This is an R prorgamming question , please explain
Q: What's the difference between type compatibility and type equivalence?
A: Type Equivalence: Which kinds are viewed as being equivalent is described by type equivalence. When…
Q: a brief explanation of the microcode interpreter
A: The outcome of more basic machine language interpretation is microcode. The register or circuit…
Q: Effective practises are needed while choosing a career. These are a few of the foundational elements…
A: Technology, Engineering: The term "engineering technology" refers to the application of scientific…
Q: In a few phrases, describe caching.
A: The solution for the above-given question is given below:
Q: you tell whether your I/O operations are running smoothly
A: Answer is in next step.
Q: What exactly are aggregates, and how can I tell? Who will gain from them?
A: Introduction:- A piece of software called an aggregator is made to gather information from several…
Q: What distinguishes computer engineering's synchronous and nonsynchronous buses
A: Synchronous bus: A bus is said to be synchronous if the steps of the bus protocol are handled by a…
Q: In a few phrases, describe caching.
A: Given: The memory known as cache is a specialised kind of the high-speed memory known as DRAM.…
Q: If all of the RadioButton controls are in the same GroupBox, how many of them may be chosen…
A: We have to explain that if all of the RadioButton controls are in the same GroupBox, how many of…
Q: What time management method is not a preemptive algorithm? Why is this happening, exactly? Round…
A: Introduction The issue at hand is the scheduling technique used in processing, in which the…
Q: Why, in your opinion, is Internet data costly in Ghana? What might be done to reduce users' data…
A: The Internet is pricey in Africa as a whole. In Ghana, it is also costly. The primary explanation…
Q: What exactly are aggregates, and how can I tell? Who will gain from them?
A: Aggregates are raw materials that are produced from natural sources and extracted from pits and…
Q: List the two most crucial qualities of a prospective key.
A: The answer of the question is given below
Q: What does iteration in a loop really mean?
A: Loops: Particular sections of code that are run dependent on certain criteria are referred to as…
Q: How does visual programming operate? What is it?
A: Visual programming is a type of programming in which the programmer uses graphical elements to…
Q: Can a statement be distinguished from an expression? De expression-oriented?
A: We know A programming language that is expression-oriented is one in which every (or almost…
Q: What is ITIL 4 in detail? Give particular examples to illustrate the importance of this.
A: What is ITIL 4 ITIL (Information Technology Infrastructure Library) is a framework designed to…
Q: Open-source software is produced by the Network Funtime Company. The business features a small sales…
A: My primary responsibility as the system administrator for the Network Funtime firm is to protect it…
Q: Define orthogonality in the context of the design of computer languages.
A:
Q: e area of computer science, compare and contrast the idea of abstraction. To emphasise the idea of…
A: Specifically, we have the following responsibility: The topic revolves around the significance of…
Q: How can a new type named doublePointeutir be produced that can be used in place of double*?
A: According to what is stated in the definition: Of the typedef keyword, the declaration of typedef…
Q: Which of the following index type will be the fastest to search for exact SSN values? O BTREE O GIN…
A: PostgreSQL, also known as Postgres, is a free, open source relational database management system…
Q: What are the two parameters that a TryParse function expects from you when you write code?
A: In c# int.TryParse method accepts two parameters. first one is a string and second one is an integer…
Q: Consider the universal set U=(2,4,6,8,10,12,14,16,18,20). Let A-(2,6,10,16) and B-(2,6,8,18,20).…
A: Solution is provided below:-
Q: Make a list of the duties that must be fulfilled throughout processor communication and provide a…
A: Actually, the duties performed during processor communication were the subject of the inquiry.…
Q: What use is a sorting algorithm if it can't locate the information you need?
A: Sorting Algorithm : An array or list's elements are sorted in a certain order using a sorting…
Q: What exactly are aggregates, and how can I tell? Who will gain from them?
A: Exactly are Aggregates: What Exactly Are These Things Called Aggregates? Sand, gravel, and crushed…
Q: What is a case where the disjoint rule is applied to a supertype/subtype connection? What use does a…
A: A property of the supertype entity known as a subtype discriminator establishes which entity subtype…
Q: An overview of Visual Studio should be provided.
A: The solution for the above given question is given below:
Q: How does information go across the layers of the Internet? model?
A: Information on the Internet travels in packets. Packets are like letters in an envelope: they have…
Q: Please provide a brief explanation of Unicode.
A: A Unicode is a character encoding standard that has well-known recognition. It is a structure to…
Q: How does a file management system operate and what is it?
A: What is File Management System? A file management system is utilized for document upkeep (or the…
Q: Look through the method header below, then, as an example, write a call to the method. an internal…
A: Please find the answer in next step
Q: What time management method is not a preemptive algorithm? Why is this happening, exactly? Round…
A: Introduction The issue at hand is the scheduling technique used in processing, in which the…
Q: Effective practises are needed while choosing a career. These are a few of the foundational elements…
A: Given: CDue to the fact that there are a number of questions that have been asked, we will just…
Q: and averages are commonly used in Interaction Design.
A: Commonly used in interaction designs are:
Q: A small research company in Pittsburgh is working to develop a new method of mass storage to replace…
A: THe answer is
Q: When a child process utilizes unnamed pipes to read the parent's message buffer, what happens…
A: In Inter - process communication Unnamed Pipe is used in between the communication of a child…
Q: What does a language that is "highly typed" mean? Static typing, what do you mean?
A: statically-typed languageA statically-typed language is a language like Java, C++, etc where the…
Q: How can a new type named doublePointeutir be produced that can be used in place of double*?
A: According to what is stated in the definition: Of the typedef keyword, the declaration of typedef…
Q: 1. a) When should punitive damages be awarded in a case for intentional infliction of emotional…
A: a) When should punitive damages be awarded in a case for intentional infliction of emotional…
Q: 1) Number of subnets that can be extracted.
A: The answer is
Q: Does a method that accepts an array as an argument really have access to the original array, or is…
A: In step 2, I have provided answer with brief explanation----------------- In further steps, I…
Q: 110.0010) = (?)p BCD BCD with BCD weight
A: The answer is
Q: What are some examples of Automata Theory's practical applications?
A: Introduction: There are several kinds of automata available to choose from. As an illustration of…
Q: Define orthogonality in the context of the design of computer languages.
A: Answer the above question are as follows
Q: What does the term "lazy evaluation" mean? What are promises exactly? What does the word…
A: An evaluation approach known as lazy evaluation delays the process of evaluating an expression until…
Q: The session layer of the OSI model is in charge of dialogue synchronisation and control. Which…
A: OSI Model:- Open System Interconnection is a reference the model that describes and how information…
Q: What distinguishes a text file from a binary file? Can a text editor be used to see a binary or text…
A: Given: Text Files are files in which the contents are kept in a manner that is readable by humans.…
Q: Nancy is leading a Scrum project for her organization. The project is to create new software for the…
A: solution is given as below: list of requirements in a prioritized view
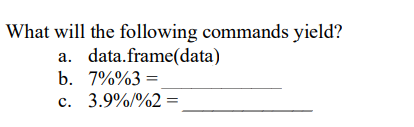
This is an R prorgamming question , please explain
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Which of the following commands would display all files that start with the characters song and end in a number 100-599? A. ls song??? B. ls song[100-599] C. ls song[0-9][0-9][0-9] D. ls song[1-5][0-9][0-9]What does the following command do? $ mkdir dir dir/dir_01/dir_02Which pattern will match all filenames containing a "b"? [!b]* *b* *b b*
- What will be the value in EAX after the following lines execute?mov eax,30020000hdec axWhich of the following lines of code will not create a file “abc.txt”? Choose an answer A cat >abc.txt B touch abc.txt C >abc.txt D echo abc.txtIn your notebook, you want to load a CSV file into a DataFrame df. This CSV is in the path 'data/payments.csv' relative to the notebook. Which command do you use? Select an answer: df = pd.read_excel('payments') df = pd.read_csv('data/payments.csv') df = csv('data/payments.csv') df = read_csv('payments.csv')
- Can someone make a flowchart out of this? ss_kiosk_df = pd.read_excel("DATA SUPREME SURVEY FORM (Responses).xlsx") ss_kiosk_rename = pd.read_excel("DATA_SUPREME_COLUMN_RENAME_MAPPING.xlsx") ss_kiosk_drop = ss_kiosk_rename.loc[ss_kiosk_rename['column cleanse'] == 'Remove'].new.to_numpy() ss_kiosk01_df = ss_kiosk_df.copy() df01_col_cleansed = ss_kiosk01_df.rename(columns=ss_kiosk_rename.set_index('old')['new'].to_dict()).drop(ss_kiosk_drop, axis=1) df01_row_cleansed = df01_col_cleansed.loc[df01_col_cleansed['Kiosk Experience'] == 'Yes'] df01_row_cleansedWhat are the resulting values of the following commands. (* 3 5)2. (+ 1 2 3) 3. (+ 2 (- 7 2)) 4. ((LAMBDA (x) (* x x)) 4)write the code to lookup, add and remove phoneentries from the phonebook text file . These are the code we use for the lookup, add and remove in the case statement.(Lookup)# Look someone up in the phone bookgrep $1 phonebook (add)echo "$1 $2" >> phonebooksort -o phonebook phonebook (Remove)grep -v "$1" phonebook > /tmp/phonebookmv /tmp/phonebook phonebook Write a complete Bash script which will accept up to three command-line arguments: the first one is either (lookup, add or remove), the second one is a name enclosed in single quotes and the third one (if doing an add) is a phone number enclosed in single quotes. Using a case statement to match on either lookup, add or remove, the script should then perform the requested operation. Again here, you should first check for null arguments before continuing with the rest of the script or requested operation. In addition, the person may not be in the phonebook for lookup or remove so, you need to account for this.
- Which cat command is used to create empty files? i. cp ii. cat iii. touch iv. createWhich of the following utilities was designed to support data extraction from tabulated files? sed grep awk uniqTry giving these 2 commands $ echo cat$ cat echoExplain the differences between the output of each command.







