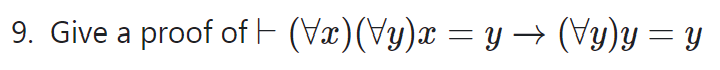
Give a proof of
Q: What is needed to build a database in the physical world? Make a list of some of the most popular…
A: A database is a software that manages data in organized manner. A database is used when huge volume…
Q: tween nodes in an eight-node network is presented in the from-to distance table below. What is the…
A: Here, from the question In the given problem, the graph contains 8 nodes from 1 to 8 in it.. The…
Q: Describe the role that LSI chips typically play in a contemporary personal computer.
A: Personal Computer: A personal computer (PC) is a multifunctional a microcomputer that is…
Q: A user is executing a tracert to a remote device. At what point would a router, whi is in the path…
A: TTL is basically the Time to live. Time-to-live (TTL) is a specific amount of the duration of time…
Q: te this form please. Random
A: I have written the HTML Code below:
Q: What are the five distinctions between CISC and RISC computers?
A: RISC and CISC: The major distinction between RISC and CISC architecture is that RISC-based computers…
Q: . For n No let w(n) denote the number of 1s in the binary representation of n. For example, w(9) =…
A:
Q: Describe the most important aspects of analog, digital, and hybrid computer architectures.
A: The correct answer for the above question is given in the below steps for your reference.
Q: Describe the meaning of the term "firewall" in terms of network security and how it is used in…
A: We need to describe the meaning of the term "firewall" and its use in network topologies and…
Q: Write a program that reads a string and checks the longest substring starting with "a" and ending…
A: We need to write a code for the given scenario. Language used is Java.
Q: Given an ordered list, what is the Big-O of finding the smallest element in the list?
A: Big O notation which refers to the one of the most efficient of the fundamental tools for computer…
Q: 2. Use a paper-and-pencil approach to compute the following division in binary. i. Dividend = 1110,…
A: Given that use a paper and pencil approach to compute the following division in binary. Dividend =…
Q: What Is A interpreter?
A: A computer programme known as an interpreter is used to execute programme instructions created in…
Q: An application includes the following functions: processing imaging orders and managing the…
A: Answer: A radiology information system (RIS) is an organized programming system for overseeing…
Q: Explain the benefits that come from using Cleanroom Software Engineering. Demonstrate the benefits…
A: Introduction: Cleanroom Software Engineering: The clean room approach was developed by Dr. Harlan…
Q: Specify the architecture of a computed unified device.
A: We need to discuss the architecture of a computed unified device.
Q: What Is A run command?
A: Simple designation of an executable for a certain Windows-based software as a run command
Q: The state of Georgia is examining population growth for all of its counties. The governor wants a…
A: Answer:- a. while population<triplePop b. years = years + 1
Q: Give examples of distance vector and link state routing.
A: Here is the information regarding link state routing protocol and vector state routing protocol:
Q: Determine a good asymptotic upper bound on the recurrence T(n) = 5T([n/4 hu the iteration mothe
A: The answer is
Q: How are data written onto a magnetic disk?
A:
Q: to describe the differences between CISC and RISC and their connections.
A: Introduction In this question, it is asked to describe the differences between CISC and RISC and…
Q: Describe the methods of user support, such as help desks and user training.
A: The following will be discussed about user support procedures like user training and help desks: The…
Q: Popular social networks like Facebook and Twitter attract a lot of people. Determine whether they…
A: Introduction: These ties, exchanges, and interactions are the building blocks of social networks. As…
Q: Which of the following registers stores the correct values after executing the instruction of MUL…
A: The above question is solved in step 2 :-
Q: cify the architecture of a computed unified dev
A: SUMMARY CUDA is the name for NVIDIA’s platform for general computing on GPUs. It includes both the…
Q: Give a single example of a sensor utilized in a mobile device.
A: Mobile phone sensors can be defined as specific technologies that are able to capture changes in the…
Q: What various kind of networks are there?
A: In the given question network is the connection of two or more computers that are linked in order to…
Q: Write Java code that uses class IntBTNode to construct the following binary tree and then print the…
A: The question is to write JAVA code for the given problem.
Q: benefits that come from using Cleanroom Software Engineering. Demonstrate the benefits of…
A: Explain the benefits that come from using Cleanroom Software Engineering. Demonstrate the benefits…
Q: Which option of rm command is used to remove a non- empty directory? A) -t B)-i C) -a D) -r
A: For removal of a directory which is not empty, we use the rm command with the -r option for…
Q: 1. Give 5 usual problems that you encounter with your internet service provider 2. Give solution…
A: The Internet Service Provider (ISP) could sometimes be the reason for the problems that are created…
Q: How is a firewall utilized in network designs?
A: A firewall is a network security device to monitor the flow of network traffic and safeguards as a…
Q: Use the bold and italic tag in one webpage and show the output?
A: I am using <b> tag for bold the text and <i> for italic text in html. Giving the code…
Q: Use the bold and underline tag in html? show the output?
A: In HTML<u> tag is used for underline the text and <b> tag is used for bold the text. I…
Q: Q5: For the Binary search tree given below. 7 15 17 In-order Travetrsal Pre-Order Traversal…
A: Given Binary Search tree:- To find In-order, pre-order and post-Order traversal for the Binary…
Q: How do the CISC instruction sets compare to the original RISC ones?
A: The question has been answered in step2
Q: Name five benefits and five drawbacks of mobile displays.
A: Introduction: There are several mobile screens available, which are distributed over a variety of…
Q: b. bits for host c. subnet mask
A: The answer is
Q: Create a pseudocode for a program that does the following: a) Prompt the user to enter the…
A: Coded using Python 3, to represent the output.
Q: restricted access protocol.
A: If a protocol is enabled for Data ONTAP, you can restrict the protocol's access to the storage…
Q: t dont answer if u r not 100% sure else very strict warning
A: Introduction :Here, We have to find the number of address lines and data lines required to…
Q: Why is an optical wand characterized as a hand-held device that reads markings or letters on paper…
A: Introduction: Optical wand: A hand-held device which reads marks or characters on paper by detecting…
Q: actly is the purpose of Artificial Intelligence (AI)? Identify its several domains and provide two…
A: Introduction: Below describe the exactly is the purpose of Artificial Intelligence (AI) and…
Q: Social networking platforms are popular (such as Facebook and Twitter). Determine why people choose…
A: Informal Social Networks - the use of specialized websites and programs to casually chat with other…
Q: Question 11. Listen ➤ What is the maximum total number of Swaps that will occur when sorting an…
A:
Q: A circuit has a pushbutton switch connected to pin PD0 and a servomotor connected to PC0 of AVR…
A: #define F_CPU 1000000UL #include<avr/io.h> #include<util/delay.h> void main() {…
Q: Company AXXAA that is selling electronics goods asks you and your team to develop two types of…
A: There are many different development techniques used to make application each technique serve its…
Q: A user is executing a tracert to a remote device. At what point would a router, which is in the path…
A: Computer networks is the set of the devices or the systems which are connected by the transmission…
Q: Consider relation R(A,B,C,D,E,F) with functional dependencies: {C,D,E)→ {B} (A,C,D] → [F] [B,E,F] →…
A: The following solution is
Step by step
Solved in 2 steps

- Prove that (p →(q →r)) → ((p →q) →(p →r)) ≡ T for all propositions p, q, r.For P= 0 and compute the value of K under the condition. if (P <= 1) K = P + 5else if (P > 1 && P <= 5) K = P + 3else if (P > 8) K= P - 1else K = PUse Direct Proof to prove this.. If x ∈ ℝ and x 2 + x + 6 < 0, then -x 2 + 2x - 9 < 0.
- Show that p ↔ q is logically equivalent to (p ∧ q) ∨ (¬p ∧¬q).Prove that it is logically equal using common equivalent proposition. 1. ¬[p v (¬p ˄ q) ≡ (¬p ˄ ¬q) 2. p → (q ˄ ¬r)Compute the gradient with respect to all parameters of f(w0 + w1a1 + w2a2) when w0 = 3, w1 = −2, a1 = 2, w2 = −1, a2 = 4, and β = 0.25 using backpropagation

