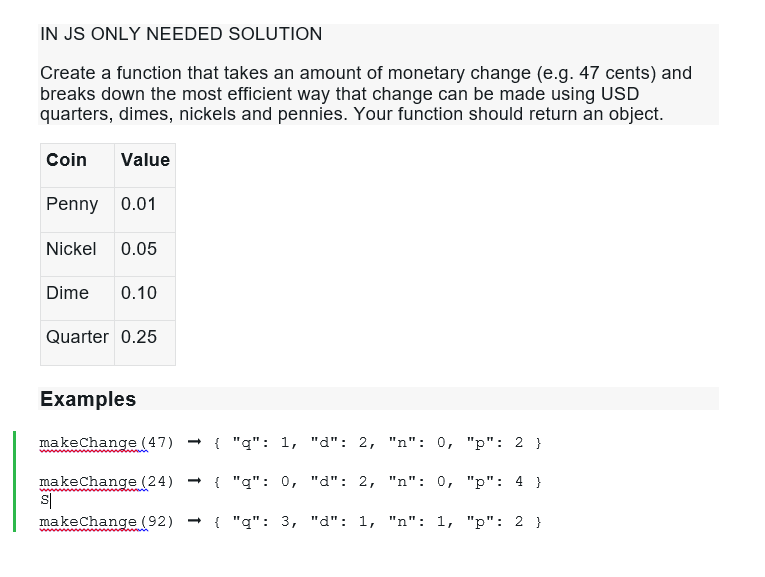
IN JS ONLY NEEDED SOLUTION Create a function that takes an amount of monetary change (e.g. 47 cents) and breaks down the most efficient way that change can be made using USD quarters, dimes, nickels and pennies. Your function should return an object. Coin Value Penny 0.01 Nickel 0.05 Dime 0.10 Quarter 0.25 Examples makeChange (47) makeChange (24) makeChange (92) S| { "q": 1, "d": 2, "n": 0, "p": 2 } { "q": 0, "d": 2, "n": 0, "p": 4 } { "q": 3, "d": 1, "n": 1, "p": 2 }
Q: The part of a program that uses a function is called thea) user b) caller c) callee d) statement
A: Function is block of statements to perform a particular task which can be used by simply calling it…
Q: Which of the following is the same ass [0 : -1] ?a) s [-1] b) s [ :] c) s [ : len(s) -1] d) s [O :…
A: Lets see the solution.
Q: Q: One of the modern devices that have (silently) crept into distributed tems are GPS receivers.…
A: The answer to the question is given below:
Q: How can the blocks get identified in the blockchain and how to modify the data in the blocks? What…
A: Blockchain consists of different blocks. The data is permanently stored in the blocks after filling…
Q: What is the first and last address in this block? 200.107.16.17/18
A: 200.107.16.17/18 in the given address: /18 means 18 : network bits in the address and 32-18 = 14…
Q: Orthogonality refers to the presence of a "backup" instruction in an instruction set design that may…
A: The CPU requires the following to function:The programme is run using the code. the reference point…
Q: What impact has the internet had on the development of different kinds of systems?
A: The Internet has turned our existence upside down. It has revolutionized communications, to the…
Q: There is an N of components, represented by the strings S1,S2, .... SN into the kitchen. The chef…
A: Input-Output Format: The first line of the input contains a single integer T denoting the number of…
Q: es to VeraCrypt and write a paragraph summarizing your results. In a second paragraph make a…
A: Introduction: The process of encoding data is referred to as encryption. This means that…
Q: What difficulties exist while working with massive datasets?
A: Introduction Big data is a method of gathering, storing, and analyzing large datasets, as well as…
Q: Do Windows machines have any potential entry points for investigators?
A: Introduction: Forensics performed on laptops collects two distinct types of data:information that is…
Q: Think about what goes into your back-up strategy and how you may improve it. Just what makes a…
A: The data in a working system may get damaged or lost over time. Important data should constantly be…
Q: If malicious traffic is redirected from one VLAN to another, it might potentially compromise the…
A: In the early stages of an assault, a nation-state finds its goal. Examining pertinent people and…
Q: A multiprocessor with eight processors has 20 attached tape drives. There is a large number of jobs…
A: operating system An operating system goes about as a go-between between the user of a PC and PC…
Q: What are the main advantages and disadvantages of cloud storage
A: Cloud computing architecture is the foundation of cloud-based data storage, which is essentially a…
Q: Explain SATA hard disk.
A: Introduced in 2003, SATA (or Serial Advanced Technology Attachment) is the standard interface for…
Q: Create a list of the top five sectors or fields associated with internet governance and provide…
A: Internet governance is 'the turn of events and application by states, the confidential area, and…
Q: Discuss OS security threats, at least 4 threats.
A: Threats When someone makes a threat to murder or hurt another person, it is considered a criminal…
Q: Using SQL data definition language, write the SQL statements to create each of the following…
A: The SQL statements to create each of the following relations.
Q: In this exercise, you are going to give a formal description of the algorithm for constructing the…
A: According to the question, we have to explain and describe the mathematical expressions for the…
Q: Consider an environment in which there is a one-to-one mapping between user-level threads and…
A:
Q: i = 2 while i < 24: j = 4 while j <= 10: print(f'{i}{j}') j = j + 3 i = i + 13…
A: The answer is solved using Python Programming language:
Q: There is an N of components, represented by the strings S1,S2, .... SN into the kitchen. The chef…
A: Algorithm: Start Read no.of test cases t Iterate through the loop t times Read n value Declare an…
Q: 2. Reading Files Create a class with a method that, given a string representing a file name,…
A: *As per the guideline I can only provide the solution for 1 question so adding the solution for the…
Q: Is it conceivable for the data breach to have a major impact on cloud security? Why should I be…
A: It certainly has an effect.Due to a data leak, an unauthorised individual has access to sensitive,…
Q: How do you create a variable with the floating number 2.8? O a. float x 2.8f O b. byte x 2.8f; Oc. x…
A:
Q: Q: One of the modern devices that have (silently) crept into distributed tems are GPS receivers.…
A: give examples of distributed applications that make use of GPS information.
Q: Q: One of the modern devices that have (silently) crept into distributed tems are GPS receivers.…
A:
Q: When compared to other branches of computer science, how does programming stand out? What criteria…
A: In basic terms, computer programming is inseparable from coding. As per a few evaluations, there are…
Q: How do the most vital parts of Phases of Compiler operate, and what are they? Each step of this…
A: Your answer is given below. Introduction :- Phases are the steps in the compilation process, whereas…
Q: When weighed against one another, what are the main upsides and downsides of cloud storage
A: Introduction: Users now have the option to exchange and access files remotely without having to use…
Q: Why should one use Java's Collection Framework, and what benefits does it provide?
A: Framework for collecting data: The implementation of generally reusable collection data structures…
Q: Several factors need to be considered in tandem to produce a compiler that is both fast and precise.…
A: Here tandem means one after other. Compiler is used to translate high level language into machine…
Q: Implement the one-time pad encryption scheme in Microsoft Excel. Your worksheet should look as…
A: The answer is written in step 2
Q: Explain how this would work.
A: The Diffie-Hellman key-exchange protocol is vulnerable to a man-in-the-middle attack by a malicious…
Q: Explain why public key encryption is more useful for securing communi-cations on the Internet than…
A: Public key cryptography's main advantage is improved data and identity security at scale. The fact…
Q: Does it make sense to restrict the lifetime of a session key? If so, give an example how that could…
A: The answer to the question is given below:
Q: How may of each type of subnet size did you need? include the unallocated subnet si
A: Here is the solution:
Q: The two variables a and b have initial values of 1 and 2, respectively. The following code is for a…
A: Introduction: Linux is an operating system available for free on the internet. In this question we…
Q: a. Find the subnet mask b. How many valid hosts are created? c. Find the first and last host address…
A: The answer is
Q: What are the many factors that must be considered while designing a compiler that generates reliable…
A: Introduction: An grasp of the target machine's runtime environment and instruction set is essential…
Q: C has a construction called a union, in which a field of a record (called a struct in C) can hold…
A: Answer : Union: Union is a user defined data type which is a collection of different variables of…
Q: When it comes to cloud computing, what are the ultimate repercussions of a data breach? In what ways…
A: Justification: Depending on the data, the ramifications might include database corruption,…
Q: How can database technology aid in the management of data as a corporate resource in a business?
A: The solution to the given question is: Data management refers to the organization, storage and…
Q: Explain the internet-related difficulties that arise within the context of each of the five main…
A: Organizations nowadays are reliant on a number of regulations controlling the protection of…
Q: Users need to be informed on how to protect themselves against session hijacking attempts. Think…
A: Session hijacking: As it sounds. An attacker may hijack a user's session, stealing their personal…
Q: This article provides both an introduction to and a summary of the IOT temperature monitoring…
A: The Internet of Things is used to link electrical devices to the internet. The devices might include…
Q: How different are conventional computers from quantum ones? What challenges must be overcome before…
A: Statement: A quantum information processing system is a quantum computer. It is a kind of computer…
Q: Assume that the address of myStr is OXOFF00 myStr: string "ABCD"
A: The answer is
Q: What are Set Associative Caches ?
A: In cache memory there are three types of mapping techniques that are: Direct cache Associative…
Step by step
Solved in 2 steps with 1 images

- IN JAVA intends to auto generate test cases for a function foo that has k integers as input arguments, i.e., foo(int n1, int n2, …, int nk). Each argument belongs to a different equivalence class, which are stored in a downloadable Eq.txt file. The content is shown below and may be modified to handle more inputs and equivalence classes. 1, 15; 16, 30 1, 10; 11, 20; 21, 30 1, 5; 6, 10; 11, 15 1, 3; 4, 6; 7, 9; 10, 12 1, 12; 13, 24 For this file, the nth row describes the nth input. Take the second row for example. There are five input arguments. The data 1, 10; 11, 20; 21, 30 indicates that argument n2 has three equivalence classes separated by the semi-colons. Develop an internal method “private int check(int val)” that returns the equivalence class the val is in. The result of check(val = 3) for n2 will be 1 and check(val = 25) for n2 will be 3. Regarding the function foo, it computes the sum of the returned values by the check function for all input arguments. Follow the contents…Q2: Write aprogram in CT' using OOP to create a class (A) , that contain the iöllowingIUnction:— (drawl) to drawa line Of Stars (Then create a class (B) , with public visibility mode inherit from class (A) ,contain the following function:(draw2) to draw the shape bellow using the tilnction (drawl),USING C++ Overload the = operator for your Rectangle class, Rectangle class is below, it should return a Rectangle in order to support multiple assignments in one line, e.g. a = b = c;. Copying from the pdfs is acceptable, but make sure you understand how it works. Overload the < and > operators in Rectangle to determine if one rectangle is bigger than the other, based on area. Demonstrate that your new operators work by writing a simple main() function to show they work. *** Rectangle Class *** Rectangle.hclass Rectangle{private:double width;double length;char* name;void initName(char* n);public:Rectangle();Rectangle(double, double,char*);//Copy ConstructorRectangle(Rectangle&);~Rectangle();Rectangle& operator=(const Rectangle&);...}; ****End of Rectangle Class**** ****Overloaded = operator, returns a rectangle by reference**** Rectangle.cpp Rectangle& Rectangle::operator=(const Rectangle& r){length = r.length;width = r.width;strcpy(name, r.name);return…
- solve the problem in java:Consider the are n=2 subjects and needed =[4,5]answered questions, to pass.The student has answered =[2,4] questions in the two subjects so far, and can answer another q=1 questions across all subjects combined. The best outcome is to answer an additional question in the second subject on order to pass it, as 2 more answers required to pass the first subject. the max number of subject s that can be passed is 1. the function must return an integer that can represent the max number of subjects that can be passed. public static int maxNumsub(List <Integer> answered, List<Integer> needed, int q){//write code here}make this code an object-oriented programming: from tkinter import *def callback(r,c):global playerif player == 'X' and states[r][c] == 0 and stop_game==False:b[r][c].configure(text='X', fg='blue', bg='white')states[r][c] = 'X'player = 'O'if player == 'O' and states[r][c] == 0 and stop_game==False:b[r][c].configure(text='O', fg='orange', bg='black')states[r][c] = 'O'player = 'X'check_for_winner()def check_for_winner():global stop_gamefor i in range(3):if states[i][0]==states[i][1]==states[i][2]!=0:b[i][0].configure(bg='grey')b[i][1].configure(bg='grey')b[i][2].configure(bg='grey')stop_game = Truefor i in range(3):if states[0][i]==states[1][i]==states[2][i]!=0:b[0][i].configure(bg='grey')b[1][i].configure(bg='grey')b[2][i].configure(bg='grey')stop_game = Trueif states[0][0]==states[1][1]==states[2][2]!=0:b[0][0].configure(bg='grey')b[1][1].configure(bg='grey')b[2][2].configure(bg='grey')stop_game = Trueif…In C++, Define a “Invalidanalyze” function that accepts an array of “Course” objects. It will return the following information to the caller: - The number of courses with empty or blank description - The number of courses with invalid negative units - The number of courses with invalid day number of the week - The total number of units for all invalid courses in the array Show how this method is being called and return proper information.
- Given two points in the plane (?,?) and (?,?), the slope of the line through them is the number ? given by?=?−? ?−?i.e. the difference in the y-coordinates divided by the difference in the x-coordinates, or rise/run. Recall the Point class defined in the series of examples found here. Below is a stripped down version of this class, with only the initializer (given), and two new class functions called slope(?,?) and colinear(?, ?, ?). The first returns the slope of the line through the points ? and ?. The second returns True if and only if the three points ?, ? and ? lie on a line.In Frac.h, extend the methods addition( const Fraction & ),subtraction(const Fraction&), multiply(const Fraction &); divide(const Fraction &); void printFraction(); by overloading operators +, -, *, /, << respectively. The concept of extend can be achieved by keeping the existing functions (e.g. addition(const Fraction &), and etc.) and design the extended functions through calling the existing functions. Add overloading operators > and < so that they can compare two FractionsWrite your own implementation file which is named Frac2.cpp to replace Frac.cpp and implement the Fraction class and the necessary overloading operators. Download the driver Frac2Driver.cpp download to test your codes. If your codes in files Frac2.h and Frac2.cpp are correct, the standard output after the execution of your program should like the following: 7/3 + 1/3 = 8/37/3 - 1/3 = 27/3 * 1/3 = 7/97/3 / 1/3 = 77/3 is:> 1/3 according to the overloaded > operator>= 1/3…Write the following program in python; There is a class with m number of students and they have n number of lessons. a)For each lesson the program has to find arithmetic,geometric,harmonic average of class b)point avarage of each student c)student numbers of highest and lowest avarage point of the class and those points too also d)for each lesson result of highest point minus lowest point e)for each lesson result of highest avarage minus lowest avarage NOTE: M and N numbers will be choosed by keyboard after.
- suppose there is a class Roster. Roster has one variable, roster, which is a list of tuples containing the names of students and their numerical grades- for example, [('Richard',90), ('Belle',67), ('Christine',85), ('Francine',97)]. Roster has a function findValedictorian that returns the name of the student with the highest grade. Find the valedictorian of the Roster object englishClass and store it in the variable valedictorian. using pythonWrite a program in C that simulates a checkout line at a supermarket. The line is a queue object. Customers (i.e.,customer objects) arrive in random integer intervals of 1–4 minutes. Also, each customer is served in randominteger intervals of 1–4 minutes. Obviously, the rates need to be balanced. If the average arrival rate is largerthan the average service rate, the queue will grow infinitely. Even with “balanced” rates, randomness can stillcause long lines. Run the supermarket simulation for a 12-hours a day (720 minutes) using the followingalgorithm:1. Choose a random integer from 1 to 4 to determine the minute at which the first customer arrives.2. At the first customer’s arrival time: Determine customer’s service time (random integer from 1 to 4);Begin servicing the customer. Schedule arrival time of next customer (random integer 1 to 4 added to the current time).3. For each minute of the day: If the next customer arrives, Say so, Enqueue the customer.Schedule the arrival time of…Suppose we're in a class called Vitamin and we have a private member variable named dosage of type double. Which one of these options is the best signature for a proper accessor function (an accessor is also known as a "getter" function)? Pay very close attention to the differences between the options. Group of answer choices A.double get_dosage() const; B.double get_dosage(const double &); C.const double get_dosage(); D.double get_dosage();

