create a truth table for a. (p^q) V~q b. r =>(p V q)
Q: Design a sequence detector circuit using the mealy model to detect when a value is not BCD, for…
A: A sequence detector circuit is a digital circuit that detects the occurrence of a specific sequence…
Q: Please detail the numerous dangers HTTPS safeguards against and the steps it takes to do so.
A: HTTPS (Hypertext Transfer Protocol Secure) is a protocol used to secure the communication between a…
Q: The architecture of a CPU may consist of a universal register, a singular accumulator, or a stack.…
A: The architecture of the central processing unit (CPU) is an important part of computer design and…
Q: File systems often use sequential media to store file blocks. Why is it crucial while working with…
A: Magnetic disks store data sequentially, such as hard disk drives (HDDs). This characteristic is…
Q: Purchases input number of drinks Restocks input number of bottles Reports inventory The…
A: The given coding practice requires you to create a VendingMachine object and perform operations…
Q: How many different types of polymorphism are there? Can you explain the key distinctions between the…
A: In object-oriented programming, there are two main types of polymorphism:…
Q: Describe an API and its relationship to system operations.
A: APIs, short for Application indoctrination Interfaces, play a basic role in modern software…
Q: Thanks to recent technological advancements, most appliances in the home are now capable of wireless…
A: What is Technology Advancements: Technology advancements refer to the continuous progress and…
Q: Create a programme that uses a single stack and a single queue to determine whether a string is a…
A: The task requires us to create a programme that identifies whether or not a given string is a…
Q: What exactly are you referring to when you say "execution flow"?
A: The phrase "execution flow" describes the order in which statements or instructions run through a…
Q: The best linkedlist has how many nodes? Which lasts longest?
A: What is linkedlist:A linked list is a data structure consisting of a sequence of nodes, where each…
Q: What is information security so crucial?
A: In order safety, often called InfoSec, is very significant due to the mushrooming trust on digital…
Q: A growing number of companies are integrating cloud computing into their data centres. Give a brief…
A: Cloud computing is a model of IT let go where the apps and data are hostedOn a system of remote…
Q: If possible, please describe at least three distinct examples of the responsibilities held by the…
A: The Win Main function is the entry point to a Windows-based application, replacing the primary role…
Q: When compared to other forms of network traffic, why are voice and video calls treated differently?…
A: Voice and video calls are often treated differently from other forms of network traffic due to their…
Q: Describe how developments in Very Large Scale Integration (VLSI) technology have enhanced the…
A: Developments in Very Large Scale Integration (VLSI) technology have played a pivotal role in…
Q: Q) You want to design an arithmetic comparison combined logic circuit. (a) List the steps that you…
A: We have drawn a logic diagram with gate using the AND, OR, NOT gates. so we will see in the more…
Q: Stuck on this problem, in java pls. Write a void method selectionSortDescendTrace() that takes an…
A: To implement a method which sorts the passed array in descending order using selection sort and…
Q: Q14: Ayşe attaches his laptop to campus network with wired connection, opens his browser and…
A: In today's digital age, accessing web pages and online content has become an integral part of our…
Q: Compare cloud computing to mobile devices. Cloud computing allows for substantial mobile device…
A: Cloud compute plus mobile devices are two divide but more and more entwined technology areas. Cloud…
Q: Create the truth table for F2 without simplifying the expression F₂ = ABC + ACD + ABC
A: A truth table is a table used in logic to display all the possible combinations of truth values…
Q: Characteristics of Unified Communications Systems? For what purposes do businesses use them?
A: => Unified Communications (UC) systems refer to a suite of integrated communication and…
Q: What is Amazon's enterprise system for its cloud computing platform?
A: Amazon's enterprise system for its cloud computing platform is known as Amazon Web Services (AWS).…
Q: D
A: Setting up a big grid computing project such as the Large Hadron Collider (LHC) is a complex…
Q: By carefully designing compilers and assemblers, the order of assembly language instructions can be…
A: Content: The primary role of a compiler in a computing surroundings is to change code written in a…
Q: ROM and RAM are the two primary components of a computer's main memory.
A: What is ROM and RAM: ROM stands for Read-Only Memory, a non-volatile memory used to store permanent…
Q: Provide your opinion and an example of where mainframe computers and mid-range servers should be…
A: processor computers are large, healthy systems that can swiftly grip and analyze large Volume of…
Q: Two String values are passed as input. Find if the second string s2 is a substring of the first…
A: Start the program.Define the isSubstring function that takes two string parameters, s1 and…
Q: Certain databases will only utilise the magnetic disk's outer tracks, leaving the inner tracks…
A: There can be some benefits for using the outer tracks of the magnetic disks leaving the inner tracks…
Q: Why a database? Databases are smaller. Databases show relationships. Databases automatically encrypt…
A: Databases are powerful tools that offer numerous advantages over traditional methods of data…
Q: Give me user requirements and System requirements specification based on the scenario given below.…
A: The purpose of this requirements specification is to define the user requirements and system…
Q: Which Qualys sensors collect the type of data needed to perform vulnerability assessments? Select…
A: Vulnerability assessments are crucial for maintaining the security of systems and networks. They…
Q: How can various technical solutions help find intrusions in a network?
A: Technical Solutions for Network Intrusion DetectionNetwork intrusion refers to any unauthorized…
Q: Use the following confusion matrices to answer Questions 4 – 13. Please note that some of the…
A: Highest Recall Rate (also known as Sensitivity or True Positive Rate): Recall rate measures the…
Q: After listing the different cloud computing services, the following part explains how organisations…
A: Organizations utilize cloud computing to manage their resources in a variety of ways. Here are some…
Q: When compared to one another, the Internet and the World Wide Web (WWW) have a number of…
A: The Internet and the World Wide Web (WWW) are two terms that are often used interchangeably, but…
Q: Provide an example of a context in which one of the four potential access control mechanisms may be…
A: What is potential access control mechanisms: Potential access control mechanisms refer to different…
Q: Describe the evolution of the Internet as well as the technological infrastructure underlying its…
A: The Evolution and Infrastructure of the InternetThe Internet, a global network connecting millions…
Q: Given an array of integers, find the maximum sum of any contiguous subarray. Example: Input: [-2,
A: I have done the code using Python 3, Make sure you are on latest version of Python.
Q: I am not recieving correct answers for the previously submitted questions. Please follow the…
A: The C++ code is given below with detailed analysis and output screenshot
Q: What are the various types of polymorphism that are possible? What are the most significant…
A: The idea of polymorphism in object-oriented programming ( also abbreviated as OOPs ) enables…
Q: Give some examples of Phantom's and Dirty's rule-breaking behaviour.
A: Phantom Reads occur in a data base when a transaction (T1) reads records…
Q: What purpose does the information security management system serve?
A: A organization for management information security (ISMS) is a systematic approach to managing…
Q: The size of the largest linkedlist in terms of the number of nodes it contains is unknown. Is there…
A: A linked list is a popular data structure used in computer science and programming to store and…
Q: A deque DQUE is to be implemented using a circular one-dimensional array of size N. Execute…
A: Define a circular array of size N to hold the elements of the deque. You'll also need to keep track…
Q: Why must audio and video traffic be managed differently than other network traffic types? What would…
A: audio and video traffic must be managed differently from other network traffic types due to their…
Q: Data representation and archiving. Each BI tool may be used in conjunction with a shared database.
A: Data symbol in BI tools refers to transforming uncooked data into an easily unspoken and analyzed…
Q: What does it mean when someone says they have a "Access Point" for their WiFi network? Have you…
A: When someone claims to have a "Access Point" for their WiFi network, they are referring to a piece…
Q: Does the HTTP determine how a web page is interpreted by a client?
A: The HTTP (Hypertext Transfer Protocol) is a protocol used for communication between a client and a…
Q: Is it possible to foresee circumstances in which default values enhance data integrity and others in…
A: Yes, it is conceivable to anticipate both scenarios in which default settings will improve data…
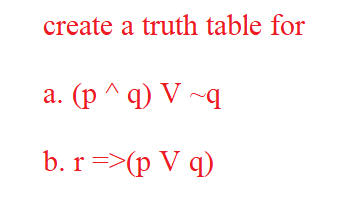
Step by step
Solved in 3 steps

- Make a truth table and determine the truth value of [p∧(r→q)]→(q∨∼r) given that p is true, q is false, and r is true.Show that (p ∧ q) → r and (p → r) ∧ (q → r) are not logically equivalent, without using truth tables.Without using truth tables, show that ¬p ® (q ® r) and q ® (p Ú r) are logically equivalent.
- Are "p ∨ q ∧ r" and "(p ∨ q)∧(p ∨ r)" logically equivalent? Show your truth tableUsing a truth table, show that P ↔ Q is logically equivalent to (P ∨ Q) → (P ∧ Q).Part 1: Truth Tables (1a) Provide complete truth tables for each of the following 1. ¬ (P ∨ Q) ∨ (P ∧ ¬Q) 2. (P ↔ ~Q) ∨ (P ∧ ~Q) 3. ¬¬(¬P ∧ ¬Q) 4. [(P ∧ Q) → R] → ¬(P ∨ Q) 5. [(P ∧ Q) ∨ R] ↔ [(P ∨ R) ∧ (Q ∨ R)] Can you please solve this Thank you



