DESTINATION San Francisco New Orleans Atlanta REG. PRICE 550.00 330.00 295.00 REDUCED SALE PRICE 495.00 55.00 33.00 59.00 297.00 236.00
Q: Name the four most common categories of fundamental data.
A: Elementary data items An object that cannot be segmented into smaller components is referred to as a…
Q: Despite the common perception that software is plagued by flaws, the aerospace industry has been…
A: The aerospace industry has a reputation for developing software with a very low failure rate due to…
Q: Can you name any situations when SSH might be useful? If you hear the letters SSH, what do they…
A: Introduction: SSH (Secure Shell) is a cryptographic network protocol used to secure remote login…
Q: USE SIMPLE PYTHON CODE PLEASE 2) Advanced version with more than two levels of processes The master…
A: Algorithm: 1. Initialize a shared result object 'result'. 2. Create 7 processes p1,p2,p3,p4,p5,p6…
Q: Information security organisations with established codes of conduct are catalogued in this chapter.…
A: Given: The Association of Computing Machinery, often known as the ACM, was founded in 1947 as "the…
Q: It's worth noting that the file deletion algorithms used by Symbian, Android, and the iPhone are all…
A: The statement "It's worth noting that the file deletion algorithms used by Symbian, Android, and the…
Q: The following are the three pillars upon which every functional and productive network is built: How…
A: Introduction: A network is a collection of computers, servers, mainframes, network devices,…
Q: The solution to the recurrence T(n) = 4T(n/2) + n turns out to be T(n) = e(n). Show that a…
A: Required Proof: Assuming T(n) < c*n^2 for some constant c, we can substitute it in the recurrence…
Q: The Compiler's complex process: how does it work? Could you provide me an example of how this works…
A: Answer: A compiler is a software application that converts developer-written high-level source code…
Q: Explain the eight fundamental ideas of computer architecture.
A: The following are the top eight concepts in computer architecture: Moore's law design
Q: Clinicians must now store patient data in databases accessible from many places for certain…
A: The answer is explained in the below step
Q: Suppose memory cell 5 at address 5 has the value 8. What is the difference between writing the value…
A: Several stages, such as fetching the opcode, reading and writing to memory, are necessary to carry…
Q: Why define separate data types for undirected graphs, directed graphs, edge-weighted undirected…
A: Data types: Data types define the type of data that can be stored and manipulated within a computer…
Q: Is there a list of three things that a network must do in order to function properly? In only a few…
A: Network:- A network is a group of connected computers, servers, mainframes, network devices,…
Q: Programming Exercise 2 :- COPY A STRING IN REVERSE ORDER Write a program with a loop and indirect…
A: Introduction Assembly language: Assembly language is a low-level programming language that is used…
Q: Someone from the outside world (10.1.2.3) attempts to open a connection from port 5150 on a remote…
A: The success of the attack depends on the security measures and configurations in place on the Web…
Q: Explain the eight fundamental ideas of computer architecture.
A: The following are the Eight Great Concepts in Computer Architecture: Design for Moore's law Use…
Q: Answer the following: 1) What is the negation of this proposition? "Either a > 0 or a is a…
A:
Q: Analyze and evaluate various software testing strategies. The quality of software is impacted by…
A: Introduction: Software testing is a critical process in software development that helps ensure that…
Q: Expalin illustrated Software engineering—why? Its importance in software development
A: Software Engineering is the study and practice of engineering as it pertains to the construction,…
Q: This assignment will require you to implement a generic interface (Queue) with an array based queue…
A: Implementation of the QueueArray class that implements the Queue interface, with TODOs replaced with…
Q: Describe a graph model that represents whether each per- son at a party knows the name of each other…
A: Please refer to the following step for the complete solution to the problem above.
Q: The fundamental capabilities of Phases of Compiler are as follows. Provide an explanation of each…
A: Compilation phases: Each step begins with a source programme and concludes with a different output…
Q: Be as specific as you can in your response to the question below. Can you explain what BCMP is and…
A: Introduction: A server is a computer system or a software program that provides resources or…
Q: Why do we have bugs? How does a flaw get into code? Provide a few specific examples.
A: Bugs in software code can arise due to a variety of reasons, including human error, incomplete or…
Q: Which features of Compiler Phases make them special? Could you provide an illustration of each step?…
A: Compiler: A compiler is a computer program that takes source code written in a programming language…
Q: Answer the Following Questions: 1- Evaluate the following to find c: c=(3+(18/2-2)) + 6/4+ (4/8 *…
A: 1- Evaluating the expression: c=(3+(18/2-2))+6/4+ (4/8 * 10) * 3 % 2 c = (3 + (9 - 2)) + 1.5 + (0.5…
Q: Could you list the six most compelling reasons why you want to study compilers?
A: Introduction: Compilers: A compiler translates the type or language in which a programme is written…
Q: You are designing the syntax for a new language. The following example presents a loop statement in…
A: Solution: BNF for class definition: CODE…
Q: The calculation of the bill will be used the following rules: -The bill will be exempted for usage…
A: Equivalence partitioning, which it is also known as equivalence class partitioning, is a software…
Q: Answer the following questions in a Microsoft® Word document and save the file on your computer with…
A: Answer: We need to explain the concept of the databases but our guidelines is answer the first three…
Q: TASK DESCRIPTION A Requirement/Need Analysis IT System Design Software development Develop IT…
A: To determine the critical path, we need to create a PERT chart and calculate the earliest start…
Q: using static System. Console; class AddBooks { } static void Main() { } Book book1= new Book ("Silas…
A: The algorithm of the code is as follows:- 1. Create a class called Book with properties for title,…
Q: What exactly is the difference between computer fraud and computer crime when it comes to computers
A: Computer crime is also known as cybercrime, which is a crime involving a computer or network.…
Q: Dissect NP and P, then provide concrete instances to show how they vary in use.
A: Introduction: In computer science, NP and P are complexity classes that describe how much computing…
Q: How to identify, evaluate, and contrast different types of back-end compiler architectures?
A: Identify different types of back-end compiler architectures: A compiler is a software tool that…
Q: QUESTION 3 Which of the following is true about Introduce parameter object refactoring technique?…
A: Here is your solution -
Q: If a cyberattacker is using a Generation 6 tactic, what should be done to stop them?
A: Cyberattacks: A cyberattack is a type of attack that uses computer technology to disrupt a computer…
Q: In terms of the bandwidth available, do access points more closely resemble hubs or switches?
A: INTRODUCTION: A device that links two or more devices that are part of the same or different…
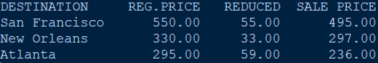
Q: Anyone Airlines is having a sale on flights leaving from Tampa. Write a program that uses a while…
A: program6_1.py Write a program that uses a while loop to store to a file the names of destinations,…
Q: Linear search has two benefits over binary search for research.
A: Here is your solution -
Q: Provide an exhaustive rundown of the techniques currently in use to enhance software quality.
A: Your answer is given below.
Q: What actions must an attacker do for a sniffer attack to be successful? Is it possible for an…
A: Introduction of Sniffer System: A sniffer system, also known as a network sniffer, packet sniffer,…
Q: SOFTWARE RELIABILITY AND QUALITY ASSURANCE DESCRIBE the shocking state of software quality in…
A: Software reliability and quality assurance are essential aspects of the software development…
Q: draw an ER diagram of the database to manage daily medical examination and treatment in the hospital…
A: An ER (Entity-Relationship) diagram is a graphical representation of entities, their attributes, and…
Q: Rewrite the following partial EBNF grammar in BNF notation. You are allowed to create new non…
A: Here is the BNF notation equivalent of the given EBNF grammar: expressions ::= expression { ','…
Q: Which of the following is true about Introduce parameter object refactoring technique? 1. Does not…
A: Answer: We need to explain the which option is correct. so we will see in the more details with the…
Q: 1) Make a list of five or more members in the programming club, including the name 'admin'. Make…
A: The algorithm of the code is as follows:- 1. create a list of members2. loop through members3. if…
Q: for the transit lightcurve I get an error message:
A: Solution: Python Code: Here is a program that plots the "uneclipsed" area of a star as a…
Q: In what ways do coding standards matter? Explore the Java language's coding standards.
A: Introduction: Coding standards are a set of guidelines and best practices that define how software…
Can you please answer the following question? Program is written in Python.
Step by step
Solved in 2 steps with 1 images

- Table Name:- Employee Empid EmpName Department ContactNo EmailId EmpHeadId 101 Isha E-101 1234567890 isha@gmail.com 105 102 Priya E-104 1234567890 priya@yahoo.com 103 103 Neha E-101 1234567890 neha@gmail.com 101 104 Rahul E-102 1234567890 rahul@yahoo.com 105 105 Abhishek E-101 1234567890 abhishek@gmail.com 102 Table :- EmpDept DeptId DeptName Dept_off DeptHead E-101 HR Monday 105 E-102 Development Tuesday 101 E-103 Hous Keeping Saturday 103 E-104 Sales Sunday 104 E-105 Purchage Tuesday 104 Table :- EmpSalary EmpId Salary IsPermanent 101 2000 Yes 102 10000 Yes 103 5000 No 104 1900 Yes 105 2300 Yes Table :- Project ProjectId Duration p-1 23 p-2 15 p-3 45 p-4 2 p-5 30 Table :- Country cid cname c-1 India c-2 USA c-3 China…Create a stakeholder register for a Greek restaurantGo to the Collectibles section of eBay (http://collectibles.shop.ebay.com/) and pick any subcategory that looks interesting to you. Find an auction that is just about to end and bookmark it. When the auction has ended, return to the auction page and click on “Bid History.” (If you have an eBay account, you have the option for searching “Completed Listings.”) Your assignment is to use the bid history to construct a demand curve. (You will have to “reorder” the bids a bit to figure this out. Try to figure out the maximum price that each of the bidders is willing to pay, and then use that information to construct the demand curve. See this example for how to get from a bid history to a demand curve.)HELPFUL NOTES: Only count the highest bid for each bidder. If one bidder bids $25 but then later bids $50 and then never bids again, it must be that his maximum willingness-to-pay is $50; the $25 bid is irrelevant. If the bidder had been willing to bid more than $50, he probably would have…
- BASIC JQUERY...Make a simple portfolio using JQuery (link below), provide much detail as possible by using the given examples in the link in creating the portfolio .... https://www.w3schools.com/jquery/jquery_examples.asp?fbclid=IwAR0WWFC39ucCIUMykf0-bRja1lMcI0vBQoGdy6V_NuWH-1cZMTMf2l6Tndw16 Examples of the user touchpoints include: Select one: a. Transaction Points b. Service Points c. All other answers are correct. d. Information Pointsplease answer with proper explanation and step by step solution. i request not copy from online site. Question: What is the relationship between f(n) = 2^n and g(n) = 2^(n–1)? Answer choices: a. f = O(g) b. f = Ω(g) c. None of the these d. f = ϴ(g)
- Given the following XML file student.xml <?xml version="1.0" encoding="UTF-8"?> <Myclass transacted= ”123”> <studlist> <student Rating= “average” > <firstName>John</firstName> <lastName>Smith</lastName> <email>jsmith@gmail.com</email> <mobile>0211223344</mobile> </student> <student Rating= “top 10” > <firstName>Ali</firstName> <lastName>Faizal</lastName> <email>ali@gmail.com</email> <mobile>0211223345</mobile> </student> </studlist> <Details> <location>Block15</location> <floor>First</floor> <roomno>909</roomno> </Details> </Myclass> Write an DTD document for the above xml file. What is the document root?Don't say its violates ur term of service. Provide correct solution and get upvotes.How many Web sites can you think of that usecrowdsourcing, that is, have nonemployeesprovide the value?
- Delete all the salesmen who make less than 200 in commission, including those who have not earned any commission EMP Table: Field --------------------------------------- EMPNO ENAME JOB MGR HIREDATE SAL COMM DEPTNO DEPT Table: Field ------------------------------- -------- -------------------------------------------------------------------- DEPTNO DNAME LOCThe Great Bear Lodge is a hotel with an adjoining indoor waterpark and indoor minature golf center. The hotel sells packages which include overnight hotel stays with waterpark passes and minature golf passes. The hotel also has a plicy of selling daily passes to the indoor waterpakr and daily passes to the indoor minature golf center (in other words people do not need to stay at the hotel to use the indoor waterpark or indoor minature golf center.) Hotel guests may also choose to reserve just a hotel room without purchasing the waterpark or minature golf center passes. Great Bear Lodge is offering an incentive for the month of April. They are offering a package in which guests who reserve an overnight stay with the waterpark pass package will receive a free pass to the minature golf center. The total price for this package is $225 per night. The typical pricing for each of these sold independently are: One night hotel stay: $180, Daily Waterpark pass: $90, Minature Golf…Which of the following is not the principles for improving the way that mixes operate: A. Use a single mix. B. Uniform transactions. C. Client-side should be automated. D. Fees should be all-or-nothing.

