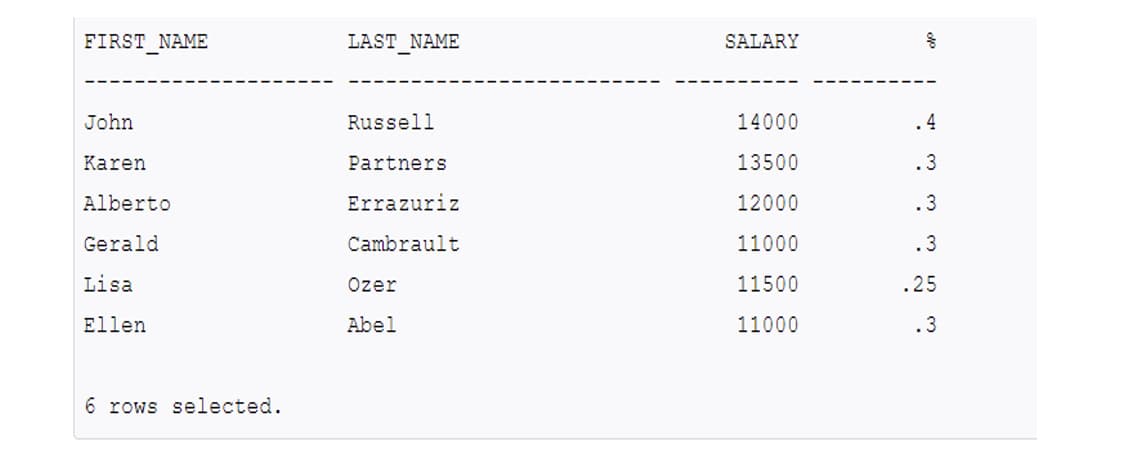
FIRST NAME LAST_NAME SALARY John Russell 14000 .4 Karen Partners 13500 .3 Alberto Errazuriz 12000 .3 Gerald Cambrault 11000 .3 Lisa Ozer 11500 .25 Ellen Abel 11000 .3 6 rows selected.
Q: Write a python program that takes a string as an input from the user and then modifies the string in…
A: Takes a string as an input from the user and then modifies the string in such a way that the string…
Q: Create an ordered link list to hold Strings. Name it OList.java Implement only the following…
A: Given data, Create an ordered link list to hold Strings. Name it OList.java Implement only the…
Q: Compliance with software accessibility standards is, with a few exceptions, optional and voluntary…
A: Increasing the revenue: By the following way a software company can earn profit even by providing…
Q: Question 1) . Apply Master Theorem to bound each one of the following recurrence relations using…
A: The master's theorem for a recurrence relation T(n) = aT(n/b) + f(n) is defined using the following…
Q: CAN SOMEONE CONVERT THIS CODE TO C++ OR JAVA this is assemnly code main: push rbp mov rbp, rsp mov…
A: Given assemnly code main: push rbp mov rbp, rsp mov DWORD PTR [rbp-12], 0 jmp.L2 .L4: mov eax, DWORD…
Q: How can i find the number of '!' chars in the user entered string. Programming language: JAVA
A: Step-1: Start Step-2: Declare a variable str and take input from user Step-3: Declare a variable…
Q: Only mobile networks employ wireless technology for the air interface between phones, antennas, and…
A: Introduction The lines that connect the main network, or backbone network, to the tiny sub-networks…
Q: 2. Encrypt the word SHIELD using an alphabetic Caesar shift cipher that starts with a shift of 8 (A…
A:
Q: Suggest measures that would help children overcome the digital divide
A: As per this question we need suggest measures that would help children overcome the digital divide…
Q: Assume the processor submits a cache request while a block from the write buffer is being returned…
A: Introduction: The write buffer as well as the cache are self-contained. The cache will be able to…
Q: Using 4-bit unsigned numbers representation multiply 0011 x 0100. Use the serial multiplier…
A: we will solve this in step No. 2
Q: Why do compilers make use of parsing techniques that only work with a subset of all grammars, rather…
A: Introduction: Because parsing techniques for any clear grammar are inefficient and difficult.In…
Q: In the midst of globalization, have technology such as the internet fostered a more harmonious or a…
A: Internet has created a more harmonious society amidst globalization. Explanation: Since technology…
Q: Give three words contained in the language accepted by the automaton A, and three words not…
A: Here, we are going to design a automaton first and then write 3 words accepted by automaton A and 3…
Q: Must be written in Python The amount of time students spent studying for an exam is exponentially…
A: According to the information given:- We have to follow the instruction to get the desired output.
Q: 1. Convert the NFAS from Figures 1.16 into equivalent regular expressions. Figures 1.16
A:
Q: IoT systems are becoming more complex. What are the preconditions for contemplating the usage of…
A: Introduction: However, all full IoT systems have a common characteristic in that they are comprised…
Q: class Pet: def _init_(self, name, species): self.name - name self.species - species def…
A: Task : Given the python code. The task is to find the output of the code.
Q: Implementation of Business Model Canvas in real time running company
A: Please find the detailed answer in the following steps.
Q: Display first name, last name and job title of all employees.
A: NOTE - Here I have Oracle SQL to solve the given problem. I have used the Select statement to…
Q: Write a single pseudocode statement that indicates each of the following: -Display the message…
A: Pseudocode is an informal way of writing programming language independent code to help programmers…
Q: Assume register $t0 and $t1 contains 0X020A007E and 0×FFFFFFF0 respectively. The content of $t0…
A:
Q: Why is it better to hash a password stored in a file rather than encrypt it?
A: It is usually preferable to hash a password rather than encrypt it when storing it in a file because…
Q: Character devices are usually faster in transmitting data than block devices. Is this statement true…
A: Block devices are basically the storage devices which helps in providing the data operations in a…
Q: Timers were required in our rdt protocols for a variety of reasons.
A: Given: Timers were required in our rdt protocols for a variety of reasons. To ensure safe data…
Q: Given the below Binary Search Tree, Answer the following questions: 100 70 212 22 99 166 300 63 150…
A: Process to find predecessor or successor of a node x in binary search tree:->perform inorder…
Q: Computer science How do app developers profit from their app if it necessitates the use of the…
A: Introduction: According to some estimates, the flexible application business might grow by as much…
Q: What are some of the benefits of operating systems that are not dependent on a particular platform?
A: Introduction: When a computer user interacts with computer hardware, the Operating System (OS) is…
Q: Computer Science Create UML component diagram and a UML Deployment diagram for the following…
A: Create UML component diagram and a UML.
Q: dangerous function below throws an error if it is given a certain integer number a. That is, the…
A: Program - def dangerous(a): z = 9302648 x = z + a return a result = dangerous(66/0)print("The…
Q: Computer Science A problem with using a production system to control robots is the Qualification…
A: A. • Functional Severity: criticality of the failure to the robot's functioning (non-critical,…
Q: Q2: Calculate the physical address for the following instruction (MOV DX, [SI]) knowing that the…
A:
Q: Write a Java Program to take 3 integers(a.b.c) from the user, print "Great Number" if one of b or c…
A: Required:- Write a Java Program to take 3 integers(a,b,c) from the user, print "Great Number" if one…
Q: MODEL SMALL .STACK 10OH .CODE MOV AX, ӨxЗС MOV BX, 000000000 ADD AY BY
A: Below the assembly code with resolve the error
Q: 1. What is Karnaugh map (K-map)? Give different figures of K-map. 2. What is a universal gate? Give…
A: INTRODUCTION: Here we need to tell about the k-map and give examples and also tell about the…
Q: What distinguishes the TPC from the SPEC in terms of its primary objective is not immediately…
A: Introduction: As a result of its work modelling a real-world computer environment, the Transaction…
Q: What is a database audit trail, Extended Events in SQL Server Computer science
A: Introduction: In SQL Server, a database is made up of a series of tables that each hold a specific…
Q: Express the following queries in SQL: a) List first name, last name and department ID of all…
A: Find the required SQL queries given as below :
Q: Given numbers = (18, 96, 71, 95, 32, 66, 85), pivot = 96 What is the low partition after the…
A: Answer: Given Number =(18,96,71,95,32,66,85) and pivot=96 so we have to find after pivot element…
Q: ages and disadvantages of virt
A: Below the advantages and disadvantages of virtual organizations.
Q: What is technical documentation? And what is it's used?
A: answer is
Q: When it comes to embedded systems, watchdog clocks are critical.
A: Introduction: In embedded systems, a watchdog timer is crucial: The watchdog timer (WDT) is a safety…
Q: Name and explain two strategies that make combining IPv4 and IPv6 addressing in a single network…
A: IPv6 is the most recent version of internet protocol which uses 128 bit addressing to find out a…
Q: Design a PDA to generate strings of the following language (Σ={a, b}): L={a4n b2n | n ≥ 0}
A:
Q: Exercise 1 Write a code to check the number in the variable (NUM1). Using the lookup table; store…
A: The code is given below.
Q: Character devices are usually faster in transmitting data than block devices. Is this statement true…
A: Character devices means these devices sent the characters independently which can use few bytes. The…
Q: In what ways does model-driven engineering serve the organization, and how does it operate?
A: INTRODUCTION: MODEL-DRIVEN ENGINEERING: Model-driven engineering is a software development process…
Q: Write a program to determine the cost of an automobile insurance premium, based on driver's age. and…
A: car price=int(input("enter the car price"): age=int(input("enter the age") premimum=car price%3 if…
Q: Discuss CSMA/CA and CSMA/CD. Explain the function of each of these, as well as the type of network…
A: CSMA (Carrier Sense Multiple Access) is a method for controlling communication when more than one…
Q: i. The following program consists of 3 concurrent processes and 3 binary semaphores. The semaphores…
A: Introduction: If all the three semaphores are initialized to 0 and all are waiting in the first…
Step by step
Solved in 3 steps

- Explain this code detail by detail like putting comments private void table_update() { int CC; try { // It is for SOMETHING ETC.*** Class.forName("com.mysql.jdbc.Driver"); con1 = DriverManager.getConnection("jdbc:mysql://localhost/linda","root",""); insert = con1.prepareStatement("SELECT * FROM record"); ResultSet Rs = insert.executeQuery(); ResultSetMetaData RSMD = Rs.getMetaData(); CC = RSMD.getColumnCount(); DefaultTableModel DFT = (DefaultTableModel) jTable1.getModel(); DFT.setRowCount(0); while (Rs.next()) { Vector v2 = new Vector(); for (int ii = 1; ii <= CC; ii++) { v2.add(Rs.getString("id")); v2.add(Rs.getString("name")); v2.add(Rs.getString("mobile")); v2.add(Rs.getString("course")); }…Sort results by reverse domain: Create a data category. Domain that depicts domain names, including a suitable compareTo() function where the natural order is in reverse domain name order. For example, cs.princeton.edu's mirror name is edu.princeton.cs. This is helpful for analysing site logs. Use s.split(".") to divide the string s into pieces separated by underscores. Create a client that takes normal input and displays the reverse domains in sorted order.MySql Workbench CREATE TABLE students ( id INT PRIMARY KEY, first_name VARCHAR(50), last_name VARCHAR(50), age INT, major VARCHAR(50), faculty VARCHAR(50)); CREATE TABLE location ( id INT PRIMARY KEY, name VARCHAR(50), rooms INT); CREATE TABLE faculty ( id INT PRIMARY KEY, name VARCHAR(50), department_id INT); 1. List last name of all students whose first name is longer than 4 letters in ascending order accordingto the last name. Duplicated rows should be removed from the output.2. Count the total number of rooms in Location.3. Find the number of students in each major.4. Find the number of employees in each department who get no commission or have salary less than5000.5. Find the maximum salary of employees in each department that the employee was hired 15 yearsbefore now. *hint: user TIMESTAMPDIFF(<unit type>,<Date_value 1>,<Date_value 2>), the unitcan be YEAR, MONTH, DAY, HOUR, etc...
- Data Structure & Algorithm: Oware ( Warri) is a game popular in some countries of the Caribbean and Western Africa. For information about this game please see the various links below. https://www.bbc.com/news/world-latin-america-56814500 https://en.wikipedia.org/wiki/Oware https://youtu.be/0paedEX0Ixw https://www.youtube.com/watch?v=ZkyPd7ftxaw What data structures and programming algorithms you would use, and at what point and why? You are free to provide drawings and code segments to make your case.Please correct the code for this lab. Current code: import random def create_random_open_ports(): #Create empty list / dictionary port = [] ports = {} #Fill list with 100 random port numbers from 10 - 100 for i in range(1,101): random_port = random.randint(10, 100) port.append(random_port) #Create a new dictionary with ports numbers as keys new_ports = ports.fromkeys(port, 0) #Iterate through new dictionary add random 0 / 1 #Closed port = 0, Open port = 1 for key in new_ports: r1 = random.randint(0,1) new_ports[key] = r1 return new_ports # TODO: create a function called create_host_IPs() that randomly generates a list of 10 IP addresses # concatenating the 4 values into a string and appending it to a host list. The function returns the generated # host list def create_host_IPs(): host = [] octet1 = "" octet2 = "" octet3 = "" octet4 = "" #Add loop with range 1 - 11 to create the 10 host IPs EX: 192.123.11.1…import csvdicta = {}csv_reader = csv.reader(f, delimiter=") for row in csv_reader:ncol = len(row) for i in range (ncol):if((i%2==0) and (i<ncol-1) and (int(row[i+1]) < 9 orint(row[i+1])>17)):dicta[row[i]] = row[i+1]if len(dicta)==0:dictionaryprint("No anomaly login attemps")else:print("Anomaly login attempts: ",end = "")for key, value in dicta.items():print(key:value,end=""). print("\n")
- There are three tables in this database (see image). Write MYSQL code for: (1) Create a trigger “insert_inventory” on table “Inventory”. The trigger is fired after a row is inserted in table “Inventory”. After a row is inserted in table “inventory”, the “itemid”, the insertion time, and the action is inserted in table “Inventory_history”. The action is set to ‘add an item’. The oldprice is set to null. Test your trigger by inserting a row into Inventory and displaying the contents of Inventory_history. (2) Create a trigger “change_quantity” on table “Transaction”. The trigger is fired after a row is inserted in table “Transaction”. After a row is inserted in table “Transaction”, update the “quantity” in table “Inventory”. For example, if 3 iWatch are sold, then the quantity of iWatch in table “Inventory” is decreased by 3. Test your trigger by inserting a row into Transaction and displaying the contents of the relevant row in Inventory. (3) Create a trigger “change_price” on table…Given the following query SELECT StudID, CourseTitle, CreditsFROM Enrollment, CourseWHERE Enrollment.CourseTitle = Course.CourseTitle ANDEnrollment.Decision = TRUE and Course.Credits > 4which of the following indexes could NOT be useful inspeeding-up the query? a) tree-based index on Enrollment.CourseTitleb) hash-based index on Enrollment.Decisionc) hash-based index on Course.CourseTitled) hash-based index on Course.Credits Can someone explain me step by step which is the correct answer and why,please?Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions: Transaction SQL Statement Retrieve the flight number, departure and arrival airports of all British Airways. Retrieve the name of every passenger together with their flight number and the associated company. Retrieve all flights departed from all airports in London. Retrieve the ticket numbers…
- Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions:1. Retrieve all rows in Airport table for all the airports in London city.2. Retrieve all British and German passengers.3. Retrieve all names of all the passengers.4. Retrieve the flight number, departure and arrival airports of all British Airways.5. Retrieve the name of every passenger together with their…Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions: Transaction SQL Statement Retrieve all rows in Airport table for all the airports in London city. Retrieve all British and German passengers. Retrieve all names of all the passengers. Retrieve the flight number, departure and arrival airports of all British Airways. Retrieve the name of…Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions: please if you could give all the sql statements needed i will appreciate that, and i promise to put thump up Transaction SQL Statement Retrieve all rows in Airport table for all the airports in London city. Retrieve all British and German passengers. Retrieve all names of all the passengers.…











