CREATE A FLOWCHART WITH THE GIVEN CODES BELO
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter12: Points, Classes, Virtual Functions And Abstract Classes
Section: Chapter Questions
Problem 29SA
Related questions
Question
CREATE A FLOWCHART WITH THE GIVEN CODES BELOW
![matl - np.array ((
(1,8,2,3],
[4,2,9,0],
[4,6,7,1],
[4,2,2,0],
1)
np.array ([
[1,7,8,4],
mat2 =
[5,2,3,1],
[8,2,9,91,
[ 8,1,9,7)
])
mat_operations (mat1, mat2)
Matrix 1: [[1 8 2 3]
[4 29 0]
[4 67 1]
[4 2 2 0]]
Matrix 2: [[1 7 8 4]
[5 2 3 1]
[8 2 9 91
[8 1 9 7)]
Sum of the given matrices:
[[ 2 15 10 7]
( 9 4 12 1]
8 16 10]
(12
(12
3 11 7]]
Difference of the given matrices:
1 -6 -1]
6 -1]
4 -2 -8]
(-1
[-4
[-4
Element-wise multiplication of the given matrices:
[[ 1 56 16 12]
1 -7 -7]]
[20 4 27 0]
[32 12 63
9]
2 18
0]]
[32
Element-wise division of the given matrices :
[[1.
1.14285714 0.25
0.75](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2F669d4a79-2169-42a9-b2ae-e9252928d27f%2F815471e6-57b9-4ec3-9959-af4b907e1c0e%2Fvkt64mp_processed.png&w=3840&q=75)
Transcribed Image Text:matl - np.array ((
(1,8,2,3],
[4,2,9,0],
[4,6,7,1],
[4,2,2,0],
1)
np.array ([
[1,7,8,4],
mat2 =
[5,2,3,1],
[8,2,9,91,
[ 8,1,9,7)
])
mat_operations (mat1, mat2)
Matrix 1: [[1 8 2 3]
[4 29 0]
[4 67 1]
[4 2 2 0]]
Matrix 2: [[1 7 8 4]
[5 2 3 1]
[8 2 9 91
[8 1 9 7)]
Sum of the given matrices:
[[ 2 15 10 7]
( 9 4 12 1]
8 16 10]
(12
(12
3 11 7]]
Difference of the given matrices:
1 -6 -1]
6 -1]
4 -2 -8]
(-1
[-4
[-4
Element-wise multiplication of the given matrices:
[[ 1 56 16 12]
1 -7 -7]]
[20 4 27 0]
[32 12 63
9]
2 18
0]]
[32
Element-wise division of the given matrices :
[[1.
1.14285714 0.25
0.75
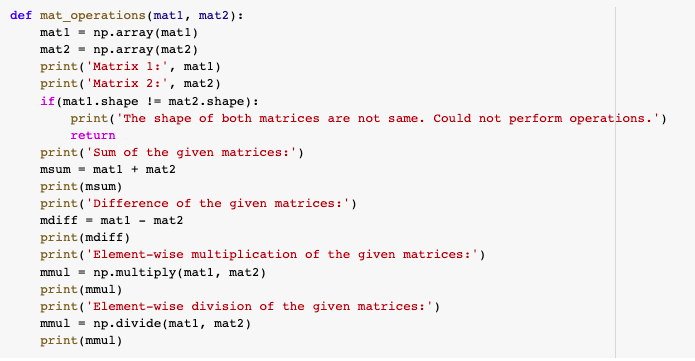
Transcribed Image Text:def mat_operations (matl, mat2):
matl - np.array (mat1)
mat2 - np.array (mat2)
print( 'Matrix 1:', matl)
print ('Matrix 2:', mat2)
if (matl.shape != mat2.shape):
print('The shape of both matrices are not same. Could not perform operations.')
return
print('Sum of the given matrices:')
msum - matl + mat2
print(msum)
print('Difference of the given matrices:')
mdiff = matl - mat2
print(mdiff)
print ('Element-wise multiplication of the given matrices:')
mmul = np.multiply(matl, mat2)
print (mmul)
print( 'Element-wise division of the given matrices:')
mmul - np.divide (matl, mat2)
print(mmul)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning