CPU Clock = 1 GHz 1 OP requires 5 clock cycles (arithmetic instruction, conditional, etc.) 1 memory access requires 100 clock cycles (Read or Write)
CPU Clock = 1 GHz 1 OP requires 5 clock cycles (arithmetic instruction, conditional, etc.) 1 memory access requires 100 clock cycles (Read or Write)
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter2: Problem Solving Using C++using
Section2.5: Variables And Declaration Statements
Problem 9E: (Practice) a. Using Figure 2.14 and assuming the variable name rate is assigned to the byte at...
Related questions
Question
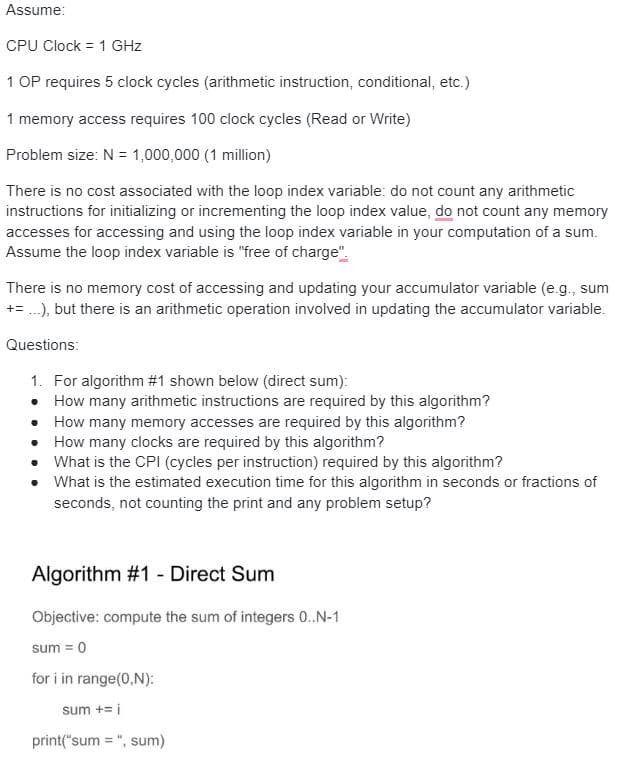
Transcribed Image Text:Assume:
CPU Clock = 1 GHz
1 OP requires 5 clock cycles (arithmetic instruction, conditional, etc.)
1 memory access requires 100 clock cycles (Read or Write)
Problem size: N = 1,000,000 (1 million)
There is no cost associated with the loop index variable: do not count any arithmetic
instructions for initializing or incrementing the loop index value, do not count any memory
accesses for accessing and using the loop index variable in your computation of a sum.
Assume the loop index variable is "free of charge"
There is no memory cost of accessing and updating your accumulator variable (e.g., sum
+= ...), but there is an arithmetic operation involved in updating the accumulator variable.
Questions:
1. For algorithm #1 shown below (direct sum):
• How many arithmetic instructions are required by this algorithm?
• How many memory accesses are required by this algorithm?
• How many clocks are required by this algorithm?
• What is the CPI (cycles per instruction) required by this algorithm?
•
What is the estimated execution time for this algorithm in seconds or fractions of
seconds, not counting the print and any problem setup?
Algorithm #1 - Direct Sum
Objective: compute the sum of integers 0..N-1
sum = 0
for i in range(0,N):
sum += i
print("sum = ", sum)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning