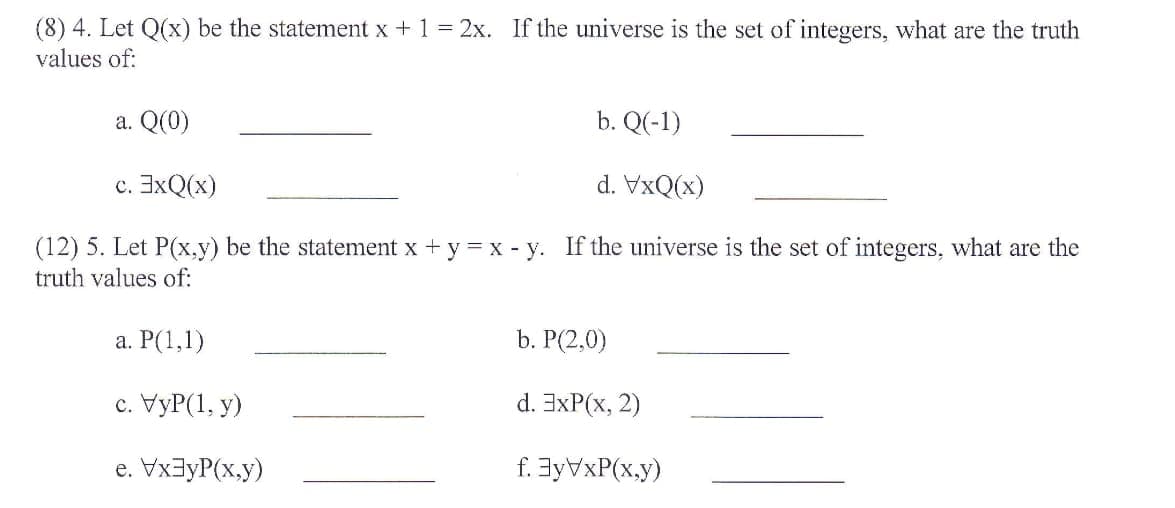
(8) 4. Let Q(x) be the statement x + 1 = 2x. If the universe is the set of integers, what are the truth values of: a. Q(0) b. Q(-1) c. 3xQ(x) d. VxQ(x)
Q: In CS240, you built a family map server. For your client, you used a HttpServer object with handlers...
A: Introduction: Cloud computing platform Amazon Web Services (AWS) combines IaaS, Paas, and SaaS compo...
Q: Exercise 2: Determine the roots of a quadratic equation, if a is not equal to zero and determinant i...
A: The answer is given below:-
Q: In the file example.html in the top left hand pane, you are asked to add two lines of code that will...
A: the answer is given below:-
Q: Build a calculator in Assembly language emu8086 with a graphical interface. The function of calcul...
A: Answer: Our instruction is answer the first three part from the first part and I have attached code ...
Q: Why do we need cache memory, which is also transistor-based, if RAM (Random Access Memory) is a vola...
A: Store memory and RAM both depend on semiconductor based why reserve memory is required:
Q: 3. Salts are typically stored in plaintext with the user's username and password hash (e.g., the Lin...
A: Your question is about how is salt hashing is secure. I have explained that below:
Q: Consider the following algorithm: Input: Array A and B both with n integers. Output: Array C with n ...
A: According to the algorithm mention we have to find out the tight upper bound on the running time of...
Q: Q1.What is the smallest 32-bit floating point number f such that 128 + f > 128 ? What is the smalle...
A: The answer is given below:-
Q: Examine different methods for gathering evidence from social media networks."
A: The solution to the given problem is below.
Q: Without using any loop In PHP programming languague The value of the input variable is 9.3,5 5,7,0 H...
A: 1) In PHP we have a function array_sum() which returns the sum of the values in an array. 2) It's sy...
Q: Develop a hypothetical architecture with illustrative instruction and data formats, instruction sets...
A: ANSWER:-
Q: What role does cryptology play in information security? What would be the implications if cryptograp...
A: Is cryptography necessary for data security? Cryptography is ubiquitous in our daily lives, and its ...
Q: If you're conducting user research, why not separate the overall design into multiple user viewpoint...
A: Introduction: If you're conducting user research, why not separate the overall design into multiple ...
Q: Why not divide the overall design into multiple viewpoints when conducting user user research?
A: - We need to know why we dont divide the overall design into multiple user viewpoints when we conduc...
Q: 3) C++ coding Practice: You are required to create an ordered linked list, OrderedlinkedList class u...
A: In questions with many sub parts, we must only do the first 3. We have solved quite a few parts her...
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: Biometrics validation gadgets depend on actual qualities like a unique mark, facial examples, or iri...
Q: Label the Recursion Requirements. int fact (int n) 1fin--1)
A: Given :- label the recursion requirements
Q: aaaaa525252 to the console. You must not add or delete any other operators and/or
A: The answer is
Q: -) How can i check the type of signature of a method. (Assume that signature may be from the array o...
A: Method signature is the thing that helps in identifying a method from multiple methods.
Q: Write a C# program to find the area of a triangle. The user must capture the inputs. Use the correct...
A: The area of triangle=(base*height)/2 Algorithm: Start Read base b and height h Calculate area=(b*h)...
Q: 14. Convert the following decimal number to negative binary number, using 2's complement in 8 bits a...
A: a) Given number is in decimal form that is: 87 Binary form of 87 is: Division Quotient Remainde...
Q: Someone should double-check the APA citations and referene provide a PowerPoint.
A: given - Someone should double-check the APA citations and references, thus I'd want to provide a Pow...
Q: Discuss possible countermeasures against Man-in-the-Middle (MITM) attacks that intercept wireless cr...
A: Man -in -the- middle :- As its name suggests man in the middle is an attack by unauthorized person a...
Q: As CISO, you are in charge of developing an information security programme that is backed by a frame...
A: Information security program consists of 3 principles:confidentialityintegrityavailability:We will h...
Q: In the C programming language, write a program to input the radius of a sphere and display the diffe...
A: C program: #include <stdio.h>#define PI 3.14 int main(){ float radius, SurfaceArea, Area; /...
Q: In GSM, a "TDMA frame" is composed of eight distinct time slots. Each
A: The answer is
Q: s.data.frame(cars2) elect(cars3, hp, mpg ample_n(cars4, 32)
A: One could adopt a hierarchical philosophical strategy. This is mentally fulfilling however innovatio...
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: Introduction: Biometrics Technology combines the words bio and metrics, which means to compute or me...
Q: As a property developer in California, you want to determine the most profitable area for a new deve...
A:   Mar 11, 2019 Read time: 6 mins Share Property Development: The Process to Follow for Success Wh...
Q: What is a distributed denial of service attack, and how can it be carried out by a single individual...
A: DDoS (distributed denial of service) attack: Following the discovery of the limits of single-system ...
Q: Based on Don Norman's concept of user difficulties, discuss how formative assessment can be used to ...
A: “Usability” refers to the ease of accessing and using a product or website. It’s a sub-discipline of...
Q: Have you used top-down design principles before? If so, please explain why. Write about at least one...
A: Let us look at the solution. True, we used a top-down approach. Top-down design is the process of br...
Q: Will the given 8086 instruction execute? MOV A, #465H
A: Given an 8086 instruction MOV A, #465H and we have to whether the given instruction will execute or ...
Q: O How can i check the type of signature of a method. (Assume that signature may be from the array or...
A: The method signature consists of the method name , parameters like type , number and position . Usua...
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a messag...
A: - First we have total N layers. - Second, The message generated at the top layer is M bytes as menti...
Q: What are routing metrics, and how can you utilise them to your advantage?
A: Answer: Only one sort of measure is used by routers to determine the best route.Router performance m...
Q: Case Study 2: Role and Types of Information Systems emoini Ahmed has recently joined as CEO at Musca...
A: Given The answer is given below. Step1: Ahmed has recently joined as CEO at Muscat Oils LLC, a large...
Q: 1. Write Lex Program check whether a given input is a word or not? 2- Write Lex Program to count the...
A: 1. code : Output :: Editable code : %{#include<stdio.h>#include<stdlib.h>%}%option...
Q: A machine cycle is a four-part closed-loop process. Explain why the machine cycle is so important. I...
A: Introduction: A machine cycle is a four-part closed-loop process. Explain why the machine cycle is ...
Q: What is the smallest 32-bit floating point number f such that 128 + f > 128 ? What is the smallest ...
A: Given that: What is the smallest 32-bit floating point number f such that 128 + f > 128 ? Flo...
Q: People who work with computers and humans use a lot of different ways to measure how well they work ...
A: Introduction: He addresses a vision articulated in his latest book Superminds a framework for reachi...
Q: What effect does hierarchy have on the growth of an organisation and administrative autonomy, and ho...
A: Introduction: In the preceding section, we defined "the network" as a collection of linked routers. ...
Q: Network Address: 192.70.10.0 Number of needed hosts: 8 Default subnet mask: New subnet mask: Number ...
A: Answer : Given data : Network address : 192.70.10.0 Number of needed hosts : 8 Note : The la...
Q: : Draw the Gantt chart for the following software development processes: Problem/ Business analysis...
A: The answer is given below:-
Q: Give me an example of f formatted string in python. Take all the data from the user.
A: Required:- Give me an example of f formatted string in python. Take all the data from the user. Appr...
Q: When the shell creates a new process to perform a command, how does it determine whether a file is e...
A: There are two type of shell:- BASH:- This shell is default shell for Unix version. C Shell:- This i...
Q: As CISO, you are in charge of developing an information security programme that is backed by a frame...
A: Answer Information security program is based on following 3 principles: confidentiality availability...
Q: What is the purpose of system engineering? How to achieve performance improvement by using system en...
A: Systems engineering is an interdisciplinary field of engineering and engineering management that dea...
Q: Discuss possible countermeasures against Man-in-the-Middle (MITM) attacks that intercept wireless cr...
A: Answer By encrypting the traffic between the network and your device using browsing encryption softw...
Q: Write a program as part of the UCAM application that will store the Fall 2021 SPL final exam scores ...
A: Actually, program is an executable software that runs on a computer.
Trending now
This is a popular solution!
Step by step
Solved in 5 steps with 5 images

- 4. Let N(x) be the statement “x has visited North Dakota,” where the domain consists of the students in your school. Express each of these quantifications in English. a) ∃x N(x) b) ∀x N(x) c) ˺∃x N(x) d) ∃x ˺N(x) e) ˺∀x N(x) f ) ∀x ˺N(x)Define the following sets: A={x, y, z, t}, B={s, t, u, v, w, x}, C={t, v, u, s}, D={s, t, u, v}Determine whether each of the statements is true, false, or meaningless. State your answer clearly.(You do not have to justify your answers, but they have to be correct.) (a){s, t}⊂D (b)A⊆B (c)A∈C (d)|C|=|B|5 A. Let * be a new logical connective such that p * q does not hold if and only if p and q are either both false or both true. (i) Write down the truth table for p * q (ii) Write down the truth table for (p * p) * (q * q). (iii) Does the table in (b) coincide with a table in *Truth table available on the given image* (By "Coincide" we mean that the respective columns of T and F values are the same) B. Construct a formula in CNF based on each of the following truth tables: *Truth table available on the given image* C. Compute CNF (NNF ( IMPL_FREE ¬(p → ( ¬ (q ∧ ( ¬p → q))))))
- Let l be a line in the x-yplane. If l is a vertical line, its equation is x = a for some real number a. Suppose l is not a vertical line and its slope is m. Then the equation of l is y = mx + b, where b is the y-intercept. If l passes through the point (x₀, y₀), the equation of l can be written as y - y₀ = m(x - x₀). If (x₁, y₁) and (x₂, y₂) are two points in the x-y plane and x₁ ≠ x₂, the slope of line passing through these points is m = (y₂ - y₁)/(x₂ - x₁). Instructions Write a program that prompts the user for two points in the x-y plane. Input should be entered in the following order: Input x₁ Input y₁ Input x₂Part I. Let p, q, and r be the following simple statements: p: Sydney is the capital of Australia. q: Thirteen is a prime number. r: The Trinity University of Asia is in Quezon City. Express each of the following propositions as an English sentence and determine its truth value. Part II. Use the truth table to determine whether the following pairs of statement are logically equivalent or not . 1. ~(p↑q)and~p↑-q 2. p↓(q↑r)and(p↑q)↓(p↑r)5. Suppose X and Y are both TRUE, A and B are both FALSE, P and Q are unknown, which of the following can have the identifiable truth value? a. (P ∨ X) → B s. ( X ∧ Y) → P d. (P→X) ∧ Q f. (A ∨ P) ⇔ X
- Ex: Let A1 ={x, y}, A2 ={1, 2}, and A3 ={a, b}, Find A1 × A2, (A1 × A2) × A3, A1 × A2 × A3.Propositions and quantifiers Let x, y ∈ {2, 3, 4}. For the following propositions provide aproof or counterexample to the statements below:•P0(x, y): x < y•P1(x, y): both x and y are even•P2(x, y): x ×y > 7•P3(x, y): x is even and x + y is a multiple of x.•P4(x, y): x ̸= y (a) for all propositions P in P0, . . . , P4,[∃x ∀y P ] →[∀y ∃x P ] (b) for all propositions P in P0, . . . , P4,[∀x ∃y P ] →[∃y ∀x P ]f : {1, 2, 3} ® {a, b, c, d} f(1) = c f(2) = b f(3) = a g : {a, b, c, d} ® {x, y, z} g(a) = y g(b) = x g(c) = x g(d) = z Find the composition gof
- 2) (L2) Prove using laws of logic that the conditional proposition (p ∧ q) → r is equivalent to (p ∧ ¬ r) →¬ q. 3) (L3) Show that the converse of a conditional proposition p: q → r is equivalent to the inverse of proposition p using a truth table. 4.1) (L4) Show whether ((p ∧ (p→q)) ↔ ¬p) is a tautology or not. Use a truth table and be specific about which row(s)/column(s) of the truth table justify your answer. 4.2) (L4) Give truth values for the propositional variables that cause the two expressions to have different truth values. For example, given p ∨ q and p ⊕ q, the correct answer would be p = q = T, because when p and q are both true, p ∨ q is true but p ⊕ q is false. Note that there may be more than one correct answer. r ∧ (p ∨ q) (r ∧ p) ∨ qI. Let P (x) be the statement “2x = x2 .” If the domain consists of the integers, what are the truth values? a) P(0) b) P(1) c) P(2) d) P(−1) e) ∃x P(x) f ) ∀x P(x) 2. Let Q(x) be the statement “x > x - 1.” If the domain consists of all integers, what are the truth values? a) Q(10) b) Q(−2) c) Q(999) d) ∃x Q(x) e) ∀x Q(x) f) ∃x ˺Q(x) g) ∀x ˺Q(x)If the first number in a sequence is a positive integer, x Let ao= x, an is defined as follows if an is even, then an+1 = an/2 if an is odd, then an+1 =3 *an+ 1 Then there exists an integer k, such that ak =1 For example, if: 75, then k = 14 and the numbers in the sequence are: 75, 226, 113, 340, 170, 85, 256, 128, 64, 32, 16, 8, 4, 2, 1. The largest number in the sequence is 340 and it is a position 4 in the sequence (assuming 75 is at position 1) Design and implement a complete C++ program that will • read a series of integers (greater than 0) from a file and for each integer display (to the screen) − the integer − the number of steps it takes to reach 1 − the largest value in the sequence and its position

