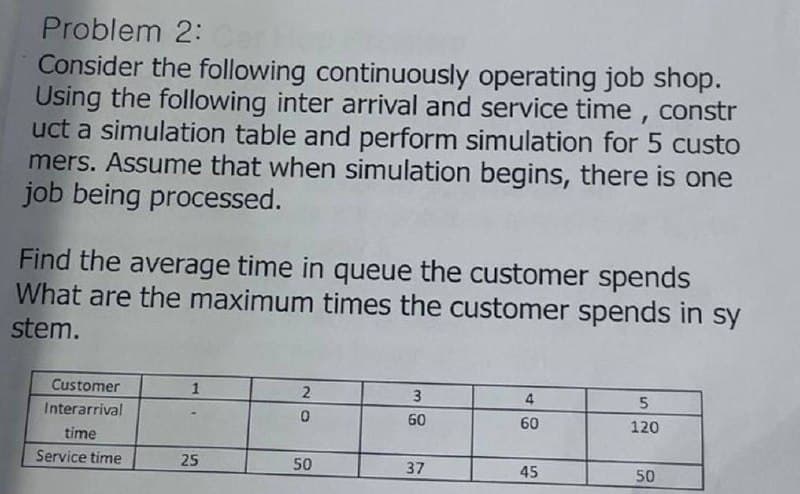
Consider the following continuously operating job shop. Using the following inter arrival and service time , constr uct a simulation table and perform simulation for 5 custo mers. Assume that when simulation begins, there is one job being processed. Find the average time in queue the customer spends What are the maximum times the customer spends in sy stem. Customer 1 3 4 Interarrival 60 60 120 time Service time 25 50 37 45 50
Consider the following continuously operating job shop. Using the following inter arrival and service time , constr uct a simulation table and perform simulation for 5 custo mers. Assume that when simulation begins, there is one job being processed. Find the average time in queue the customer spends What are the maximum times the customer spends in sy stem. Customer 1 3 4 Interarrival 60 60 120 time Service time 25 50 37 45 50
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter20: Queuing Theory
Section20.10: Exponential Queues In Series And Open Queuing Networks
Problem 6P
Related questions
Question
i need the answer quickly
Transcribed Image Text:Problem 2:
Consider the following continuously operating job shop.
Using the following inter arrival and service time, constr
uct a simulation table and perform simulation for 5 custo
mers. Assume that when simulation begins, there is one
job being processed.
Find the average time in queue the customer spends
What are the maximum times the customer spends in sy
stem.
Customer
1
3
4
Interarrival
60
60
120
time
Service time
25
50
37
45
50
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole