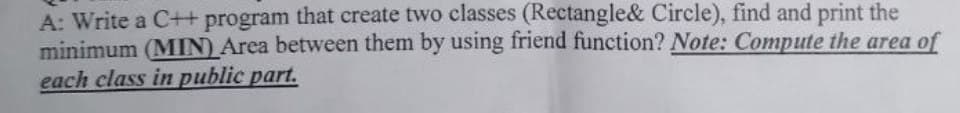
A: Write a C++ program that create two classes (Rectangle& Circle), find and print the minimum (MIN) Area between them by using friend function? Note: Compute the area of each class in public part.
Q: What decisions must be taken in order to define database field requirements?
A: The database has its own "data dictionary," which is comprised of the field requirements. Within the…
Q: What does a Repository and Data Dictionary mean in terms of computers?
A: Given: What is a Contrast Repository and Data Dictionary in computing?
Q: Would you mind defining and explaining cloud scalability? What elements influence the cloud's…
A: Answer is
Q: Describe some strategies for session theft. Can anything be done to stop this from occurring?
A: Session Hijacking is an attack that enables unauthorized access to authorized session connections.…
Q: How may interface designers do a hierarchical task analysis? Describe the seven-step procedure
A: Introduction: Hierarchical Task Analysis: This methodical, objective technique helps users define…
Q: There are various techniques to authenticate messages.
A: The techniques of message authentication are discussed into below step
Q: A. test plan B. 【】 Set the correct order of the process of testing D. C. test requirement E. test…
A: The above question that is the correct order of testing is answered below step
Q: Should the IT director answer to the company's president?
A: An IT director, or chief information officer, is responsible for putting up a corporate strategy,…
Q: Computer science vocabulary includes phrases like Data Dictionary and Contrast Repository.
A: An info dictionary :- A database, information system, or research project's data items are listed…
Q: Write a report outlining how the system could be improved to render decisions faster.
A: Four Simple Steps to Boost System Performance Remove Cache. Clear your cache sometimes, then restart…
Q: What decisions must be taken in order to define database field requirements?
A: introduction: In the first step of the process, the following are some of the considerations that…
Q: When and how does a compiler create an Object() function by default in native code?
A: If we don't specify our own Object(): [native code] function, the C++ compiler will create a default…
Q: oduces an exhaustive list of all the files and their perm
A: Introduction: Below describe the command produces an exhaustive list of all the files and their…
Q: Is the security of the cloud endangered by a data breach? The following are some potential solutions…
A: Introduction: Information theft, a ransomware, phishing, password guessing, viruses, malware,…
Q: 5. Complete the arithmetic on these signed numbers. Convert the result to decimal. The computer is…
A: Below I have provided the solution to the given signed numbers.
Q: What does "predictive analysis" mean? Give a use example f
A: Predictive analytics is the use of data to predict future trends and events. It uses historical data…
Q: What traits distinguish NoSQL databases?
A: Given: Dear student we need to explain about , What traits distinguish NoSQL databases.
Q: 1. Create a program that will display the following output. 7654321 654321 54321 4321 321 21 1
A: Note: As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: Xero and Zoho Books are two other small business accounting applications that can support the import…
A: Solution: If you are looking for an accounting application to support the import of transactions…
Q: 2. There are, by hypothesis, infinite number bases, but in computing we use hexadecimal, octal and…
A: The complete answer is below:
Q: 1. Front-Running Detector Front-running is defined as trading a stock or another financial asset by…
A: Option (A) is correct. "Front running" is an illegal practice in which broker/specialists trade…
Q: How and to what extent is physical security distinct from other forms of security? We must be aware…
A: Physical security is the protection of personnel, hardware, software, networks, and data from…
Q: Help required! What advice would you give someone deciding between Linux and Windows?
A: INTRODUCTION: Unix. A series of open-source Unix-like operating systems known as Linux is based on…
Q: How probable do you believe it is that a data breach will have a future impact on cloud security? Is…
A: Given: Successive organisations are confident in their efforts to prevent data breaches and aware of…
Q: What advantages do both vertical and horizontal partitioning offer?
A: The following is a list of benefits that may be gained from both vertical and horizontal…
Q: Let L be the set of strings (N, w) where N is an NFA that accepts the string w. Pick all that apply.…
A: Let's discuss why each option correct or incorrect.
Q: Refer to the given brief system descriptoin and answer the questions (a-c) below using your…
A: Below I have provided the solution to the given subpart question
Q: What substitutions are there for message authentication?
A: There are many techniques that can be alternative for message based authentication , Message based…
Q: What are some restrictions on the Tor network?
A: Firstly, it doesn’t offer cease-to-cease encryption. TOR encrypts your information whilst it enters…
Q: Can the kernel components of a standard operating system be summed up in a single sentence?
A: The main processing component of an operating system is called the kernel (OS) for a computer. It is…
Q: What is the general name for the AMD-created Hyper-Transport feature of CPUs? ?
A: Answer: HT was AMD's bus for connecting multi-socket computer systems into a single coherent memory…
Q: What is a file manager? Describe Windows Explorer. Include a few file and storage places. The…
A: File Manager: Every file management operation is supported (open, search, navigate directory, copy…
Q: 6 4 7 1 8 6 4 1 7 8 6 4
A: Explanation: 1) The most straightforward sorting method is Bubble Sort, which repeatedly switches…
Q: Does data encoding always make more sense than data encryption? When is it necessary to encrypt…
A: Data encoding is a process of changing the data into another format. It is reversible process that…
Q: Is there a danger associated with Internet usage?
A: Start: The loss of data is the cloud computing practise that poses the greatest potential threat to…
Q: 1)A tuple is a named column of a relation. True or alse 2)Each attribute in a relation has a…
A: Ans :1 A tuple is a row of a relation. Ans :2 In a relation has a distinct name. Ans: 3 The degree…
Q: What processes does intrusion detection software employ?
A: Introduction: An IDS monitors a network or system for malicious activities or policy breaches. Any…
Q: Consider that a new company hires you as an IT architect. The CEO of the company instructed your…
A: Introduction: The active acceptance approach, which includes the creation of a backup plan, is…
Q: What are the most effective cloud-based data backup procedures?
A: Answer the above question are as follows
Q: Exist any tools for database maintenance and data entry that maintain the integrity of the data?
A: According to the information given:- We have to define the database maintenance and data entry that…
Q: How would you define information and communications technology (ICT) in light of everything that you…
A: Information and communication technologies (ICT) is defined as a diverse set of technological tools…
Q: How are sessions susceptible to being hijacked? Can anything be done to stop this from occurring?
A: Session Hijacking: IP spoofing, the most popular technique for session hijacking, involves an…
Q: This task is solved in Python. 3. Write a function build_my_graph2 () that: a) creates the following…
A: Here is the python3 code: See below step for code.
Q: Consider the potential and security risks of cloud computing. When examining the hazards and risks…
A: Answer:
Q: In order to defend and secure networks, firewalls are crucial. Remember to define the term and…
A: It is necessary to provide an explanation of the function of the firewall in terms of network…
Q: Client data was stolen as a consequence of database hacking at several well-known businesses.…
A: The solution to the given question is: EXPLANATION Database. Security is important because it is a…
Q: What are the ramifications of a data breach on the security of the cloud? In your perspective, what…
A: Introduction: A data breach occurs when private information is made accessible to an uninvited…
Q: How can I get access to Application Software? The most effective technique to convey your point is…
A: Introduction: Application software is made to assist with a wide range of functions, including…
Q: It is important to recognize and quickly describe the many information systems-related problems that…
A: Introduction: Numerous countries now use global information systems. global issues relating to…
Q: Comparisons between a parallel simulation environment and a fully integrated test facility are…
A: Test data is the auditor, which is sending fictitious data to the client's system in order to verify…
Step by step
Solved in 3 steps with 1 images

- Write a Number class that holds a double, and add overloaded operators for +, –, *, /, and assignment. Choose the return values for these functions so that expressions can be chained together, and for efficiency. Write an automatic type conversion operator int( ). Please submit code inDoes a friend function violate the data hiding? Explain briefly. Write a program to swap variables of two classes using friend function. C++I need help Implement the operators for class Login and class Person. Please help me out
- PLZ help with the following: IN JAVA Given the following code (where the function FunTest() and the main method are inside one class in the same file where classes X, Y and Z are), predict what is the output?Write a program to swap the values of private data members of a class named as class_1 and class_2 by using the concept of friend classes.Reuse your Car class . In a main, build an object of that class, and print out the object using System.out.println(). Notice that this simply reports the memory address of the object in question, and we’d like to do something more useful. To replace (or override) the toString (or equals) function. Now, build a toString function that prints out the make, model, and odometer reading for a vehicle object. public class Car { //instance variables private int odometer; private String make; private String model; //overloading //constructors public Car(int odometer,String make, String model) { this.odometer = odometer; this.make = make; this.model = model; } public Car(String make, String model) { this.make = make; this.model = model; } public Car(String make) { this.make = make; } /* *getter & setter methods */ public int getOdometer() { return odometer; } public void…
- Writing in C++, using <iostream>, using (Pointers), (Concrete and abstract class), (Overloaded functions and constructors), (Inheritance), (Polymorphism), Write a program that user can add lists of ordered food, then user give program information if ordered food delivered, then program shows inventory(delivered food) and food that did not delivered yet.Write the definitions of the functions to implement the operations for the class dayType as defined in Programming. Also, write a program to test various operations on this class.Write a program to add members of two different classes using friend Function. Problem: Design: Code: Output:
- Q3: Write a program in C++ using OOP to create a class (A) , that contain integer number(x) , contain the iilnction (FACT) to calculate the factorial of (x!)and create a class (B) , that contain integer number (n ) , contain the functions (POWER),to calculate ( .xü).-Illen create a Class (C) , with public visibility mode inherit from class (A)and public visibility mode inherit from class (B),contain the tunction that findGiven the Class Definition for ClockType discussed extensively in class, write what would have to be added to the IMPLEMENTATION FILE for the Class ClockType to overload the “= =”, i.e., the comparison “equal-equal sign,” here: That is, write the FULL FUNCTION DEFINITION for THE FUNCTION associated with Class ClockType to overload the “= =” remembering the private members are: b) int hr; // that contains the hours int min; // that contains the minutes int sec; // that contains the secondsWrite a code in c++ to calculate area of triangle (A=1/2 ???ℎ? ∗ ????ℎ). Take objects of class and pass static value to set parameter. By overloading binary operator “_”to subtract the values of two objects. At the end calculate area of triangle by using these value and display it



