CHALLENGE 4.3.3: While loop: Insect growth. ACTIVITY Given positive integer numinsects, write a while loop that prints, then doubles, numinsects each iteration. Print values < 100. Follow each number with a space. After the loop, print a newline. Ex: If numInsects = 8, print: 8 16 32 64 Learn how our autograder works 480676.1279990.qx3zqy7 1 #include 2 3 int main(void) { 4 5 6 7 8 9 10 11 } Run int numInsects; scanf("%d", &numInsects); // Must be >= 1 /* Your solution goes here */ return 0; 1 test passed All tests
CHALLENGE 4.3.3: While loop: Insect growth. ACTIVITY Given positive integer numinsects, write a while loop that prints, then doubles, numinsects each iteration. Print values < 100. Follow each number with a space. After the loop, print a newline. Ex: If numInsects = 8, print: 8 16 32 64 Learn how our autograder works 480676.1279990.qx3zqy7 1 #include 2 3 int main(void) { 4 5 6 7 8 9 10 11 } Run int numInsects; scanf("%d", &numInsects); // Must be >= 1 /* Your solution goes here */ return 0; 1 test passed All tests
Chapter7: Characters, Strings, And The Stringbuilder
Section: Chapter Questions
Problem 3GZ
Related questions
Question
100%
Need help C
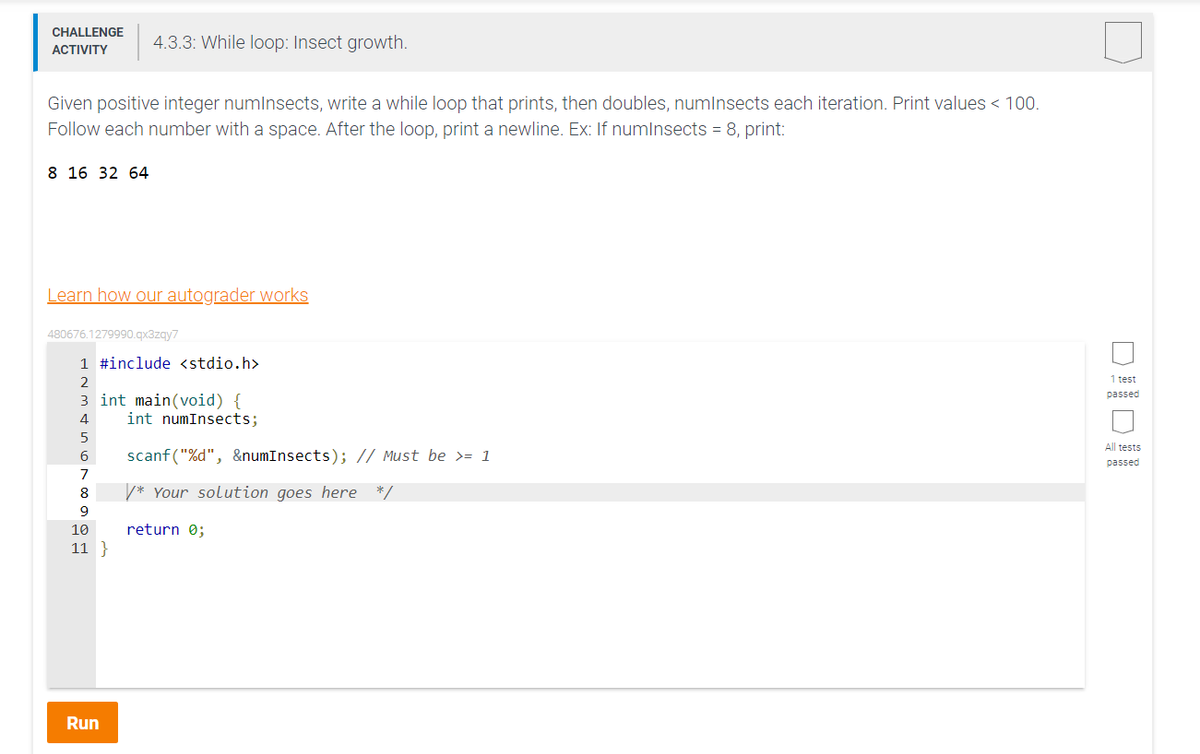
Transcribed Image Text:CHALLENGE 4.3.3: While loop: Insect growth.
ACTIVITY
Given positive integer numInsects, write a while loop that prints, then doubles, numInsects each iteration. Print values < 100.
Follow each number with a space. After the loop, print a newline. Ex: If numInsects = 8, print:
8 16 32 64
Learn how our autograder works
480676.1279990.qx3zqy7
1 #include <stdio.h>
2
3 int main(void) {
4
5
6
7
8
9
10
11}
Run
int numInsects;
scanf("%d", &numInsects); // Must be >= 1
/* Your solution goes here */
return 0;
1 test
passed
All tests
passed
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage