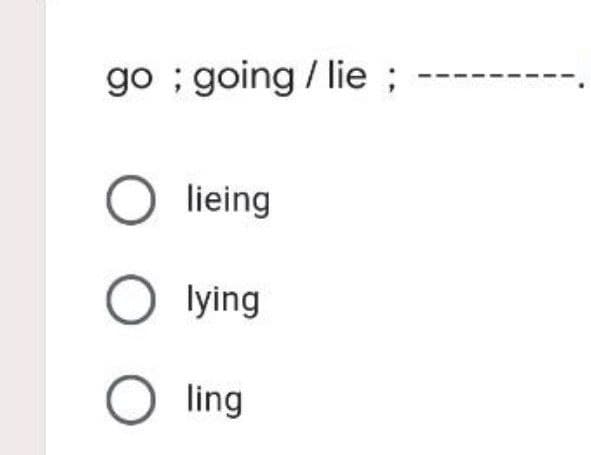
going / lie;
Q: It is feasible to set up a compiler for assembly language and an assembler in such a way that a…
A: Given: Compilers and assemblers may be programmed to sequence assembly language instructions in…
Q: It is possible to sequence the instructions for the assembler in order to reduce pipeline hazards to…
A: Intro Pipeline / Risks: A pipeline is an implementation technique in which numerous instructions…
Q: It is of the utmost importance to offer an explanation for the present convergence of digital…
A: Digital gadgets: Digital devices, sometimes known as gadgets, are innovative technological…
Q: What exactly is meant by the use of a poison package in an assault, and what does the fact that it…
A: Intro Any type of attacks involves the violation of the security by exploiting the vulnerability…
Q: The following three considerations were prioritized by website designers and developers in order to…
A: The ability of website developers to generate high-quality web design may be attributed to the…
Q: In the context of C++ and pointers. A pointer is of data type Blank 1 as it holds the address of a…
A: Note: As per student asked I answer the question. Student just asked to fill the blank space. Here i…
Q: Computers have made their way into every aspect of our society, from the workings of our economy to…
A: Computer development: Computer development has had a significant influence on human existence, and…
Q: What are the advantages and disadvantages of various authentication techniques in terms of security?
A: Introduction: This kind of authentication relies on a monitoring team or a third party, such as a…
Q: What are the most essential criteria that must be observed by web developers when developing a…
A: Beginning: To describe the criteria that Web designers must adhere to while designing a site that is…
Q: What different sorts of data structures are required in order to carry out the instructions that are…
A: Data structures: When a programme is generated, the compiler generates executable files for that…
Q: mes to the functionality that they provide, object-oriented programming and procedural programming…
A: Introduction: Below the describe functionality that they provide, object-oriented programming and…
Q: When the programme is being compiled, what kinds of exceptions are caught?
A: There are two exceptions in Java: Checked and Unchecked Exceptions. Checked exceptions are those…
Q: Explain the following: i) Connection Oriented and Connectionless Thanks in advance.......
A: The basic difference between connectionless and connection-oriented is as the name suggests that in…
Q: A time-consuming procedure for selecting the most suited programming language
A: Inspection: A programming language is nothing more than a collection of instructions for writing…
Q: The term "Network Database System" refers to a kind of database management system that is predicated…
A: Introduction: The network database system is an ownership-based database management system.
Q: What type of long-term repercussions does a data breach have for the cloud's security, and how…
A: Introduction: Here we are required to explain what type of long-term repercussions does a data…
Q: s there anything in particular that the developers are concerned about as the process of development…
A: here i am explaining development of software:…
Q: In computer logic, what are the eight symbols in a flowchart?
A: Introduction: Flowcharts are used to show a variety of different actions or steps in a process, and…
Q: Packet Switching and Circuit Switching
A: Answer: Packet switching Switching the package to transfer small pieces of data to all different…
Q: Define the terms "scope creep" and "feature creep."
A: Introduction: The following is the distinction between scope creep and future creep:
Q: What is encryption
A: To secure the data while data transfer is big task. So many attackers try to hack the data what we…
Q: Based on the following SQL statement: SELECT acct_id, balance FROM Account WHERE balance < 0 AND…
A: Answer: The given question is from Database Sql. As we know * is used to retrieve all the column…
Q: What are the benefits of having a working knowledge of how to operate computers and other modern…
A: Computer skill can be defined as a life skill in today’s world. Without the use of computers,…
Q: What exactly is meant by the use of a poison package in an assault, and what does the fact that it…
A: ARP Poisoning, also known as ARP Spoofing, is a form of Internet attack on the Local Area Network…
Q: What approaches do various operating systems utilise to protect the system's resources?
A: Introduction: An operating system (OS) is a piece of software that controls all computer functions;…
Q: In the context of computer systems, what exactly is the difference between architecture and…
A: COMPUTER SYSTEM: A computer system is a collection of elements (hardware, software, and liveware)…
Q: Investigate the ways in which magnetic secondary storage systems and solid-state secondary storage…
A: Introduction: Magnetic data storage: The capacity of data on a charged media is referred to as…
Q: It is your obligation as a university network administrator to select the appropriate NAT setup. To…
A: Intro A network administrator is the person inside an organization who is in charge of administering…
Q: Choose an ICMP-based attack, describe it thoroughly, and offer a solution.
A: Intro Choose an ICMP-based attack, describe it thoroughly, and offer a solution.
Q: The kind of data model that concentrates on concepts in the same way that computer systems store…
A: Introduction The following is the response: Data Models are key aspects of a DBMS. The way in which…
Q: Which encryption standard assures that data isn't tampered with after it's sent and before it's…
A: TLS/SSL: TLS/SSL is the most used encryption protocol, and it is used on the internet on a daily…
Q: Provide some historical context on the current trend of the convergence of digital gadgets and the…
A: The above question is answered in step 2 :-
Q: Explain why an operating system may be unable to integrate additional software.
A: Introduction: The most crucial programme that runs on a computer is the operating system.
Q: Given int[][] a = {1}, {2, 3}, {4, 5, 6}, {7, 8, 9, 10); Which of the following statements is…
A: In Step 2, I have provided answer with brief explanation---------------
Q: In order to properly deploy mobile technology, there are a number of challenges that must be…
A: A quick introduction: although there are numerous benefits to be gained by using mobile technology,…
Q: What are some of the ways dimension tables aren't normalised?
A: Introduction: Normalization is not performed on the star sshema dimension tables; however,…
Q: What precisely are "virtual classrooms," and how do their functions contrast with those of…
A: Introduction: To assist teaching and learning, educational technology employs software, hardware,…
Q: Explain various types of service categories specified in ATM networks.
A: The Atm network services are of various types. Some of them are listed as under:
Q: What forms of authorization, authentication, roles, and mitigation measures are used in small,…
A: Given: Healthcare firms must prevent the possibility of a ransomware attack and threats put on them,…
Q: A database system has taken the role of the traditional file processing system. Utilizing this fresh…
A: Introduction: A database(DBMS) is a logically organized collection of structured data, usually kept…
Q: In terms of the functionality that they both provide, could you please give a full description of…
A: Object-Oriented Programming: Object-oriented programming, sometimes known as OOP, is a kind of…
Q: Utilization of computer systems and several other types of information technology It is important to…
A: While using information technology, information should be transferred from a person to computer…
Q: In today's Internet world, why is it that the vast majority of audio and video data is sent over TCP…
A: Find the required answer given as below :
Q: When it comes to the authentication technique, what do you mean by "goals"? Why do certain…
A: Intro Authentication technology controls system access by determining if a user's credentials match…
Q: Are you in agreement with the statement that "there is no concept of client and server sides of a…
A: Inspection: For a P2P file-sharing programme, there is no idea of client and server sides of a…
Q: Which style of organisation is best for you? Why?
A: Answer: What type of organization is best for your business depends on a number of factors,…
Q: This are 200 cases, 120 of which would be confirmed to be A. -After the testing, the data is…
A:
Q: You It's bad for your eyes. must shouldn't should Thank you very much for the information. You've…
A: lets understand the statements given: You --- sit so close to the TV! It's bad for your eyes. its…
Q: What resolution do you think a conventional display should have, and why?
A: A monitor is a computer's primary output unit. The resolution and refresh rate of the monitor's…
Q: In general, there are two types of files: Which of these two file types is preferable than the…
A: Introduction: A binary code is a two-symbol method representing text, computer processor…
Max Function
Statistical function is of many categories. One of them is a MAX function. The MAX function returns the largest value from the list of arguments passed to it. MAX function always ignores the empty cells when performing the calculation.
Power Function
A power function is a type of single-term function. Its definition states that it is a variable containing a base value raised to a constant value acting as an exponent. This variable may also have a coefficient. For instance, the area of a circle can be given as:
Step by step
Solved in 2 steps

- NumberFormat static method ---------- returns a ---------- NumberFormat that’s used to format a number as a percentage.C LANGUAGEA private railway company has just purchased a computer for its new automated reservationssystem. You have been asked to write a program to assign seats on each train of the railway havingonly (capacity: 100 seats). Your program should check whether it is a valid seat number or not.Also print its berth type i.e lower berth, middle berth, upper berth, side lower berth, side upperberth. Furthermore, then print a ticket indicating the person's seat number and whether it’s in the firstclass or economy section of the train. Use a single-subscripted array to represent the seating chartof the train. Initialize all the elements of the array to 0 to indicate that all seats are empty. As eachseat is assigned, set the corresponding element of the array to 1 to indicate that the seat is no longeravailable.pizza (python)Mario owns a pizzeria. Mario makes all of his pizzas from 10 different ingredients, using 3 ingredients on each pizza. Mario’s cousin Luigi owns a pizzeria as well. Luigi makes all his pizzas from 9 ingredients, using 4 ingredients on each pizza. Mario and Luigi have made a bet: Mario believes that customers can order a larger selection of pizzas in his pizzeria than they can order in Luigi’s pizzeria. Use functions for this assignment. Implement a factorial() function yourself (do not use the one from the math module) When choosing k items from n possible items, the number of possibilities can be obtained using the following formula: (??)=?!?!(?−?)!(nk)=n!k!(n−k)! Make a function called choose with two parameters n and k, that implements the above formula. Write a program that calculates the number of pizzas Mario and Luigi can make. The outcome should look like this: Mario can make 120 pizzas.Luigi can make 126 pizzas. Luigi has won the bet.
- True or FalseA value-returning method must contain a return statement.mport java.util.Scanner; public class ParkingCharges { // function to calculate the basic charge using the asked hours static double getBasicCharge(int hours) { if (hours >= 7 && hours <= 8) return 5.50; else if (hours >= 5 && hours <= 6) return 4.50; else if (hours >= 2 && hours <= 4) return 4.00; return 3.00; } // function to return the amount to subtract based on local living and OAP static double getDiscount(String isLocal, String isOAP) { if (isOAP.equals("Yes") && isLocal.equals("Yes")) return 2.0 + 1.0; else if (isOAP.equals("Yes")) return 2.0; else if (isLocal.equals("Yes")) return 1.0; return 0; } public static void main(String[] args) { // create a new Scanner object Scanner sc = new Scanner(System.in); // prompt the user to ask if they are disabled…(Financial application: payroll) Write a Java program that reads the following information and prints a payroll statement:
- True or False An error will occur if the compiler finds a statement that tries to change the value of a constant field.It is advised to include a description of the GetConsoleTitle function.assign(self, assignment:Assignment) -> AssignmentResult: """ This function is to simulate the process of the student receiving an assignment, then working on the assignment, then submitting the assignment and finally receiving grade for the assignment. This function will receive an assignment then a grade should be calculated using the following formula: grade = 1 - (Student's current energy X Assignment difficulty level). The min grade a student may receive is 0% (0) After the grade is calculated the student's energy should be decreased by percentage difficulty. Example if the student has 80% (.8) energy and the assignment is a difficultly level .2 there final energy should be 64% (.64) = .8 - (.8 * .2). The min energy a student may have is 0% (0) Finally the grade calculated should be stored internally with in this class so it can be retrieved later. Then an Assignment Result object should be created with the student's ID, the assignment…
- If the new operator cannot allocate the amount of memory requested, it throws_____________Java Questions - (Has 2 Parts). Based on each code, which answer out of the choices "A, B, C, D, E" is correct. Each question has one correct answer. Thank you. Part 1 - 9. In Java, composition is said to use __ relationship. A. is-aB. part-ofC. has-aD. both is-a and part-ofE. both has-a and part-of Part 2 - 10. Given the following code, which statement is true? class Water() { ... }class Juice() extends Water { ... }class Apple() { ... }class ApplePie() { Apple a1 = new Apple(); }class AppleJuice() { Apple a1 = new Apple(); Water w1 = newWater(); } A. Juice is a superclass and Water is a subclass.B. ApplePie is a superclass of Apple.C. ApplePie is a composite class that contains an instance of Apple class.D. AppleJuice is a superclass that contains an instance of Apple class and an instance of Water.E. Water is a composite class that contains an instance of Juice.Monty Hall Problem – Coding Lab In this lab, you will write a code that simulates the Monty Hall Game Show. Thegame host gives the participant the choice of selecting one of three doors. Twodoors has a goat behind them and one door has a prize. The set of choices arerandomized each round. The participant needs to select the door with the prizebehind it. When the participant selects a door, the game host reveals a door with agoat behind it. The game host opens a door (different from the one selected by theparticipant) that has a goat behind it. The participant is then given the option tochange their choice. When you run your code, the code would display a message prompting the user toinput their door choice, labelled as 1, 2, and 3. Then the code will display a doornumber (different from the one the user picked) with a goat behind it and ask theuser if they would like to change their choice. The code then displays a message onwhether the user guessed the correct door. The game then…

