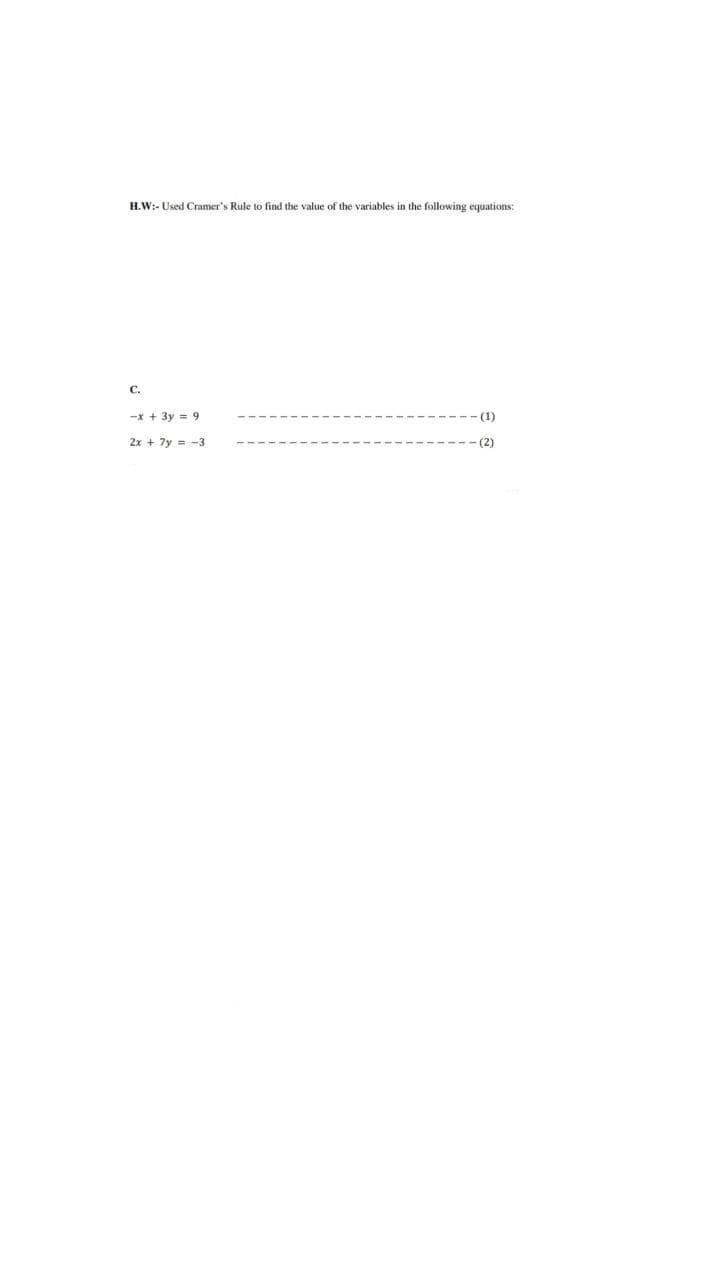
H.W:- Used Cramer's Rule to find the value of the variables in the following equations: C. -x + 3y = 9 --(1) 2x + 7y=-3 - (2)
Q: Propose suitable information security mechanisms or techniques or methods based on the concept of…
A: Networks like WiFi, LAN and WAN utilize the CIA protection which is capable for eliminating the…
Q: Prototyping and agile development methodologies may be used to database and application development.
A: Given: Agile development methodologies and methodsAgile development is defined as gathering…
Q: H.W:- Used Cramer's Rule to find the value of the variables in the following equations: A. 3x - 2y =…
A: Here in this question we have given two equation and we have asked to use cramers rule to solve…
Q: What are the benefits of using pure functions, and how do these functions really operate?
A: Introduction: The fact that pure works have no side effects is a significant advantage. You don't…
Q: Do several methods of authentication have any negative effects? What precisely does it do to assist…
A: Given: Next, we will walk you through an explanation of what multi-factor authentication is, as well…
Q: QUESTION You are hired by Rizalman Boutique management to develop a web-based application to assist…
A: as per the requirement designed HTML form and performed action. code is given below.
Q: What are your thoughts on the future of technology in transportation systems?
A: Future of Technology in Transportation Systems is very bright. Ibn older times, transport used to be…
Q: What are the responsibilities of an operating system when it comes to memory management?
A: Start: Memory management is a feature of operating systems that is responsible for managing the…
Q: Why is phyton so popular in cloud computing? Can you describe why it is favored over other…
A: let us see the answer:- Introduction:- Python is an excellent language for data science and…
Q: Which kinds of printers may be assigned an IP address?
A: Given: A network setup page, which provides the printer's IP address, is printed by almost all…
Q: Exactly what is meant by the term "memory void"? What causes it, and how does the operating system…
A: Introduction: Void of memory: One way to allocate contiguous memory is to partition all available…
Q: In a three-tier design, distinguish between the presentation layer, the database tier, and the…
A: A 3-tier application architecture is a client-server implementation that uses a presentation tier,…
Q: What are the benefits of adhering to a code of ethics in software engineering?
A: Please find the detailed explanation in the following steps.
Q: When it comes to the architecture of software systems, performance and security may seem to be…
A: Given: Supportability, usability, longevity, cost, scalability, reliability, concurrency,…
Q: Write a code to reverse string using reverse function in java
A: In this java based programming question, it is asking for code to reverse string using inbuilt…
Q: ou name any of omous cars?
A: Cruise, Tesla, Alphabet Inc's (GOOGL. O) Waymo and Aurora Innovation Inc (AUR. O) are the forms…
Q: It takes Google only one nanosecond to provide a response that includes millions of URLs that are…
A: Introduction: The pace of electron flow is clearly restricted by all modern PC gadget advancements.…
Q: Provide some instances of internalized services and discuss some important topics about externalized…
A: Internal services are those responsibilities a government provides to support its own internal…
Q: Instead of only two addresses, we have four in a WiFi frame (source and destination MAC). To…
A: ANSWER:-
Q: Think about the ways in which you can use Structured English to explain processes that aren't…
A: Institution: The process of studying a method or company to discover its goal and objectives and…
Q: A database management system evaluation and selection checklist should include five common criteria.
A: Database Management System: A database management system (or DBMS) is fundamentally a computerized…
Q: Please enumerate the qualities that distinguish well-designed service systems.
A: Service system: A setup of the organization's technology and its various networks constitutes a…
Q: Learn all there is to know about the various social media platforms. What precisely is meant by the…
A: Given: Despite the fact that young people all around the globe utilise social networking, not…
Q: Cybercrime might be enticing to certain people. It is not the case with other people.
A: Answer: What is cybercrime, exactly?Cybercrime is a new kind of crime in which criminals break…
Q: Think about the ways in which you can use Structured English to explain processes that aren't…
A: Start: "The process of studying a method or company to discover its objective and purposes and build…
Q: Prove that CFLs are closed under * (Kleene Star).
A:
Q: H.W:- Used Cramer's Rule to find the value of the variables in the following equations: B. 5x + 4y =…
A: Please go through the below image for the complete solution.
Q: Sketch the signal to carry through the medium if the sequence of bits to send using AMI line…
A: We need to sketch the signal to carry through the medium if the sequence of bits to send using AMI…
Q: Do all of an organization's needs can be met by cloud computing? issues with IT infrastructure at…
A: The solution to the given question is: Cloud Computing : Cloud computing is now taking over the IT…
Q: Will there no longer be a lottery? why, and why not? why not? Provide evidence from the reading to…
A: Answer: The lottery will, indeed, become extinct. People in the northern town have already said that…
Q: What cybercrime theories are there? Answer this question with specific examples from the literature.
A: We recently rejected the cybercrime theory to explain the decline in international crime (Farrell…
Q: List THREE (3) usages of the header() function in PHP?
A: In the given question header() function in PHP sends a raw HTTP header to a client or browser.…
Q: Parallel electrical conductors link the motherboard's various components to each other. It's up to…
A: Introduction: In this question, we are approached to compose the name of those lines that are equal…
Q: word. (a) What is the probability that T(w) = 10100011? (b) What is the probability that T(w) =…
A: The answer is
Q: Explain when it is cost-effective to use formal specifications and verification in the development…
A: Mathematical modeling is known as formal techniques in the definition, development, and verification…
Q: If you have the time, could you go into further detail on how metrics are used in the software…
A: A software metric is a quantitative or quantifiable measurement of the qualities of a program.…
Q: In a computer's random access memory (RAM), an operating system will always include the following…
A: This question requires us to list the operating system components that are always present in RAM.…
Q: How can the ARP protocol let a host A deliver a datagram to its destination B if A does not know B's…
A: ARP protocol: One of the most important TCP/IP protocol suites is the ARP. It's used to assign an…
Q: Which kinds of printers may be assigned an IP address?
A: Launch: A network setup page, which provides the printer's IP address, is printed by almost all…
Q: Write a C++ program to calculate the total salary of an employee using Class and Constructor. You…
A: Step-1: StartStep-2: Create a class Employee Step-2.1: Create public data members basic, hra,…
Q: Cloud computing, IoT, and wireless revolution.
A: Start: IoT cloud computing is used to store IoT data as part of a collaborative effort. A cloud is…
Q: Compare and contrast the benefits and drawbacks of using cloud computing and the many different ways…
A: Answer
Q: What is a digital scholarship?
A: Explain digital scholarship.
Q: Implement the numerical approximation of √√2 using for loop, (conforming to 12 dec places). 2 X₁ = 1…
A: Given:
Q: What kinds of cultural and global political factors, such privacy rights, are taken into account…
A: Development: Data is pricey and every business's fuel. Today, data is shared abroad and used to make…
Q: Assembly language instructions may be optimized by writing compilers and assemblers that rearrange
A: The answer is
Q: Why is the use of technology that improves education such a significant subject in this field?
A: INTRODUCTION: Here we need to tell how the use of technology improves education for a subject in…
Q: Question: Unit Converter Need HTML code a. cm to metre b. Metre to cm c. Metre to km d. Km to…
A: Find the required HTML code given as below and sample output :
Q: 53- write an instruction sequence that generate a byte-size integer in the memory location defined…
A: write an instruction sequence that generate a byte-size integer in the memory location defined as…
Q: List and discuss possibilities for utilizing the Internet for e-commerce, including judgments, the…
A: Given: The internet may serve several functions when it comes to the activities that are involved in…
Step by step
Solved in 2 steps with 2 images

- 6. B) Write equivalent expressions for each of the following by using De Morgan’s Law. !(a || b) !(y > 2 && !found )1) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’yz+x’yz’+xy’z’+xyz+xyz’ , can be written as: 2) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’y’z+x’yz+x’yz’+xy’z’+xyz’ , can be written as:Find a formula that generates the following sequence a1,a2,a3, …. a) 4, 6, 8, 10, 12, ... b) 0, 3, 8, 15, 24, ….
- (Practice) Determine the value of the following floating-point expressions: a.3.0+4.06.0b.3.04.0/6.0+6.0c.2.03.0/12.08.0/4.0 d.10.0( 1.0+7.03.0)e.20.02.0/6.0+3.0f.20.02.0/( 6.0+3.0)g.( 20.02.0)/6.0+3.0h.( 20.02.0)/( 6.0+3.0)(Mechanics) The deflection at any point along the centerline of a cantilevered beam, such as the one used for a balcony (see Figure 5.15), when a load is distributed evenly along the beam is given by this formula: d=wx224EI(x2+6l24lx) d is the deflection at location x (ft). xisthedistancefromthesecuredend( ft).wistheweightplacedattheendofthebeam( lbs/ft).listhebeamlength( ft). Eisthemodulesofelasticity( lbs/f t 2 ).Iisthesecondmomentofinertia( f t 4 ). For the beam shown in Figure 5.15, the second moment of inertia is determined as follows: l=bh312 b is the beam’s base. h is the beam’s height. Using these formulas, write, compile, and run a C++ program that determines and displays a table of the deflection for a cantilevered pine beam at half-foot increments along its length, using the following data: w=200lbs/ftl=3ftE=187.2106lb/ft2b=.2fth=.3ft(Automotive) a. An automobile engine’s performance can be determined by monitoring its rotations per minute (rpm). Determine the conversion factors that can be used to convert rpm to frequency in hertz (Hz), given that 1rotation=1cycle,1minute=60seconds,and1Hz=1cycle/sec. b. Using the conversion factors you determined in Exercise 7a, convert 2000 rpm into hertz.



