A hash function takes an item and makes it into a number. A hash code is the number computed by a hash function modulo the table size. A hash table is an array (or array of linked lists) that you put values into for storage. An item's location in this table is based on the hash o The load on a table is the number of values in the table divided by the number of free slots in the table. Java's hash contract states that if two items are equal they will have the same hash code, and if two items are not equal they will have diff
A hash function takes an item and makes it into a number. A hash code is the number computed by a hash function modulo the table size. A hash table is an array (or array of linked lists) that you put values into for storage. An item's location in this table is based on the hash o The load on a table is the number of values in the table divided by the number of free slots in the table. Java's hash contract states that if two items are equal they will have the same hash code, and if two items are not equal they will have diff
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter18: Stacks And Queues
Section: Chapter Questions
Problem 16PE:
The implementation of a queue in an array, as given in this chapter, uses the variable count to...
Related questions
Question
Need help with this computer scinece question
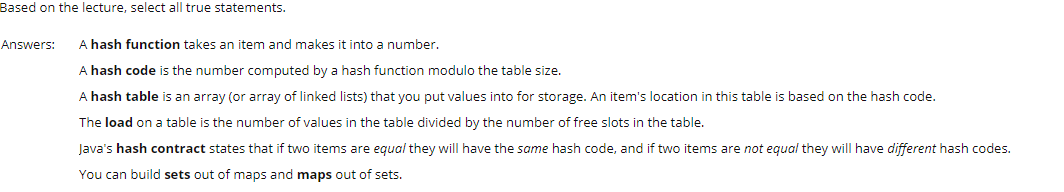
Transcribed Image Text:Based on the lecture, select all true statements.
Answers:
A hash function takes an item and makes it into a number.
A hash code is the number computed by a hash function modulo the table size.
A hash table is an array (or array of linked lists) that you put values into for storage. An item's location in this table is based on the hash code.
The load on a table is the number of values in the table divided by the number of free slots in the table.
Java's hash contract states that if two items are equal they will have the same hash code, and if two items are not equal they will have different hash codes.
You can build sets out of maps and maps out of sets.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning