an ER-Diagram for a University database. A university consists departments. Each department offers several courses. A fe s make up each course. Students enroll in a particular course ar odules towards the completion of that course. Each module
an ER-Diagram for a University database. A university consists departments. Each department offers several courses. A fe s make up each course. Students enroll in a particular course ar odules towards the completion of that course. Each module
Principles of Information Systems (MindTap Course List)
12th Edition
ISBN:9781285867168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter5: Database Systems And Applications
Section: Chapter Questions
Problem 4PSE: Using a graphics program, develop an entity-relationship diagram for a database application for an...
Related questions
Question
Need Both questions asap.
And do it correctly and neatly and I'll surely give your question an upvote.
Thank you so much.
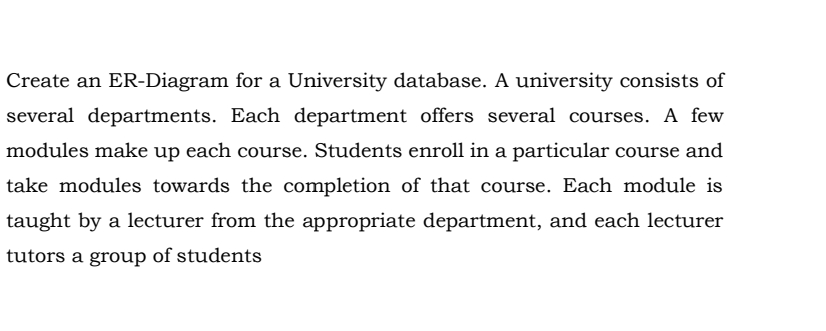
Transcribed Image Text:Create an ER-Diagram for a University database. A university consists of
several departments. Each department offers several courses. A few
modules make up each course. Students enroll in a particular course and
take modules towards the completion of that course. Each module is
taught by a lecturer from the appropriate department, and each lecturer
tutors a group of students
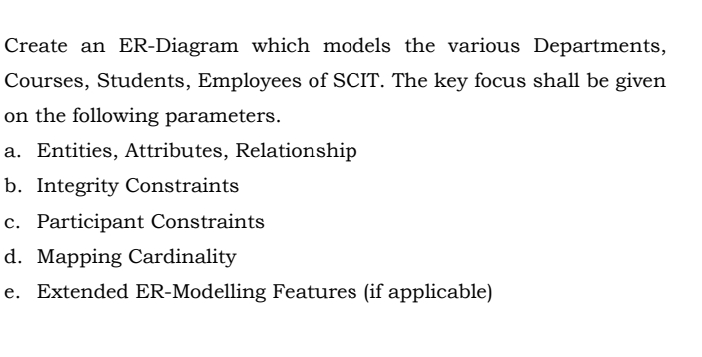
Transcribed Image Text:Create an ER-Diagram which models the various Departments,
Courses, Students, Employees of SCIT. The key focus shall be given
on the following parameters.
a. Entities, Attributes, Relationship
b. Integrity Constraints
c. Participant Constraints
d. Mapping Cardinality
e. Extended ER-Modelling Features (if applicable)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning