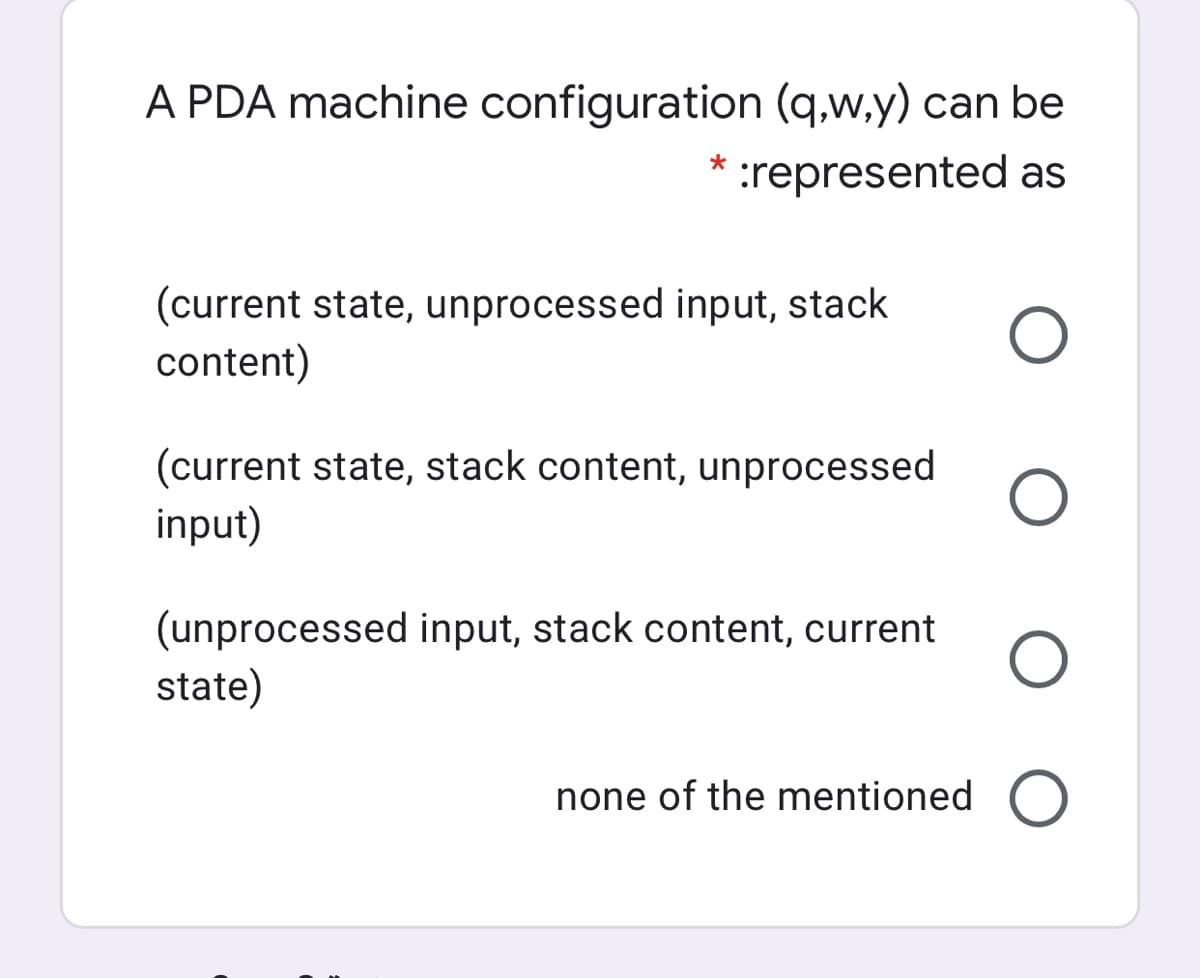
A PDA machine configuration (q,w,y) can be :represented as (current state, unprocessed input, stack content) (current state, stack content, unprocessed input) (unprocessed input, stack content, current state) none of the mentioned O
Q: When should you use Power Pivot? When you want to clean, shape and transform data When you need to c...
A:
Q: Descriptive models have some important qualities and properties, which we will discuss below
A: Introduction: A descriptive model elucidates the link between a system or other object and its surro...
Q: In what ways may we as programmers be defensive, and what are some examples of defensive programming...
A:
Q: Write a program that takes in a line of text as input, and outputs that line of text in reverse. The...
A: ANSWER:-
Q: How can managers use the visualisations in Power BI?
A: The Manager effectiveness dashboard for Power BI uses Workplace Analytics data to analyze people man...
Q: 5. What is the gray code of 101011110010102? 6. Solve: ABF5H - 9CDFH 7. What is the 2's complement o...
A: Answers: 1. 11111000101111 2. Result (hex) f16 , Result (decimal) 3,862 3. 0000 0010 0100 1011
Q: Write a Python program to input an integer t and print the sum of all multiples oft and 5 in the out...
A: Python Program: # Enter an integer t by user as inputt = int(input("Enter an integer: ")) # s for su...
Q: pplication for each level of healthcare services and the data mining technique to be used.
A: Data mining Data mining is the act of sifting through big data sets in order to find patterns and r...
Q: AVA PROGRAMMING - Write a program that displays the employees Ids together with their first and last...
A: As per the requirement program is done in java. Here Employee.java and EmployeeDetails.java are inte...
Q: 2. What type of architecture, under ISA classification, directly uses the memory, instead of a regis...
A: The expression "CISC" (complex instruction set computer or computing) alludes to PCs planned with a ...
Q: What value is will be loaded into the register $t0, if the following MIPS statements were executed. ...
A: Solution:-
Q: While reporting your data, discuss the many types of visuals that are utilized in technical papers i...
A: Photography and film have a long history in anthropological study, Photography has a long history of...
Q: . Fragments, Creating Fragments with java Code explain detailed
A: Overview:A fragment is a reusable class executing a part of a movement. A Fragment ordinarily charac...
Q: Reference link: https://www.healthit.gov/providers - professional /faqs/what - does - http-web - ad...
A: HTTP and Web Address - HTTP stands for hypertext transfer protocol which means that it provides comm...
Q: Write a program that takes in an integer in the range 11-100 as input. The output is a countdown sta...
A: Program Explanation: Import the class for scanner Define a class for countdown Declare and define t...
Q: So, what's so important about the von Neumann bottleneck?
A: INTRODUCTION: Von Neumann bottleneck: The standard computer architecture imposes a throughput restri...
Q: In the.NET Framework, what is the difference between a DLL and an EXE?
A: Answer :- DLL - Dynamic Link Library If an assembly is compiled as a class library and provides t...
Q: Discuss the importance of systems administration in the context of a company or organization.
A: Answer:
Q: examples of two-way communication in which each party take turns transmitting
A: Two way communication means that communication is happened between both sides Here both sender and r...
Q: Write the pseudo-code for an algorithm that reverses the order of the elements in an array of size N...
A: An array is the sequential collection of similar elements. The array is a fixed size data structure....
Q: Your data warehousing project team is discussing whether to build a prototype before implementing it...
A: INTRODUCTION: Here we need to give suggestions.
Q: How many networks have been discovered as a result of the routing protocol?
A: Routing protocols are means for exchanging routing information between routers and making routing ch...
Q: 1. Identify conditional and join probabilities from the following example. Explain how the probabili...
A: Solution :-
Q: In Python Make a function that given an integer list of lists, returns a list of couples such as th...
A: Step 1 : Start Step 2 : Define a function myFunction() to return a list of couple where the differen...
Q: 2. Next Destination by CodeChum Admin Yay! Because of your help, we're now at our first destination...
A: Algorithm: Start Initialize next_destination to 10 Declare 2 integer pointer variables pointer_1 an...
Q: 10. Q1 : What is an atomic instruction? Show that if the wait operation is not executed atomically,...
A: I have answered this question in step 2.
Q: KMP -- What are tables next and fail for the pattern ABCABDABB. Show how the answer is derived.
A: Introduction: Given pattern is ABCABDABB Rules:Prefix: For a string, all substrings from first chara...
Q: Subject : Data Structure Language : C What is hashing?Give it's application. Also, discuss the pros ...
A: Hashing: Hashing is one of the technique or methodology for mapping the keys and value by using hash...
Q: The most basic peer-to-peer networks are made up of two computers that are directly connected over a...
A: A peer-to-peer network is used for connecting two networks together. The communication between netwo...
Q: Is it possible to insert a menu item, a check menu, or a radio menu item into another menu item?
A: Introduction: Although the menu items used in the preceding examples are every day, JavaFX specifies...
Q: 2) What parameters are passed in this web string and what dynamic language do you think is being use...
A: The type of language is identified using the file extension we have Here, we are trying to load inde...
Q: ite algorithm and draw a flow chart to develop a simple calculator that perform addition, subtractio...
A: Lets see the solution.
Q: Given a list of n positive integers, show that there must two of these integers whose difference is ...
A: As per the code asked, from a list of n positive integers, show that there must two of these integer...
Q: There are three ways to pass arguments to parameters in a function. List them. Python.
A: Following is the all possible ways to pass arguments to parameters in a function in python. 1. Way I...
Q: Unlike most other PC operating systems, the Mac OS stores a large portion of the operating system in...
A: The answer is given in the below step
Q: Express the switching circuit into binary logic notation(boolean expression) and contruct logic diag...
A: S1 OR S2 denotes And Condition are S3 OR S1' denotes by
Q: 1. Write a Java program to determine the answers to the following: a. The squre of 30 ...
A: Since you have asked multiple questions, we will solve the first question for you. If you want any s...
Q: Why is studying ICT important in today's society?
A:
Q: A number of key elements, such as cost, time, scalability, and sustainability, are taken into accoun...
A: Introduction: It is possible to think of network infrastructure as a collection of interconnected co...
Q: Each cloud provider has a product blueprint related to Big Data. Name and explain just one of the a...
A: what is Cloud Computing technique: The term cloud computing is the delivery of computing services ...
Q: How would the class DD be created?
A: There are three interfaces AA , BB and CC. To implement multiple interfaces in java the syntax is ...
Q: When it comes to computer software, operating systems (OSs) rank first. A variety of operating syste...
A: Introduction: An operating system (OS) is a kind of system software that is used to manage computer ...
Q: Write JavaScript codes to validate a name text field so that when a user submits the form with the n...
A: function validateform() { var name = document.myform.name.value; var Regex =...
Q: In this c# program please provide the height (feet and inches) in this program and please show the p...
A: In this question, we are asked to modify the code to that user can able to add height and calculate ...
Q: 2. What is the bandwidth of a signal that can be decomposed into five sine waves with frequencies at...
A: The answer for the given question is as follows.
Q: PROBLEM STATEMENT: In late 1990's, the Department of Education started to get concern about the heal...
A: Your C# code is below with an output.
Q: MATLAB When having a two-dimensional lattice, in lexocographic order I need to be able to move arou...
A: Code: K = 16; h = sqrt(K); lex=zeros(h,h); iup=zeros(1,K); idn=zeros(1,K); x=zeros(1,K...
Q: Why compilers sometimes change the order of executions of the assembly instructions? Give one exampl...
A: compiler: Compilers are used because computer can't understand directly source code . It will only ...
Q: Explain why CSMA/CD requires a constraint on frame size in order to function properly and what the b...
A: Find the answer given as below :
Q: If you want to provide Power BI Services on your own, "in-house" server, which Power BI product shou...
A: Power BI Report Server is an on-premises report server that includes the web site for viewing and ma...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Create a stack-based program which computes: 7 & (9 | 8). Your answer should include an illustration which shows the state of the stack after each instruction and show the workings of all the calculations that are required.A program stack is to use 800 h bytes and SS= 0300 h, A = 1234 h and B = 6AB3 h. Shows the contents of the stack, stack pointer, and physical address using appropriate diagram after the instruction PUSH BXConsider your stack contains two parameters A and C each of 4 Bytes. Give an instruction that will be used to empty the stack after execution of your main program.
- SPIM: 1.Create a program (SPIM) that can find the values of a function f(a,b) =a+b using stack and the jump and link instruction. (i.e. a=2, b=3)In 8086, instruction queue is a part of _____. a. neither EU nor BIU b. BIU c. both EU and BIU d. EUDesigning stack structures, accumulator architectural designs, and general-purpose register architectures are all possibilities. Explain the distinctions between these options and provide examples of instances in which one could be preferable to the other.
- Microprocessors Fill in the following blanks with appropriate answers 4. If there is a carry from lowest nibble during addition, …………. flag sets.5. …………. register is used as a default counter in case of string and loop instructions.6. In PUSH instruction, after each execution of the instruction, the stack pointer isMake a distinction between the Code Segment, the Data Segment, and the Stack Segment. Then, for each segment, determine the registers combination that was utilized to address the data objects in each segment.Hi there, any help with the following would be greatly appreciated. Context in the image:Assume a register-based protocol for the function call. Show how this is achieved. You can assume– call-by-value;– variable v is stored in register $s0;– variable f is stored in register $s1.Explain if a stack frame is required, and justify your answer.
- In MIPS, the stack pointer is manipulated using the instruction addiu $sp, $sp, XX where "XX" is a number that may be positive or negative. If we need to reserve enough room on the stack for 14 integers in addition to the $ra register, what is the value of XX?Explain the concept of dynamic multithreading in processor architecture and how it differs from static multithreading.Explain the Register stack organization of 32 locations of the stack (0 to 31 ). take the initial value of the stack pointer is SP = 09 in Hex. Explain the following push and pop instructions through the Register stack organization diagram.(1) PUSH R2 WHERE R2 = XX in Hex(2) POP R1 WHERE R1 = (XX + 5 ) in Hex where XX is your class roll no , for example roll no 64 is having the data in R2 = 64 Hex and R1=( 64+5 = 69 Hex)

