a) f(n) = 3n³ log³n + 2n/n + 5nº n² + 5n log“ n log n .2 b) f(n) = 5n + 3; c) f(n) = 4"n² + 5" + n³ log n
Q: What are the benefits and drawbacks of utilising parameters instead of a global variable in a C prog...
A: The advantages and disadvantages of global variables and parameters over each other in a C program a...
Q: Why does polymorphism cause greater concern than traditional malware? How does it affect detection?
A: Introduction First of all let's talk about Polymorphism: Polymorphism: The concept of polymorphism i...
Q: What precisely is anti-forensics, and how does it work?
A: Introduction: Anti-forensic tactics are content activities intended to obstruct or harden proper for...
Q: Describe the many types of semantics, when and how they are used, and the benefits and drawbacks of ...
A: Semantics is a key part of linguistics that deals with the comprehension and meaning of words, sente...
Q: Identify and briefly describe each of the five basic task management approaches used in operating sy...
A: 1. Multiuser Multitasking is the ability to perform more than one task simultaneously. It is an im...
Q: Answer the following questions: a) State two advantages of the "orthogonal least square (OLS)' metho...
A:
Q: What is the anticipated modelling approach, and why was it chosen for a certain model?
A: The framework's model methodology is a cycle situated portrayal that underscores the effect or strea...
Q: Distinguish between security management, fault management, and performance management.
A: Distinguish between security management, fault management, and performance management.
Q: What is the function of the Ack Queue in HDFS?
A: Introduction: HDFS is a distributed file system that works on commodity hardware and manages large d...
Q: What should happen if the processor sends a request to the cache while a block from the write buffer...
A: What should happen if the processor sends a request to the cache while a block from the write buffer...
Q: NPBKTCET (national plan for building-up K-12 teachers’ competence of educational technology). The co...
A: 2. The many parties engaged in the elaboration of requirements: Consists of the individuals who elic...
Q: Why not divide the overall design into multiple user viewpoints when conducting user research?
A: Introduction: Design teams use the technique to build products that give consumers meaningful and r...
Q: Distinguish between security management, fault management, and performance management.
A: given - distinguish between security management , fault management, performance management
Q: SQL REQUEST
A: SQL: SQL stands for Structured Query Language. It is used to interact with the database. It is desig...
Q: Write a program that prints out the letters of a word, one on each line, in the format "The letter i...
A: Logic :- use split() method to separate string and store it in array. display each word of array.
Q: Complete the Login class implementation. For the class method check_credentials(), you will need to ...
A: Python Code for above : class Login: # set variable def __init__(self): self.si...
Q: techniques and equipment for data entry with a stylus What exactly does it mean to be a digitiser?
A: Introduction: The digitizer is a layer of glass in touchscreen devices that is meant to translate an...
Q: 13) All computer devices that employ twos-complement mathematics include built-in circuitry that che...
A: Here is the explanation regarding both the questions:
Q: Cache memory is important in today's computers. Explain how cache memory works and why there was no ...
A: Intro Cache memory refers to a memory component that holds data on a temporary basis while performin...
Q: Which user management tool is required to assign a logon script to a user?
A: Local Users and Groups is said to be a Microsoft Management Console (MMC) snap-in which lets you man...
Q: fill in the blank question of Architectural Styles about software enginneer ____________style encaps...
A: Answer: 1. ____style encapsulates functional processing. Data-centric 2. ____________style restri...
Q: Recall in a three-pass compiler the only objective of the middle-end is improving the code while pre...
A: The benefits of a two-pass compiler more than a single-pass generator: In comparison to that same pr...
Q: Cryptography Question Show that each of the ciphertexts ZOMCIH and ZKNGZR, which were obtained by sh...
A: The shift cipher is one of the simplest and most widely known encryption techniques.
Q: Why would we use circular Queue instead of a simple or Double Ended Queue? Explain
A: the answer is given below:-
Q: Two stacks S1 and S2 can be implemented using one array. Write procedures: PopS1(Stack), PushS1(Stac...
A: IMPLEMENTATION OF TWO STACKS USING ONE ARRAY: Create an array. ( size == n // n is an integer ) ...
Q: Write MIPS assembly code implementing the following C/C++ statement: a[k*2-4] = a[k]*2 + 7;
A: Given C++ statement: a[k*2-4] = a[k]*2 + 7; To convert: Convert the given statement into MIPS as...
Q: What is the output printed by writeln statement if the parameter passing mechanism is call by value?...
A: The Answer is
Q: WAP to convert a square into a rectangle. Perform the conversion in source class.
A: Explanation: Include the necessary header files. Create two functions. One for printing square and ...
Q: Was there any impact on the Symbian, Android, and iPhone operating systems as a result of the file d...
A: Intro The mobile operating system Android is built on a modified version of the Linux kernel and oth...
Q: Each time slot contains 148 bits. Just 114 of these 148 bits reflect speech or other info. The remai...
A: The answer is
Q: Programing language is Java. Define a class Person that represents a person. People have a name, an...
A: the answer is given below:-
Q: What are the fundamental building blocks of manufacturing?
A: What are the fundamental building blocks of manufacturing?
Q: You are given 4 items as (value, weightpairs in this format {{20, 5}, {60, 20}, {25, 10}, {X, 25}}Yo...
A: Required:- Give me an example of f formatted string in python. Take all the data from the user. Appr...
Q: PLEASE ENSURE TO USE THE FRAMEWORK PROVIDED IN THE IMAGES, AND THAT IT WORKS WITH THE TESTER CLASS. ...
A: CODE TEXT SO YOU DON'T HAVE TO TYPE :) public class Circuit { private int firstSwitchState; // 0 ...
Q: %D What is T(n) = 6T(n/7)+n, Vn >2 and T(1) = 1. O O(n) O O(log n) loge O 0(1) O(n log n) No valid a...
A:
Q: People who work with computers and humans use a lot of different ways to measure how well they work ...
A: Answer Introduction: He addresses a vision articulated in his latest book Superminds a framework for...
Q: xamine the benefits and drawbacks of various system models.
A: Introduction: The following are some of the benefits of using a modelling methodology: It forces us ...
Q: What are the benefits and drawbacks of utilising parameters instead of a global variable in a C prog...
A: INTRODUCTION: The user may transmit the values of local variables specified in the main program to s...
Q: What are the different ways the project manager uses Webcams?
A: A webcam is a kind of video camera that transmits or streams images or video in real time to or over...
Q: How is UML's abstract class modelled? bold no markup italics
A: Introduction: An abstract class is a class that has an action prototype but no implementation.
Q: umber f such that 128 + f > 128? and
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: When designing a solution for a problem, which parts of speech are most likely to become objects? An...
A: The designing of the solution depends on many factors if you are designing a solution one main thing...
Q: People who work with computers and humans use a lot of different ways to measure how well they work ...
A: Introduction: He addresses a vision articulated in his latest book Superminds a framework for reachi...
Q: Consider the following code. What will be printed to screen? def my_func(): a += 1 return a a = 5 re...
A: B) UnboundLocalError
Q: In GSM, a "TDMA frame" is composed of eight distinct time slots. Each
A: The answer is
Q: 3. Show the sequence of numbers that would be generated by below range expressions: a. range(5): b. ...
A: (a) Code:- # Syntax of range can be given as for variable_name in range(starting_point, ending_point...
Q: What should happen if the processor sends a request to the cache while a block from the write buffer...
A: Introduction: The cache will be able to satisfy the request since it will be idle while the writing ...
Q: List down the terminals in the above grammar.
A: A grammar in regular language is defined as a set of productions that usually define a language. The...
Q: insa הרב[ הSחה ו רו1 ם| ןוו יח *Python' [1] "Strings are sequences len("wonderful") "Mystery' [:4] "...
A: Code: print ('Python'[1])print('Strings are sequences of characters.'[5])print(len('Wonderful'))prin...
Q: rite code that generates 100 million random points (X,Y) that are uniformly dis- tributed on the tri...
A: The idea is to simulate random (x, y) points in a 2-D plane with domain as a square of side 1 unit. ...
Computer Science
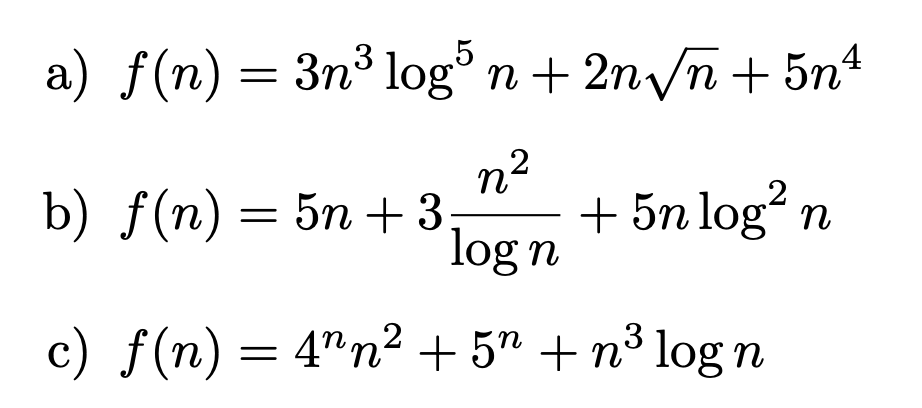
Give asymptotic estimates, using the Θ-notation, for the following functions. Justify your answer, using asymptotic relations between common functions.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- f(x)=x^2(x-4)(x+2)^2 Bounce(B) or Cross(C) (in ascending order of zeros): Incorrect (So type CBC or BBB or...)1. Write the code using vpasolve and find the x and y values. (1) ((log(x)/log(3))+3y=13, x^2-2y=1 2. Quadratic square matrix A=[2 3; 1 a], the sum of all elements of A^5 is 2474856. Find the value of the constant a. (a<=100, natural number)If S = { x | 0 ≤ x ≤ 10}, A = { x | 1 ≤ x ≤ 5}, B = { x | 1 ≤ x ≤ 6}, and C = { x | 2 ≤ x ≤ 7}(a) S ⋃ C(b) A ⋃ B(d) A’ ⋂ C(c) A’⋃ (B ⋂ C)(e) (A ⋂ B) ⋃ (B ⋂ C) ⋃ (C ⋂ A)
- eliminate arbitrary constant: a. y^2 = 4ax b. y = cx + c^2 + 1 c. y = A + Bx + Cx^2 - 2x^3An operation ∗ on the set of positive integers is defined by a ∗ b = (a + b) a−b . Evaluate 1024 ∗ (512 ∗ (256 ∗ (128 ∗ (64 ∗ (32 ∗ (16 ∗ (8 ∗ (4 ∗ (2 ∗ 1). a. 2028 b. 2048 c. 2047 d. 2027What is the smallest 32-bit floating point number f such that 128 + f > 128? and What is the smallest 32-bit floating point number g such that 1 + g > 1 ? solve this please
- def sind_approx(x: float) -> float: """ sind_approx(x) returns the Bhaskara I's sine approximation for sine in degrees. This approximation is only valid within the range [0, 180]. The sine approximation is given as: 4 * x * (180 - x) / (40500 - x * (180 - x)) example: sind_approx(90.0) -> 1.0 example: sind_approx(0.0) -> 0.0 example: sind_approx(180.0) -> 0.0 example: sind_approx(45.0) -> 0.7058823529... TODO: add param and return descriptions here """ pass # TODO: replace 'pass' with the function implementation7) Under computer integer arithmetic, the quotient J/K of two integers J and K is less than or equal to the usual quotient. True or false?C (n,k) = n! k!(n-k)! Using above formula calculate the following: C(15,14) C(20,7)
- Given the following definitions: U={a,b,c, d, e, f, g} A={a, c, e, g} B={a,b,c,d} find A n BGiven sphereRadius, compute the volume of a sphere and assign sphereVolume with the result. Use (4.0 / 3.0) to perform floating-point division, instead of (4 / 3) which performs integer division.Volume of sphere = (4.0 / 3.0) π r3 (Hint: r3 can be computed using *)For all positive numbers aaand bbwith a>ba>b, ln(a−b)=ln(a)/ln(b)ln(a−b)=ln(a)/ln(b) True or false

