C++. Explanation please.
Q: Assume that the Kerberos protocol is used by an organization's authentication system. Security and…
A: Given: Kerberos is a verification protocol for computer networks that is based on the concept of…
Q: Investigate the similarities and differences between an assembler, a compiler, and an interpreter.
A: Compiler :It is software that translates high-level language applications into machine language.…
Q: Computing at the quantum level and block chains are two topics that are timely and should be…
A: Given: Even more exciting is the fact that the technology behind blockchain is gaining popularity at…
Q: Explain what you mean by distributed systems. Please explain why the definition of distributed…
A: The above question that is mean by distributed system and defination of distributed systems has so…
Q: In an entity-relationship diagram, what does cardinality mean? 1:The data is saved concerning a…
A: In an entity-relationship diagram, what does cardinality mean? 1:The data is saved concerning a…
Q: Can you provide instances of asynchronous, synchronous, and isochronous connections and explain…
A: Asynchronous Connection:- sign communication, data is transferred from one end to the other.…
Q: DRaaS: Disaster Recovery as a Service and Razor Technology provide similar services. To what extent…
A: Given: Disaster recovery as a service (Dramas) is a cloud computing service model that allows an…
Q: What precisely does the phrase "quantum computing" refer to, and how does the corresponding process…
A: AT THE QUANTUM LEVEL COMPUTING: Quantum computing is a kind of computer that uses an item's quantum…
Q: Give an explanation of how selective retransmission might be an advantageous expansion of the TCP…
A: Introduction: Step arrow forward to get the answer. Packets are acknowledged cumulatively by the…
Q: What is the correct noun ending for the phrase "computer mice"
A: The plural of computer mouse is mice. In computing, a mouse is a handheld pointing device that…
Q: How do I find the key in caesar cipher using the plaintext
A: The answer is
Q: What precisely does it imply when people talk about a race when they're referring to the typical…
A: Introduction: Primary and foreign keys are the cornerstones of relational database theory. Primary…
Q: Give an example of a synchronous connection and an example of an isochronous connection, and then…
A: The above question is solved in step 2 :-
Q: (3) In maximum mode, 8088 CPU requires the use of the [3] to generate some of the control signals.…
A: According to bartleby guidelines we need to answer only three sub questions so i have answered first…
Q: To transmit the data 1011000 to his friend using hamming code technique. Calculate (i) number of…
A: 1. 4 bits [0,1,0]2. 7, 6, 5, 4, 3, 2, 13. 7 bits4. 10110105. After using the hamming code…
Q: To work in AI and machine learning, what qualifications are required? There are several definitions…
A: Given: Artificial intelligence is a broad subfield of computer science that focuses on the…
Q: A mousepad may be thought of as the plural form of a computer mouse.
A: Given: It is possible that the majority of the technical improvements made today may be attributed…
Q: In its simplest terms, what is the Dynamic Host Configuration Protocol (DHCP), and how does it…
A: Dynamic Host Configuration Protocol: This protocol is abbreviated as DHCP (Dynamic Host…
Q: In an entity-relationship diagram, what does cardinality mean? 1:The data is saved concerning a…
A: Foundation This question was taken from the Database Management System paper that was given in the…
Q: To what standards should a disaster recovery strategy be held?
A: Answer: Identifying key IT systems and networks, prioritising the RTO, and detailing the processes…
Q: How does a quantum computer differ from a normal computer? What challenges must be overcome before…
A: Introduction: Qubits, which can represent both 0 and 1 simultaneously, are used in quantum…
Q: Obtain the 1's and 2's complement of the following binary numbers 1010101, 0111000, 0000001, 10000,…
A: Answer is given below-
Q: What distinguishes traditional computers from their quantum analogues, and how do these differences…
A: Introduction: What sets regular computers different from their quantum counterparts, and how do the…
Q: Create a Visual Basic project to solve for the roots of the quadratic equation -b+√b²-4ac 2a 3…
A:
Q: When a company decides to employ vendor-provided cloud services, what risks does it take on? Either…
A: The risks to employ vendor-provided cloud services are: 1) Security risks at the vendor : Some of…
Q: Acquire a solid understanding of the concept of social networking. What precisely does the word…
A: Intro SOCIAL NETWORKING :- Social Networking is using online social media to interact with friends,…
Q: If you don't provide an adequate response, the experts will downvote your answer. What exactly is…
A: Inspection: The graphic depicts a simplified diagrammatic overview of a software process framework.…
Q: When establishing a disaster recovery strategy, what elements should be taken into account?
A: Introduction: The disaster recovery plan checklist identifies key IT systems and networks,…
Q: What distinguishes traditional computers from their quantum analogues, and how do these differences…
A: In comparison to a traditional computer, there is a significant difference: Binary computers, which…
Q: Is it still feasible to accomplish pipelined execution even if the time it takes to execute pipeline…
A: Pipelining: Pipelining does not aid in the completion of a single project; rather, it aids in the…
Q: What are some of the advantages and disadvantages of using connectionless protocols as opposed to…
A: INTRODUCTION: A connection less protocol is used to illustrate communication between two network…
Q: How to find the susceptibility of your network?
A: Network vulnerabilities: Network vulnerabilities are defects or gaps in hardware, software, or…
Q: Sniffing the network and wiretapping are two of the most common methods for finding out whether…
A: Sniffing is the process of monitoring and capturing all packets that pass through a particular…
Q: Describe four challenges that might arise while merging relationships.
A: Given: With the merging of relationships, four challenges arise, and their resolution is as follows:…
Q: Investigate the similarities and differences between an assembler, a compiler, and an interpreter.
A: THE above question that is similarties between an assembler , a compiler ,and an interpreter is…
Q: How does a quantum computer differ from a normal computer? What challenges must be overcome before…
A: Given: Qubits, which can represent both 0 and 1 at the same time, are used in quantum computing.…
Q: Sniffing the network and wiretapping are two of the most common methods for finding out whether…
A: Introduction: What exactly is Object-Oriented Programming (OOP), and how does it function? Using a…
Q: Give a concise explanation of the benefits and drawbacks of connectionless protocols in comparison…
A: The Answer is in step2
Q: a) Using the following function definition, show how equational reasoning could be used incorrectly…
A: This function isEmpty returns true if the list passed to it is empty, and false otherwise. So, if…
Q: Title: Attributes, Headings and Paragraphs Goal: To apply attributes, headings anc paragraphs in a…
A: Code: <!DOCTYPE html> <html> <head> <title>Attributes,…
Q: What are some of the drawbacks of using symmetric encryption for key management?
A: The Answer start from step-2.
Q: CODE HAS TO BE IN EMU 8086 ASSEMBLY LANGUAGE Write a program to find the maximum number and the…
A: org 0x0100 ;srarting position Arrayd: dw…
Q: In order to work in artificial intelligence and machine learning, what qualifications are necessary?
A: In the given question Machine learning and artificial intelligence are two advanced technologies…
Q: What kind of data would you keep in an entity subtype?
A: Given: A subtype is sub-grouping of the entities that make up an entity type that has significance…
Q: What would you say is the best way to explain the typical synchronisation error known as a race?
A: Given: A race situation is a synchronisation error caused by errors in the operating system's code.…
Q: What is the main difference between composition and aggregation? Provide a concise explanation.
A: Comparison between aggregation and composition.
Q: What would you say is the best way to explain the typical synchronisation error known as a race?
A: The following is an answer to the provided question: A race situation is a synchronization mishap…
Q: In Python, Use the file named numbers.txt numbers.txt ——————- 10 25 36 45 89 42 54 —————— to create…
A:
Q: Write a program to create a file named Exercise13_1.txt if it does not exist. If it does exist,…
A: Answer:
Q: What are some instruments that may be used to disrupt wireless signals?
A: There are wide variety of devices that can disrupt wireless signals. Microwave ovens Fluorescent…
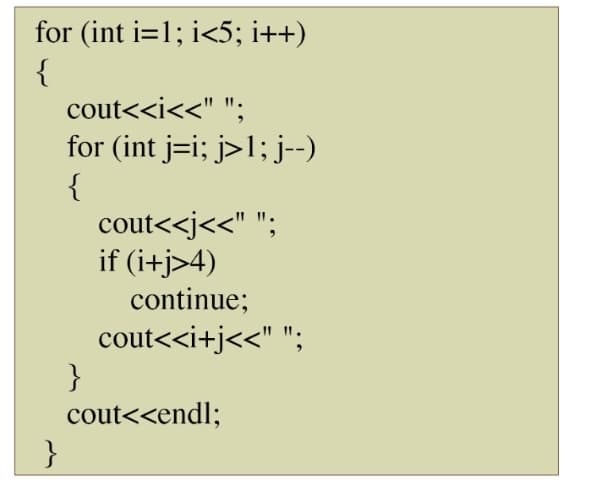
Step by step
Solved in 3 steps with 1 images

- IN HASKELL PROGRAMMING LANGUAGE PLEASE In case you do not know it: the game is played on a 3x3 grid that is initially empty. Two players are playing, by alternatingly making moves. A move by a player places their token (an X for player 1, an O for player 2) into a cell that was empty. We are using algebraic notations for indexing the positions in the board, with A,B,C indexing the columns and 1,2,3 the rows. Specifically, these coordinates would be used in the implementation for moves made by a human player. If the X X O Figure 1: Sample board position same token appears 3 times in any of the three columns, three rows or two main diagonals the game is over and that player wins. If the grid is filled without that happening the game is a draw. For the depicted board, we have Xs in positions C3 and A2, and an O in position B1. It would be O’s turn to make a move; a legal move would be C2, but it is not a good move, because X can force a win by responding A1. O cannot force a win, but…Recursive Exponentiation (using c language) Write a recursive function power(base, exponent) that when invoked returns baseexponent. For example, power(3, 4) = 3 * 3 * 3 * 3. Assume that exponent is an integer greater than or equal to 1. Then, write a demo program that uses the power function and test it out for a number of inputs. Hint: The recursion step would use the relationship baseexponent = base * baseexponent–1 and the terminating condition occurs when exponent is equal to 1 because base1 = baseCalculator.java, to accept an expression as astring in which the operands and operator are separated by zero or more spaces.For example, 3+4 and 3 + 4 are acceptable expressions. Here is a sample run:
- (Coding Language C++) Dynamic Programs Hoskins College offers both curriculum and continuing education courses. Write a program that dynamically tracks these courses using an array of object pointers. Every course (both curriculum and continuing education) has a course id, title, room number, and number of contact hours. A curriculum course has credit hours and tuition rate. Tuition is calculated by multiplying the course's credit hours by tuition rate. A continuing education course has a flat fee (cost). Implement a show() function in every class that displays the data in the object. Part A: Create an inheritance-based collection of classes to represent these different courses. Include code in main to test your work by instantiating objects of the two derived classes. Part B: Modify your program. Remove the objects you created in main to test the classes. Modify the base class so that show() becomes a virtual class. In main, create a single array capable of holding pointers to…Code thisDemonstratic the concept of pointer arithmatic
- A binary operator is an operation that is performed on two operands. For example, addition is a binary operator that adds two operands (e.g., 2 + 4). In the provided UML diagram, all binary operators have two operands and an execute method that performs the appropriate operation on the operands. The AddOperation class should add the two operands. The SubtractOperation class should subtract the two operands. Here is an example of how a binary operator could be used: IBinaryOperator operator = new AddOperator(8, 12);System.out.println(operator.execute()); // should print 20operator.setLeftOperand(18);System.out.println(operation.execute()); // should print 30 crate a Main.java to test your code(C Language) Write a recursive function called DigitCount() that takes a non-negative integer as a parameter and returns the number of digits in the integer. Hint: The digit count increases by 1 whenever the input number is divided by 10.Define the term " pointer constant " .
- Problem Statement: The mathematician Conway imagined a game, called game of life, which considered cells that are susceptible to reproduce, disappear, or survive when they obey certain rules. These cells are represented by elements on a grid of squares, where a grid has an arbitrary size. Thus, each cell (except those on the boundaries of the grid) is surrounded by eight squares that contain other cells. The rules are stated as follows: 1. Survival: Each cell that has two or three adjacent cells survives until the next generation.2. Death: Each cell that has at least four adjacent cells disappears (or dies) by overpopulation. Also, each cell that has at most one adjacent cell dies by isolation.3. Birth: Each empty square (i.e., dead cell) that is adjacent to exactly three cells gives birthto a new cell for the next generation.It is worth noting that all births and deaths occur at the same time during a generation. Write a program that simulates this game and displays all successive…Find out the similarities between a reference and a pointer."Pointers are known to have issues with dangling and wild pointers." With the use of appropriate examples, justify the stated statement.

