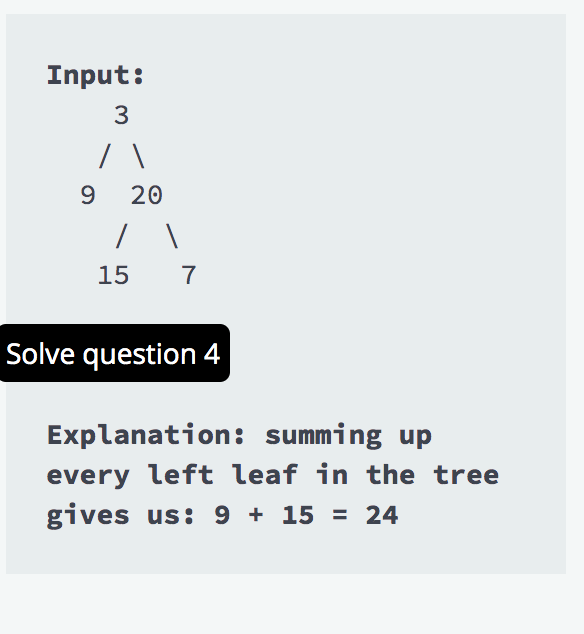
Explanation: summing up every left leaf in the tree gives us: 9 + 15 = 24
Q: Examine the tester program to see how the functions are used. overload.cpp 1 #include "overload.h" 2…
A: In this question we need to write a C++ program to overload product method such that one product…
Q: Create a graphical timeline depicting the evolution of client-server web technologies.
A: Given: Midway through the 1980s, corporations started to see the necessity to network their…
Q: A problem-to-algorithm translation procedure is referred to as a computer program.
A: A problem is a description of something that is difficult to comprehend or involves massive…
Q: the study of computer technology Application software is available in several forms and sizes. Add…
A: Introduction The Study of Computers: Which of the many different kinds of a application software are…
Q: 1. Consider a system of 9 processes, P = {p1, ..., p9}. Associated with the system are 6 memory…
A: As per our policy, we are allowed to answer one question at a time. If want an answer or some other…
Q: It is necessary to examine connectionless protocols as a potential substitute for connection-based…
A: Answer: Benefits of connection-based protocols include: It is really trustworthy. Every bundle…
Q: Programmers with extensive programming language knowledge could benefit from learning more dialects…
A: Computer language Programmers communicate with computers using a programming language (developers).…
Q: For the following code, determine dependencies and data hazards (along with types). How many clock…
A: Data Hazard: Data risks happen when instructions that display data reliance alter data at various…
Q: Describe the process by which data is transferred from one component of a web-based application to…
A: HTTP is a protocol for encoding and transmitting data between a client (such as a web browser) and a…
Q: Difference between Static and Instance method working in java Program
A: Difference between Static and Instance method working in java Program:-
Q: What precisely do you mean by "quick Launch Tray" when referring to the "system tray"?
A: What precisely do you mean by "quick Launch Tray" when referring to the "system tray"?
Q: It is essential to understand the contrast between operational and denotational semantics since it…
A: Syntax and Semantics: Both syntax and semantics are research areas relevant to studying programming…
Q: the Rational Unified process with the Classical Water Fall model side by side?
A: Rational Unified process (RUP) is an agile software development method, in which the existence cycle…
Q: What forms the foundation of the Oldham-Hackman model of job characteristics?
A: Introduction: According to the job characteristics model developed by Hackman and Oldham in 1974,…
Q: The multiple aspects of a compiler must be taken into consideration in order to generate efficient…
A: Introduction: An improving compiler is a kind that works to restrict or expand the capabilities of a…
Q: What are, in your view, the six most compelling reaso
A: Compiler: We know Compiler is a program that translates source code in to an executable form.…
Q: People are traveling more and more, and with rising gas prices, they are becoming more aware of the…
A: Javascript JavaScript is a scripting language that allows you to do pretty much anything else,…
Q: If the term "optimize compilers" is to be used, is its meaning clear and comprehensive? When would…
A: We need to discuss if the term optimize compilers is clear and comprehensive. *As per the guidelines…
Q: Where is the code?
A: I attached your answer below.
Q: Identify and explain the contributions of the first two major participants in the Internet's…
A: Introduction: The communication between the networks is referred to as the Internet. But the…
Q: What is Bayes’ Theorem? How is it useful in a machine learning context?
A: The likelihood of an event occurring in relation to any circumstance is described by Bayes' theorem.…
Q: Instructions 1. Using NetBeans, create three (3) linked lists named songs, artists, and playlist.…
A: The answer for the above question is given in the below step.
Q: In Python, Given the 2D list below, convert all values to 255 if they are above a threshold or to 0…
A: Code a =[[77,68,86,73],[96,87,89,81],[70,90,86,81]] # 2d array #printing the orignal…
Q: task-5 Change Summation Integers problem to Finding the minimum problem. Make sure you properly…
A: Java program to solve the given problem is below.
Q: What are the key functions of the Phases of the Compiler? Exist examples for every phase?
A: INTRODUCTION: Here we need to tell the key functions of the compiler phases and give examples also.
Q: What is the three types of attribute scopes (Access Modifiers).
A: The above question is solved in step 2 :-
Q: It is prudent to compare the pros and cons of connectionless and connection-based protocols side by…
A: According to the information given:- We have to compare the pros and cons of connectionless and…
Q: Give an example of a vertically coded control unit and describe your design strategy.
A: Vertical microcode: Each microinstruction is encoded using vertical microcode. The bit field can…
Q: Q5 (Intro to R + Functions) Q5: Create a function 'order_print' that takes a vec elements by order…
A: Answer- R programming: seq() Function for creating a vector of elements that are sequential. To…
Q: We're going to start simple. Declare and implement a function called addOne. Your function should…
A: Steps to do- In Main function ask user for a number Then call addOne with number as its parameter…
Q: Explain the output The algorithm Seq(n) is shown below. What is the number of recursive call in the…
A: Recursive call : Recursive calls occur when a procedure calls itself or another procedure, which…
Q: Given a spanning forest T of an undirected simple graph G = (V, E), the following hold.
A: (T1) For each edge e ∈ E, either e or its reverse belongs to T. (T2) For any two distinct edges e…
Q: Define TCP, UDP, and IP Compare the header of TCP, UDP, and IP packets. Why are there more field in…
A: Define:- TCP:- One of the key Internet protocol suite protocols is the Transmission Control Protocol…
Q: Talk about the computer system's core functions. Essay
A: Computer has a very important part in bringing the digital revolution.
Q: Utilizing search engines offers several benefits. Search engine optimization may be illustrated with…
A: Answer is
Q: Given the adjacency matrix of an undirected simple graph G = (V, E) mapped in a natural fashion onto…
A: Breadth first search which refers to the Traversal means visiting all the nodes of a graph. Breadth…
Q: What factors must be considered while organizing a software team? How to assign the appropriate…
A: Each and every great software starts with a strong and clear plan to be successful. Explanation: The…
Q: What is a challenge-response authentication system? Specify it here. Why is this method more safe…
A: The answer is as below:
Q: How can you find out what a computer program that is now executing is really doing?
A: Utility programmes are the tools that assisted in our analysis and provided details on the process…
Q: What is the precise history of the area of computer science?
A: Computer has a very important part in bringing the digital revolution. Prior to digital computers…
Q: I need help in this MCQ of this data structure and algorithm question. ALGO1(A)// A is an integer…
A: In this question we have to provide a worst cast running time for the ALGO1 on an array of size n…
Q: What forms the foundation of the Oldham-Hackman model of job characteristics?
A: Introduction: According to the job characteristics model developed by Hackman and Oldham in 1974,…
Q: Write a SQL query to delete all duplicate email entries in a table named Person, keeping only unique…
A: a SQL query to delete all duplicate email entries in a table named Person, keeping only unique…
Q: The StayWell Property Management team considers creating a discount scheme for the property owners…
A: Given: The StayWell Property Management team considers creating a discount scheme for the property…
Q: Programmers with extensive programming language knowledge could benefit from learning more dialects…
A: 1) JavaScript:- One of the key components of the World Wide Web is the high-level computer language…
Q: On disk, operating systems endeavor to store files in sequentially arranged blocks. The usage of…
A: Given: Operating systems store consecutive file blocks on successive disc sectors by default. What's…
Q: Authentication systems use a challenge-response methodology. What makes it more safe than a system…
A: In the world of computer security: challenge-response authentication is a collection of protocols…
Q: Explain why you believe a web server to be the most sophisticated system.
A: Web server: A description of a web server may be considered the final system. The ultimate system…
Q: Here, the distinctions between "connectionless" and "connection-based" protocols are examined.
A: GIVEN: The benefits and drawbacks of the connectionless protocols are contrasted with those of…
Q: 3) Using Excess-8 notation convert following fractional numbers into decimal. a) 01010100 b)10111100
A: given data:- here we have to convert -8 notation numbers into decimals given the following:- a)…
Algo to code as part.
Step by step
Solved in 3 steps with 2 images

- Java / Trees: *Please refer to attached image* How many leaf nodes are there on this tree? Multiple chocie. 0 3 4 10e) (2a + 5b) ^ 3 * (x - 7y) ^ 4 f) Evaluate the binary expression tree in e) usingthe arrows method. Assume a=1, b=0, x=2, y=0BOX IN YOUR ANSWERclass BST: def __init__(self, root = None): if root != None: root.setparent(None) self.__root = root def getroot(self): # Returns the root node of the tree ####################################################################### # Remove the pass and write your code ####################################################################### pass ####################################################################### # End code ####################################################################### def setroot(self, node): # Sets the root node of the tree ####################################################################### # Remove the pass and write your code ####################################################################### pass ####################################################################### # End code…
- Please help! // TreeNode.java class TreeNode<T> { T item; TreeNode<T> leftChild; TreeNode<T> rightChild; public TreeNode(T newItem) { // Initializes tree node with item and no children. item = newItem; leftChild = null; rightChild = null; } // end constructor public TreeNode(T newItem, TreeNode<T> left, TreeNode<T> right) { // Initializes tree node with item and // the left and right children references. item = newItem; leftChild = left; rightChild = right; } // end constructor } // end TreeNode // BinaryTreeBasis.java public abstract class BinaryTreeBasis<T> { protected TreeNode<T> root; public BinaryTreeBasis() { root = null; } // end default constructor public BinaryTreeBasis(T rootItem) { root = new TreeNode<T>(rootItem, null, null); } // end constructor public boolean isEmpty() { // Returns true if the tree is empty, else returns false. return root == null; } // end isEmpty public void makeEmpty() { // Removes all nodes from the…Write the method "isALeafNode" to check weather a specific node is a leaf or not { }(public boolean isALeafNode(Node nWrite the following string with your information: string=”your fullName 19-arid-yourNo” //e.g.Isha Tir Razia 19-ARID-1098 //consider & use space after each word Now draw a Huffman tree and generate codes.
- The size value of various nodes in a weight balanced tree areleaf – zerointernal node – size of it’s two childrenis this true?a) trueb) falseIn a tree, a(n) ____ is a node that has at least one child. Question 6 options: branch interior node root leafPROLOG PROGRAMMING LANGUAUGE PLEASE (* First argument is a BST and the second argument is a file name. Visits the tree nodes in preorder recursively and writes its data to the file separated by spaces. *) preOrderWrite/2
- Java / Trees: *Please refer to attached image* What is depth of Node W in this tree? Multiple chocie. 0 1 2 3 4 10public int insert(int value);/* Creates a node with the parameter as its value* and inserts the node into the tree in the appropriate position.* This method should call upon the recursive insert_r() helper method* you write.** we will make the assumption for this assignment (and implement it so) * that the values in a BST are unique... no duplicates** If we insert a value and it succeeded... adds it to the tree* return the element that was added** If we try to add an element and it is a duplicate, return the element* but make no changes to the tree... no new nodes added** @param int value to be inserted in tree* @return integer that was insrted after insertion is done.** Example 1: Suppose we have the tree below:** (27)* / \* (4) (29)* / \* (1) (8)* After calling insert(5), we'd obtain the following tree:** (27)* / \* (4) (29)* / \* (1) (8)* /* (5)** Example 2: Suppose we have the tree below:** (87)* / \* (42) (128)* \ \* (46) (145)* /* (44)** After calling insert(147), we'd obtain the…Complete the findMin() method. This method should return the minimum of the values in the tree. If findMin was called with the tree pictured before, it should return 1. class Main { public static void main(String[] args) { BinaryTree.main(args); } } public class BinaryTree { public BinaryTree() { root = null; } public BinaryTree(Node node) { root = node; } static class Node { Node(int d, Node l, Node r) { data = d; left = l; right = r; } public int data; public Node left; public Node right; } public Node root; public int findMin() { return -1; } public static void main(String[] args) { BinaryTree myTree = new BinaryTree(); myTree.root = new Node(10, new Node(5, new Node(20, null, null), new Node(25, new Node(15, new Node(30, null, null), new Node(35, null, null)), null)), new Node(40, null, null)); System.out.println(myTree.findMin()); } }











