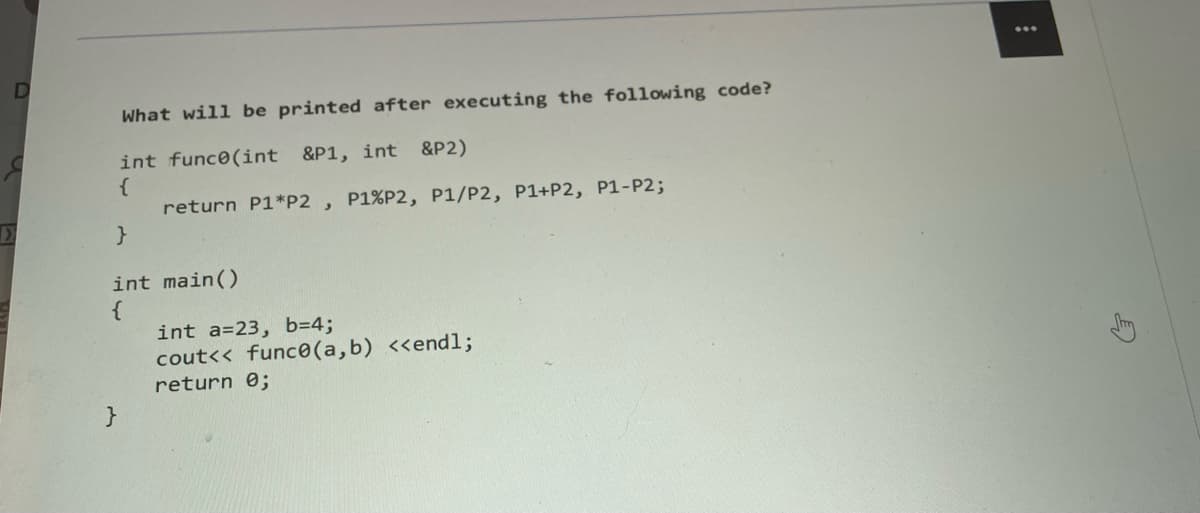
92 B 19 C 27 D E 3
Q: In terms of accuracy and training time, how do Decision Trees and Artificial Neural Networks compare…
A: Neural networks and decision trees are often contrasted: since both can model data with nonlinear…
Q: Examine a method that you would use to manufacture a high-quality computer (machine) that is both…
A: Introduction: build a high-quality computer: (machine) that provides high performance at a modest…
Q: A virus that attaches itself to an executable file on a computer What should be altered in the…
A: File infectors: The Michelangelo virus is a well-known boot sector virus that infects the system's…
Q: End-user requirements must be documented for systems analysts for many reasons.
A: Systems Analysts: Computer Systems Analysts Work Analysts draw diagrams to assist programmers and…
Q: An overview of virtualization and the many shapes it might take is provided (Language, Operating…
A: Introduction: Virtualization is a prevalent practise in the development of IT businesses. It is also…
Q: What is the difference between the OSI levels if routers occupy many layers?
A: In response to your query, The Open Systems Interconnection Model (OSI Model) is a conceptual…
Q: Write pseudocode for map and reduce function for decision tree algorithm
A: ___________ _______
Q: Does utilizing mobile devices have any drawbacks? Are the savings equal to those of systems based on…
A: Challenges to implement mobile technology: Wireless communication is feasible with the aid of a…
Q: ain the difference between he erence data is stored in mem of stack and heap memory.
A: In software engineering, primitive data types are a bunch of fundamental data types from which any…
Q: Find the smallest r such that 0,(n) > (log2 n). maxk=[ (log2 n)2]; maxr=Max[3, [(Log2 n)1]; (*maxr…
A: I have solved your question with Explanation please check next steps for solution.
Q: Comprehensively discuss the five functionalities of a computer. Takes data as input. Stores…
A: The above question is answered in step 2:-
Q: In what ways does product-service bundling benefit the end customer?
A: Bundling Benefit: Bundling reduces marketing and delivery costs by increasing efficiency. It enables…
Q: What is the name of the port in a modern PC (or server) that connects it to a LAN network? O NIC O…
A: Option: NIC DAC PCI port SATA port USB port
Q: How can intrusion detection and prevention contribute to network security and cybersecurity?
A: The Answer start from step-2.
Q: In the context of computer security, what are intrusion detection and prevention systems?
A: Intrusion Detection System: It is either a hardware device or a software program that monitors and…
Q: es to one of the Progra odule is recorded in a c and the customer (soft
A: This article is planned to act as a glossary of terms for programming advancement and handling…
Q: Why do you believe a JVM's method area is shared by all threads executing within the virtual…
A: Introduction: Class files, the machine language of the Java virtual machine, contain the byte codes…
Q: on cloud security after a data breach has taken place? Are there any other measures you think could…
A: Yes, it affects An unapproved individual gains access to classified, sensitive, or safeguarded…
Q: about assigning IP a
A: what is DHCP? It is an application layer convention in the network stack which is used by the host…
Q: define the objective of the PMT function and the arguments in support of it
A: Beginning: A monthly payment for security or loans is known as a PMT. The interest rate is…
Q: What does the RAND study say exactly? What was the holdup? RAND Report R-609 sought to answer this…
A: Introduction:
Q: Explain the distinction between integrity and authorisation restrictions.
A: Constraints on Integrity: Constraints on Authorization It is generally used to ensure data…
Q: Sample Input Ut: Depicted below are sample outputs when the program is executed (the items in bold…
A: Here, I have prepared the JAVA code and Flowchart as required, Please appreciate and Upvote. Code:…
Q: What are the main characteristics of cloud computing?
A: Introduction: Cloud computing is a concept that refers to the omnipotent and omniscient, rapid, and…
Q: ) Wireless mesh network (WMN) Metropolitan Area Network (MAN) Wi
A: define : Personal Area Network (PAN)Local Area Network (LAN)Wireless mesh network (WMN)Metropolitan…
Q: Seatwork BUG BUSTER: What is wrong with the following code fragment? int x,y; int array[10][3];…
A: The answer is given below.
Q: When generating volumes on a dynamic disc in Windows Server 2016, describe any two methods for…
A: Given: Volume is a word that refers to the notion of a disc partition that has been formatted with a…
Q: hree requirements for a successful and efficient network
A: 1.Performance Transit time and response time are two examples of performance indicators. The length…
Q: How many words can you use to describe a mobile database?
A: The answer is given below.
Q: Convert the following numbers to decimal: a) 623(16) b) 525(8)
A: Steps: Hexadecimal to decimal: Sum up each digit multiplied by 16 raise to the power number from 0…
Q: What are the most important considerations while developing a website?
A: A website is a collection of web pages and associated material with a shared domain name and hosted…
Q: What draws certain people to the world of cybercrime
A: Cybercrime, likewise is also called PC crime, the utilization of a PC as an instrument to additional…
Q: What are the responsibilities of the HLR and VLR in GSM networks? What characteristics of mobile IP…
A: Introduction: The acronyms HLR and VLR stand for Home Location Register and Visitor Location…
Q: Explain the difference between how a primitive data is kept in memory and how a reference data is…
A: Memory: Memory refers to the procedures for acquiring, storing, retaining, and retrieving…
Q: How are centralized and parallel/distributed databases different?
A:
Q: Find the smallest r such that O,(n) > (log, n). maxk=[ (log2 n)2]; maxr=Max[3, [(Log2 n)11; (*maxr…
A: Please check further steps for your answer.
Q: When developing a programme, each language has a set of rules that must be properly observed. What…
A: Programming: Each programming language has its own set of rules that govern its structure. A…
Q: indows, Mac, Android, etc.) are compared for multithreading approaches. The CPU Scheduling Algorithm…
A: Multithreading approaches for uniprocessor and multiprocessor systems in various working systems…
Q: Explain how a character set is utilised to represent the string in question.
A: The character set refers to a set of all the valid characters that we can use in the source program…
Q: How can mobile Mapping and DaaS (Data as a Service) implemented in Database system (HR)?
A: Both Mobile mapping and DaaS can be implemented in Database system.
Q: Are there any definitions available for the term "intrusion prevention system?"
A: Solution : Intrusion Prevention System : Intrusion prevention systems (IPS) are network security…
Q: At least four (4) internet security best practises should be discussed, describing how their…
A: Internet Security: The word "internet security" refers to the protection of online activities and…
Q: Sample Input/Output: Depicted below are sample outputs when the program is executed (the items in…
A: Flowchart is a pictorial representation of the flow of the program depicted using mathematical…
Q: We'd want to know why magnetic tape is still being utilized at the place you discovered it.
A: Magnetic tapes are used in the following ways: Initially designed to capture sound, the tape…
Q: lain what an intrusion dete
A: Introduction: Below an intrusion detection system
Q: When a process is terminated, identify the procedure that is responsible for creating free memory…
A: Fragmentation: When fragments are allocated, some space is saved; nevertheless, after the procedure…
Q: Tell us how LCDs function and how colour pictures are produced?
A: INTRODUCTION: Here we need to tell how LCDs function and how colour pictures are produced.
Q: Is Cisco deciding to adopt IP networked access control?
A: Your network will make connections: More rapidly if you setup a Cisco switch appropriately. We'll…
Q: Is there a way to avoid intrusions?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Most PC…
Q: How does an Intrusion Detection System work?
A: In the network security world, an Intrusion Detection System (IDS) is a piece of hardware and…
Step by step
Solved in 2 steps with 1 images

- . What will be the output of the following code, consider the memory address of variable x is 0x0044c and pointer variable ptr is 0x0066f, and consider int data type take 2 byte in the memory void main() { int x[5] = { 1,2,3,4,5 }; int *ptr = x; ptr = ptr + 1; cout << ptr << endl; cout << *ptr << endl; cout << &ptr << endl; cout << &x[0] << endl; cout << *x << endl; x += 2; cout << x << endl; }What is the value of the following expressions (or ERROR)?1. __________ s.length()2. __________ t.length()3. __________ 1 + a4. __________ a.toUpperCase()5. __________ "Tomorrow".indexOf("r")6. __________ "Tomorrow".lastIndexOf('o')7. __________ "Tomorrow".substring(2,4)8. __________ (a.length() + a).startsWith("a")9. __________ s = = a10. __________ a.substring(1,3).equals("bc")Please help me make memory diagrams for points one, two and three in the program. I dont know how to do so and I need to understand, also please explain what youre doing as youre solving#include <stdio.h> int foo (int);int jupiter(int, int);int mercury(int, int); int main(void){ int x = 2, y =4, z = 10; y = foo(y); y = -4 + jupiter(x, z) * 2 ; // Point 3 return 0;} int mercury(int m, int n){ int t; t = m + 2 * n; // Point 1 return t;} int jupiter(int i, int j){ int d = j; d = mercury(i % 400, i); // Point 2 return d;} int foo(int x){ int y = x; x = y * 2; return x;}
- Create the generated machine code from snippet code as follow: int i=10, j, x;for (a=10; a>0; a--) {if (a % 2 == 1) i += a;else i /= 2;j = i*2;}x = i+j; please solve max in 30 minutes thank uWhat is the output of the following code int a = 10, b = -12, c = 0, d; d = ++a + b ++ / --c; cout<<"\n"<<a<<" "<<b<<" "<<c<<" "<<d<<endl; 11 11 -1 23 12 -11 -1 23 10 -11 -1 24 11 -11 -1 23 11 -11 -1 22 No hand written and fast answer with explanationWrite the C equivalent “train” function #void train(int*A, int*B, int*C, int k) train: add $t4, $0, $0bus: add $t5, $t4, $a1 lw $t6, 0($t5) add $t5, $t4, $a2 lw $t7, 0($t5) add $t6, $t6, $t7 add $t5, $t4, $a0 sw $t6, 0($t5) addi $t4, $t4, 4 slt $t5, $t4, a3 bne $t5, $0, bus jr ra
- Identify all private, shared variables in the following code snippet. What is the output of the program (e.g. the value of IS)? int A[100]; int count; void work(int index[]) { float B[10]; …… } void main(){ int IS = 10; int i=0; #pragma omp parallel private(i) { int index[10]; work(index); #pragma omp for reduction(+:IS) for(i=0;i<100;i++) { IS = IS + i; } } printf(“%i\n”, IS); }I need to create an UML digram from the following code: import java.util.Scanner;//Code Provided For Project Two.class Main {public static void main(String[] args) {Scanner input = new Scanner(System.in);System.out.print("Enter the first complex number: ");double a = input.nextDouble();double b = input.nextDouble();Complex c1 = new Complex(a, b);System.out.print("Enter the second complex number: ");double c = input.nextDouble();double d = input.nextDouble();Complex c2 = new Complex(c, d);System.out.println("(" + c1 + ")" + " + " + "(" + c2 + ")" + " = " + c1.add(c2));System.out.println("(" + c1 + ")" + " - " + "(" + c2 + ")" + " = " + c1.subtract(c2));System.out.println("(" + c1 + ")" + " * " + "(" + c2 + ")" + " = " + c1.multiply(c2));System.out.println("(" + c1 + ")" + " / " + "(" + c2 + ")" + " = " + c1.divide(c2));System.out.println("|" + c1 + "| = " + c1.abs()); Complex c3 = null;try {c3 = (Complex)c1.clone();}catch (CloneNotSupportedException e)…need main class in java with user input that prints like the following in a (y/n) loop. reads from a txt file and second class
- When the code below is run, it produces undefined and unpredictable results. Why?Can you suggest an intervention to resolve this issue without removing or changingany of the existing lines of code? (hint: add a line of code) char *myPtr;myPtr = malloc(10*sizeof(char));for (int i = 0; i < 10; i++){myPtr[i] = 'a';}myPtr[10] = '\0';Java Program ASAP Modify this program so it passes the test cases in Hypergrade becauses it says 5 out of 7 passed. Also I need one one program and please correct and change the program so that the numbers are in the correct places as shown in the correct test case. import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.ArrayList;import java.util.Arrays;import java.util.InputMismatchException;import java.util.Scanner;public class FileSorting { public static void main(String[] args) { Scanner scanner = new Scanner(System.in); while (true) { System.out.println("Please enter the file name or type QUIT to exit:"); String fileName = scanner.nextLine(); if (fileName.equalsIgnoreCase("QUIT")) { break; } try { ArrayList<String> lines = readFile(fileName); if (lines.isEmpty()) { System.out.println("File " +…In python, Problem Description:Sheldon and Leonard are physicists who are fixated on the BIG BANG theory. In order to exchange secret insights they have devised a code that encodes UPPERCASE words by shifting their letters forward. Shifting a letter by S positions means to go forward S letters in the alphabet. For example, shifting B by S = 3 positions gives E. However, sometimes this makes us go past Z, the last letter of the alphabet. Whenever this happens we wrap around, treating A as the letter that follows Z. For example, shifting Z by S = 2 positions gives B. Sheldon and Leonard’s code depends on a parameter K and also varies depending on the position of each letter in the word. For the letter at position P, they use the shift value of S = 3P + K. For example, here is how ZOOM is encoded when K = 3. The first letter Z has a shift valueof S = 3 × 1 + 3 = 6; it wraps around and becomes the letter F. The second letter, O, hasS = 3 × 2 + 3 = 9 and becomes X. The last two letters…











