Refer to this video lecture about multidimensional arrays. Write a program that takes the scores of four students on three quizzes. Then output the total and average score of each student. Store the scores in a two-dimensional array. Consider the following sample Input/Output flow:
Refer to this video lecture about multidimensional arrays. Write a program that takes the scores of four students on three quizzes. Then output the total and average score of each student. Store the scores in a two-dimensional array. Consider the following sample Input/Output flow:
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter12: Points, Classes, Virtual Functions And Abstract Classes
Section: Chapter Questions
Problem 29SA
Related questions
Question
C++ PROGRAM
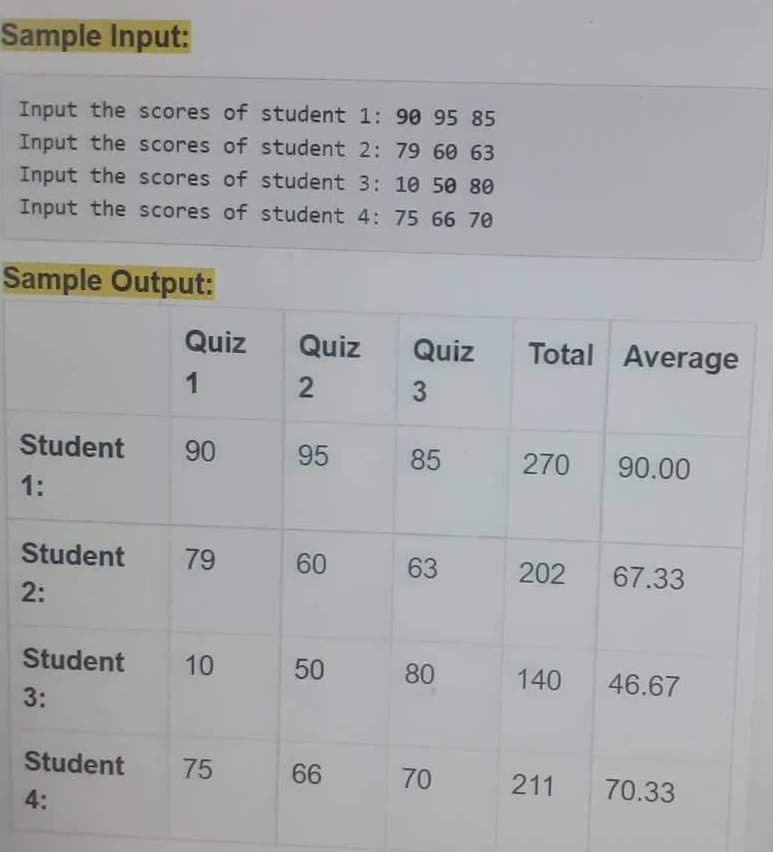
Transcribed Image Text:Sample Input:
Input the scores of student 1: 90 95 85
Input the scores of student 2: 79 60 63
Input the scores of student 3: 10 50 80
Input the scores of student 4: 75 66 70
Sample Output:
Quiz
Quiz
Quiz
Total Average
1
3
Student
90
95
85
270
90.00
1:
Student
79
60
63
202
67.33
2:
Student
10
50
80
140
46.67
3:
Student
75
66
70
211
70.33
4:
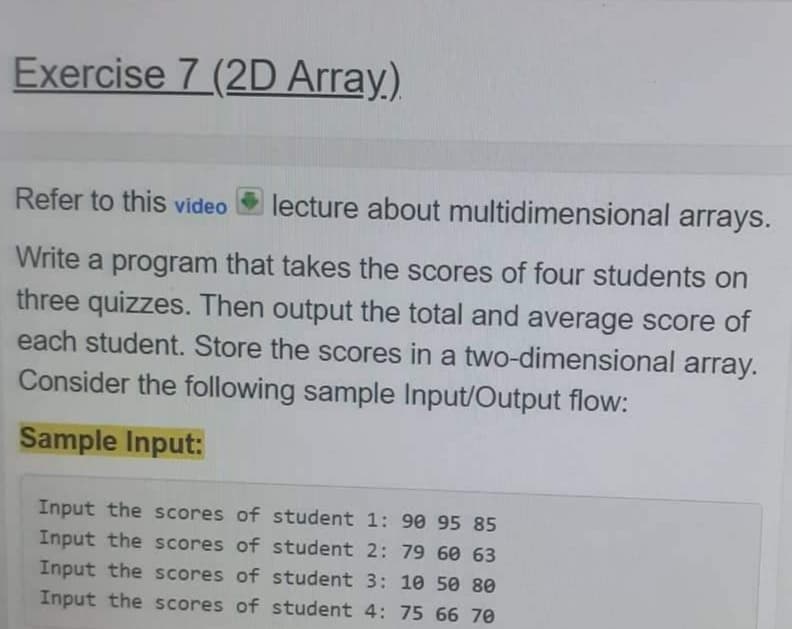
Transcribed Image Text:Exercise 7 (2D Array,)
Refer to this video
lecture about multidimensional arrays.
Write a program that takes the scores of four students on
three quizzes. Then output the total and average score of
each student. Store the scores in a two-dimensional array.
Consider the following sample Input/Output flow:
Sample Input:
Input the scores of student 1: 90 95 85
Input the scores of student 2: 79 60 63
Input the scores of student 3: 10 50 80
Input the scores of student 4: 75 66 70
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning