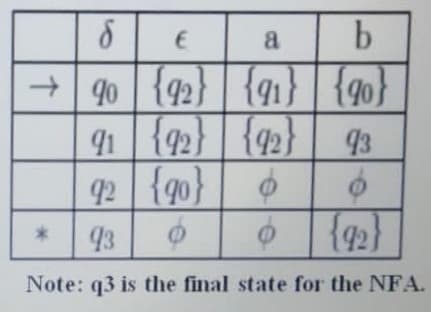
a + | 90 {92} | {g1} {90} 91 {92} | {42} 93 92 {g0} | ¢ 6 | {92} 93 e NEA
Q: Exercise 7: Convert the DFA below into 1) a regular expression 2) a regular grammar 1
A: 1) DFA to Regular Expression: Above DFA:- Where s0, s1, s2, s3 in circles represents the remainders...
Q: Write the code for adding new elements dynamically.
A: Your solution is here with an output .
Q: What is the difference between a monochrome display and a multicolor display?
A: your question is about What is the difference between a monochrome display and a multicolor display?
Q: Prove that the following grammar is ambiguous: → → + | → a | b | c
A: Given :- Prove that the following grammar is ambiguous: <S> → <A> <A> → <A>...
Q: (a) Rewrite each of the terms of the following expressions in binary and simplify the expression. Co...
A:
Q: Ask the user to enter a number between 1 and 20. If they enter a number outside of that range, print...
A: Use a switch with all 20 cases along with default case which will handle the out of range case So al...
Q: This happens when a security mechanism fails and then permits all activity Fail-severe Fail-cl...
A: FAIL OPEN
Q: Because authorization lists are so vulnerable to tampering, they must be encrypted and guarded. What...
A: The authority list is an encrypted list that must be guarded. If it were to be changed, the authorit...
Q: Perform the specified operation using the given format Fill in table Operation Integer Binary Overfl...
A: According to the information given:- We have to fill the blank box with its operation.
Q: What is a system unit
A: What is a System Unit and what are the common components inside the system unit? (watch the video in...
Q: A Wireshark trace of TCP traffic between hosts A and B indicated the following segments. Host A sen...
A: Protocol for Controlling Transmission: Amongst the most important finding in the TCP / IP protocol s...
Q: (c) Find the sum-of-products expansion of the following Boolean function: f(a, b,c) = a(b+ č) + ab +...
A: Defined the sum of products and equivalent of given boolean functions
Q: VHDL Behavioral Modeling ORIGINAL CIRCUIT (not the simplified)
A: This diagram seems like a Full Adder. S=A⊕B⊕Ci Co = AB+BCi+CiA
Q: What exactly are artificial intelligence (AI) and machine learning? How do corporations make advanta...
A: Introduction: Al discusses artificial intelligence (AI) and machine learning, as well as how organis...
Q: Identify any two business strategies and discuss the link between strategy and business analytics(BA...
A: INTRODUCTION: The concerns of any business are defined by what happens in their daily environment, ...
Q: What is the content of the list based on the following stateme Ist1 = [ aval for aval in range(1, 16...
A: The answer is
Q: te PL/SQL anonymsblock to fill newly added colum nsfor ea ch gmploxeeid entered by end user from scr...
A: DECLARE v_empno emp_temp.employee_id%TYPE := 176; v_asterisk emp_temp.stars%TYPE := NULL; sal em...
Q: Why is least privilege so crucial? Why should employees rotate jobs, separate duties and take mandat...
A: INTRODUCTION: The principle of least privilege, often known as PoLP, is an information security the...
Q: Problem 4: Write a C program to input cost and selling price of a used car and check after selling t...
A: Code #include<stdio.h> int main() { int cp,sp,x,y; scanf("%d", &cp); scanf("%...
Q: List 3 purposes of a stack?
A: Three purpose of stack are Implement Functions - It is generally used to implement function which ...
Q: Suppose a program has runtime proportional to nlogn, where n is the input size. If the program take...
A: Let, runtime for input n be T(n) Given, T(n) ∝ nlog(n) Let the proportionality factor be k. We have,...
Q: Compare full mesh topology and dual-home implementation in Wide Area Network.
A: Compare full mesh topology and dual-home implementation in Wide Area Network.
Q: Three rounds have been taken with an iterative method for equation solving. The approximation has in...
A: clcclear digit_colors = {'Black','Brown','Red','Orange','Yellow','Green','Blue','Violet','Gray','Whi...
Q: irite a Javascript program to validate an email assuming it is taken from the user and print its res...
A: Start Take the input email address Validate the email address Email is valid Print it is valid Stop
Q: WEB DEVELOPER EXERCISE 1) write a Javascript program to validate an email assuming it is taken from ...
A: Required:- WEB DEVELOPER EXERCISE 1) Write a Javascript program to validate an email assuming it is ...
Q: Modify the unsortedArrayAccess class by adding a method that find the smallest element and average i...
A: According to the Question below the Solution:
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms
A: The answer is
Q: Returns the number of times item appears in aList.
A: Python is a popular programming language among developers used for data analysis and predicting mode...
Q: Hi in the below code I would like to remove the blank tokens and how to achieve it. #include #i...
A: You want to remove blank token from your code.. So, In Strep 1 your given code and output. In step 2...
Q: ove to describe the protocol of du
A: In Wi-Fi Direct, groups are created as one of the following types: Persistent, in which automatic re...
Q: What are the important javascript array method explain with example.
A: Step 1 The answer is given in the below step.
Q: What are some ways we can make sure our database and data is secure?
A: Given To know various ways for securing the database.
Q: Computer Science Establish the input, processing, and output of airline and hotel reservation credi...
A: Establish the input, processing, and output of airline and hotel reservation credit card transaction...
Q: Use Matlab commands to load mat into the workspace, then use the information in the inventory variab...
A: According to the information given:- We have to write a Matlab code to create matrix.
Q: Solution is needed in C# Language please! You are tasked with writing a program to process students...
A: Code:= using System;class Program { static void Main() { Console.WriteLine(" -----------------...
Q: Which of the following constraints correctly describe this requirement: The management also requires...
A: Given The answer is given below.
Q: In Java Determine the output of the following code. boolean done = false; if (done = false) S...
A: Below i have answered:
Q: python" Call the function tourism with the arguments 1 and 4 (in that order) and print the value the...
A: 0.30959752321981426
Q: Computer hardwere application Assignmant (pascaline) stating features of both machine
A: Pascal's calculation: Pascal's calculation (sometimes called the numeracy instrument or the Develope...
Q: In a computer with a 32-bit data-bus, how many 4-bit wide memory components are used? the answer to ...
A: The answer is
Q: Tb=1; fc=10; t=0:Tb/100:1; c=sqrt(2/Tb)*sin(2*pi*fc*t);
A: The goal of these BASK commands is to imitate fourier series noise. The result is a curve with a pea...
Q: You will be creating an interactive chat-bot type program. Eliza is a therapist program that interac...
A: Below is the complete solution of the given question in detail. Below steps contains Python Progra...
Q: Determine the machine code of the given instructions. Include operand or address size prefix. For th...
A: Assembly language is a low-level programming language. It converts instruction into the machine code...
Q: Risk is unavoidable. Which of the following is not something we would do with risk? Accept it ...
A: Answer:- Risk Transfer is a Risk Management strategy and is not part of Risk Management. 1- Risk Ac...
Q: Translate from hexadecimal to RISC-V.
A: vscale/src/test/inputs have several hex inputs with similar format: 32 hex chars per line (16 bytes,...
Q: Using asterisk (*) pattern to write a program in C++ to display such below style: ***** ***
A: The Answer is in Below Steps
Q: Recall the naïve divide and conquer O(n2)-time multiplication algorithm, call it NaiveD&Cmult, to mu...
A: Answer: I have done code and also I have attached code and code screenshot as well as output
Q: Device controllers cannot directly access the main memory without using CPU. true or false?
A: The answer is
Q: efined, show that f ◦
A: It is defined as,
Q: Develop a fictional ethical hacking scenario. Describe the scenario in enough detail that someone ca...
A: Answer: I have given answered in the brief explanation
Step by step
Solved in 2 steps with 1 images

- 3. Assume $s1 = 0xefbcad97, $s2 = 0x6521fedc, calculate...Lines of code can only be added inbetween gery lines of code. ie, lines 12-14.Numbers between 0 and 15 are stored in the memory location starting from physical address B000Fh randomly. Write a program which finds the element order number in the string starting from 0 to 15 and writes to physical address C000Fh. (Eg: "1" is 2nd element in the first string, "2" is 4th element, ....etc)
- Floor(2.4) + Ceil(2.9) is equal toAssignment for Computer Architecture: N Factual by Recusion *please have comments in the code* You are to write a program in MIPS that computes N! using recursion. Remember N! is the product of all the numbers from 1 to N inclusive, that is 1 x 2 x 3 x (N – 1) x N. It is defined as 1 for N = 0 and is undefined for values less than 0. The programs first requests the user to input the value of N (display a prompt first so the user knows what to do). If the input value is less than 0, the program is to display “N! undefined for values less than 0” and then requests the user to input the value of N again. If the value input is non-negative, it is to compute N! using a recursive function, that is one that calls itself. You are to have your name, the assignment number, and a brief description of the program in comments at the top of your program. Since this is an assembly language program, I expect to see comments on almost every line of code in the program. Also make the…Using the python code below Identify the following: a) Variables b) Conditional Statements C) Operators d) Loops e) Functions PYTHON CODE: name = []age = []dep = []address = []sr_code = []status = []condition = []def add(): inp = input("Name: ") name.append(inp) inp = input("Age: ") age.append(inp) inp = input("Department: ") dep.append(inp) inp = input("Address: ") address.append(inp) inp = input("SR-Code: ") sr_code.append(inp) inp = input("Vaccination Status: ") status.append(inp) inp = input("Health condition: ") condition.append(inp)def delete(sr_code): ids = input("Enter Sr_code to DELETE:") for i in range(0,len(name)): if(sr_code[i]==str(ids)): del name[i] del age[i] del dep[i] del address[i] del sr_code[i] del status[i] del condition[i] print("Deleted Successfully!") return print("Sr code not found!")def update(sr_code):…
- Please design a data structure to allow the following three operations: 1. push (insert a new number) 2. find_Kmin (return the value of the K-th smallest number without removing it). 3. pop All operations should be done in 0(log n) time or better.4.16 LAB: Interstate highway numbers Primary U.S. interstate highways are numbered 1-99. Odd numbers (like the 5 or 95) go north/south, and evens (like the 10 or 90) go east/west. Auxiliary highways are numbered 100-999, and service the primary highway indicated by the rightmost two digits. Thus, I-405 services I-5, and I-290 services I-90. Given a highway number, indicate whether it is a primary or auxiliary highway. If auxiliary, indicate what primary highway it serves. Also indicate if the (primary) highway runs north/south or east/west. Ex: If the input is: 90 the output is: I-90 is primary, going east/west. Ex: If the input is: 290 the output is: I-290 is auxiliary, serving I-90, going east/west. Ex: If the input is: 0 the output is: 0 is not a valid interstate highway number. Ex: If the input is: 200 the output is: 200 is not a valid interstate highway number. See Wikipedia for more info on highway numbering. 344614.2153518.qx3zqy7 Use Python. Don't use Java cause that's…JAVA and Netbeans Using Looping Statement, Create a simple Multiplication Table for user input number (same as below):
- Topic: Binary Operation True or False The operation a * b = a + b − 1 on the set of integers has no identity element.C++ 3.23 LAB: Interstate highway numbers Primary U.S. interstate highways are numbered 1-99. Odd numbers (like the 5 or 95) go north/south, and evens (like the 10 or 90) go east/west. Auxiliary highways are numbered 100-999, and service the primary highway indicated by the rightmost two digits. Thus, I-405 services I-5, and I-290 services I-90. Given a highway number, indicate whether it is a primary or auxiliary highway. If auxiliary, indicate what primary highway it serves. Also indicate if the (primary) highway runs north/south or east/west. Ex: If the input is: 90 the output is: I-90 is primary, going east/west. Ex: If the input is: 290 the output is: I-290 is auxiliary, serving I-90, going east/west. Ex: If the input is: 0 the output is: 0 is not a valid interstate highway number.Solve this problem, include c++ code and flowchart please. Problem Bad Spelling (Recurse) Problem Overview: Annagramma Hawkin is a witch… but not a very good one. According to some very senior witches she is overly concerned with flashy magics and not nearly concerned enough about real problems facing real people. Her latest equipment acquisition underlines this flair for the dramatic. She bought an enchanted Boggle set. This device functions by generating a 5x5 grid of letters. Any sequence of letters connected to each other either by being beside or diagonal from each other (with each letter used only once) creates a successful and entirely satisfyingly flashy spell. It really just saves witches from having to generate their own spell names and allows them to avoid the use of ones like: Hocus Pocus. For example, consider a 5x5 grid with random letters as depicted below. The object is to find words formed in the grid by contiguous sequences of letters. Letters are considered to be…

