Answer the following questions: • Write the precondition axioms for the actions. • Write the effect axioms for the actions. • Show how successor state axioms for the fluents would be derived from these effect axioms. Argue that the successor state axioms are not logically entailed by the effect axioms by briefly describing an interpretation where the effect axioms are satisfied but the successor state ones are not. • Show how frame axioms are logically entailed by the successor state axioms.
Answer the following questions: • Write the precondition axioms for the actions. • Write the effect axioms for the actions. • Show how successor state axioms for the fluents would be derived from these effect axioms. Argue that the successor state axioms are not logically entailed by the effect axioms by briefly describing an interpretation where the effect axioms are satisfied but the successor state ones are not. • Show how frame axioms are logically entailed by the successor state axioms.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter10: Classes And Data Abstraction
Section: Chapter Questions
Problem 19PE
Related questions
Question
100%
Transcribed Image Text:A
B
C
Ꭰ
F
d
E
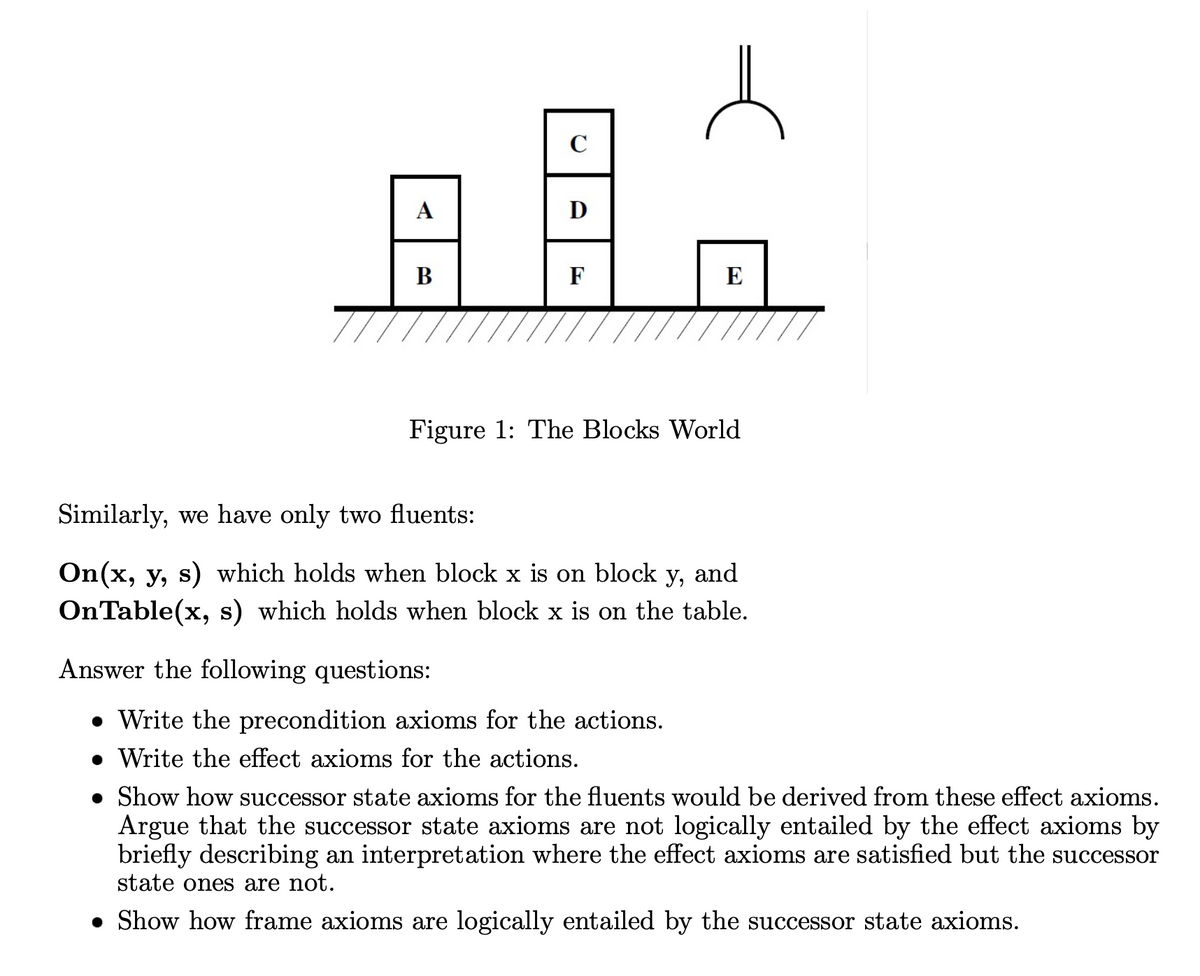
Figure 1: The Blocks World
Answer the following questions:
• Write the precondition axioms for the actions.
.Write the effect axioms for the actions.
Similarly, we have only two fluents:
On(x, y, s) which holds when block x is on block y, and
On Table(x, s) which holds when block x is on the table.
• Show how successor state axioms for the fluents would be derived from these effect axioms.
Argue that the successor state axioms are not logically entailed by the effect axioms by
briefly describing an interpretation where the effect axioms are satisfied but the successor
state ones are not.
• Show how frame axioms are logically entailed by the successor state axioms.
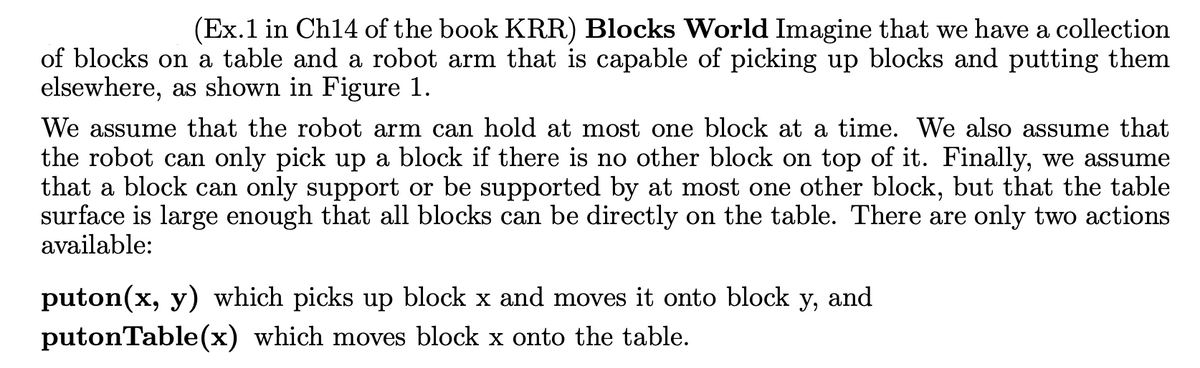
Transcribed Image Text:(Ex. 1 in Ch14 of the book KRR) Blocks World Imagine that we have a collection
of blocks on a table and a robot arm that is capable of picking up blocks and putting them
elsewhere, as shown in Figure 1.
We assume that the robot arm can hold at most one block at a time. We also assume that
the robot can only pick up a block if there is no other block on top of it. Finally, we assume
that a block can only support or be supported by at most one other block, but that the table
surface is large enough that all blocks can be directly on the table. There are only two actions
available:
puton(x, y) which picks up block x and moves it onto block y, and
putonTable(x) which moves block x onto the table.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning