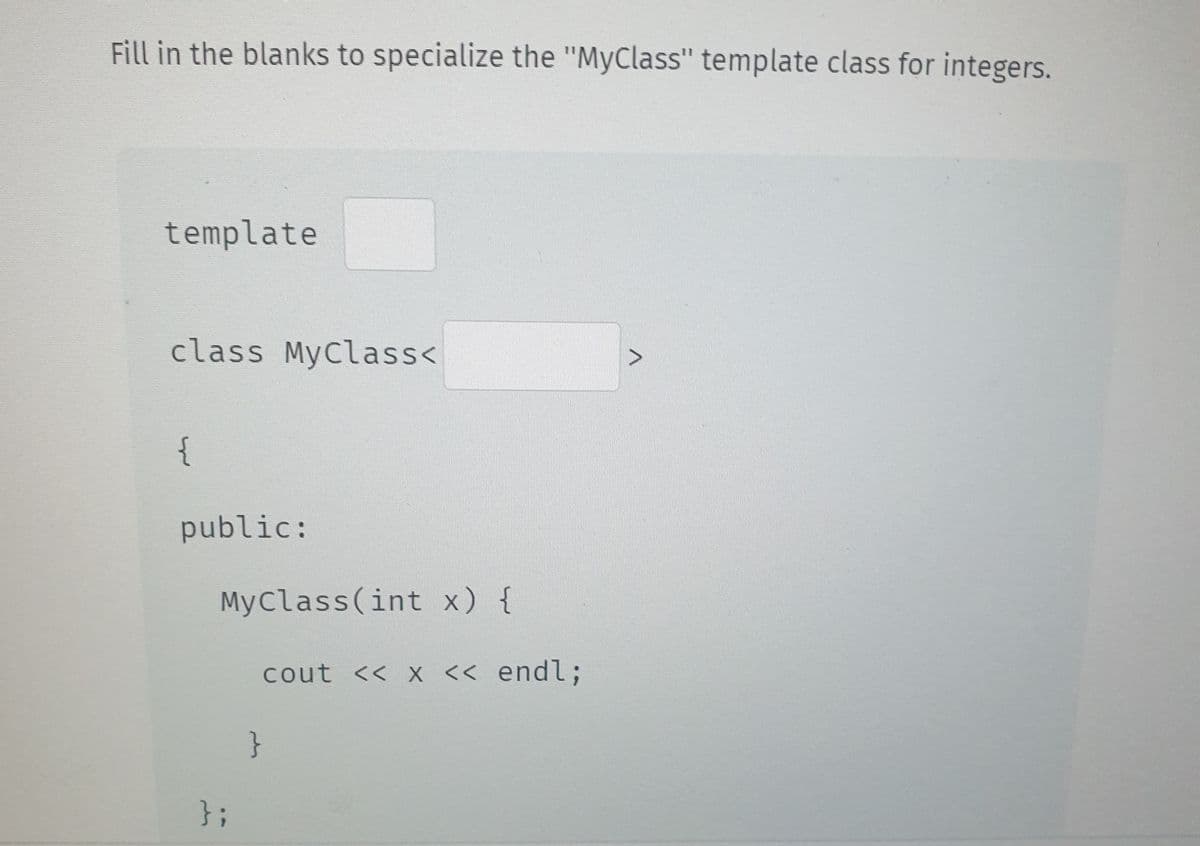
Fill in the blanks to specialize the "MyClass" template class for integers. template class MyClass< { public: MyClass(int x) { }; cout << x << endl; } >
Q: The post-order traversal of a binary tree is O P Q R S T. Then possible pre-order traversal will be…
A: Indeed, the postorder traversal of the binary tree right subtree is traversed before visiting the…
Q: functions
A: Introduction A friend function is a kind of function that is been used in C++ programming language…
Q: What are the applications of computers in various domains, such as education, health, and so on?
A: Introduction: The applications of computers in a variety of fields due to the fact that computers…
Q: How would you describe the global spread of Is the Internet used?
A: Introduction: The internet is a globally interconnected network infrastructure that facilitates…
Q: Assume that there are
A: “Since you have posted a question with multiple sub-parts, we will solve first three sub-parts for…
Q: The ascending heap property is ___________ a) A[Parent(i)] =A[i] b) A[Parent(i)] = A[i] d)…
A: In this question we have to provide a valid option for the ascending heap property. Lets answer
Q: Which of the following methods is the best choice for complex applications? a) binary heap b)…
A: Introduction We characterize a complex application as any application supporting expansive,…
Q: hical design of an AI-powered system that can interact with the patients, schedule an appointe
A: Introduction: Below describe the present a graphical design of an AI-powered system that can…
Q: Explain the following terms: Cursor, Embedded SQL, JDBC, SQLJ, stored procedure.
A: Cursor: The device known as a cursor makes it possible to access rows from a relation and read their…
Q: lation R on a set S, defined as x R y if and only if y R x. This is an example of? a) reflexive…
A: Introduction: A relation R on a set S, defined as x R y if and only if y R x. This is an example…
Q: ompare and contrast batch versus online data entry methods' benefits and drawbacks. There is a…
A: Introduction: Batch processing is more expensive than online input.A batch of data can be processed…
Q: possi ee fo 2
A:
Q: Why do you think data quality is one of the most important aspects of data warehousing? Describe the…
A: Data quality is a method of evaluating the condition of data based on factors such as correctness,…
Q: What is the depth of any tree if the union operation is performed by height? a) O(N) b) O(log N) c)…
A: The question has been answered in step2
Q: In a game called NIM, there are two players. At the start, two piles of matches are placed on the…
A: The game tree is sketched as follows. In this tree, we only consider the best strategy for player1…
Q: Explain the different factors affecting the processing speed of CPU.
A:
Q: Lottery number generator: Write a program that generates a seven-digit lottery number. The program…
A: Step-1: StartStep-2: Declare a empty listStep-3: Start a loop from i=0 to 6 Step-3.1: Declare a…
Q: Computer Science There is an n × n grid of squares. Each square is either special, or has a…
A: Answer: Here not mention any specific language so we have written code in C++ programming language…
Q: write alogrithms for the following blocks of code... 1st block: void HRM::UpdatePerson(){ int…
A: Define one structure to hold the details of an employee. This structure can hold the first name,…
Q: A binary search tree contains values 7, 8, 13, 26, 35, 40, 70, 75. Which one of the following is a…
A:
Q: Apply the system of linear equations to solve the problem: One day in the morning, a vegetable…
A: Python Program: # let x be the price of one potato and y be the price of 1 tomato # From the…
Q: The maximum number of nodes in a tree for which post-order and pre-order traversals may be equal is…
A: Answer:
Q: Some highly confidential documents need to be kept in a super secured vault. The vault has 5 steps…
A: The answer of the above following questions are given below:
Q: A number 428 in duodenary (base 12) is to be added to C10 in tredinary (base 13). The from 10211 in…
A: The answer is
Q: Using C++ Using your own creativity, make a set of function templates that have these features:…
A: I am limited to answering the first three subtasks of the query because of company policies. Please…
Q: Consider the dataset in terms of attribute-value pairs where F is the value, and A,B, C are…
A: We can think about the entropy of a dataset in terms of the probability distribution of observations…
Q: Describe the algorithms for semi-supervised learning. Discuss methods for evaluating candidates…
A: Describe the algorithms for semi-supervised learning. A subclass of machine learning algorithms…
Q: among the following provided the first suffix tree contribution for all alphabet? a) Weiner b)…
A: It is defined as a tree data structure typically used to store a list of strings. It is also…
Q: Is there not an answer where there are more classes to form the relationship between the…
A: According to the information given:- We have to define the class diagram that is used in the…
Q: Write a program that reads a list of words. Then, the program outputs those words and their…
A: Program: #include <iostream>#include <vector>#include <string>using namespace std;…
Q: What is the worst case efficiency for a path compression algorithm?
A: please check the step 2 for answer
Q: Which of the following is the implementation of the ternary tree? a) AVL Tree b) Ternary Heap c)…
A:
Q: What is a threaded binary tree traversal? a) a binary tree traversal using stacks b) a binary tree…
A: answer is
Q: Joseph is a doctor. He works at the Chris Hani Baragwanath Academic Hospital in Soweto. He is…
A: Attribute : Profession, work, responsibility (private ) Method: getProfession() ,…
Q: In term of encapsulation, please explain how a message from Source can be transmitted to…
A:
Q: An electricity board charges the following rates to domestic users:- Units consumed Tariff For the…
A:
Q: Discretization using binning has two approaches, name them. You are given the following dataset: 11,…
A:
Q: Fill in the blanks to declare a pointer to the "st", where "st" is of type "Student", then call…
A: What is Pointer: In C language, A variable that contains the address of another variable is known…
Q: Why is binary search faster than linear search? Make an argument for what you did.
A: Introduction: Linear search: The simplest way to search a data collection is linear. From the…
Q: What are double and single threaded trees?
A: Single Threaded Binary Tree:In this each node is threaded towards either the in order predecessor or…
Q: Review sequence, selection, and repetition control structures. Give an example of each in python.
A: ANSWER:-
Q: Consider a swapping system in which memory consists of the following hole sizes in memory order: 12…
A: Given memory hole sizes are, 12 MB, 4 MB, 20 MB, 12 MB, 18 MB, 7 MB, 9 MB and 12 MB Given segment…
Q: Consider a weight balanced tree such that, the number of nodes in the left sub tree is at least half…
A: A weight balanced tree is self-balancing tree in which the number of nodes for each is at least half…
Q: A binary search tree contains values 7, 8, 13, 26, 35, 40, 70, 75. Which one of the following is a…
A: A binary search tree contains values 7, 8, 13, 26, 35, 40, 70, 75. Which one of the following is a…
Q: Consider the following normal form of the game with two players. Which of the following is the…
A: The answer is given in the below step
Q: Who among the following algorithm is used in external memory and compression of the suffix tree? a)…
A: The given question asks which of the following algorithm is used in external memory and compression…
Q: What is the other name for Suffix Tree? a) Array b) Stack c) Priority Queue d) PAT Tree
A: A compressed tree holding all the suffixes of the provided text as their keys and locations in the…
Q: What exactly is the notion of privacy in terms of information security? What distinguishes this…
A: According to the information given:- We have to define the notion of privacy and privacy from the…
Q: ) O(N) b) O(log N) c) O(N log N) d) O(M log N)
A: Explanation for a reason: In Data structure for The worst-case efficiency for a path compression…
Q: Given the initial statements: s1 = "spam" s2 = "ni!" Show the result of evaluating each of the…
A: String slicing helps to obtain a sub-string from the given string by slicing it from start to end.…
Answer the picture below.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- C#: PLease add inheritance and polymorphism in the code. And display the vehicle/s. Thanks!using System;using System.Collections.Generic;using System.Linq;using System.Text;using System.Threading.Tasks;namespace DemoApplication{ public class Vehicle { protected int VehicleID; protected string VehicleName; public void SetTutorial(int pID,string pName) { VehicleID=pID; VehicleName=pName; } public String GetVehicle() { return VehicleName; } } public class VehicleDetails:Vehicle { public void RenameVehicle(String pNewName) { VehicleName=pNewName; } static void Main(string[] args) { VehicleDetails VD=new VehicleDetails(); VD.RenameVehicle("CarName:Audi"); VD.RenameVehicle("Number of doors:4"); VD.RenameVehicle("Number of wheels:4"); VD.RenameVehicle("Maxspeed:180 KMPH"); VD.RenameVehicle("Fuel capacity:50 lts"); Console.WriteLine(VD.GetVehicle()); Console.ReadKey(); } }}Running polymorphism has certain benefits than compiling polymorphism. Overloading vs. overriding: what's the difference? Explain.plz draw uml and implemnt classes
- Q> Can we inherit Constructors or not?Declare classes Person and Student where Student is derived from Person class. Person has Name and Student has RollNo as its private member. Create a Student class object and initialize it with the already existing object of Student class. Analyze the behavior of default constructors of Person and Student classes. Note: use OOP Concepts with C++ language Solve as soon as possibleWrite a class definition that creates a class called leverage with one private data member, crowbar, of type int and one public function whose declaration is void pry(). Opp Java
- Based on the following Diagram answer the below questions. a. What is the Definition of Polymorphism? b. Extract from the above UML Diagram an example of Overridden method? Explain the meaning of Overridden? c. Extract from the above UML Diagram above an example of Overloading method? Explain the meaning of overloading? d. Write an array declaration that is expected to hold up to 10 objects of type Student and Employee?Start with this class declaration: class Student { int sId; String name; double gpa;} Implement a Comparable and Comparator interface to provide the following three (3) alternative ways of ordering for the Student objects - based on sId (i.e., assume that this is selected as the natural ordering)- based on name, - based on gpa. Next declare a list of five Student objects, initialize them with random values. Test your code by printing out each of the following on separate lines: (original list of students, sorted list of students in ascending sId order, sorted list of students in ascending name order, sorted list of students in ascending gpa order).Java- Suppose you write a new constructor for an extended class. Describe two different ways that the superclass's instance variables could be initialized within the constructor for the extended class.
- Hello, I am having trouble with this homework question for my c++ course. Implement a Rational Number class with the following specifications. Data members a) numerator and denominator Functions a) Constructors: 1) default constructor 2) single parameter constructor to create numerator/1 3) dual parameter constructor to create numerator/denominator 4) Use constructor delegation across all constructors. b) Accessors and Mutators for both data members. c) Static recursive GCD function using Euclid's algorithm. d) Static LCM function for two numbers. e) Reduce function simplify a rational number. This function modifies its calling object. f) Your program should work with the supplied driver program. Notes LCM (Least Common Multiple) This function returns the smallest multiple of a and b. Step 1: Multiply a and b to find a common multiple. Step 2: Divide the common multiple by the GCD of a and b. Step 3: Return the result of Step 2. Reduce: This function reduces a fraction to…What is overloading? How is this different from coercion and polymorphism?Write a Java class Person for dealing with persons. Your class must have the following features:



