You are given 4 items as (value, weightpairs in this format {{20, 5}, {60, 20}, {25, 10}, {X, 25}}You can assume that the array is sorted based on the capacity of knapsack is 50. The item no. 4 (whose weights 25 ) is taken fractionally to fill upto the knapsack capacity. That fraction is represented in format. What is the lowest possible value of b? ratio. The For the question above, assume the total value stored in the knapsack is 135 after you have filled upto the knapsack capacity. What is the value of X(in other words, the ralue the item no. 4) ? Bive your answer to at least two decimal places
You are given 4 items as (value, weightpairs in this format {{20, 5}, {60, 20}, {25, 10}, {X, 25}}You can assume that the array is sorted based on the capacity of knapsack is 50. The item no. 4 (whose weights 25 ) is taken fractionally to fill upto the knapsack capacity. That fraction is represented in format. What is the lowest possible value of b? ratio. The For the question above, assume the total value stored in the knapsack is 135 after you have filled upto the knapsack capacity. What is the value of X(in other words, the ralue the item no. 4) ? Bive your answer to at least two decimal places
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter6: Arrays
Section: Chapter Questions
Problem 17RQ
Related questions
Question
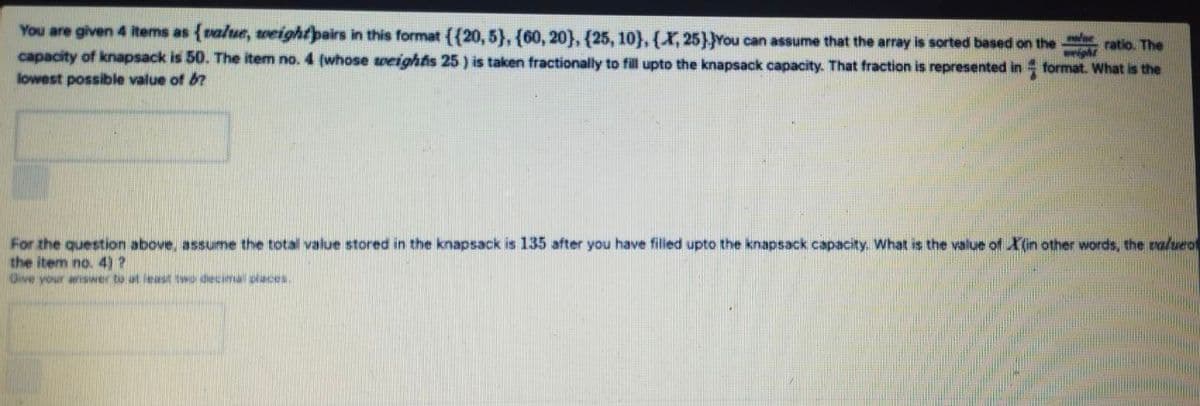
Transcribed Image Text:You are given 4 items as {value, wveightpairs in this format ({20, 5}, {60, 20}, {25, 10},{X,25}}You can assume that the array is sorted based on the
capacity of knapsack is 50. The item no. 4 (whose weightis 25 ) is taken fractionally to fill upto the knapsack capacity. That fraction is represented in format. What is the
ratio. The
lowest possible value of b?
For the question above, assume the total value stored in the knapsack is 135 after you have filled upto the knapsack capacity. What is the value of X(in other words, the valueo
the item no. 4)?
Give your arSwer to at least two decimal places
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage