Create it.!
Q: Give advice on how to maintain a secure wireless network in your house.
A: What is wireless network? Wireless network is a network set up by using radio signal frequency to…
Q: Let's imagine there is only place for one additional student in the course, but two people wish to…
A: Both students can't take the last seat that's open in a database system because in the database each…
Q: Why did you choose Microsoft Excel over the other choices you had?
A: Microsoft Excel is a calculation sheet created by Microsoft for Windows, macOS, Android and iOS. It…
Q: Trace the following code: class Natural: definit__(self, val): self.val= val @property def val…
A: Program Trace Consider the below statement: r = list(range(1, 10, 2)) This will create a list…
Q: Is it feasible for a business to deploy social computing, a system of technology that incorporates…
A: Solution: Social computing is a network that describes the way individuals communicate their…
Q: Reverse Polish Notation (RPN) is a mathematical notation where every operator follows all of its…
A: In this question we need to write a code to convert algebraic expression into reverse polish…
Q: An attack that degrades a system is referred to as
A: A degradation of service attack is a kind of forswearing of administration (DoS) assault intended…
Q: Get a selection of reviews and reports on the four major personal productivity software packages…
A: Suitable applications for productivityThe Google Suite is an all-inclusive alternative to Microsoft…
Q: It is generally accepted that database architectures
A: A three-tier architecture offers a number of benefits over a two-tier architecture. First, it allows…
Q: Look closely at how Windows and Android were created using very different approaches to software…
A: The operating system of a computer is the software that enables the machine to function. It enables…
Q: What procedures are used to assess an individual's degree of risk?
A: What is a risk assessment?In short, a risk assessment is an examination of a task you perform at…
Q: To put it another way, what does "Internet 2" really mean and how does it work?
A: Solution Internet 2 Internet 2 is a US based non profit network community led by researchers,…
Q: You must be aware of downgrade attacks and know how to defend against them.
A: Attacking with less priority:It is a specific kind of cryptography attack against a computer system…
Q: Which is a correct implementation of the Checking Account constructor?
A: Answer:- E) I, II and III
Q: Why will the existing environmental conditions cause American businesses to face new challenges? How…
A: Business environments change frequently and require consideration when planning and conducting…
Q: When a company's security is compromised online, what are the repercussions?
A: Answer Here's a brief rundown of five of the most serious consequences of data breaches. Continue…
Q: Does hiring software service providers to handle your IT demands sound like a smart idea? There must…
A: In the present environment, organisations should think about outsourcing their technical…
Q: Explain Asynchronous Time Division Multiplexing in detail? Also discuss its advantages over…
A: What is Time Division Multiplexing – TDM? Time-division multiplexing (TDM) is a communications…
Q: Parallel processing allows a computer to simultaneously work on subparts of a problem. Select…
A: Parallel processing is a method in which two or more processors are runto handle separate parts of…
Q: other way, what does "Internet 2" really mean and how does it work?
A: Introduction: The Internet is a vast collection of interconnected computer networks spanning the…
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a…
A: The answer is
Q: python Write a function called has_odd that accepts a set of integers as a parameter and returns…
A: Hello student :-
Q: Focus on the positive aspects of cloud computing and contrast them. Knowing the risks associated…
A: Introduction: A scalable online environment provided by cloud computing makes it possible to manage…
Q: The manner in which coherent and non-coherent psk demodulators demodulate signals varies.
A: According to the information given:- We have to describe coherent and non-coherent psk demodulators…
Q: Four sources of vulnerability intelligence should be taken into account. Which do you think is the…
A: Vulnerability Intelligence : Vulnerability Intelligence is a particular type of danger insight…
Q: The impact of information technology on society at large and on our daily lives Describe both the…
A: The response is provided below. One way that science has had a long-lasting effect on society is by…
Q: Exist distinct methods of processing things? Which are and which are not in a line?
A: - The query inquires as to whether there are several processing methods. Furthermore, describe…
Q: Several things can trigger a downgrade attack.
A: Introduction: Downgrade attacks can be used to carry out cryptographic assaults that would otherwise…
Q: iscuss the importance of firewalls in protecting the privacy and security of your network. Give…
A: Fencing your property protects it and keeps intruders out. Firewalls are similarly used to secure…
Q: What qualities do computer graphics need to have in order to function properly?
A: Computer graphics is a sub-field of software engineering which reads up strategies for carefully…
Q: Do you have any experience writing about the Internet? What components of the Internet…
A: Introduction The operation of the internet: The internet operates through a packet routing network…
Q: To what extent does employee contentment in their jobs determine a company's fortunes?
A: According to studies done by researchers at the University of Warwick, happy workers are around 12…
Q: Briefly describe the nonvolatile solid-state memory technologies that are becoming more popular.
A: Given: nonvolatile memory composed of solid-state components.Data storage that is not susceptible to…
Q: What is the significance What are the advantages teaching tool? of Microsoft Powerpoint in today's…
A: One of the most significant presenting tools is Microsoft PowerPoint. Presentation is an essential…
Q: Every year the Loebner prize is awarded to the program that comes closest to passing a version of…
A: In the 2018, September 8 Loebner Prize was announced. And as of now, the Loebner Award given to the…
Q: why a wireless connection will not lead to security issues in the network when using an Adhoc…
A: It is defined as a network is one that is spontaneously formed when devices connect and communicate…
Q: Microsoft may no longer update or fix Windows Server, but it is still likely installed on hundreds…
A: Answer: When a vendor quits supporting a piece of software or hardware technology, there are serious…
Q: Please provide definitions for worm, computer virus, and trojan horse. Which viruses mostly depend…
A: Malware is software that has been built with the intent to do damage to your computer system or the…
Q: This is not a coding question, yet the answer you gave me is a set of code This is just Simulation…
A: Consider the scenario where we need to generate a sequence of random two-digit numbers. First,…
Q: What justifies vulnerability assessments, and how are they carried out?
A: Vulnerability evaluations are important for many reasons: Finding weaknesses before hackers. VA…
Q: Please answer the question in C++ only Given an integer N, let us consider a triangle of numbers of…
A: Algorithm - Take input from user. Now use the below logic - return s.replace(" " + w, "");…
Q: Should we use an asynchronous or synchronous bus to link the CPU and memory? I'd want to hear how…
A: In this section, the CPU and memory are connected through an asynchronous or synchronous bus. A bus…
Q: Let's assume your company's mail server notifies you that your password has changed and that you…
A: Two types of attacks are: Phishing: Phishing is a type of attack in which the user receives a…
Q: The ____ is a digital circuit that generates timing pulses, or signals, and transmits the pulses to…
A: Computer clock: A clock is a microchip that is used to regulate the timings and speed of all…
Q: What should you do to defend yourself in the event of a downgrade attack?
A: Introduction:Downgrade attack: This is a form of cryptography attack against a computer system or…
Q: Which of the following uses for Excel's features would you make?
A: Here is the solution: She questioned Excel: Excel is a crucial tool for the company. This helps in…
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms…
A: the answer is an given below :
Q: It is important to describe how metrics are used to assess the process and final product quality of…
A: The above question is solved in step 2 :-
Q: Consider a piece of online banking software that includes a hidden function that allows the…
A: Start: We are going to explore whether or whether someone (the developer) has incorporated a hidden…
Q: Given the 8-bit binary number: 1 1 0 0 1 1 0 1 What decimal number does this represent if the…
A: The above question is solved in step 2 :-
Create it.!
Step by step
Solved in 3 steps with 1 images

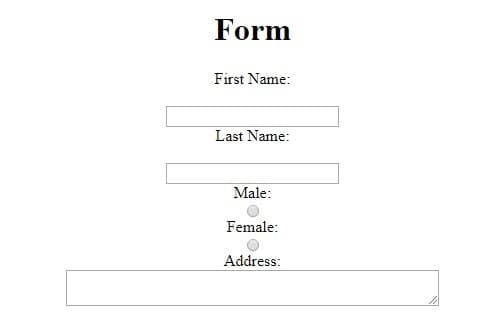
- Window 1Should have a welcome message, a textbox to receive AN EXISTING ID of the user and a button to access the data base. All users ID should be saved in a data base (Don’t use access). Once the Id is verified then the program will give the user access to the main menu window.Your database should have the following columns.Window 1Should have a welcome message, a textbox to receive AN EXISTING ID of the user and a button to access the data base. All users ID should be saved in a data base (Don’t use access). Once the Id is verified then the program will give the user access to the main menu window.Your database should have the following columns. Use SQL/mySQL to create the database and Netbeans as the IDE.<input type="text" id="number" placeholder="Choose from item 1-9"> write a java script code that makes sure once the user enters a number 1 through 9 it is valid for example if the user puts 10 it says "its invalid" under the box in html if they put 3 then it says its valid!
- TEMPERATURE CONVERTER WEBSITE The user will input a temperature in either Fahrenheit or Celsius and press a "convert" button. The converted temperature will then be displayed with the correct unit. Your Ul should include four main elements: Input field for the user to type in their temperature - don't forget to validate that the input is a number! Dropdown menu or radio button for the user to choose if they are inputting in Celsius or Fahrenheit "Convert" button to trigger the temperature conversion Display area for the final converted temperature and unit For an extra challenge: You can add in a third conversion option to convert from and to Kelvin as well. please Don't Copy from internetReview the customer requirements Customer Requirements: The customer needs an application that creates a report telling how many months it will take to pay of a loan given a loan payment. The application will accept a client’s loan amount and monthly payment amount. It will then output the customer’s loan balance each month until the loan is paid off. The report should not have any negative numbers (the final month should reflect a balance of $0). Display the month and remaining balance for each month until paid off. In addition, the program should display what the original loan amount was. Review the example IPO below. Open Flowgorithm and save with the required naming conventions in the “Lab Task Checklist” and remember to enter your Program Attributes. Use Flowgorithm to create the algorithm meeting the customer requirements Make sure you are using the correct datatype Use prompts to describe required input before asking for input Test using the IPO test…consumers for residential housing. Your task is to create an application to be used by the loan officers of the company when presenting loan options to its customers. The application will be a mortgage calculator that determines a monthly payment for loans. The company offers 10-, 15-, and 30-year fixed loans. The interest rates offered to customers are based on the customer’s credit score. Credit scores are classified into the following categories: Table 1: Credit Score Categories Rating Range Excellent 720-850 Good 690-719 Fair 630-689 Bad 300-629 The program should initially prompt the user (the loan officer) for the principle of the loan (i.e. the amount that is being borrowed). It should then ask him or her to enter the customer’s credit score. Based on the customer’s credit score, the program will randomly generate an interest rate based on the following ranges: Table 2: Interest Rate Assignments…
- write row_echelon_form method using elementary operator NOTE: Explanation is must and do not copy from other websites ( I will directly downvote)Which class is used to create a badge? .label .badge .tag .flaghi I have no idea what to do here Write a Java GUI application that will keep track of student results at a local college and save the process result into a database. The application must contain the result that a student has obtain for a test, assignment and exam. Question 1 On the form create a list box that will allow the user to select the student ID populate populate from the text file. Also create a search button when clicked will display the average , highest and lowest result according to the student number and a Save button to save the result to an online data base. Student number should be used as a primary key for your database. Question 2 Create a sequential file (student.txt) that contains data for the following fields The student ID number The student test result The student assignment result The student exam result Question 3 Load the data from the student.txt file and populate the list box with the student numbers Question 4 Calculate the average result…
- Q2) Answer true or false and correet the answer for the following question, 1- If age >= 13 And < 20 Then ttOutput. Text - You are a teenager." 2- The Caption property is used to enter or edit text during program execution.. 3- OLE is used to join VB with database application. 4- The command button is the most important button used to execute code. 5- The methods are used to change the behavior of tool.HTML and JSP You will create a simple Job application app. The user enters their first name, last name, phone number, email, and their skills. When the user clicks submit, your app should check that the fields are not empty. If a field is empty, it will indicates in red that the field is required. If all fields contains data, then when the user clicks submit, it will present the same information for the user to review. In the review page, if user thinks the information is incorrect, they can click "back" to go back to application form. Otherwise, the user can submit the application by clicking on "submit." After the application has been submitted, a thank you page including the applicant's is displayed.A control's visibility on the form is controlled by its associated attribute during runtime.









