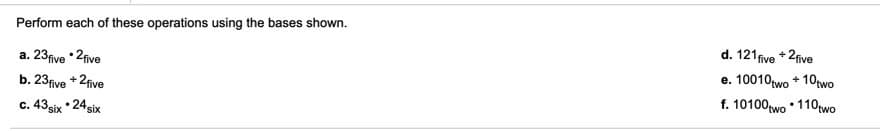
d. 121five + 2five e. 10010wo + 10two f. 10100wo • 110rwo Perform each of these operations using the bases shown. е. a. 23five •2five + 2fve b. 23five c. 43six • 24 six
Q: 4. Given one 4-digit hex number a and b, how many bits of storage space is needed to store a? a+b ?…
A: - The question is to identify the bits space of storage space required for the number, addition and…
Q: X=(101), is converted into Y=(145), , where a and b are the bases of X and Y. The numbers X and Y…
A: Multiply the decimal number with the base raised to the power of decimals in result:24.250×81 = 194…
Q: A computer word has n=36 bits and 9 bits are used for exponent of real numbers. (a) What is the…
A: a) range is -255 to 256 b) precision is [-2.136e77 +2.136e77] =1/255
Q: Explain how to multiply two complex numbers, a + ib and c+ id, using just three multiplications of…
A: Introduction: A complex number is any number that can be written as a+bi, where i is the imaginary…
Q: In CRC, bits in divisor are the CRC Redundant bits Select one: O a. More than O b. Equal to O c.…
A: CRC: CRC Stands for Cyclic Redundancy Check it is used to check the error in the raw data when raw…
Q: Perform the following operations in the Galois field used in AES. Remember that each byte represents…
A: 42hex + 5Chex 7Ahex x 2Bhex
Q: We reviewed bitwise logical operations in C (&=AND, |=OR, ^=XOR): A = 0011 1100 B = 0000…
A:
Q: 2). 4o111.00) - (1111. 4), using 2's Com Plemut: Gre4 Gro
A: First, convert the gray code into binary form Second, subtract the two binary equivalents using 2’s…
Q: Q. If 8 Bits are equals to 1 byte then how many bytes can be formed in 67464 Bits?
A: This question is related to computer architecture.
Q: b a The following binary numbers are 4-bit 2's complement binary numbers. Which of the following…
A: Overflow in Addition: By adding two complement numbers with the same sign (both positive or both…
Q: Consider the string of data '&'. The ASCII value of data & is 26 H which has to be moved from source…
A: Dear Student, The for Calculating source address we use the SI, DS and for Calculating destination…
Q: 5. Compute FIRST and FOLLOW for the following gramma S→ aAB | CD A → CD | SE | & B → aSB | AS C→ CC…
A: FIRST and FOLLOW of the grammar
Q: (a). Explain how many words are to be generated from 128 bits main key in AES. (b). how many bytes…
A: the answers are given below
Q: 3. What percent error we would have in representing the value = 0.345678 in a computer where we can…
A: Answer: I have given answered in the handwritten format in brief explanation
Q: 7. Assume that X consists of 3 bits, x2x1x0. Write boolean algebra functions that are true if and…
A:
Q: b = mod(24,5) b = 3 O b =6 O b =5 b =4
A: mod is the built-in function available in matlab to find the remainder that was obtained after…
Q: 7. Given a text file that contains 50 characters as follows. Use Huffman coding to encode these…
A: Huffman coding is used for file compression. In this method, highest occurrence characters are…
Q: Suppose we want an error-correcting code that will allow all single-bit errors to be corrected for…
A: According to the question, we have to find parity bits are necessary to an error-correcting code…
Q: 1. (A V B), ~(A & C), ~BH (CƆ D)
A: Posting only first answer as it contains many questions.
Q: .ORIG x3005 LD R7, D LD R7, C LD R7, A D LD R7, B HALT .END The following bit pattern is loaded into…
A: Dear Student, Here the values passed in LD R7, D are hexadecimal values where D = 1101 in binary…
Q: Answer the following short questions briefly. Convert the following decimal integers into binary,…
A: AS PER OUR POLICY “Since you have posted a question with multiple sub-parts, we will solve the first…
Q: 1. It is guaranteed that a _--- has at least 8 bits and a has at least 16 bits. A. bool, char B.…
A: Size of the primitive data types is as follows: Where 1 byte = 8 bits size of the bool data type is…
Q: Suppose we want an error-correcting code that will allow all single-bit errors to be corrected for…
A: Below is the answer to above question. I hope this will be helpful for you.. .
Q: 21. Suppose we want an error-correcting code that will allow all single-bit errors to be corrected…
A: As i have read guidelines i can provide answer of only 1 part of questions in case of multiple…
Q: A computer architecture uses 6 bits for exponent and 9 bits for fraction and 1 bit for the sign. a)…
A: The brief solution of your question is given below
Q: 2) Describe the order of magnitude of each of the following code sections, using Big-O notation: a)…
A: We have to find the time complexity of the given codes and the order of them. Here is the…
Q: ion is c ewm the bse The given arthmetc opere least one mumber ssiem INw in the operation
A: The answer for given arithmetic operation is correct at least one number system the base in the…
Q: Consider the string of data '#. The ASCII value of data # is 23 H which has to be moved from source…
A: The memory is divided into four segments: Code Segment (CS) Data Segment (DS) Stack Segment (SS)…
Q: Please please don't copy Computer Science for BCH (16,12). when input is (0, 4, 14, 14, 4, 4, 15,…
A: Answer is given below-
Q: rray X[-10...5, on is at 250. If 54 byte of space der then what will
A:
Q: Addition, subtraction, and multiplication are binary operations on _________ I. Z II. Q III. R…
A: - We need to choose the right option for the right operation. - We have Z,Q,R and N denoting…
Q: A. How many bits are needed to represent 214(octal) in binary?
A: As per the guidelines, we are only allowed to answer 1 question at time.
Q: QUESTION 15 6.3a Using C(..., ...) notation, write out a formula for the number of bitstrings of…
A: Here, the arrangement of bits is not mattered because a number of 0s are asked instead of the order…
Q: Q1. Calculate the following number conversions, complements and arithmetic operations: (xx=58) a)…
A: As per our guidelines we can answer only maximum 3 question so post another one seperately.
Q: (b) Convert the following hexadecimal numbers to binary: (i) 111111 (ii) 101 (c) How many bits are…
A: a) Convert the following hexadecimal to binary (i) 111111 Ans: 000100010001000100010001 In…
Q: 11) All binary numbers are made up of 0s and 1s. (Is it a T or a F)?
A: The answer is given below.
Q: s[0]=7;s[1]=0;s[2]=-12;s[3]=9;s[4]=10;s[5]=3;s[6]=6; the value of [s[6-s[5]]is:
A: s[6-s[5]] = 9
Q: Consider the 1-bit ALU, shown below: Car Camyou Write down the values of ALU control bits (Ainvert,…
A: Truth Table to Solve the Problem: -
Q: a. If rl-Ob00010100, then what is the value of r2 when CPU execute the following operations? 1. LSL…
A: given r1 = 0b000101001. LSL r2,r1,#3 i.e logical shift left by 3hence r2 = 0b10100000 ; three first…
Q: Q10: List the priorities of the arithmetic operations. Q11: Find the value of A for the following: A…
A: Priority list of Arithmetic operations: Bracket Division/multiplication addition/subtraction…
Q: of 16-bit, if the result is negative applg 8/write progrmm to sbtrnct two nunbers each 1program of…
A: program to substract 2 number each of 16-bitgiven below
Q: • c. Discuss steps to writing and reading in the memory • d. Convert the following binary number to…
A:
Q: 11. Translate the following code into MIPS. Assume that a=$a0 and b=$al are integer arrays whose…
A: # a = $a0, b = $a1, n = $a2 li $t0, 0 # i = 0 for: bge $t0, $a2, end # for (i < n) ble…
Q: 2. For a computer that uses 8-bit word size and Signed Magnitude (SM) arithmetic to represent…
A: a) To get a magnitude representation we need to divide the number with 2. 29 in sign magnitude…
Q: 5. What is the largest decimal number that can be represented using 6 bits? (a) in binary system (b)…
A:
Q: Assume you have a word of 16 bits; what would be the equivalent value in terms of Bytes, Nibble and…
A: 1 Word = 16 Bits 1 Byte = 8 Bits 1 Nibble = 4 Bits
Q: You need to show detail work on how you get the answer. Dont use answers from other websites…
A: Answ given below:-
Q: 2. Add-4.63 x 10 to -5.96us x 10', assuming that you have only three significant digits, first with…
A: The answer for the given question is given below:
Q: 1. Calculate the sum of series of odd numbers from the list of numbers. The length of the list is in…
A: Assembly program is written. you will have to enter numbers into memory locations specified above.…
first three. I have asked the rest three separately.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Copy the contents of x3500 into x3512. Assume your code is loaded in x3550. [x3512] = [x3500] 0011 0101 0101 0000 ; start x3550 0010 101 1 1010 1111 ; x3550 ; R5 = [x3500] 0011 101 1 1100 0000 ; x3551 ; [x3512] = R5 Target = x3500 - PC+1 = x3551 ================= PCOffset = xFFAF = 1111 1111 1010 1111 b PCOffset9 = 1 1010 1111 Target = x3512 - PC+1 = x3552 ================= PCOffset = xFFC0 = 1111 1111 1100 0000 b PCOffset = 1 1100 0000 Based on the above example swap the contents of x3200 and x3201. Assume your code is loaded in x3250.extern "C" int f(int *,int,int); int a[2][2] = {{11,12},{21,22}}; void setup(){ Serial.begin(115200); while(!Serial); delay(500); int *arr = (int*)a; Serial.println(f(arr,2,2)); } void loop(){ } .global f f: ldr r3,[r0] // get first element mov r2,#0add r2,r3 mov r1, #3 lp: add r0,#4 // add next elementldr r3,[r0]add r2,r3sub r1,#1 bgt lp mov r0,r2 bx lr Describe what operation is being performed in this code18. In this instance, dirty reads are disallowed, while nonrepeatable reads and phantom reads are allowed. a. Read committed b. Read uncommitted c. Repeatable read d. Serializable
- Use C/C++ Write a program to store n integers in a chained hash table of 9 memory locations. Use h(k) = k mod n. The program can do jobs as follows: a) Add a number to the table. b) Print out the hash table. c) Search for a given value. d) Remove a number from the hash table.which instructions best apply to the following prompt Implement an open addressing hash table to store a list of integers. Your task is to handle collisions using open addressing and implement basic operations such as insertion, deletion, and searching. The open addressing technique you will use is linear probing.1.use open addressing2.implement this in python3.use double hashing 4.use linear probing5.implement an open addressing hash table to store integers1. A computer department is assigning random computers to faculty members attaching an ID number to each of them. The ID numbers include 2 letters of the English alphabets, followed by a 5-digit number, for example “CD95368”. There are no restrictions on letters or digits. How many different ID numbers can be created using this format? 2. In the previous question about ID numbers, how many can be created if the repeatation of letters is not allowed and the digit 0 is not allowed to be used?
- #include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){ char Email_id[60]; int i;//p1=0,p2=0; printf("Enter your Email_id: "); scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.') { printf("Your Email_id is valid"); } else { printf("Email_id invalid.Please enter a valid id."); } } int loginUser(char email[], char pass[]){ //Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){ //Write your code here} void searchByName(char name[]){ //Write your code here} void searchByAddress(char address[]){ //Write your code here} int main(){ while(1) {…#include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){char Email_id[60];int i;//p1=0,p2=0;printf("Enter your Email_id: ");scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.'){printf("Your Email_id is valid");}else{printf("Email_id invalid.Please enter a valid id.");} } int loginUser(char email[], char pass[]){//Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){//Write your code here} void searchByName(char name[]){//Write your code here} void searchByAddress(char address[]){//Write your code here} int main(){while(1){printf("*******************************************************************\n");printf("1. signup User. 2. login User. 3. build User Profile.…#include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){char Email_id[60];int i;//p1=0,p2=0;printf("Enter your Email_id: ");scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.'){printf("Your Email_id is valid");}else{printf("Email_id invalid.Please enter a valid id.");} } int loginUser(char email[], char pass[]){//Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){//Write your code here} void searchByName(char name[]){//Write your code here} void searchByAddress(char address[]){//Write your code here} int main(){while(1){printf("*******************************************************************\n");printf("1. signup User. 2. login User. 3. build User Profile.…
- #include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){ char Email_id[60]; int i;//p1=0,p2=0; printf("Enter your Email_id: "); scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.') { printf("Your Email_id is valid"); } else { printf("Email_id invalid.Please enter a valid id."); } } int loginUser(char email[], char pass[]){ //Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){ //Write your code here} void searchByName(char name[]){ //Write your code here} void searchByAddress(char address[]){ //Write your code here} int main(){ while(1) {…Consider the following list:6, 25, 32, 39, 65, 77, 88, 99, 110, 124, 130Using the binary search, how many comparisons are required to determine whether the following items are in the list or not? a. 5 b. 25 c. 30 d. 65 e. 77 f. 110 g. 134me remaining: 00:09:34 Computer Science Create a MPI version of the program below that uses a striped decomposition. Each process is responsible for some number of columns of the square and also maintains two columns of ghost cells to mirror the columns on the neighboring processes. The ghost cells are needed in order to update the cells along the process boundary. At each time step, a ghost cell exchange takes place, then the update takes place. #include <stdlib.h> #include <assert.h> #include "anim.h" const int n = 200; // number of discrete points including endpoints int nstep = 200000; // number of time steps int wstep = 400; // time between writes to file const double m = 100.0; // initial temperature of rod interior const int h0 = n/2 - 2, h1 = n/2 + 2; // endpoints of heat source const double k = 0.2; // diffusivity constant char * filename = "diff2d.anim"; // name of file to create double ** u, ** u_new; // two copies of the temperature function ANIM_File…

