Determine if it is possible to design an expanding opcode to allow the following to be encoded in a 12-bit instruction. 4 instructions with three registers. 255 instructions with one register. 16 instructions with zero register. If this design is not possible, what will be the maximum size of instruction that would accommodate the design? Show your work and provide explanation.
Determine if it is possible to design an expanding opcode to allow the following to be encoded in a 12-bit instruction. 4 instructions with three registers. 255 instructions with one register. 16 instructions with zero register. If this design is not possible, what will be the maximum size of instruction that would accommodate the design? Show your work and provide explanation.
Chapter4: Processor Technology And Architecture
Section: Chapter Questions
Problem 15VE: A(n) ________________ instruction always alters the instruction execution sequence. A(n)...
Related questions
Question
Instruction formats
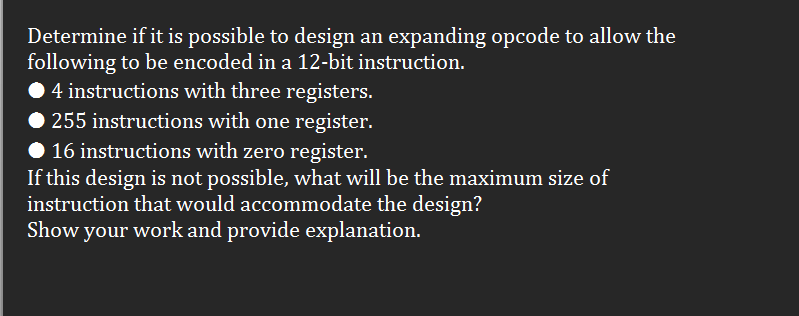
Transcribed Image Text:Determine if it is possible to design an expanding opcode to allow the
following to be encoded in a 12-bit instruction.
4 instructions with three registers.
255 instructions with one register.
16 instructions with zero register.
If this design is not possible, what will be the maximum size of
instruction that would accommodate the design?
Show your work and provide explanation.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 1 steps

Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning