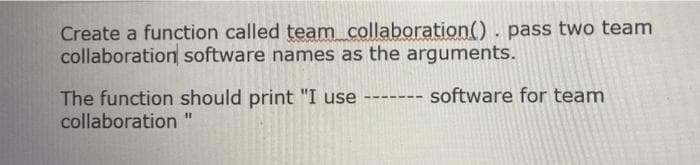
Create a function called team collaboration(). pass two team collaboration software names as the arguments. The function should print "I use collaboration software for team ---- ---
Q: Many companies are undergoing server virtualization. This is the concept of putting multiple "virtua...
A: Explanation: (a) Return on investment for the server virtualization involve initial cost such as the...
Q: Decide whether each of the following statements is true or false. Any function from the natural numb...
A: *As per the company norms and guidelines we are providing first three sub parts of the question so p...
Q: Write a Java program that obtains products' numbers (array named products[]), and allows the user to...
A: The Answer is given below step.
Q: What are the canonical and standard forms of Boolean function?
A: The Answer is
Q: 1. Many companies pay time-and-a-half for any hours worked above 40 in a given week. Write a program...
A: PROGRAM INTRODUCTION: Take the number of hours from the user. Convert the number of hours into floa...
Q: An airline firm LTd limited was looking for a solution that would allow them to dynamically bundle h...
A: Intro Actually, given information regarding airline company LTd
Q: ii) In JAVA language input the elements of an integer array A of size 10 and find the count of all h...
A: In JAVA language input the elements of an integer array A of size 10 and find the count of all hills...
Q: Create a Personal Information table with the following field's First name, Gender, Nationality, add...
A: NOTE : AS PER BARTLEBY GUIDELINES WE ARE ALLOWED TO ANSWER ONLY THE FIRST 3 QUESTIONS OF ANY MULTIPL...
Q: Instruction: A mathematician named Ulam proposed generating a sequence of numbers from any positive ...
A: PROGRAM EXPLANATION Import the java.util package. Create the main class. Define the main method. As...
Q: How does virtual memory fare in terms of speed in comparison to random access memory?
A: RAM stands for Random Access Memory and is known by the name of Main memory.
Q: What exactly is the Protector role?
A: What exactly is the Protector role?
Q: Excellent example of partitioning
A: Excellent example of partitioning is dividing hard disk
Q: 1. ( For the Cities database, discuss one problem with either the correctness of the data or what ca...
A: Introduction 1. ( For the Cities database, discuss one problem with either thecorrectness of the dat...
Q: For recognizing anomalies for unusual sequences of credit card transactions, define what can be the ...
A: According to the question, we have to identifying unusual sequences for 20 instances. and Discuss ab...
Q: Items for mobile users are controlled through a "Application Store" interface. Users may browse, dow...
A: Intro Browse. Download install
Q: ompeting demands for resources cause all deadlocks.
A: Introduction: A deadlock is a stalemate that arises when many processes compete for the same resourc...
Q: What does the term "implicitness" in SE mean?
A: Introduction Implied or understood though not directly expressed an implicit agreement not to raise...
Q: The three core processes of the requirement engineering process are elicitation, specification, and ...
A: Introduction Requirement Engineering: In general requirement, engineering may be defined as the pr...
Q: What is a data cube? Define three data dimensions of a data cube that might be used to analyze sales...
A: A Data solid shape as its name recommends is an augmentation of a 2-Dimensional information 3D squar...
Q: hat distinguishes a software development process from software modelling? Explain how one aids the o...
A: Introduction: Process of Software Development: A software development process is a method of separat...
Q: students in the BIT Level 300 class obtained various grades in a mid semester exam. create an algori...
A: Flowchart is a representation of an algorithm in the graphical way. It is very effective and efficie...
Q: One of the benefits of a Hadoop installation is the high level of compute redundancy. Why is this so...
A: Introduction: One of the benefits of a Hadoop installation is the high level of compute redundancy. ...
Q: Identify ten computer, network, and information security attacks and analyse how each of them affect...
A: Introduction An attack is any attempt to expose, alter, disable, destroy, steal or gain information ...
Q: Suppose an algorithm takes exactly the given number of statements for cach value bclow, in terms of ...
A: Big-O complexity is the maximum time taken in power. If two terms are given then we select maximum o...
Q: Python question
A: Python CODE: def isLeap(year): if year % 4 <> 0: return False elif year % 100 ...
Q: QUESTION 9: Pumping lemma with length Use the Pumping Lemma with length to prove that the following ...
A: Below is the answer to above question. I hope this will be helpful for you..
Q: Identify any four UNIX utility commands and explain its use with an example
A: four UNIX utility commands are 1) cal 2) date 3) banner 4) who
Q: An IT Company tasked your group as network experts to create a new infrastructure with the following...
A: Below is the diagram for high level network.
Q: What impact will artificial intelligence have in the future? What artificial intelligence-based soft...
A: Introduction: The application of computer-assisted reasoning: Artificial intelligence (AI) is a bran...
Q: Cybersecurity outline budget proposal for a small business of a cell phone/laptop repair shop. Provi...
A: Hardware requirements - 1.spare parts for mobile and laptop 2.soldering iron 3.Screwdriver 4. diffe...
Q: Question 3 Design push-down automaton that recognises the following languages. a. Ll={a"ba" | n>0} b...
A: Here, we are going to design a Push down automaton (PDA) for given language L1. In PDA, We use stack...
Q: Lets say that class Laptop has been implemented. In order to compare two laptops a compareTo method ...
A: The answer of this question is as follows:
Q: Write a Java program to take 2 strings from user a and b, return a string of the form short+long+sho...
A: With the shorter string on the outside and the longer string on the inside. The strings will not be ...
Q: Write Scheme expressions to define these named bindings endvalue: principle + interest
A: There are two basic components that make up every mortgage payment: principal and interest. The prin...
Q: Write a Python program with two or more functions that has three or more paramters and arguments to ...
A: import randomimport string
Q: Please justify your answer: Some sorting algorithms require extra space, apart from the space neede...
A: An algorithm is a set of instructions and rules that are required to complete a task. It gives a rou...
Q: What are the characteristics of Bluetooth
A: answer is
Q: Problem 3: What is the relation between Employee Class and Lawyer Class? What does super do in the c...
A: Employee class is the super class of Lawyer and Lawyer class is derived class of Employee class. ...
Q: Which statement reflects a legitimate benefit of phishing?
A: We need to answer: Which statement reflects a legitimate benefit of phishing? A. B....
Q: USB sticks often utilise drivers that load in order to offer a path to their contents. How would ...
A: Introduction: Malicious code inside driver can be installed from USB drive inside the operating sys...
Q: For each of the following values, specify the proper primitive numeric data type: 12 bananas
A: Introduction: For 12 bananas, the proper basic numeric data type is:
Q: Describe how the three characteristics of big data are related to data collected by healthcare provi...
A: Introduction: The first stage is to acquire big data, which can come from a variety of sources, incl...
Q: Consider the following relations about NBA: P LAY ER(pid, pname, nation). Each tuple describes a p...
A: 1 Select t.tname,r.year from TEAM t join REGISTER r on t.tid = r.tid join PLAYER on p.pid= r.pid...
Q: Write the Java statement for the following: (Statements must be properly terminated) 1. Declare x,y...
A: Primitive data types: The basic data types of a programming language are called primitive data types...
Q: The variable t after these commands t = (16:-4:1) '.^ 2 will be O a 4-element vector a 4x4 matrix O ...
A: Answer:
Q: List appropriate Worst Case Big O Notation under the different algorithms or data structure operatio...
A: To compare algorithms on the basis of running time complexity Big O notation is used.
Q: Justify the requirement for a trained project manager to oversee complicated tasks.
A: According to the question the project manager always has power to conduct something explain everyone...
Q: They are used to address the problems O principles O patterns O state O relation
A: Correct Option is Principles
Q: The Eight-Queens Problem: Place eight (8) queens on a chessboard so that no queen attacks another. A...
A: The Answer is given below step.
Q: Discuss in depth any two Artificial Intelligence application areas.
A: Artificial Intelligence Artificial Intelligence (AI) is a type of computer intelligence that mimics...
Explain.......
Step by step
Solved in 4 steps with 1 images

- Review the DonationTimeLeft function as a group. What value do you think the function will return if it is given 1300 as the argument? Write your answer below. What information do you think will be stored in time_left after calling DonationTimeLeft(1300)? Which lines of code do you think will call the AnnounceDonation function? Write the line numbers below.It is better to have functions that are specified by the user as opposed to ones that are pre-defined.Create a function employeeSalary() in such a way that it should accept employee name, and its salary and display both. If the salary is missing in the function call assign default value 40,000 to salary. Output: Employee salary is: 40,000 Employee Ben salary is: 40,000
- Functions that are user-defined, as opposed to ones that are pre-defined, are more efficient.Explain how the background process of calling inline functions varies from that of a regular function by giving an example of how it is different.Define 3 new functions of your choice and include comments on what your written function does.
- A student has a number of attributes including: stName, stNo and stMark If we have a LIST of 4 students as follow (note: select suitable representation for a student) stName stNo stMark Sami 2019205030 77.5 Ahmad 2018407080 80.5 Dana 2020607089 71 Sara 2019876545 63 - Write a function that finds the maximum mark . Your function will return stName and stMark for the student who has the maximum mark. Call your function from main program to print your result.in C++ langauge please and with the given functions. I submitted earlier and someone did it with a peek(); function which i didnt need and was confusing meExplain why invoking inline functions results in a different background process than calling a regular function and provide an example.
- The effectiveness of user-defined functions much exceeds that of pre-defined ones.2. David is used to doing programming in Python and since the print() function in Python by default prints a newline after printing the string passed to the print() function. But in his current project, he is using PHP programming language and the echo function does not print a newline by default after the end of the string. So, he often misses giving a newline after printing a message. Help David by writing a function myecho() that takes a string as a parameter and also prints a newline after printing the string.Define a getter function named totalRevenue() that subtracts budget from boxOffice and returns the result. // Code will be tested with a different movielet movie = { title: "Forrest Gump", director: "Robert Zemeckis", composer: "Alan Silvestri", budget: 55000000, boxOffice: 677900000, awards: [], /* Your solution goes here */ };

