and FnFn-1+Fn-2 for n > 1 In other words, each number is the sum of the two previous numbers in the sequence. The not gata J Eik. Jo platic
and FnFn-1+Fn-2 for n > 1 In other words, each number is the sum of the two previous numbers in the sequence. The not gata J Eik. Jo platic
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 21PE
Related questions
Question
.
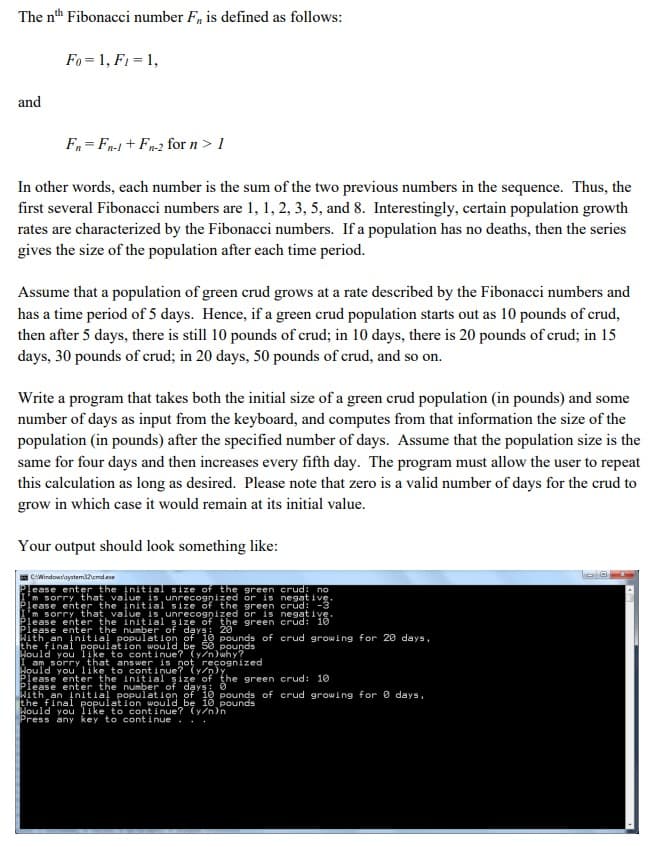
Transcribed Image Text:The nth Fibonacci number F, is defined as follows:
and
Fo= 1, F1 = 1,
Fn=Fn-1 + Fn-2 for n > 1
In other words, each number is the sum of the two previous numbers in the sequence. Thus, the
first several Fibonacci numbers are 1, 1, 2, 3, 5, and 8. Interestingly, certain population growth
rates are characterized by the Fibonacci numbers. If a population has no deaths, then the series
gives the size of the population after each time period.
Assume that a population of green crud grows at a rate described by the Fibonacci numbers and
has a time period of 5 days. Hence, if a green crud population starts out as 10 pounds of crud,
then after 5 days, there is still 10 pounds of crud; in 10 days, there is 20 pounds of crud; in 15
days, 30 pounds of crud; in 20 days, 50 pounds of crud, and so on.
Write a program that takes both the initial size of a green crud population (in pounds) and some
number of days as input from the keyboard, and computes from that information the size of the
population (in pounds) after the specified number of days. Assume that the population size is the
same for four days and then increases every fifth day. The program must allow the user to repeat
this calculation as long as desired. Please note that zero is a valid number of days for the crud to
grow in which case it would remain at its initial value.
Your output should look something like:
C:\Windows\system32cmd.exe
Please enter the initial size of the green crud: no
'm sorry, that, value, is unrecognized or is negative.
Please enter the initial size of the green crud: -3
'm sorry, that, value is unrecognized or is negative.
Please enter the initial size of the green crud: 10
Please enter the number of days: 20
With an initial population of 10 pounds of crud growing for 20 days,
the final population would 50 pounds
continue? (y/n)why?
am that is
you
to
Bould you like to continue? ognized
15
initial size of the green crud: 10
Please enter the number of days
With an initial population of 10 pounds of crud growing for 0 days,
the final population would be 10 pounds
Hould you like to continue? (y/n)n
Press any key to continue...
1-0
A
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr