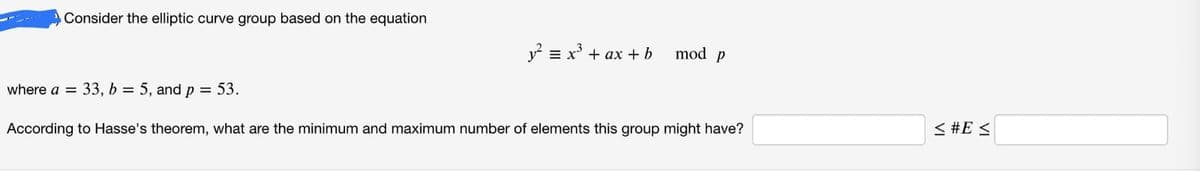
Consider the elliptic curve group based on the equation. where a = 33, b = 5, and p = 53. y² = x³ + ax + b mod p According to Hasse's theorem, what are the minimum and maximum number of elements this group might have? < #E≤
Q: distances between nodes in an eight-node network is presented in the from-to distance table below.…
A: Here, from the question In the given problem, the graph contains 8 nodes from 1 to 8 in it.. The…
Q: Give a single example of a sensor utilized in a mobile device.
A: The question has been answered in step2
Q: Turning ON/OFF a list of pins We want to create a program that repeats the following sequence…
A: Here we have given aurdino code using arrays and for loops. You can find the details in step 2.
Q: What is the point of charts and similar data illustrations? What do they offer someone that merely…
A: - We need to talk about the supremacy of charts over spreadsheets.
Q: (a) Determine a good asymptotic upper bound on the recurrence T(n) = 5T([n/4])+n by the iteration…
A: Given Data T(n) = 5T([n/4]) + n Iteration method An iterative method is a mathematical technique…
Q: Social networking platforms are popular (such as Facebook and Twitter). Determine why people choose…
A: Individuals prefer digital social networks due the following reasons:1. Introverts find it easy to…
Q: Write a simple trivia quiz game using c++ Start by creating a Trivia class that contains…
A: Define Trivia class that stores information about a single trivia question. Define default…
Q: Given that a 4-way set associative cache memory has 64 KB data and each block contains 32 bytes. The…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Q: What is the biggest disadvantage to adding error detection bits to a data stream to check for bit…
A: It is defined as the process when the data is transmitted from one device to another device, the…
Q: Write an application that inputs three integers from the user and displays the sum, average,…
A: You didn't mention any programming language, hence according to Bartleby policy, I have answered in…
Q: what is wrong with the code ? % Determines the decimal equivalent of a % binary number in…
A: bin = input('Type in the binary fraction = = '); b = length (bin) - 1; d = 0; for k = 1:b d = d +…
Q: For the 8-bit word 00111001, the check bits stored with it would be 0111. Suppose when the word is…
A:
Q: Question 2: Prove that the following grammar is ambiguous. A-> ABA A -> e
A: The question is to check if the given grammar is ambiguous or not.
Q: Exercise 1.5 What are the responsibilities of a DBA? If we assume that the DBA is never interested…
A: A Database Administrator (DBA) design, implement, administers and monitors data management systems…
Q: What led to the creation of the RISC architectural idea?
A: The RISC or the Reduced instruction set Computer is a special kind of Microprocessor which is…
Q: 2. Consider a server with RAID Level 3 and given Figure 2 below, determine the bit for data…
A: Note: as per guidelines we are supposed to answer only one question at a time. please repost the…
Q: Excuse me, about the line 10 and line 37 i want the data[2] is variable like data[%d] thank you!
A: In the C program contains two functions which are used to find the maximum element position and that…
Q: A common unit of measure for failure rates of electronic components is the Failure unIT (FIT),…
A: MTBF means to predict average time between inherit failures of system during operation of normal…
Q: Talk about two specific database design issues for the creation of Web-based applications.
A: Please find the detailed explanation in the following steps.
Q: What is needed to build a database in the physical world? Make a list of some of the most popular…
A: A database is a software that manages data in organized manner. A database is used when huge volume…
Q: / A A user is executing a tracert to a remote device. At what point would a router, which is in the…
A: A user is executing a tracert to a remote device. At what point would a router, which is in the path…
Q: Calculate the number of nodes in a complete binary tree with height h. Where h is equal to the 3rd…
A: A binary tree is a tree with at most 2 child nodes in which the left node is always lesser than the…
Q: Design a class called Stack with three methods. void Push(object obj)object Pop()void Clear() We…
A: The solution is provided below.
Q: What Is Java Virtual Machine (JVM)?
A: A computer can run programmes written in other languages that have also been translated into Java…
Q: Question 2: Prove that the following grammar is ambiguous. A-> ABA A -> e
A: The context free grammar is the form of grammar which is used to generate all the possible pattern…
Q: Example ID: 201710 349. You must use your own ID. Key values: 201, 710, 340 tableSize: 2 hash(x) = x…
A: Considering each 3 consecutive digits in your ID as a key value. Using linear propping, insert items…
Q: What exactly is the purpose of Artificial Intelligence (Al)? Identify its several domains and…
A: Artificial Intelligence's ultimate goal Software that can handle real-world issues efficiently and…
Q: Give a brief definition of machine language. Please also explain why English is not understood by…
A: Please find the detailed answer in the following steps.
Q: CPU scheduler will decide which process should be given the CPU for its execution. For this it uses…
A: code- #include<stdio.h>int main(){ int AT[20],WT[20],BT[20],TT[20]; int n; int…
Q: Question & Listen MC9: The following screenshot is the network configuration in one computer host of…
A:
Q: Suggest reasons why RAMS traditionally have been organized as only 1 bit per chip whereas ROMs are…
A: RAM is also known as random access memory.
Q: Explain the benefits that come from using Cleanroom Software Engineering. Demonstrate the benefits…
A: The clean rooms depend's on the rules that deformity anticipations is superior to surrender…
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Answer: The industry has coined the term "Shared Responsibility" to describe the tasks and…
Q: Explain the differences between Big Endian and Little Endian in the context of computer architecture
A: The difference between little endian and big endian formats, also sometimes called endian-ness is…
Q: Which option of rm command is used to remove a non- empty directory? A) -t B)-i C) -a D) -r
A: For removal of a directory which is not empty, we use the rm command with the -r option for…
Q: Create a webpage showing strikethrough underline text?
A: Question wants a webpage with underlined strikethrought text.
Q: Please go into depth about the restricted access protocol.
A: Protocol for Controlled Access: In restricted access, both departments examine one another's records…
Q: Popular social networks like Facebook and Twitter attract a lot of people. Determine whether they…
A: Introduction: These ties, exchanges, and interactions are the building blocks of social networks. As…
Q: How is a firewall utilized in network designs?
A: A firewall is a network security device to monitor the flow of network traffic and safeguards as a…
Q: Consider a magnetic disk drive with 8 surfaces, 512 tracks per surface, and 64 sectors per track.…
A: Given: Number of disk surface=8 Track per surface=512 Sector size =1 KB Sector per track=64 Avg seek…
Q: The Class: (CHECK ALL THAT APPLY) is the definition or "blueprint" defines a list of attributes and…
A: 1) A class is a blueprint that defines the variable and the methods commom to all objects of a…
Q: Give a proof of
A: Let x and y be arbitrary objects. Suppose that for all x and y, x=y implies that for all y,…
Q: Consider a logical address space of 512 pages with a 4-KB page size, mapped onto a physical memory…
A:
Q: ass then perform the following: 1) Output the array elements 2) Output the sum of prime numbers in…
A: The program is written in Java. Please find the program and output in the following steps.
Q: Your supervisor said, “Integration testing is a waste of time. If each program is tested adequately,…
A: Introduction Your supervisor said, “Integration testing is a waste of time. If each program is…
Q: Give a single example of a sensor utilized in a mobile device.
A: Mobile phone sensors can be defined as specific technologies that are able to capture changes in the…
Q: For the 8-bit word 00111001, the check bits stored with it would be 0111. Suppose when the word is…
A: Introduction So in this given question, we are asked What is the data word that was read from…
Q: Explain the benefits that come from using Cleanroom Software Engineering. Demonstrate the benefits…
A: Cleanroom Software engineering:- This is based on set of formal specifications which describes the…
Q: Create a webpage with bold and strikethrought text?
A: Given question wants a webpage with using some formatting tags in html.
Q: Q. Give example of H3 and h4 tags in html?
A: <html><body> <h3>HELLO!</h3> <h4>HELLO!</h4>…
2.3
Step by step
Solved in 2 steps with 2 images

- Consider the elliptic curve group based on the equation ?2≡?3+??+?mod? where ?=2, ?=11, and ?=17. In this group, what is 2(4,7)=(4,7)+(4,7)? In this group, what is (4,10)+(6,1)? What is the inverse of (6,16) (with entries in ℤ17)?Consider the elliptic curve group based on the equation ?2≡?3+??+? mod? where ?=294 ?=601 and ?=1297. According to Hasse's theorem, what are the minimum and maximum number of elements this group might have? ≤#?≤≤#E≤Given the following sets: A = {7, 5} B = {1 , 2 , 5, 4} C = {1, 7} Find B x A x C. Question: What is the cardinality of the resulting cartesian product?
- Let R=ABCDEGHK and F= {ABK→C, A→DG, B→K, K→ADH, H→GE} . Is it in BCNF? Prove your answer.Let Π1, Π2, and Π3 be the problems. Prove that if Π1 ≤p Π2 and Π2 ≤p Π3, then Π1 ≤p Π3.Given the following sets: A = {7, 5} B = {1, 2, 3, 4, 5} C = {1, 7} Find C x B x A Question: what is the cardinality of the resulting cartesian product?
- 2. Let (Finite_DFA) = {w, Mx is a DFA and L(Mx) is finite}. Show that (Finite_DFA) is decidable.Let E : y2 = x3 + 3x + 4 be an elliptic curve over F37. (a) Find all the elements of the elliptice curve group.(b) Find the order of the group.(c) Find a primitive element of this group and call it G.(d) Compute [30]G = G ⊕ G ⊕ · · · ⊕ G (addition of 30 many G’s) kindly help with full explanation. Thank you!Given that h(p)=p2−3p+5, Find;h(x-3)
- Find the value of x for the following sets of congruence using the Chinese remainder theorem.a. x ≡ 2 mod 7, and x ≡ 3 mod 9b. x ≡ 4 mod 5, and x ≡ 10 mod 11c. x ≡ 7 mod 13, and x ≡ 11 mod 12Use the Time-Hierarchy Theorem to prove that P!= EXP.1.1 Define a growth factor for the above difference equation (in the picture), also verify that your function is a growth factor for the above difference equation. ( Reccomend Use of Python3) 1.2 Determine all the equilibria of the above difference equation by solving an appropiate equation using simpy. 1.3 Use numpy and matplotlib to make a line plot of the graph of the growth factor g that you defined above on the interval 1.4 Use your plot to classify all determined equilibra as stable/unstable. Explain your reasoning.

