Explain the steps for the following operations using binary scarch.
New Perspectives on HTML5, CSS3, and JavaScript
6th Edition
ISBN:9781305503922
Author:Patrick M. Carey
Publisher:Patrick M. Carey
Chapter12: Working With Document Nodes And Style Sheets: Creating A Dynamic Document Outline
Section12.1: Visual Overview: Exploring The Node Tree
Problem 5QC
Related questions
Question
There are N numbers of visitors in Muscat festival, Manager wishes to search particular visitor information based on visitor ID. Consider the records are already arranged in ascending order bascd on visitor ID. Use this scenario to answer the below assignment questions. 1. Explain the steps for the following operations using binary scarch. Search for any visitor ID which is available in the list. b. Search for any visitor ID which is not available in the list. 2. Use Mid-Square Hashing Technique to explain the following. a. Place all the records into the hash table. b. Use linear probing or chaining technique to eliminate collision. 3. Write your own hash function.
Note: 1. N value must be at least 7. 2. Use your own data for visitor ID and it must be 4 digit number.
Please i need answer same way through by picture please
Transcribed Image Text:ding
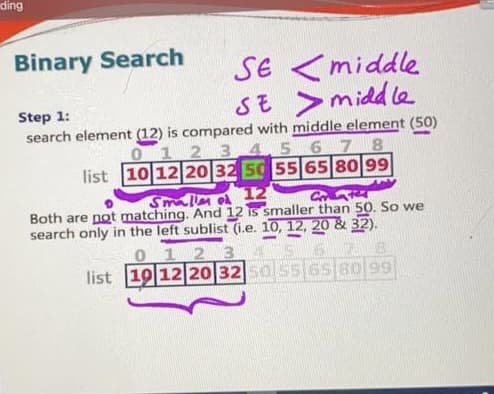
Binary Search
SE
<middle
SE >midd le
search element (12) is compared with middle element (50)
01234.5 6 7 8
list 10 12 20 32 50 55 65 80 99
Step 1:
Smallm o 12
Both are not matching. And 12 is smaller than 50. So we
search only in the left sublist (i.e. 10, 12, 20 & 32).
012 3
list 19 12 20 3250 556s 80 99
5 6 7 8
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:
9781305503922
Author:
Patrick M. Carey
Publisher:
Cengage Learning

New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:
9781305503922
Author:
Patrick M. Carey
Publisher:
Cengage Learning