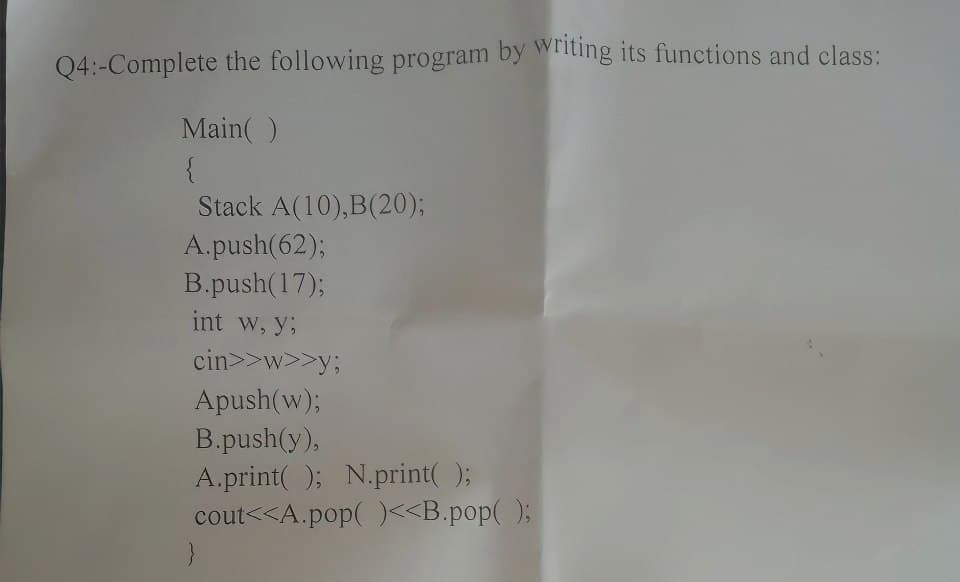
:-Complete the following program by writing its functions and class:
Q: In 1-2 sentences explain the difference between cyber forensics and data recovery. In 1-2 sentences…
A: STEP BY STEP COMPLETE SOLUTION REGARDING YOUR PROBLEM WITH EXPLANATIONS :
Q: Encode devopov with Huffman coding. a. List all symbols and their probabilities b. Find the Huffman…
A: ANSWER:
Q: Experiment with Hypercard or another hypertext system if you have access to one. As you work through…
A: Hypertext which refers to the text which is displayed on a computer devices or electronic devices…
Q: Prove that the height of a complete binary tree with n nodes is exactly ceil(lg(n+1))-1 using…
A:
Q: Note: Please answer in C++ Programming language. During Eid, it is a tradition for every father to…
A: C++ programming language is an object oriented based language but it also supports functional and…
Q: Can the system under consideration be represented as an actor? Justify your answer.
A: Answer : No , system under consideration not be represented as an actor.
Q: Explain the relative advantages and disadvantages of an embedded OS based on an existing commercial…
A: Operating system An operating system goes about as a middle person between the client of a PC and…
Q: What is the shortest path from node A to node D, where shortest path is defined as the path with the…
A: Introduction: The shortest route problem may be defined as whether a graph is undirected, directed,…
Q: https://www.perforce.com/blog/qac/ai-writing-code-will-ai-replace-programmers why is AI not a…
A: The human software developers around the world can breathe a sigh of relief. Here are the answers to…
Q: It is clear that a software development project carried out by a software house for a specific…
A: Introduction: In the question, there are three parts related to software development, Let’s discuss…
Q: It is clear that a software development project carried out by a software house for a specific…
A: 1) The answer is an overwhelming YES. Because when we think about what the customer-supplier…
Q: General Description For this assignment, you will read and process historical stock data for the…
A: Code is given below TeslaStock.java import java.time.LocalDate; public class TeslaStock {…
Q: Define the concept of a unified memory architecture.
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: I'm struggling to make this calculator function. Please make it function. These are my files:…
A: The correct code is given below with output screenshot
Q: During Eid, it is a tradition for every father to give his children money to spend on entertainment.…
A: Input-Output Format: The first line of the input contains a single integer T denoting the number of…
Q: Briefly describe the services provided by the data link layer.
A: The second tier in the OSI reference model is called the Data Link Layer. It describes setting up a…
Q: Describe how testing activities can be initiated well before implementation activities. Explain why…
A:
Q: Given positive integer numInsects, write a while loop that prints that number doubled without…
A: Here I have taken input from the user and stored it into a variable. Next, I have created an…
Q: Explain how configuration management can be beneficial to developers, even in the absence of a…
A:
Q: This challenge is based on the classic videogame "Snake". Assume the game screen is an n * n square,…
A: Program Plan: The following code is written in Python language. Define a Python function, snakefill…
Q: Using suitable example/s differentiate between structural testing and funci
A: The answer is
Q: T lines are designed for Digital data how they can be used for Analog Transmission?
A: Analog to Digital Encoding: Microphones create analog voice and camera creates analog videos, which…
Q: Briefly describe the issues involved in using ATM technology in LANS.
A:
Q: A. Write a C++ program that create struct to read an informations of 20 Students (Name, 7 Degrees,…
A: Hello student I am giving this code as per my best of knowledge :-
Q: Show how STS-9's can be multiplexed to create an STS-36. Is there any extra overhead involved in…
A:
Q: Discuss the functions of each SONET layer.
A: Introduction: The SONET specification has four distinct levels: the photonic, section, line, and…
Q: Describe how testing activities can be initiated well before implementation activities. Explain why…
A: Testing: We ought to check out at this in extraordinarily more direct words for better awareness.…
Q: n of a parent who
A: Solution - In the given question, we have to tell the practices/procedures for a child to start…
Q: C++ program (5 points) Implement a class with the required data fields, constructor, and…
A: Your C++ program is given below as you required with an output.
Q: After composing the code for the " Create Horse Table with Constraints" I'm still not getting an…
A: Given query: CREATE TABLE Horse ( ID SMALLINT UNSIGNED AUTO_INCREMENT PRIMARY KEY,…
Q: What are the relative advantages of flat staffing versus gradual staffing?
A: Here we have given a brief note on advantages of flat staffing versus gradual staffing. You can find…
Q: Perform the following base conversions using subtraction or division-remainder (show the steps): a)…
A:
Q: What would be the average case access time if we could increase the rotation speed from 2,400…
A: To calculate the average case access time, we need to know the rotational speed of the disk and the…
Q: 1 2 3. 4 5 6. 7 8 0 1 4 5 class Solution { public: }; Autocomplete char repeated Character(string s)…
A: The given code snippet is a class in which we are finding the repeated character of the given…
Q: Problem 1. Suppose you have to design software for the Oscar Jury members where they can ate the…
A: Code is given below #include <stdio.h>#include <stdlib.h>#include <string.h>…
Q: nterface in Java. Tru
A: Solution - In the given question, we have to tell whether the given statement is true or false.
Q: Write a program that asks the user to enter an integer consisting of 4 digits only, and check how…
A: C programming language is used below to solve the given problem. Algorithm: Start Initialise the…
Q: Consider a program that accesses a single I/O device and compare unbuffered I/O to the use of a…
A: Following are several ways to explain the buffering scheme: Transfers of input data are conducted to…
Q: Describe how testing activities can be initiated well before implementation activities. Explain why…
A: Testing activities can be carried out using a model known as the V-model. The V-model actually…
Q: QUESTION 26 Given: vector mag = 78,107, 37,102, 37, 120, 121, 122, 105, 106, 115, 121, 37, 120,…
A: The above question is solved in step 2 :-
Q: value generated
A: Solution - In the given question, we have to select the correct answer from the given options.
Q: I am trying to write a an essay on the five step design method for relational databases
A: The above question is solved in step 2 :-
Q: Assume you are part of the IEEE committee that will revise the IEEE 1074 standard. You have been…
A: The first step in modeling communication as an explicit integral process is to identify the various…
Q: Convert the following decimal fractions to binary with a maximum of six places to the right of the…
A: Note: As per our company policy, the answers of the first three subparts are given in this solution.…
Q: Mubashir needs your help to find out the next happy year. A Happy Year is the year with only…
A: Algorithm - Take input from user. Now use the below logic - if (new Set(String(year + 1)).size…
Q: Briefly describe the issues involved in using ATM technology in LANS.
A: ATM stands for Asynchronous Transfer Mode. For transmission of data from source to destination it…
Q: A stream of data is being carried by STS-1 frames. If the data rate of the stream is 49.540 Mbps,…
A:
Q: How does IPSec create a set of security parameters?
A: Introduction: IPsec was at first evolved on the grounds that the most well-known web convention,…
Q: what are your thoughts/opinions on what you think the challenges may be in the implementation of CQI…
A: what are your thoughts/opinions on what you think the challenges may be in the implementation of…
Q: Write a program to print the lyrics of the song "Old MacDonald." Yourprogram should print the lyrics…
A: Lets see the solution.
Step by step
Solved in 5 steps with 4 images

- Assume the function: void F(stack<T> &S){ } and we send a stack S to the function F, as a result of it إختر أحد الخيارات: a. Both (copy constructor and destructor) should be called b. Both (copy constructor and destructor) should not be called c. Destructor should be called d. Copy constructor should be calledin C++ Suppose we have class named NumberList that holds a linked list of double values. In this section you will modify the class by adding recursive member functions. The functions will use recursion to traverse the linked list and perform the following operations:• Count the number of nodes in the list.To count the number of nodes in the list by recursion, we introduce two new member functions: numNodes and countNodes. countNodes is a private member function that uses recursion, and numNodes is the public interface that calls it.• Display the value of the list nodes in reverse order.To display the nodes in the list in reverse order, we introduce two new member functions: displayBackwards and showReverse. showReverse is a private member function that uses recursion, and displayBackwards is the public interface that calls it.write a program in C++ , (Postfix Evaluation) Write a program that evaluates a valid postfix expression such as 6 2 + 5 * 8 4 / -The program should read a postfix expression consisting of digits and operators into a string. Using modified versions of the stack functions implemented earlier in this chapter, the program should scan the expression and evaluate it. The algorithm is as follows: While you have not reached the end of the string, read the expression from left to right. If the current character is a digit, Push its integer value onto the stack (the integer value of a digit character is its value in the computer’s character set minus the value of '0' in the computer’s character set). Otherwise, if the current character is an operator, Pop the two top elements of the stack into variables x and y. Calculate y operator x. Push the result of the calculation onto the stack. When you reach the end of the string, pop the top value of the stack. This is the result of the postfix…
- In the following code, assume myStack is a stack that holds integers. What would be the contents of the stack after the following operations, indicating what element is currently at the top and the bottom of the stack. myStack.push(1);myStack.push(2);myStack.push(3);myStack.pop();myStack.push(4);myStack.push(5);myStack.pop(); Group of answer choices 4 <- Top21 <- Bottom 5 <- Top31 <- Bottom 4 <- Top32 <- Bottom 5 <- Top21 <- BottomTrue or False For each statement below, indicate whether you think it is True or False. If you like, you can provide a description of your answer for partial credit in case you are incorrect. Given a stack implemented as an array, and the following functions performed: Push(A), Push (B), Push(C), Pop(), Push(D), Push(E), Pop(), Push(F) The array will be [A][B][D][F] and the “top” of the stack will be at index 3 where [F] is The next element that will be removed when Pop is called will be A If we Push(G), [G] will be inserted at index 0 Given a queue implemented as an array with a maximum capacity of 5 elements and O(1) insert and remove, and the following functions are performed: Insert(7), Insert(6), Insert(5), Insert(4), Remove(), Remove(), Insert(3), Insert(2), Insert(1), Remove() The removeIndex value will be index 4 The array will be [2][1][ ][4][3] The insertIndex value will be index 2 Given a priority queue implemented as a standard linked list with only a…Task3: Some of the scientific calculators are capable of identifying errors based on the imbalance of parentheses used in mathematical equations. (4+6)*[7/(9-3)] ==> ()[()] ==> BALANCED (4+6)*7/(9-3)] ==> ()()] ==> IM-BALANCED From the above-mentioned example, we can clearly see that the checking of balance in an equation is simple, which is comparing opening parentheses with the closing ones. As a developer, you are required to write a code that checks an equation for being balanced or not.(HINT: use stack) in c++
- Project 4: Maze Solver (JAVA) The purpose of this assignment is to assess your ability to: Implement stack and queue abstract data types in JAVA Utilize stack and queue structures in a computational problem. For this question, implement a stack and a queue data structure. After testing the class, complete the depth-first search method (provided). The method should indicate whether or not a path was found, and, in the case that a path is found, output the sequence of coordinates from start to end. The following code and related files are provided. Carefully ready the code and documentation before beginning. A MazeCell class that models a cell in the maze. Each MazeCell object contains data for the row and column position of the cell, the next direction to check, and a bool variable that indicates whether or not the cell has already been visited. A Source file that creates the maze and calls your depth-first search method. An input file, maze.in, that may be used for testing. You…Stacks 1- Write a Python function that takes a user input of a word and returns True if it is a Palindrome and returns False otherwise (Your function should use a Stack data structure). A palindrome is a word that can be read the same backward as forward. Some examples of palindromic words are noon, civic, radar, level, rotor, kayak, reviver, racecar, redder, madam, and refer. 2- Write a Python function that takes a stack of integer numbers and returns the maximum value of the numbers in the stack. The stack should have the same numbers before and after calling the function. 3- Write a main function that tests the functions you wrote in 1 and 2 above and make sure that your code is well documented.Can anyone convert this c++ code to python? //THIS PROGRAM IS CREATED TO DEMONSTRATE THE OPERATIONS PERFORMED ON STACK & ITS IMPLEMENTATION USING ARRAYS #include <iostream>#include <stdio.h>#include <conio.h>#include <stdlib.h>#include <process.h> //Defining the maximum size of the stack#define MAXSIZE 7 using namespace std; //A class initialized with public and private variables and functionsclass STACK_ARRAY { int stack[MAXSIZE]; int Top; public: //constructor is called and Top pointer is initialized to -1 when an object is created for the class STACK_ARRAY() { Top = -1; } void push(); void pop(); void traverse(); }; //This function will add/insert an element to Top of the stackvoid STACK_ARRAY::push(){ int item; //if the top pointer already reached the maximum allowed size then we can say that the stack is full or overflow if (Top == MAXSIZE-1) { cout << "\nThe Stack Is Full"; }…
- Can anyone convert this c++ code to python? //THIS PROGRAM IS CREATED TO DEMONSTRATE THE OPERATIONS PERFORMED ON STACK & ITS IMPLEMENTATION USING ARRAYS #include <iostream>#include <stdio.h>#include <conio.h>#include <stdlib.h>#include <process.h> //Defining the maximum size of the stack#define MAXSIZE 7 using namespace std; //A class initialized with public and private variables and functionsclass STACK_ARRAY { int stack[MAXSIZE]; int Top; public: //constructor is called and Top pointer is initialized to -1 when an object is created for the class STACK_ARRAY() { Top = -1; } void push(); void pop(); void traverse(); }; //This function will add/insert an element to Top of the stackvoid STACK_ARRAY::push(){ int item; //if the top pointer already reached the maximum allowed size then we can say that the stack is full or overflow if (Top == MAXSIZE-1) { cout << "\nThe Stack Is Full"; }…6. Write the prototype and definition of a new non-member function int size(…..) to the class Stack based on compile array which returns the current size (number of actual items) in your object of type StackTrue or False For each statement below, indicate whether you think it is True or False. provide a description of your answer for partial credit in case you are incorrect. 1) Given a stack implemented as an array, and the following functions performed: Push(A), Push (B), Push(C), Pop(), Push(D), Push(E), Pop(), Push(F) a. The array will be [A][B][D][F] and the “top” of the stack will be at index 3 where [F] is b. The next element that will be removed when Pop is called will be A c. If we Push(G), [G] will be inserted at index 0

