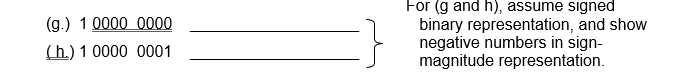
(g.) 1 0000 0000 binary representation, and show negative numbers in sign- (h.) 1 0000 0001 magnitude representation.
Q: purpose in making the Three Level ANSI SPARC Architecture ma
A: In 1971, the Database Task Force (DBTG) recognized the need for a two-tiered approach with views and...
Q: 9. Do Programming Exercise 3 from Chapter 5 using a function grade(score) that returns the letter gr...
A: Functions in python: Functions provide a way to break problems or processes down into smaller and in...
Q: What effect does Al have on "Systems Analysis and Design"?
A: Introduction: The primary objective of systems analysis and design is to enhance organizational syst...
Q: A U (B U C) (CU B) - (A N B) (A - B ) N (A - C)
A:
Q: how a hash table with linear probing collision handling works internally. Illustrate by showing a ha...
A: The hash table is a special collection used to store the KeyValue element.Caution is implemented in ...
Q: Write down the transition function values for each state and symbol for the DFA in question 1(a) and...
A: For the given language in 1.a which is: A language that accepts strings of length not more than 5 an...
Q: Create a read function and a print function
A: Question is to implement two functions read and print. It is given in next step.
Q: Create a flowchart that determines whether the positive number typed by the user is a prime number o...
A: Here in this question we have asked to create a flow chart that check for given number is prime numb...
Q: In C++, a variable that has been defined but not initialized may not be used as an 1-value Or r-valu...
A: A variable is a name of memory location.
Q: (1) Show the solution of following recurrence relation T(n) is O (nlogn) by using substitution metho...
A:
Q: Q1: Consider the following instruction: Instruction1: AND Rd,Rs,Rt Instruction 2: SUB Rd, Rs, Rt
A: a ) ALU Operation is AND,BSrc will look to register,OpSel will tell ALU to perform AND. MemW is fal...
Q: What's the difference between symmetric and asymmetric key encryption? What exactly does GSM stand ...
A: Symmetric key encryption: Symmetric key encryption is the process to encrypt the actual content by u...
Q: Using a the shopping situation, explain briefly what is all about computer security, highlighting o...
A: A) Using a the shopping situation, explain briefly what is all about computer security, highlighting...
Q: This causes a recurring impasse in your installation's spooling process. Is it possible to resolve ...
A: In a functioning framework, a deadlock arises when at least two cycles need an asset held by the oth...
Q: In which cases you can transform an else-if statements to switch? Provide an example
A: The solution to the given problem is below.
Q: People go to the beach and often buy a bunch of stuff that will only be used at the beach. Pretend y...
A: Assume that we are placing the input txt file in the same folder as the working directory. Please fi...
Q: plot the curve between theta and x axis by using matlab microsoft
A: polarplot(theta,rho) polarplot(theta,rho,LineSpec) polarplot(theta1,rho1,...,thetaN,rhoN) polarplot(...
Q: What role do individuals play in a computer system?
A: Introduction: Information System Information systems (IS) refers to the combination of hardware and...
Q: Using C program. Create an array of 15 integers. Add all elements located at ODD index positions and...
A: #include <stdio.h> int main(){ //creating array and variables int a[15],sum_odd,sum_ev...
Q: sider the following JavaScript program: var a, y, c; function sub1() { var b, z, c; function sub2()...
A: the answer is an given below :
Q: ormation about each player. The UML diagram is given below. Player -name: string -symbol :char P...
A: given - Write a program with C# to Simulate a game of tic tac toe. A game of tic tac toe has two pla...
Q: P4: 0 is an equivalence relation
A: Big theta is either the exact performance value of the algorithm, or a useful range between narrow u...
Q: Program to input the elements(integer type) of a array of size 17 and check if all the elements of t...
A: Code: class Main{ public static void main(String args[]){ int a[]={33,3,4,5,5,8,96,23,11,56,78...
Q: Explain the GRANT statement and how it pertains to security. What kinds of privileges are available?...
A: Introduction; the question is about Explaining the GRANT statement and how it pertains to security. ...
Q: If the name of a Mongoose model is Student, what is the name of its corresponding collection in the ...
A: mongodb collection is- db.createCollection(student,document) ...
Q: Explain why it is logical to presume that advances in information technology are driven by people an...
A: Introduction: People and information systems are the driving drivers behind information technology a...
Q: What methods do forensic investigators use to gather volatile and non-volatile data from Windows sys...
A: Introduction: The process of identifying and compiling digital proof from any medium while keeping i...
Q: Which Group Policy preferences would be the most useful for typical networked Windows systems?
A: Introduction: Here we are required to mention some group Policy preferences that would be the most u...
Q: Write a MATLAB program to solve this equation (using function) X=((V-B) /(2.3A/5S))
A: Given function is X = (V-B)/((2.3*A)/(5*S)) Take the required values to solve the equation.
Q: Write two scnr.nextInt statements to get input values into birthMonth and birthYear. Then write a st...
A: According to the Question below the Solution: Output:
Q: A retail company assigns a $5000 store bonus if monthly sales are more than $100,000; otherwise a $5...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read sales of prese...
Q: Write a computer code (or using MS Excel or any technique) to sketch the curves given in polar as: r...
A: Introduction : Note: Answering in python as no language is mentioned. Given : •Range values of theta...
Q: A drink costs 2 dollars. A taco costs 3 dollars. Given the number of each, compute total cost and as...
A: start Accept numDrinks ,numTacos from the user totalCost <- numDrinks*2 + numTacos*3 print total ...
Q: Computer Science - Describe two information systems/technology concerns that you believe organisatio...
A: Introduction: Data Backup IssuesA backup copy of the data is something every business should do, eac...
Q: 1- convert the following decimal numbers to 32-bit two's complement numbers а. +17, -17 b. +35,-35 с...
A: Note - Since you have posted a question with multiple sub-parts, we will solve first three subparts ...
Q: ^^111^11111^^^ = ^^^11^1^^^ What wo
A: Sum : user will add three numbers bu using sum operator'+' subtract : user will subtract by using '-...
Q: Explain how many programing language are there?
A: The programming language is a set of rules that have a specific syntax and are used for creating sof...
Q: Given a list of integers, you want to know whether it is possible to divide the integers into two se...
A: #include <bits/stdc++.h> using namespace std; bool subset (int arr[], int n, int sum) { ...
Q: leting an element from a ha
A: Below implement deleting an element from a hash table with linear probing
Q: This is a proof by induction over, The property P =
A: This is very simple. The question is based on Propositional Logic proposition, proposition Solutio...
Q: If you have a small firm in a small facility and want to perform network networking amongst 40 machi...
A: Introduction: The question is about If you have a small firm in a small facility and want to perform...
Q: Iwc (lightning web componentO make a calendar that keeps track of the user Requested Task (a request...
A: This is a very interesting question based on the concept of arithmetic and algorithmic computer scie...
Q: Make a C program to input n numbers and will output (a) the sum of all positive odd integers, (b) th...
A: Here is the approach:- First take input from the user for the number of integers and then create th...
Q: To 3 7 $ 3 6 %24 2.
A:
Q: A linked list is developed with the following set of nodes in sequence: 25, 40, 66, 38 and 53. The l...
A: A linked list is a sequence of data structures, which are connected together via links. Linked List ...
Q: A consistency index measures the degree of inconsistency in pairwise comparisons. Discuss how you ca...
A: Actually every consistency index for pairwise comparison judgment among criteria from the goal. Co...
Q: What are the functions of HDFS in the Hadoop architecture?
A: Introduction: HDFS is an abbreviation for Hadoop Distributed File System. It serves as the primary d...
Q: What are Web-influenced sales and what is a reasonable estimate of total Web-influenced sales?
A: Web-influenced sales is an online business model in which businesses offer their products or service...
Q: = ax+b is
A: 1) f(x) = ax+b is O(x2) 2) explain a condition where the code isn't O(x). also prove witness and gra...
Q: 14. Write code that reproduces the output shown below. In [18]: # Code Here In [19]: # DON'T WRITE H...
A: The answer is given below.
Convert binary to decimal.
Step by step
Solved in 2 steps

- I want the values of numbers from positive 1 to 15 and from negative 1 to negative 15 in Signed Magnitude, Signed-2's Complement, and Signed-1's Complement representations, like this image.Represent 5 in three ways using only 8 bits: Signed-magnitude (a), signed 1's complement (b), and signed 2's complement (c).111111002 and 011100002. a) Which number is larger? b) Which is bigger on a machine utilizing signed-two's complement representation? c) Which is smaller in signed-magnitude representation on a computer?
- The data word 10101110001101 is given for transmission. Draw the following encoding formats. NRZ-L NRZ-I Bi-phase Manchester RZ Differential ManchesterWith signed binary representation, what is the range of numbers as written in binary and in decimal for an three bit cell?Show your work Using 7 bits to represent each number, write the representations of 23 and -23 in signed magnitude, 1’s complement and 2's complement integers.
- Represent −5 three ways with 8 bits: (a) signed-magnitude (b) signed 1’s complement, and (c) signed 2’s complement.Assume that a digital circuit represents numbers in 8-bit. In this circuit what is the 1’s and 2’s complement representations of -51 and +127?Show your steps. Show the 8-bit binary signed-magnitude representation for the following decimal numbers: 10910 -10910 +4310 -4310 +(0)10 -(0)10
- Find the two's complement representations, using bit strings of length six, of the following integers. a)22 b)31 c) -7 d) -19Draw the time domain representation of ASK, FSKand PSK of the binary data 110001010111Using the line coding techniques, draw the waveform of the data 01001100011In Manchester encoding and differential Manchester.

