the DAG for the expression, (a*b) + (c-d) * (a*b) + b.Draw diagrams of the expression trees for the following expressions:(a) 3 * 5 + 6(b) 3 + 5 * 6 (c )3 * 5 ** 6
- (End of Chapter 4, Exercise 18, page 140) Convert the following grammar into Chomsky Normal FormExercise Expression Tree Question 1 A) Build an expression tree for the following expressions: a*b + (c+d) Explore the expression tree using: i. Prefix - ii. Infix - iii. Postfix – B) Build an expression tree for the following expressions: (A-B+C)*D Explore the expression tree using: i. Prefix - ii. Infix - iii. Postfix –Draw a parse tree and show: phrases, simple phrases and handle for the following:S -> aAb | bBA A -> ab | aAB B -> aB | b (a) aaAbb(b) bBab(c) aaAbBb
- Draw parse tree structure for the following sentences : a) Cute girl eats an icecream with spoon. b) Sushil went to the doctor for treatment in the hospital.Draw the expression trees that represent the following expressionsR -> AaB | bAb | AaA | BaB A -> aA | bB | a B-> bB| aA| b draw a parse tree for the right sentential form abaaabb

