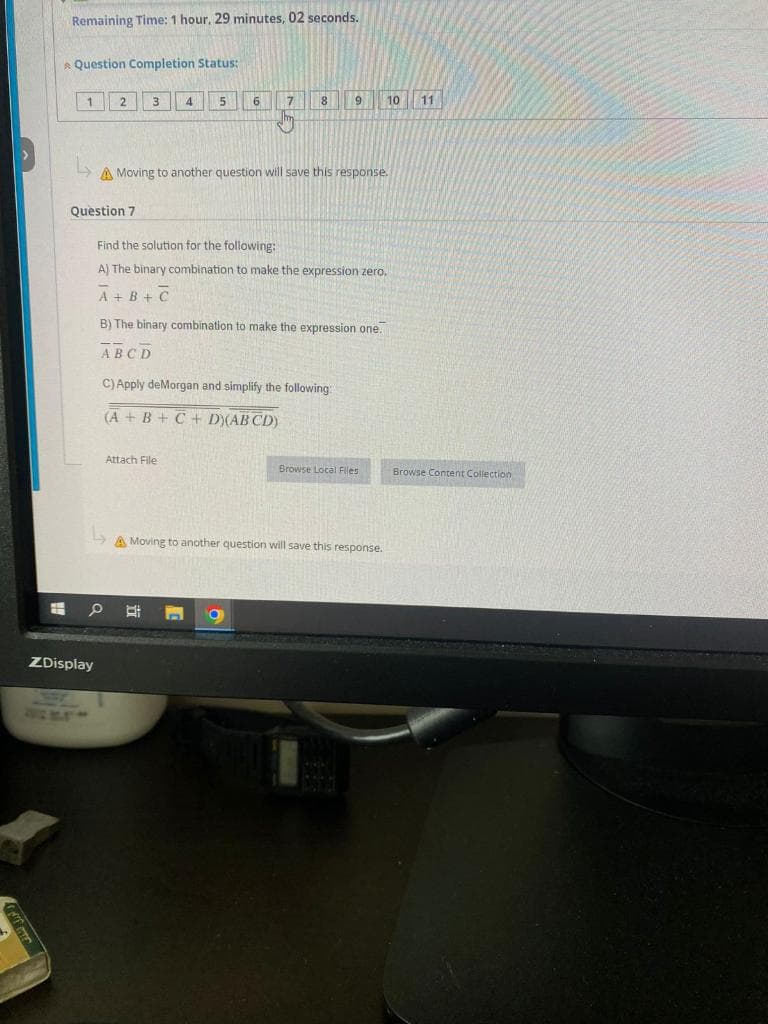
A) The binary combination to make the expression zero. A+B+C
Q: Question 21 The ________ instruction, works like an assignment statement Group of answer choices…
A: The solution is given below with explanations
Q: Python code Use input data from input file Output the results in an output file You will use…
A: We have to create a program that reads prefix expressions from a text file and converts them into…
Q: Which kind of firewall configuration is used by the most companies today? Why? Explain.
A: A firewall is a security system in network that provides threat protection by monitoring and…
Q: Assume that EBX and ECX have the following values EBX: FF FF FF 75 ECX: 00 00 01 A2 After the…
A: Question 13: ADD EBX, ECX ; this instruction add the content of EBX and ECX and stored…
Q: e standards for mobile communication that CELLULAR CONCEPT establishe
A: Describe the standards for mobile communication that CELLULAR CONCEPT established.
Q: An informative essay about the role of networking in IT growth would be a great assignment.
A: Introduction: Write an essay on networking's role in information technology growth. IT helps…
Q: Consider a text corpus consisting of N tokens of d distinct words and the number of times each…
A: Introduction: The question asks to compute Laplace smoothed estimates of word probabilities for a…
Q: Write Algorithm to Decision-making for a wumpus hunter using influence maps. Wumpus-Hunter-React(v)…
A: To make decisions for a wumpus hunter using influence maps, we can follow the below algorithm:
Q: Discuss the benefits and drawbacks of cloud storage. Can you name a few companies that offer…
A: Storage of clods putting data in the cloud we may access data in the cloud without needing any…
Q: What scenarios do you foresee where tacacs+ might be preferable than RADIUS or Kerberos?
A: Introduction: TACACS+ (Terminal Access Controller Access Control System Plus), RADIUS (Remote…
Q: When you say "scalability in the cloud," what do you mean exactly? Isn't it one of the biggest…
A: In this question, it is asked what is the concept of scalability of cloud computing. And if it is…
Q: Question 38 The number of bits in ECX register are __________ Group of answer choices 32 16 8 none…
A: According to Bartleby Guidelines we need to answer only one question so I have answered first…
Q: How does online anonymity affect the flow of traffic
A: Online anonymity can have both positive and negative effects on the flow of traffic.
Q: Why do you think Firewall rules are helpful?
A: Introduction: The advantages of a firewall are innumerable. Explanation: 1) Network traffic…
Q: In Division Nim, the heap cannot be divided into equal halves. Factor Division Nim relaxes this…
A: Solution: Here is the complete game tree for Factor Division Nim with seven matches: Each node…
Q: To what extent does networking play a role in IT?
A: Networking is a crucial aspect of information technology (IT) that allows different devices,…
Q: A user is going to process an unspecified quantity of numbers. The desired result is to have the…
A: Sorting numbers from smallest to largest is a common activity when processing an unknown number of…
Q: (-3,0) 1 (5,7) Diagram of a rectangle defined by lower left and upper right points. The distance…
A: Please refer to the following steps for the complete solution to the problem above.
Q: USING SIMPLE JAVA CODE TAKE GIVEN CODE AND MODIFY MODIFY GIVEN CODE USING JAVA RECURSIVE ACTION DO…
A: In Java, RecursiveAction and RecursiveTask are classes provided by the java.util.concurrent package…
Q: How has the state of computer security changed over time
A: INTRODUCTION: Computer security, often known as cybersecurity, safeguards computer systems and data…
Q: Now that you have done your research, explain your understanding of the data breach that happened at…
A: - We can solve the first three problems only as per our restrictions. Kindly post the remaining…
Q: Several users are having login issues after a recent password change. A call concerning this problem…
A: Please find the answer below:
Q: We have discussed two data structures -- arrays and array lists. Both can be used to store multiple…
A: First lets understand arrays and arraylists: array : is a fixed size data structure. Size of array…
Q: Is there a paper that could be published regarding the value of IT networking?
A: Introduction: Businesses benefit from information technology (IT) by being able to work more…
Q: Can you explain what "Inverse ARP" means?
A: An Inverse Address Resolution Protocol, or Inverse ARP, is another name for this. Inverse ARP is a…
Q: Is biometric authentication a method of ensuring privacy and security? Discuss
A: Here is your solution -
Q: How does data stewardship fit into a data governance program, and what are the most crucial parts of…
A: Introduction: Data stewardship refers to the procedures necessary to ensure that data is accurate,…
Q: What concrete examples can you provide of how virtual servers and services are really put to use?
A: Virtual servers should emulate dedicated servers. Multiple virtual servers on one server can…
Q: Write Algorithm to Decision-making for a wumpus hunter using influence maps. Wumpus-Hunter-React(v)…
A: In this algorithm, we first set a threshold for shooting an arrow. We then initialize the influence…
Q: In a multi-system environment, how can we ensure that no two systems' signals interfere with one…
A: The back-off method delays the first 11 tries by 0 to 2 time units and 12 to 16 by 0 to 1023. The…
Q: 94 47 72 82 84 Is this binary tree a valid red-black tree? Select all that apply. Yes No, root node…
A: According to the information given:- We haev to choose the correct option to satisfy the statement.
Q: Consider exploring options for mining social media for data.
A: Mining social media for data has become an increasingly popular way for businesses and researchers…
Q: In order to increase the sign length of an unsigned integer from 8 to 16 bits, the most significant…
A: Option is the response that is appropriate for the questions ("False") EXPLANATION When the signed…
Q: PYTHON/JUPYTER NOTEBOOKS given the attached fourier data : # Measurements of fourier data…
A: Jupyter Notebook is a web-based interactive computing platform that allows you to create and share…
Q: Do you have any advice on the management of firewalls? Explain.
A: A firewall is a type of network security system that keeps an eye on and regulates incoming and…
Q: Explain how you would link AIT's Sea View and Knowledge City campuses, taking into account their…
A: AIT (Asian Institute of Technology) has two campuses, the Sea View campus and the Knowledge City…
Q: 2 Write a program that will have two priority queues with the following values: {"George", "Jim",…
A: Create the first priority queue pq1 with the values: ("George", "Jim", "John", "Blake", "Kevin",…
Q: Do you think you have enough knowledge to create an essay about the role of networking in the…
A: Given: Write an essay on the value of networking in the advancement of information technology.
Q: using R please provide the code needed to run a hypothesis test using the iris data set, conduct a…
A: Answer is
Q: 1. Explain why using StringBuffer (or StringBuilder) objects is preferred over String objects when…
A: Introduction: In Java, handling strings is a crucial aspect of programming, as they are used in…
Q: hester A 1 2 3 4 5 Question #4 Multiple Choice A shipping company wants to use an algorithm to…
A: To solve this problem, shipping companies may need to use specialized optimization algorithms to…
Q: A complex number is a number of the form a + bi, whereby a and b are constants, and i is a special…
A: Define a function called "add_complex_numbers" that takes two tuples as inputs Extract the real and…
Q: What, in your opinion, sets a hacktivist apart from a cyberterrorist? Is it a crime of war for a…
A: Now, let's take a closer look at the reply. Hacktivism is the politically-motivated, peaceful use of…
Q: Doing research on the significance of networking to the evolution of IT?
A: Introduction: Information Technology (IT) has rapidly evolved in the past few decades, and one of…
Q: Provide your answers based on your chosen reading material(s) such as books, magazines, and journals…
A: According to Bartleby Guidelines we need to answer only one question so I have answered first…
Q: What makes mobile cloud computing unique from other portable computer solutions? Tell me about M…
A: cellular computing: Simple mobile computing refers to the use of mobile devices for computing tasks…
Q: Should a paper be published on the topic, given the importance of networking to IT?
A: The value of networking in information technology: Information is the foundation of persuasive…
Q: Please implement a B+ tree in Java
A: To implement a B+ tree in Java
Q: Is there a reliable way to know whether you've discovered useful information online?
A: Introduction: In today's digital age, the internet has become an indispensable tool for acquiring…
Q: PLEASE DO NOT COPY THE CURRENT SOLUTION ON BARTLEBY THIS REQUIRES A DIFFERENT SOLUTION. A database…
A: The task requires creating triggers in a database to handle the "created_at" and "updated_at"…
Step by step
Solved in 3 steps

- 3a- Please I want solution of all question's subparts by typing. Thanksplease solve the question new solution, don't copy other solutions in questions bank c++ In this task, you are required to write a code that converts an Octal number into its equivalent Decimal value or vice versa. The user first selects the conversion choice by inserting 1 or 2. Choice 1 is followed by inserting an Octal integer and getting its Decimal equivalent value as an output. Choice 2 requires inserting a Decimal integer and prints out its Octal equivalent. The Octal numeral system, is the base-8 number system, and uses the digits 0 to 7, that is to say 10 octal represents 8 Decimal and 100 octal represents 64 Decimal. Convertion from an Octal integer into Decimal In the Decimal system, each number is the digit multiplied by 10 to the power of its location (starting from 0). For example: 74 decimal = 7 x 10^1 + 4 x 10^0 1252 decimal = 1 x 10^3 + 2 x 10^2 + 5 x 10^1 + 2 x 10^0 each number is the digit multiplied by 8 to the power of its location (starting from 0).…18. Tom and Jerry opened a new lawn service. They provide three types of services: mowing, fertilizing, and planting trees. The cost of mowing is $35.00 per 5,000 square yards, fertilizing is $30.00 per application, and planting a tree is $50.00. Write an algorithm that prompts the user to enter the area of the lawn, the number of fertilizing applications, and the number of trees to be planted. The algorithm then determines the billing amount. (Assume that the user orders all three services.) (9)
- Determine whether the following argument is valid or invalid. Include a truth table and a few words explaining why the truth table shows validity or invalidity. Use the space provided below to draw the truth table If Hugo is a physics major or if Hugo is a math major, then he needs to take calculus. Hugo needs to take calculus or Hugo is a math major. Therefore, Hugo is a physics major or Hugo is a math major.Please code in OOP C++, show example output to see if no errorsCrossword Puzzles An unlabeled crossword is given to you as an N by M grid (3 <= N <= 50, 3 <= M <= 50). Some cells will be clear (typically colored white) and some cells will be blocked (typically colored black). Given this layout, clue numbering is a simple process which follows two logical Steps: Step 1: We determine if a each cell begins a horizontal or vertical clue. If a cell begins a horizontal clue, it must be clear, its neighboring cell to the left must be blocked or outside the crossword grid, and the two cells on its right must be clear (that is, a horizontal clue can only represent a word of 3 or more characters). The rules for a cell beginning a vertical clue are analogous: the cell above must be blocked or outside the grid, and the two cells below must be clear. Step 2: We assign a number to each cell that begins a clue. Cells are assigned numbers sequentially starting with 1 in the same order that…units = int(input(" Please enter Number of Units you Consumed : ")) if(units < 50): amount = units * 2.60 surcharge = 25 elif(units <= 100): amount = 130 + ((units - 50) * 3.25) surcharge = 35 elif(units <= 200): amount = 130 + 162.50 + ((units - 100) * 5.26) surcharge = 45 else: amount = 130 + 162.50 + 526 + ((units - 200) * 8.45) surcharge = 75 total = amount + surcharge print("\nElectricity Bill = %.2f" %total) Find the error and resolve the problem.
- R studio : profit margin for each month - equals to profit a after tax divided by revenue profit.margin <- round(profit_after_tax/revenue, 2)*100 profit.margin Result: 12 18 -30 -22 -5 63 50 28 23 -11 4 53 How to change the results based on the note: All results need to be presented as vectors. Results for dollar values need to be calculated with $0.01 precision, but need to be presented in Units of $1,000 (i.e. 1k) with no decimal points. Results for the profit margin ratio need to be presented in units of % with no decimal points. Note: You colleague has warned you that it is okay for tax for any given month to be negative (in accounting terms, negative tax translates into a deferred tax asset).Please write a R code for the following questiondictionaries = [] dictionaries.append({"First":"Bob", "Last":"Jones"}) dictionaries.append({"First":"Harpreet", "Last":"Kaur"}) dictionaries.append({"First":"Mohamad", "Last":"Argani"}) for i in range(0, len(dictionaries)): print(dictionaries[i]['First']) ************************************************* please modity the above code to "Add an ‘if’ statement(s) to the loop in your solution in Exercise 7 to only show the full name if the first name is “Bob” or if the last name is “Kaur”.
- This Code print the first occurrences of x, Please Modify the code to print the last occurrences of x and print how many times it exists? ( with explanation for each line if possible) many thanks.Correct answer will be upvoted else Multiple Downvoted. Computer science. You are given two positive integer groupings a1,… ,an and b1,… ,bm. For each j=1,… ,m track down the best normal divisor of a1+bj,… ,an+bj. Input :The primary line contains two integers n and m (1≤n,m≤2⋅105). The subsequent line contains n integers a1,… ,an (1≤ai≤1018). The third line contains m integers b1,… ,bm (1≤bj≤1018). Output :Print m integers. The j-th of them ought to be equivalent to GCD(a1+bj,… ,an+bj).q -> (p ^ r) What is the truth value of the following statement when p is false, q is false and r is true?







