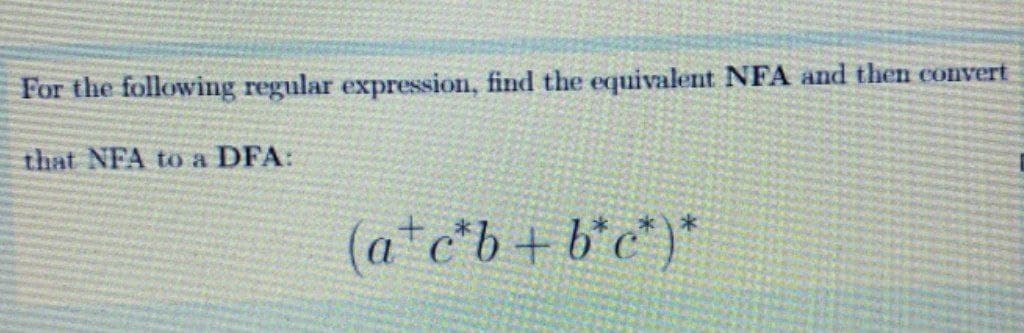
For the following regular expression, find the equivalent NFA and then convert that NFA to a DFA: (a*c*b+b*c°)*
Q: What is Swap space?Explain LILO?
A: The Answer for the given question is in step-2.
Q: When it comes to establishing and maintaining cable networks, why is following a structured cabling ...
A: INTRODUCTION: Cabling Structured: Structured cabling is a term used in the cable management industry...
Q: How do you figure out how much RAM LINUX uses? Computer science
A: Let us see the answer:- Introduction:- There are many commands to check that how much RAM or memory ...
Q: The worst case time complexity for insertion, deletion, and search is O(logn) for a, binary tree bin...
A: Solution1: the correct option is (c) AVL tree Explanation: Because AVL tree has a property with no d...
Q: What does the Linux system utilize to delay a service's start at boot time?
A: The sleep command is used by Linux for delaying the start of a service at boot time. The sleep comma...
Q: Write a C++ program that tests the function main and the functions discussed in parts 1 through 5. (...
A: Pass the alpha array as constant pointer so that alpha doesn't gets updated and beta can be udpated
Q: 1. Identify the suitable path using DFS 2. Give the complexity of DFS when using adjacency list./
A: Introduction: Here we are required to show the suitable path using DFS for the given graph, also we ...
Q: What is the abbreviation for the American Standard Code for Information Interchange in Computer Scie...
A: Introduction: This question is about the abbreviation for the American Standard Code for Information...
Q: 7). The microcontroller has only one or two instructions to move data between memory and CPU. A. Tru...
A: According to the question the microcontroller are used to moved the data one source to another on th...
Q: hich of the following options contain only things that should be avoided in a data visualization? ...
A: Lets see the solution.
Q: Write a C program using switch statement. The program will read a character (op) and will calculate ...
A: 1) Below is C Program using switch statement to read a character(op) and calculalate and print volum...
Q: Need matlab code and explanation Share output
A: This is a required code to draw above periodic signal in matlab. See below step for code and output.
Q: 7). The microcontroller has only one or two instructions to move data between memory and CPU. A. Tru...
A: microcontroller have one or two instruction to move data between memory and CPU
Q: conditional structures Create a program that will ask three (3) numbers from the user then display ...
A: C++ program to print largest among the tree number
Q: cle delves into the details of how to program parallel compu
A: Below the How to program parallel computing applications
Q: What is the purpose of a Branch Prediction Buffer (BPB) or Branch HistoryTable (BHT), and what is sa...
A:
Q: do a chart Showing the: load, increments, select lines and Memory.
A:
Q: A Locker can be opened by A and B when they are both there, as the locker has two keys, one of which...
A: Below is the answer to above question. I hope this will helpful for you....
Q: 4. Exercise. Q1. Consider transferring a file of 5000 bytes from Host A to Host B. Assume an MSS of ...
A: The solution to the given question is:
Q: Which types of systems lend themselves to agile development the best?
A: Agile Development Methodologies include the following: The use of an agile approach to project manag...
Q: To add scripting to the existing web page and work with JavaScript Es-6 features like class, object ...
A: script.js var itemList = new Set(); // DO NOT CHANGE THIS STATEMENT var Item= class Item{ // DO NOT...
Q: computer science - Discuss the reasons for globalisation and the use of global information systems,...
A: Introduction: The reasons for globalisation and the use of global information networks, including e-...
Q: Using C++ Language In this program you will write a function of void return type named compare that...
A: rand() function will generate random numbers Here requirement is generate random number between 1 a...
Q: 3. Given the following memory values and a one- address machine with an accumulator and a register, ...
A: The following instructions are given in binary:1. 0101 0000 0001 00002. 0101 0000 0001 01003. 0101 0...
Q: 1- Determine the minimum expression for each K-map in figure below CD CD CD CD CD AB AB 100 1 AB 0 0...
A:
Q: Describe virtualization and its various forms (Language, Operating System and Hardware).
A: Virtualization is a technique of how to separate a service from the underlying physical delivery of ...
Q: Breadth first search and best-first search.
A: Introduction Breadth-First Search is a kind of algorithm that basically demonstrates a tree that con...
Q: This binary number is represented using 32-bit single precision floating point representation. What ...
A:
Q: Arduino board. 2. Arduino Integrated Development Environment
A: Interface LEDs on the Arduino board - In interface LEDs we have two LED which are connected wit...
Q: What is the name of the type of network address translation that is used to allow multiple users to ...
A: Introduction: The issue seeks to determine which Network Address Translation may be performed with a...
Q: What is the standard procedure for requesting permission to make a network change in a major corpora...
A: Introduction: Network: Multiple computers are linked together via a network to share resources (such...
Q: How would you change the file's name from "in" to "out"? on the Linux platform
A: mv command is used to rename a file
Q: On this code, if that is true for all characters, but only if I put character: %%, it fails the prog...
A: The fixed code for the python program is in the next step.
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let Bob’...
A: The answer is
Q: 3+5 748 (a) Prefix (b) postfix
A:
Q: In Linux, what is network bonding? (short answer is ok) Computer science
A: Network Bonding is a process of combining more than two network interfaces to form a single network ...
Q: Hexadecimal is used in Machine Language. Is it true or false?
A: Let us see the answer
Q: How should the security of a database differ from the rest of the system's security? What difference...
A: The database security is the most important factor in any organization as data is very powerful. Dat...
Q: a. Describe briefly symmetric and asymmetric cryptography! and What are the benefit and the drawback...
A: Symmetric and asymmetric cryptography . Their benefits and drawbacks
Q: Explain any ten(10) React Native APIs in a few words.
A: React Native: It is a JavaScript framework for writing natively for mobile applications. It is used...
Q: What are the reasons for the importance of software development? In order to improve software develo...
A: Introduction: Software development is a collection of computer science activities concerned with the...
Q: Write a program to calculate and display ticket price. using python The flight ticket price inc...
A: ALGORITHM:- 1. Take input from the user for all the variables. 2. Calculate the cost of the ticket b...
Q: Rewrite the two print statements in the code using format printing to show the result in two decimal...
A: As the requirement is to rewrite the two print statements in the code using format printing we use f...
Q: conditional structures Create a program that will do the following: Press 1 to ADD Press 2 to Subtr...
A: C++ program to calculate the addition , subtraction ,multiplication, division
Q: Design of ALU control circuit for maximum 4 input variables (Ainvert, Binvert , F1 and F0) using QMM
A: Solution ::
Q: The Collatz conjecture says that you will always eventually reach the number 1. This conjecture has ...
A: python program: # taking input from the user N = eval(input("N:")) # if the input is non-positive t...
Q: Install JavaFX SceneBulder, make sure you have the relevant Java version Then develop the following ...
A: What is JavaFX scene builder: JavaFX Scene Builder is a visual layout tool that allows users to easi...
Q: One disadvantage of actively integrating a user with a software development team is that the user ca...
A: Introduction: A software development process breaks down software development activity into smaller,...
Q: Create an HTML page that should display the error status message when the user clicks the button ‘Cl...
A: employee.html <!-- DO NOT ALTER THIS FILE --> <!DOCTYPE html> <html> <body> ...
Q: The hosted software approach for enterprise software assists customers in acquiring, implementing, a...
A: Introduction: The hosted software paradigm allows the programme or application to be hosted on a ded...
Step by step
Solved in 5 steps with 5 images

- Using Verilog operators listed in Table 8.2 , assume that A=4′b0110, B=4′b0010, and C=4′b0000 and evaluate the result of the following operations:A * B; A + B; A − B; ∼C; A & B; A B; AΛB; & A; ∼C; A B;A& & C; A; A < B; A > B; A! = B;For the following logical statements below: A.B.C + A.B'.C + A.B' A'.C' + A'.B.C + A'.B 1. Create truth tables2. Represent the functions represented in the truth tables as sum of products3. Simplify each one of the logical statementsConvert the following NFAs to the equivalent DFA

