function
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter15: Recursion
Section: Chapter Questions
Problem 8SA
Related questions
Question
(C
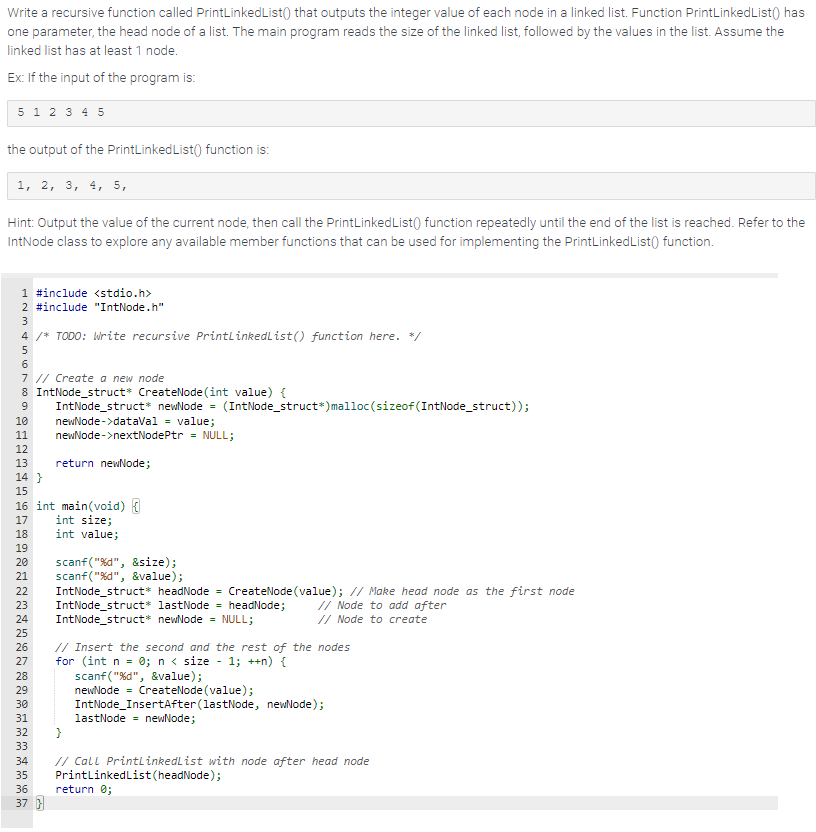
Transcribed Image Text:Write a recursive function called PrintLinkedList() that outputs the integer value of each node in a linked list. Function PrintLinkedList() has
one parameter, the head node of a list. The main program reads the size of the linked list, followed by the values in the list. Assume the
linked list has at least 1 node.
Ex: If the input of the program is:
5 1 2 3 4 5
the output of the PrintLinked List() function is:
1, 2, 3, 4, 5,
Hint: Output the value of the current node, then call the PrintLinked List() function repeatedly until the end of the list is reached. Refer to the
IntNode class to explore any available member functions that can be used for implementing the PrintLinked List() function.
1 #include <stdio.h>
2 #include "IntNode.h"
3
4 /* TODO: Write recursive PrintLinkedList() function here. */
5
6
7 // Create a new node
8 IntNode_struct* CreateNode (int value) {
9
IntNode_struct* newNode = (IntNode_struct*) malloc(sizeof(IntNode_struct));
10
11
12
13
14 }
15
16 int main(void) {
17
int size;
18
int value;
19
20
21
23
22 IntNode_struct* headNode = CreateNode (value); // Make head node as the first node
IntNode_struct* lastNode = headNode;
22222222mm
25
24 IntNode_struct* newNode = NULL;
29
newNode->dataVal = value;
newNode->nextNodePtr = NULL;
return newNode;
30
26 // Insert the second and the rest of the nodes
27 for (int n = 0; n < size - 1; ++n) {
28
scanf("%d", &value);
newNode = CreateNode (value);
IntNode_ InsertAfter (lastNode, newNode);
lastNode = newNode;
31
scanf("%d", &size);
scanf("%d", &value);
33
32 }
37}
// Node to add after
// Node to create
34 // Call PrintLinkedList with node after head node
35 PrintLinkedList (headNode);
36
return 0;
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning