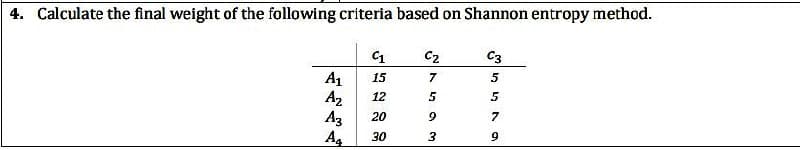
Calculate the final weight of the following criteria based on Shannon entropy method. A₁ Az A3 A₁ C₁ 15 12 20 30 57593 Cz C3 5 5 7 9
Q: \A=0. \ B = 0 nly A is TRUE nly B is TRUE oth A and B are TRUE oth A and B are FALSE 43 11 {0,
A: Here in this question we have given two statements and we have asked that which of them are true.
Q: Is it feasible to use this strategy to describe how a computer works? Following that, we'll most…
A: Introduction: Computers combine input, storage, processing, and output. Inputs: Input devices are…
Q: What are the key differences between a local-area network and a wide-area network in terms of…
A: Introduction: This topic highlights the primary differences between a local area network (LAN) and a…
Q: Because of recent technological advances, the majority of today's appliances can connect wirelessly.…
A: Introduction: Technology has revolutionized our world and daily lives. Additionally, technology for…
Q: select pre increment operators .A variable++ .B ++variable .C variable-- .D --variable
A: Let us see the answer below,
Q: 3) Write a program to read math A= [3 5 2 11 6 413 9 1 108 3 7 612 1 1. Maximum Number in each Row.…
A: We are asked to write a program to read matrix A(4,4) , but since no programing language is mention…
Q: Is it necessary for every cut edge e in an undirected graph G to be an edge in G's depth-first…
A: Intro Here, we must prove or disprove the following statement: "In an undirected graph G, every…
Q: What is the insert anomaly, update anomaly, and delete anomaly computer?
A: Intro Computer bug: There is no such thing as a flawless operating system or piece of software;…
Q: Find as for the sequence defined by ak+1 = 2ak - 1 with ao = 3.
A: Dear Student, The answer to your question is given below here we have used the substitution method -…
Q: Data moved from RAM to virtual storage is referred to as
A: Intro Random Access Memory (RAM): RAM is a physical part of the computer that stores the data and…
Q: The application of data analytics may help to modernise aeroplane maintenance technology. What are…
A: Intro The benefits that data analytics may bring to the field of aircraft maintenance technology The…
Q: The relationships between the ISA and HASA classes.In a class design, how would you implement each?
A: Intro Explain The Isa And Hasa Class Relationships. How Would You Implement Each In A Class Design?
Q: Computer Science Consider the following sequence of keys: (5,16,22,45,2,10,18,30,50,12,1). Consider…
A:
Q: What is Ring Topology and also tell drawback of it?
A: Question is asking about the ring topology and it's drawback in networking.
Q: When it comes to cryptography, what is the difference between a private and a public key?
A: Public key and private key: A private key that is used to encrypt and decrypt data is shared by the…
Q: Distinguish how OLAP functions in descriptive analytics.
A: Introduction: Even while OLAP engines make it easy to do operations such as slicing, dicing,…
Q: Arrow tool, Arc tool, Pen tool and Drawing Elements tool are used to add to ChemDraw document. O…
A: Hello student, hope you are doing well. The correct option is the 1st one 1. Shapes
Q: Which of the following loops would correctly add 1 to to all but the first element in values? Choose…
A: Problem is find all loops : that would correctly add 1 to all but first element in values lets…
Q: What is network address in an IP Address? Give Example?
A: Given question is asking for a term Netwrok Address used in networking.
Q: The graphics card is the component of a high-end gaming computer that consumes the most power.
A: Given: Where is the high-end gaming PC's power-hungry component most likely to be located? Answer: A…
Q: why i is will be = 11000110002 ? Why not use the INFORMATION WORD, 11011001?
A:
Q: Is it possible to avoid access control by performing certain steps?
A: Introduction Can access control be circumvented?
Q: Upgrading to Windows 8 can give you with a better gaming experience if your gaming setup includes…
A: Introduction: The following specifications should be met by a graphic card: The whole game…
Q: Programmatically, why is deep access better than shallow access? Don't rely just on performance.
A: Introduction: Don't just establish a performance case; instead, explain why deep access is…
Q: Define function print_popcorn_time() with parameter bag_ounces. If bag_ounces is less than 3, print…
A: Herecour task is to write a python program for the task mentioned in the question. Let's prepare the…
Q: Which of the following two situations best matches your experience trying to remove software?
A: Certain apps and programs may leave undesired or persistent data or refuse to be erased.
Q: Investigate the several layers that make up the rendering process, as well as the processes that are…
A: Each step of the rendering process represents the environment as viewed by the camera. The camera…
Q: When a procedure written in assembly language is called by a high-level language program, must the…
A: Introduction: When high-level languages that call assembly language procedures: Both should utilize…
Q: is this statement correct or not. A process is a collection of non related work tasks. write the…
A: We must write the proper solution to the provided statement.
Q: One of the oldest and best-known (wired) communication networks in the world is the telephone…
A: let us see the answer:- Introduction:- Data transmission via a wire-based communication technique is…
Q: B) Wha
A: Below I have provided the handwritten soluction to the given question
Q: Define fragmentation. What makes internal and exterior fragmentation different?
A: FRAGMENTATION: Continuous loading and unloading of processes takes place inside the main memory.…
Q: Is it required to run a simulation on a computer for it to be useful? Explain.
A: Intro The management is able to both measure and watches the behavior of the system via the use of…
Q: Provide examples of design principles that will be used to create the proposed system's user…
A: Introduction: The guiding concept of structure. Your design should organise the user interface in a…
Q: A) Add these two number AD45H and 98FCH. *
A:
Q: Is it possible to keep security in an office with shared resources such as a printer?
A: Intro Shared resources are equipment that may be accessed by several distant computers that are…
Q: What relatives does the compiler have? A short description of each of them is required
A: Relatives or cousins of a compiler are: Preprocessor Assembler Loader and Link-editor
Q: Because of the inherent properties of wireless networks, various challenges occur. Give three…
A: Intro Problems with network connection are the most common complaint from wireless network users.A…
Q: Q2) (A) Write the following expressions in Fortran language: 1- If a 3, y sin x 2-z = 26-3 7 3-yx2+3
A: The answer is given in the below step
Q: What are the fundamental actions you should take to get the computer to begin searching for…
A: Intro CD-ROM stands for compact disc read-only memory, which is a kind of computer memory that…
Q: (B) Write a program to print the value of y y= 21+31 31441 + 41+5!
A: I give the code in Python along with output and code screenshot
Q: Because of the nature of wireless networks, a multitude of challenges develop. In your own words,…
A: Intro Nowadays, company groups depend upon reliable, secure wi-fi networks to hold their operations…
Q: What topologies would you suggest for networks?
A: This question provides information about network topologies. The network architecture connects…
Q: What exactly does the shorthand for "Data Definition Language" signify when broken down into its…
A: Language for the Definition of Data: It is abbreviated as "Data Definition Language," which is the…
Q: Java Script Create a function that calculates the number of different squares in an n * n square…
A: Answer: Algorithms: Step1:we have create numberSquares to take arguments as integer Step2: we have…
Q: The rise of computer technology, information technology, information networks, and the internet…
A: Intro The proliferation of computer technology, information technology, information networks, and…
Q: What safeguards exist against DDoS attacks?
A: Introduction: The most fundamental kind of a Denial of Service attack is saturating an IP address…
Q: What if the programming paradigms were documented? How many different paradigms do we really need?…
A: Programming paradigms are classification schemes for programming languages based on the traits they…
Q: A lift calling system is to be programmed for an organization building having 4 floors. The CEO of…
A: ASSUME that lift reaches CEO 3rd floor be A, 1st floor be B and 2 nd floor be C and D Ground floor…
Q: To delete many objects, you need to select them before and choose the "Delete" command or "Delete"…
A: To delete many objects you need to select then and then press delete. True
Step by step
Solved in 2 steps with 2 images

- How does Hartley measure the information that he collects? What exactly does Shannon mean when he refers to the measurement of information? Kindly discuss the parallels as well as the variances.Is my truth table correct for the following conditions? If W is greater than X , then A is 1, B and C are 0. If W equals X, then B is 1, A and C are 0. If W is less than X, C is 1, A and B are 0.Please explain how to complete this truth table. If W is greater than X, then A is 1, B and C are 0. If W is equal to X, then B is 1, A and C are 0. If W is less then X, then C is 1, A and B are 0.
- Express the following in canonical forms , simplify using KMAP and make a truth table of the simplified expression: 1. F(x, y, z) = π (0, 2, 5, 7) 2. F(A, B, C, D) = ∑ (0, 1,2,5,8,9, 10) 3. F(w, x, y, z) = Σ (I, 3, 7,11,15) + d(w, x, y, z) = Σ (0, 2, 5) 4. F(A, B, C, D, E) = Σ(0, 1,4,5,16,17,21,25,29) Note: Pls. show groupings and highlight if possible.3. Display the following on a common, four-case truth table. Use “M” and “C” for “Moriarty is guilty” and “Crun is guilty.” (a) Either Moriarty and Crun are both guilty or Crun is innocent. (b) Either Crun is guilty or both he and Moriarty are. (c) Either Moriarty is guilty or both he and Crun are innocent. (d) Either Moriarty is guilty or Crun is innocent or both are guilty. (e) They are not both guilty, and at least one is innocent. j i f) Either both are guilty or Moriarty is but Crun is not. (g] Either they are not both guilty or they are not both innocent. Which are tautologies? Among the rest, which imply which others? Which imply that Moriarty is guilty? Which imply that Crun is guilty? The seven statements a to g are not jointly satisfiable, but certain six membered subsets are. Which? Which of the seven are individually satisfiable?Question 11 Mah What is the full message for obtained after appending CRC computed with CRC-8 after the message: 0011011 Full explain this question very fast solution sent me step by step
- For the source coding: (a) What is/are the benefit(s) of calculating entropy? (b) What is/are the disadvantage(s) of calculating entropy?(a) What is the difference between variable length source coding and fixed length source coding?Express the following in canonical forms , simplify using KMAP and make a truth table of the simplified expression: 3. F(w, x, y, z) = Σ (I, 3, 7,11,15) + d(w, x, y, z) = Σ (0, 2, 5) Note: Pls. show groupings and highlight if possible.Is (xy+w)' the same as (xy)' + w’ - Create the truth tables to answer the question

