f(x) = |x| %3D AREA absolute, CODE EXPORT main ALIGN ENTRY main PROC
Q: ArrayList
A: Answer is in given below:-
Q: Explain what the word "firewall" implies in the context of network security, as well as how it is…
A: Firewall: A firewall is a network security device that monitors and filters incoming and outgoing…
Q: Explain the features of the pandas library file in Python in detail.
A: In the below step we provide the some features of pandas library.
Q: For a rudimentary network, which type of routing path (static or dynamic) would you use? Why would…
A: Given: Static routing, simply said, is ideal for networks that do not change. Dynamic routing…
Q: A number of years ago at an ACM SIGCSE Technical Symposium, there was a presentation from a school…
A: Twisted pair cable is the ordinary copper wire that connects home and business computers to the…
Q: Make a list of databases that contain your data. How is each database's data stored, and how often…
A: Given: Tables are used to store all of the information in a database. If a number in a field of the…
Q: What do you think are the best firewall management techniques? Explain.
A: Firewall: Firewall Security Management Software allows you to monitor and configure firewalls from a…
Q: Create a process graph for the following program. int main () { int x = 4; if (fork() == 0)…
A: fork() system call is used to create the child processes. For n fork() system calls 2n processes are…
Q: In this section, we'll discuss how to write an array notation.
A: Array notation: The following is the syntax for writing all array items. Array-name[*] => PUT…
Q: Using an example, what are the essential components of the HTTP request and response?
A: HTTP Response - There are 3 main components of HTTP response - 1.) Status Line 2.) Header 3.) Body…
Q: Why is it necessary for the network layer protocol to offer packetizing services to the transport…
A: Definition: The transport layer is in responsibility of segmenting data, transmitting segments to…
Q: Test data, an integrated test facility, and parallel simulation are compared and contrasted.…
A: Integrated test facility and Parallel: Using test data, the auditor creates false transactions that…
Q: What do you consider to be the meaning of the term "computer"?
A: Computer: It is an electrical gadget that can be programmed and that manipulates information or…
Q: A list of the five subtypes of DoS attacks may be found here.
A: The Answer is
Q: Collision domains broadcast domains is a Cisco switch command that can be used to debug VLAN trunk…
A: In order to see if your VLANs and your peers' work together, type "display interface trunk." It…
Q: Describe Computer science has benefited greatly from John von Neumann. Specifically, what are his…
A: Von Neumann architecture is the design upon which many general purpose computers are based.
Q: What is the ultimate purpose of Artificial Intelligence (AI)
A: The goal of AI is to provide software that can reason on input and explain on output. AI will…
Q: Packet filtering controls access to a network by analyzing the incoming and/or outgoing packets and…
A: The Answer is given below step.
Q: How do cloud-based network services and applications get to their final destination?
A: There are three primary methods to connect: Cloud hosting makes cloud resources available for apps…
Q: Assume you're a systems analyst working on a comprehensive test plan. Describe the testing…
A: analyzer of information systems: A system analyst is someone who gathers and organizes…
Q: Is it possible for a single individual to orchestrate a distributed denial of service attack?
A: Introduction: What is a distributed denial-of-service assault, and how can a single individual…
Q: If the task runs an average input of size 100, rank the algorithms from least time- complex to…
A: The answer is
Q: Create a C function that will input 10 numbers and will perform the following 1. Display all even…
A: I give the code in C along with output and code screenshot
Q: What were the three options available to GE for building the hardware and software capabilities…
A: There are three components to the Internet: Sensors, microprocessors, storage, controls, software,…
Q: b. With the aid of an example, describe the dimensional table
A: A dimensional table contains the all details about the fact. For example, a time dimensional table…
Q: Explain how a botnet may be built and how it can be used to launch a distributed denial of service…
A: The points below may be utilised to build a botnet: Prepare host systems to discover the…
Q: What does it take to be a successful manager?
A: Intro: In any sector, one of the most often discussed topics is how to become a better boss. This is…
Q: Exactly what is a system selection report?
A: System Selection Report: Work with the team to develop deliverables and include stakeholders in…
Q: Describe the similarities and differences between a firewall and a stream of packetized data.
A: Firewall: Stateful firewalls may track and protect depending on traffic patterns and flows by…
Q: Referring to the register transfer system below, determine the transfer operation, which will happen…
A: Answer
Q: Considering the importance of the network to the organization's day-to-day operations, please…
A: Network to the organization's: You may have access to opportunities that you would not be able to…
Q: What is a firewall for? How can it be used?
A: Start: At its most fundamental level, a firewall is the physical barrier that separates a private…
Q: In what ways does a firewall serve its purpose and how does it operate?
A: A firewall is software or hardware that can be configured to block data from certain locations,…
Q: Compared to other programming languages, how does assembly language vary from the others?
A: Compared to other programming languages, how does assembly language vary from the others? Answer:…
Q: Where can I learn more about SSL's supported protocols? How do SSL and SSH vary one from the other?…
A: Difference between SSL and SSH are as follows: SSH is a secure tunneling protocol that allows you to…
Q: Could you please clarify what arrays are?
A: Given To know about the arrays.
Q: In what ways might an operating system be described as essential?
A: Operating System An operating system is a system software that act as interface between software and…
Q: What are microcontrollers and how are they used
A: Introduction What are microcontrollers and how are they used?
Q: A firewall serves what purpose? What are the rules for packet filtering in this environment?
A: A firewall's primary function is as follows: The primary role of a firewall is to A security device…
Q: Collision domains broadcast domains is a Cisco switch command that can be used to debug VLAN trunk…
A: VLAN Trunk: The show interface trunk command may be used to determine if the local and peer-native…
Q: For example, if you were to create a media company and needed graphic designers and media producers,…
A: Given: A backup storage device is used to duplicate data that is currently in use. Data that is…
Q: Why does the network layer protocol need to provide transport layer packetizing services? For what…
A: Question: Why does the network layer protocol need to provide transport layer packetizing services?…
Q: In C#, what is a Collection? Explain the many sorts of collections.
A: Introduction: Collections are, in fact, modifiable. Mutables are just data that will not change once…
Q: What protocols are included in SSL? Is there a difference between a secure connection and a secure…
A: SSL protocols: These features address basic problems regarding web and other TCP/IP communication.…
Q: Java is an object-oriented programming language. Objects are known to exist in the real world. As a…
A: Foundation: A Programming in the object-oriented paradigm, in which each and every item is…
Q: ogic
A: Linear address: The linear address space means everything addresses that can be shaped on the…
Q: When designing a huge system's architecture, why do you often use a variety of architectural…
A: Architectural Patterns: Within a specific context, an architectural pattern is a broad, repeatable…
Q: C++ is a programming language. What are the advantages and disadvantages of using an array?
A: Answer the above question are as follows:
Q: What would be the BER encoding of {weight, 190} {lastname, “Sloanel”}?
A: Given: {weight, 190} {lastname, "Sloanel"} The above given sets are BER encoded as: a) {weight, 190}…
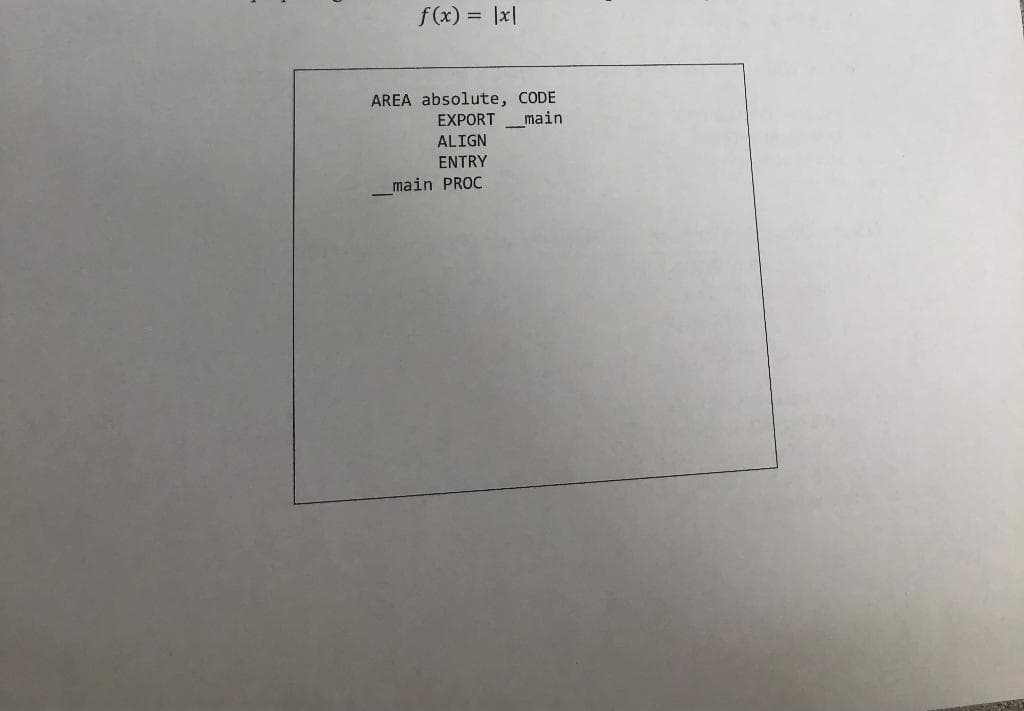
Complete the assembly subroutine below that calculates the absolute value of x. Consider proper argument and return value handling while using registers.
f(x) = |x|j
Step by step
Solved in 2 steps

- # Create Custom Transformer Create a custom transformer, just as we did in the lecture video entitled "Custom Transformers", that performs two computations: 1. Adds an attribute to the end of the numerical data (i.e. new last column) that is equal to $\frac{x_1^3}{x_5}$ for each observation. In other words, for each instance, you will cube the $x_1$ column and then divide by the $x_5$ column. 2. Drops the entire $x_4$ feature column if the passed function argument `drop_x4` is `True` and doesn't drop the column if `drop_x4` is `False`. (See further instructions below.) You must name your custom transformer class `Assignment4Transformer`. Your class should include an input parameter called `drop_x4` with a default value of `True` that deletes the $x_4$ feature column when its value is `True`, but preserves the $x_4$ feature column when you pass a value of `False`. This transformer will be used in a pipeline. In that pipeline, an imputer will be run *before* this transformer. Keep…Write an Add method that adds the contents of the decPrice variable to the lstPrices control.Simple Student Management System Build the following app using Python Tkinter library. Using this app, user can • add student information • view all students • search student(s) by name • remove student by id Add • First name, last name, date of birth cannot be blank while adding a specific student information. • However major can be blank, which gets set to "Undefined" if left out blank. • Student Id is automatically generated by the program (ex: 1001, 1002, 1003, 1004 ….) If the user keeps a mandatory field blank (ex: First name) and presses "Add Student" button, it displays the following message box: first name is required If the user successfully enters all the necessary information and presses the "Add Student" button, it displays the following confirmation message box: student added View All When the user presses the "View All" button, it displays all the student’s information (Id, First name, Last name, Date of birth, and Major) in a nice formatted way. Example below: • Must…
- C programming pseudocode pointers help. { totalInAGivenHour+=*(rawReadings+ monthNo*30*14*4 + 14*4*nThDateOfMonth+ 4*nThHourOfDateFrom7AM + nThReadingTimeOfHour); // the pointer is to assign the values in the bracket and storing them in totalInAGivenHour }To place a node in the left region of a BorderPane p, use ___________. Question 4 options: p.setEast(node); p.setWest(node); p.setLeft(node); p.getChildren().add(node);function myChoice(items) {if (!this.value && !this.items) {this.items = items[0];} else if (!this.value || (params.length > 0 && params[0] == "rechoose")) {let index = Math.floor(Math.random() * (this.items.length - 0)) + 0;this.value = this.items[index];return this.value;}return this.value;} var a = myChoice([1, "a", 3, false]);console.log(myChoice(3, 12));console.log(myChoice(51, -2));console.log(myChoice("happy", false));console.log(myChoice([1, 2, 3]));console.log(myChoice("rechoose"));console.log(myChoice(a, a)); these are directions and examples myChoice( items ) This function accepts a list of items as input and creates a function that returns a randomly-chosen item. After choosing a random item, that same item will be always be returned, regardless of the functions input, with one exception. If the first input is the string 'rechoose', then a new random item will be chosen and therafter returned. this is KEYYYY!! Examples var a = myChoice( [1, "a", 3, false]…
- Computer Science Write in Javascript please and use high order functions liek map or filter or reduce let obj = [ { mode: "hot" }, { temp: "low" }, { mode: "cold } ] I want to create a function that get object by key such as: myFunc("mode"); returns { mode: "hot" } next call of myFunc("mode") returns { mode: "coldCompare userNumber with compareNumber and display 'Numbers are not equal' if the numbers are different. Then, display 'Variables are not identical' if the variables are not identical (not strictly equal). let compareNumber = 3; // Code will be tested with: 3, 8, 42let userNumber = '3'; // Code will be tested with: '3', 8, 'Hi'A c++ code that performs a search for a specific employee and returns the employee ID if found and 0 if not: int findEmployeeById(Employee list[], int size, int myId)
- What happens when a programmer attempts to access a node's data fields when the node variable refers to None? How do you guard against it? *PYTHONstruct Info { int id; float cost; }; Given the struct above, the following code segment will correctly declare and initialize an instance of that struct. Info myInfo = {10,4.99}; Group of answer choices True False ============== Consider the following code fragment. int a[] = {3, -5, 7, 12, 9}; int *ptr = a; *ptr = (*ptr) + 1; cout << *ptr; Group of answer choices 4 -5 3 Address of -5 =============== What will happen if I use new without delete? Group of answer choices The program will never compile The program will never run The program will run fine without memory leak None of theseDouble any element's value that is less than controlValue. Ex: If controlValue = 10, then dataPoints = {2, 12, 9, 20} becomes {4, 12, 18, 20}. #include <iostream>using namespace std; int main() { const int NUM_POINTS = 4; int dataPoints[NUM_POINTS]; int controlValue; int i; cin >> controlValue; for (i = 0; i < NUM_POINTS; ++i) { cin >> dataPoints[i]; } /* Your solution goes here */ for (i = 0; i < NUM_POINTS; ++i) { cout << dataPoints[i] << " " ; } cout << endl; return 0;}

