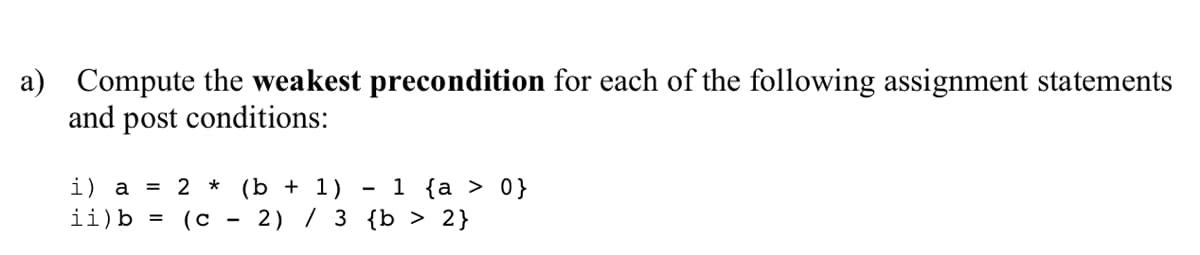
a) Compute the weakest precondition for each of the following assignment statements and post conditions: 1 {a > 0} 2) / 3 {b > 2} i) a = 2 * (b + 1) ii)b = (c
Q: A hypothetical video game involves two phases. In the first phase, players negotiate to obtain weapo...
A: Given That: (1) In the first phase, players negotiate to obtain weapons and resources by sending an...
Q: The first CPU was made by someone.
A: Design Behind CPU: The Central Processing Unit (CPU) is a computing unit that performs arithmetic an...
Q: Explain how a tri-state output AND gate
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: Why is data transformation simplified?
A: Introduction: Transformed data may be easier to utilise for both people and computers. Data that has...
Q: Is it required to reorganise databases?
A: Intro The question is about reorganize data base and here is the solution in the next step.
Q: What exactly is file handling, and why is it required? Explain in depth
A: Introduction: In programming, we may need to create some certain input data a number of times. It is...
Q: can change how text is aligned within the text b
A: Lets see the solution.
Q: As a Python programmer in one company/institution, you are task to create a program that converts te...
A: In this user has to input choice whether user wants to convert Celsius to Fahrenheit or Fahrenheit t...
Q: Plot the following for x = [1:10]. Plot on a linear plot and on a semilog plot (y-axis logarithmic) ...
A: Note: There are different plotting styles for this question. So the answer can vary according to pro...
Q: Laboratory #1 (part 1) of programming and application of the Assembler instruction set. Exercise 1: ...
A: #include <bits/stdc++.h> using namespace std; // recursive function to count set bits int coun...
Q: How can i find the octal number from the user inputted decimal number. In ct
A: Lets see the solution.
Q: If given a chance, how would you teach this class in the online set up?
A: You can teach the students by google meet, google classroom, zoom etc.
Q: 17. 2D Array Operations Write a program that creates a tw
A: Write a program that creates a two-dimensional array initialized with test data. Use any primitive d...
Q: Give an example of how the read-committed isolation level prevents schedules from causing a cascade ...
A: Given :- Give an example of how the read-committed isolation level prevents schedules from causing a...
Q: In this text, we'll talk about SRAM and how it's used most often.
A: Given: In this text, we'll talk about SRAM and how it's used most often.
Q: P address of one host is 25.38.11.56/16. What are the first address (network address) and the last a...
A: The given IP address is 25.38.11.56/16. First, we need to convert this into binary. For 25:Divide (2...
Q: SECTION I: FILL IN THE BLANKS: PICK EXACT TRUE ANSWER************ISO standards include everything fr...
A: Solution: The ISO standard are used world wide for the quality management standard for the product. ...
Q: * CENGAGE | MINBTAP Programming Exercise 3-10 D Instructions + JobPricing.java 1 import java.util.Sc...
A: import java.util.Scanner; public class JobPricing { public static void main(String[] args) { ...
Q: What is the a) "The Weakest Link In Cybersecurity" and b) what can be done to prevent it?
A: a) "The Weakest Link In Cybersecurity Ans:- the weakest link is the employee of any organization. t...
Q: There are multiple ways to prevent from this spyware. There are some that should always keep in mind...
A: Auditing is a mechanism, which is used to record the actions whatever happens on a computer system. ...
Q: Problem 2 Write the recurrence for the runtime of the following algorithm and estimate its asymptoti...
A: SUMMARY: - Hence, we discussed all the points.
Q: 1. AES is used to encrypt data transferred over a wireless channel. Unfortunately, on arrival, one o...
A:
Q: 1. If a node x is the inorder successor of node y then node x must appear in y's subtree. (In Binary...
A: inorder traversal means traversal through left root right.
Q: .How do l create Content Web for engaging teaching and learning
A: Creative content web for engaging teaching and learning.
Q: rovide the menu as shown below; use an infinite loop; stop when user opts 4. dd a process should add...
A: import java.io.*;class Node{int data1; Node next1; public Node(int p){ data1=p; next1=null;}}class s...
Q: 1. The SQL command to create a table is: A. ΜΑΚΕ ΤABLE B. ALTER TABLE. C. DEFINE TABLE. D. CREATE TA...
A: The SQL command to create table is: D. CREATE TABLE Create table is used to create a new table Synt...
Q: Figure out how many subnets are available given the following network addresses: 1. 244.0.0/20
A: Below is the answer to above question. I hope this will be helpful for you....
Q: This question concerns the field GF(256). The modulus is P(x) = x° + x* + x° + x + 1. answer the fol...
A: (0x52)16 (0xA5)16 x7 + x3 + x + 1 x5 + x3 + x2 + 1
Q: Mr. Ali deposits an amount x in a Bank. The bank gives an annual interest of 6% and also charges a m...
A: As per the requirement code is developed. Algorithm: Step 1: Ask the user to enter the amount using ...
Q: und, CPU bound, and memory-bound process
A: In what ways are I/O bound, CPU bound, and memory-bound processes different
Q: You are required to use any OOP language(Java or any other) to create programs that contain differen...
A: According to the Question, we have to create programs that contain different types of coupling using...
Q: 1. Given the following point to point (/30) network, what is the IP address of the unknown router (l...
A: Solution : In above question. All the question are not inter-linked. Hence provided the 1 st answe...
Q: Suppose that Motorola uses the normal distribution to determine the probability of defects and the n...
A: Solution is given below:-
Q: List "Three Main Security Threats categories that you might expect for an enterprise Network. And, g...
A:
Q: The six components of an information system must be identified, listed, and described.
A: Introduction: Information System (IS): An information system is a system for organizing, storing, c...
Q: 3 What makes content web effective?
A: Clear, relevant, and keyword-rich content that delivers the proper message with power and conviction...
Q: What exactly is a server, and what is it often used for?
A: Intro A server is a central computer that stores data (databases) and applications for connecting to...
Q: Write the sum -3+5 – 7+9 – 11+ 13 – 15 + 17 – 19 +21 using sigma notation. The form of your answer w...
A: Given series is, -3+5-7+9-11+13-15+17-19+21 This series contains the odd numbers one one starting fr...
Q: Topic: Big-O Notation and Algorithm
A: solution : The required Python code is as follows: def user_input(n):for i in range(1,int(n)+1):prin...
Q: ARP spoofing and ARP poisoning attack.
A: ARP: ARP stands for Address Resolution Protocol. It is used for mapping MAC address to a IP address...
Q: on any VM out there, how to find and report on the following services using commands: find the tcp ...
A:
Q: 2. Consider the following grammar: 5- aS/ bA A - E Show the detail procedure of parsing 'a bb' in LL...
A: Given that S -> aS/bA A-> ε Non terminals = {S,A} Terminals = { a,b,ε} Starting symbol = {S...
Q: /rite a function in Java that implements the following logic: We are having a party with amounts of ...
A: Logic:- if tea>=5 && candy>=5 return 1 else if tea>=2*candy || candy>=2*tea ret...
Q: Give at least two responsibilities of a Notification Holder
A: Background: Developing a new product's concept is a critical step in the product launch process. Whe...
Q: What is included in the user interface?
A: Introduction: The user interface (UI) is the point at which humans communicate with computers and co...
Q: Using Jcreator, open, compile, and run java and observe its runtime. Write your observation regardin...
A: First let's understand what is encapsulation and then try to obersve the code Encapsulation :- Enc...
Q: O Ox1111ff22
A: Bit-representation of 0xff22 is: 1111 1111 0010 0010 Sign extension of a number means repeating the ...
Q: Given sphere_radius and pi, compute the volume of a sphere and assign to sphere_volume. Volume of sp...
A: C++ code to find volume of sphere of given radius #include <iostream> using namespace std; in...
Q: What are the fundamental components of an Android application? Explain each one.
A: Introduction: Activities, views, intents, services, content providers, fragments, and AndroidManifes...
Q: ned integer may be stored in whic
A: A 32-bit signed integer may be stored
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- For the following, compute the weakest precondition for the following assignment statement given the postcondition. y = 2y – 1 { y > 1}Compute the weakest precondition for each of the following sequencesof assignment statements and their postconditions:1. a = 2 * b + 1;b = a - 3{b < 0}2. a = 3 * (2 * b + a);b = 2 * a - 1{b > 5}Compute the weakest precondition for each of the following assignment statements and selection constructs. Detailed steps are needed. a = 2 * (b - 1) - 1 {a > 0} a = 2 * b + 1 b = a - 3 {b < 0} if (a == b) b = 2 * a + 1 else b = 2 * a {b > 1}
- Write assignment statements for the following: Assign a value of 1 to between if n is in the range -k through +k, inclusive; otherwise assign a value of 0 Assign a value of 1 to uppercase if ch is an uppercase letter; otherwise, assign a value of 0. Assign a value of 1 to divisor if m is a divisor of n; otherwise, assign a value of 0.Solve the following questions: a)Solve the following postfix expressions i)2 3 + 1 - ii)3 4 - 10 + 7 2 3 * - 9 * /a) Convert the following infix to postfix expressions i)2 * 3 - 5 / 2 + 4 ii)1 * 2 * 3 * 4READ QUESTION CAREFULLY AND STRICTLY USE PROVIDED TERMS IN QUESTION AS IT IS. MATCH INPUT AND OUTPUT. DON'T USE FOREIGN TERMS IN SOLUTIONS -------------QUESTION BELOW-------------- Write a C++ program to display the donor details with the collected details. Strictly adhere to the Object-Oriented specifications given in the problem statement. All class names, member variable names, and function names should be the same as specified in the problem statement. Create separate classes in separate files. The class Donor has the following private member variables. Data Type Variable Name string Name int Age float Height float Weight string Gender string BloodGroup important:- Define the member variables and include appropriate getters and setters for the above class. Define a function to display the donor details which will be able to access the private data members of the Donor class. Method Member Function void display(Donor obs) This function is used to display…
- Consider the following programming problem: The values of three integer variables—first, second, and third—must be placed in the three variables max, mid, and min, with the obvious meanings, without using arrays or user-defined or predefined subprograms. Write two solutions to this problem, one that uses nested selections and one that does not. Compare the complexity and expected reliability of the two.Write a simple assignment statement with one arithmetic operator in a programminglanguage you know. For each component of the statement, list the various bindingsthat are required to determine the semantics when the statement is executed. For eachbinding, indicate the binding time used for the language.2. Mention one problem likely to be faced by programs written in programming languageswhich do not support garbage collection.3. Describe the following approaches to garbage collection, giving advantages and disadvantages of each approach.(a) the lazy approach(b) the eager approach(c) generational garbage collection.4. Describe 2 problems that l Write a Java program that inputs a list of integer values in the range of -100 to 100from the keyboard and computes the sum of the squares of the input values. Thisprogram must use exception handling to ensure that the input values are in range andare legal integers, to handle the error of the sum of the squares becoming larger thana standard…1:- USE " ARITHMETIC OPERATIONS USING OPERATOR OVERLOADING " WHILE SOLVING PROBLEM 2:- AND USE PROVIDE TEMPLATES PROVIDED AT END OF QUESTION. --------------------------------------- Write a C++ program using the operator overloading concept and display its results. Strictly adhere to the Object-Oriented specifications given in the problem statement. All class names, member variable names, and function names should be the same as specified in the problem statement. Consider a class named Complex with the private member variables. Datatype Variable int real int imaginary Include the private member variables and the constructor in the class Complex.Define the following public methods in the class Complex. Method Name Description Complex operator+(Complex a2) This function is used to perform the additional operation ofthe two complex numbers and returns the result. Complex operator-(Complex a2) This function is used to perform the subtraction operation ofthe two complex…
- Book: C++ Programming: From Problem Analysis to Program Design 8th edition, D. S. Malik In C++ In this programming exercise, you use abstract classes and pure virtual functions to design classes to manipulate various types of accounts. For simplicity, assume that the bank offers three types of accounts: savings, checking, and certificate of deposit, as described next. Savings accounts: Suppose that the bank offers two types of savings accounts: one that has no minimum balance and a lower interest rate and another that requires a minimum balance and has a higher interest rate. Checking accounts: Suppose that the bank offers three types of checking accounts: one with a monthly service charge, limited check writing, no minimum balance, and no interest; another with no monthly service charge, a minimum balance requirement, unlimited check writing, and lower interest; and a third with no monthly service charge, a higher minimum requirement, a higher interest rate, and unlimited check…Asymptotic function relationships. Verify each of the following statements by the definitions to see if they are true or false 1. If ?(?) = Θ(?), then ??(?) = Θ(?2 ) 2. If ?(?) = ?(?2 ) and ?(?) = Ω(?(?)), then ?(?) = ?(?2) 3. If ?(?) = ?(0. 5?2 ) and ?(?) = Ω(7?2 + ?????), then ?(?) = Θ(?2 ) 4. If ?(?) = ?(?3 ), then ?(?) = Ω(2?3 ) 5. If ?(?) = Θ(?3 ), then ?(?) = ?(2n )Consider the following function definition.void mystery(int* x){// function body}(a) Inside the definition of mystery, the C++ language provides a way to distinguishif x points to a region of memory of automatic or dynamic storage duration.A. TrueB. False

