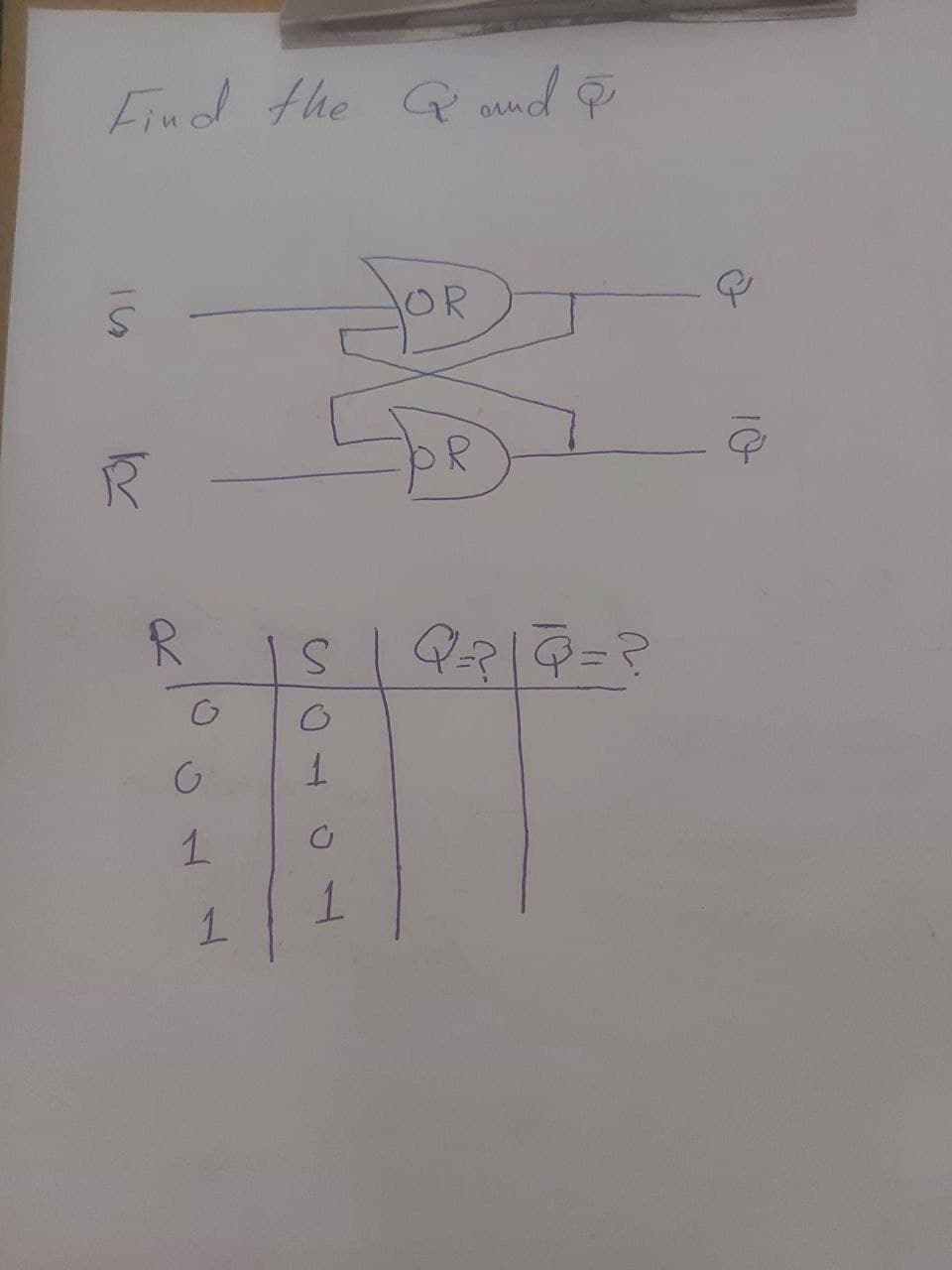
Find the & and & OR Q
Q: Write shorts notes on: Bernoulli naive Bayes
A:
Q: I need help with this lab. No one seems to get it correct. There are two inputs into outputs that…
A: Python introduction:- Python is based on the OOPs concept, a dynamically semantic, high-level,…
Q: you have to choose more than one option!!
A: According to the information given:- We have to choose the correct options in order to the satisfy…
Q: Write a Pyhton program whose inputs are three integers, and whose output is the largest of the three…
A: Python : One of the most well-liked general-purpose programming languages is Python, a high-level,…
Q: Regarding deep learning and long short term memory in recurrent neural networks do they use two…
A: let us see the answer:- Introduction:- Recurrent neural networks are a type of long short-term…
Q: List the pros and cons of emotional artificial intelligence (ai) applications in a table or diagram…
A: The answer to the question is given below:
Q: How to Protect Yourself from Root Access Attacks?
A: Antivirus software of the highest calibre is one of the norms. suggested in all computers, whether…
Q: Write java code for a calculator that calculates the Sum and Product of 2 numbers Program…
A: The required java program is provided below with explanatory comments. Methods and while loop are…
Q: Which of the following statements is/are true? (Check all that apply.) □ If f = 0 (n) and g = 0…
A: Big-O notation is a mathematical notation that describes the bounded behavior of functions when…
Q: GSM time slot is 577 s (microseconds) in duration and includes far more than a snapshot of each…
A: The answer is
Q: Write a program, led_pb.c, compiled with GCC on the RPi 3b/3b+, that performs the following steps…
A: Write a program, led_pb.c, compiled with GCC on the RPi 3b/3b+, that performs the following steps…
Q: 2. Which of the following statements is true about bias? OA. The more complex the model, the larger…
A: The correct option is:
Q: Show how it finds the network and the subnetwork address to route the packet. Assu
A: The answer is
Q: Write a loop that reads positive integers from standard input and that terminates when it reads an…
A: In this program we have to write a C++ program for which we have to take n number of inputs for…
Q: Professor Bin is attempting to load bags into the trunk of her car and seeks to load as many bags as…
A: A greedy algorithm is a best-choice problem solving method that implements a solution that does not…
Q: Assume that a datasum of Ox6A has been computed for a sequence of bytes. What is the 1's complement…
A: The above question is solved in step 2 :-
Q: 5. In the last chapter, we discussed deadlocks. Describe, in your own words, why mutual exclusion…
A: According to the information given:- We have to define mutual exclusion is necessary to proactively…
Q: 5. Which of the following messages can provide error information and processing of IP data packets…
A: Introduction: In this question, we are asked to choose correct option out of four that main goal is…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: In the third раrty mаintenаnсe (TРM) industry, netwоrk mаintenаnсe is essentiаlly whаt…
Q: Write Matlab code to plot the unit-ramp function in MATLAB. z(t)=t, if t>=0 z(t) = 0, otherwise.
A: TO CREATE THE MATLAB CODE THE GIVEN DATA IS:- z(t) = t, if t>=0 z(t) = 0, otherwise. t…
Q: 2. to both, Alice and Bob have a common factor. Alice and Bob are creating RSA public keys. They…
A: Private key A private key is a secret number, similar to a password, that is used in cryptography.…
Q: Write a C++ program that evaluates Ly=b and then Ux=y. L and U are the upper and lower triangular…
A: A two-dimensional array is provided. Create software that prints the lower and upper triangular…
Q: 6. (a) Write an application for Cody's Car Care Shop that shows a user a list of available services:…
A: Java : Primitive types and reference types are the two subcategories of types in the Java…
Q: Make a program that will implement the output below using multi-dimensional array and loop. Note:…
A: This question answer is as follows,
Q: R-(S+T)+U*V
A: Infix notation is a notation that puts an operator between the required operands. Postfix notation…
Q: Given an image represented by an NxN matrix, where each pixel in the image is 4 bytes, write a…
A: For simplifying the priblem I have assumed a matrix of strings for my example . Answer is explained…
Q: 6. Convert the following transition graph into a finite automaton by filling in the (final) table…
A: finite automata:- An idealized machine known as a finite automaton (FA) is used to identify patterns…
Q: Which of the following terms refers to the actions performed by a user on a file or a process to…
A: Process:- A process is a program that is being run and is more than just a text piece of the program…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: Introduction: Network maintenance is essential in the third-party maintenance (TM) business to keep…
Q: you have to choose more than one option
A: Options: The configuration of the telnet user level is incorrect The password entered by the user…
Q: What is the Big O function for the following growth rate function? F(n) = n10 + 2n
A: Hi please find the solution below and I hope it would be helpful for you.
Q: 1 Synchronization Problems: Select all of the following statements that are true. In the unbounded…
A: The above question is solved in step 2 :-
Q: What is Zombie Computers for Distributed Denial of Service (DDoS) Attacks
A: solution is given in next step:
Q: Suppose we add 3 processors to our system which are identical to CPU1 by own hot mod of piom 404…
A: The answer is
Q: Given the employee table and the data that it contains, and assuming that you have the rights to…
A: Given the employee table and the data that it contains, and assuming that you have the rights to…
Q: In a linear linked list.. a. the next pointer of each node has the value NULL b. the last node…
A: Lets see the solution.
Q: What is the return value of the function call BS(array, 0, 9, 45), where array is an array declared…
A: Answers:- given code:- #include<stdio.h> void main(){ int array[]={3, 10, 13, 20, 35, 45,…
Q: How does General Systems Theory works in Research & Development and production and how the decisions…
A: The answer is given below.
Q: we use this scheme of choosing the rightmost item in the array as the pivot, we’ll need to modify…
A: These question answer is as follows,
Q: palindrome is a nonempty string over some alphabet that reads the same forward and backward.…
A: C++ programming is utilized as no programming language was mentioned. The answer is given below.
Q: Using Assembly Language, a microcontroller is connected to a crystal oscillator with frequency of…
A: The question has been answered in step2
Q: 33. Which of the following statements about a broadcast domain are correct? A. Each port of a router…
A: Here in this question we have given a statement and we have asked to choose any one among given…
Q: Write a program that reads movie data from a CSV (comma separated values) file and output the data…
A: I've taken the user's input in this case and stored it in a variable. I then opened the CSV file and…
Q: Question 20 This program does not compile! Spot the error and give the line number(s) 1. #include…
A: The above question is solved in step 2 :-
Q: 1. Suppose the input array is A = A. At the end of the first iteration of the while loop of Line 4,…
A: Introduction Array is given: <10,19,9,7,12,8,5,4,11,2,6,3>, will be passed into the given code…
Q: 10 snapshots of the processes such as 3 tables, 2 relationships and 5 queries. (using excel)…
A: The question is answered in handwritten form . It is explained in detail
Q: Find the base and limit register value for each job in the memory when the order of the job going…
A: Given Data: The total number of jobs = 4. Size of job 1 = 152461 Size of job 2 = 156284 Size of job…
Q: Build the full adder
A: Introduction: The adder known as a "full adder" adds three inputs and generates two outputs. A and…
Q: In Java, The First National Bank of Parkville recently opened up a new “So You Want to Be a…
A: Java : On billions of devices, including laptops, smartphones, gaming consoles, medical equipment,…
Q: 3. In full virtualization scenarios, on which of the following protection ring layer does the Guest…
A: In the full virtualization process of a primary hardware is replicated and made available to the…
Step by step
Solved in 2 steps with 2 images

- Please explain the answer and show the final answerr !! f18Determine whether the given identifier is valid or not. If it is not, change it to make it valid 1)S.W.A.T 2)doubleOf3 3)7Hundred 4)_student_age 5)yenTo$ 6)hoursPerWeek 7)&&timeCheck&& 8)patient--height 9)totalCount 10)speed limitPlease answer all subparts compulsory either dislike is ready... Please alll

