have to take n-10 an
Q: In javacode: Use ArrayList to create an array called myAL of type integer. --Fill the array with…
A: Java code: import java.util.ArrayList; public class Main { public static void main(String[] args)…
Q: Examine how wireless infrastructure affects developing countries. Since existing infrastructure such…
A: Introduction: Wi-Fi and cellular networks are hopeful technologies that may help bridge the digital…
Q: If facial recognition technology were employed in public places like shopping malls without the…
A: 1) Facial recognition technology is a type of biometric technology that uses algorithms to identify…
Q: To further illustrate a point, it is helpful to give examples. There are four distinct methods of…
A: The answer is given in the below step
Q: What lessons can we learn or insights can we get from this with regards to the crime of committing…
A: Internet: The Internet is a global network of interconnected computers, phones, and other devices…
Q: My Solutions > Formatted Strings (sprintf fixed point) Code has already been provided to generate a…
A: Here is a sample code in Java to accomplish the task: This code uses the DecimalFormat class to…
Q: Although encryption of a company's electronic documents is not required by law, it is strongly…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Q2 Combining languages Let L₁ = {ab, ba}, L2= {b, aa, abba}, L3= {x|x {a,b}* ^ |x| ≤ 3} = {A, a, b,…
A: We are given three languages and we are asked to evaluate (L1 *.L2) ∩ L3. First we will find out…
Q: Think about the many difficulties and setbacks you'll face as you build the structure, as well as…
A: Introduction: Cloud computing is a current technology with a reliable, user-friendly system that…
Q: Describe how the characteristics of the operating system aid middleware. Also, you should discuss…
A: Introduction: Network operating systems access distant resources because they have network…
Q: Instead than focusing on how fast something can be done, argue in favor of giving developers full…
A: Hello student Greetings Hope you are doing great. Thank you!!!
Q: Locate some reading material on the usage of hands-free devices while driving. In which…
A: Your answer is given below.
Q: Create a class Stack. This stack will be implemented using the LinkedList class that has been…
A: A Stack class that could hold values of any type was to be created in this question utilizing the…
Q: Explain why it's preferable to utilize user-defined functions rather than built-in ones.
A: The answer is given in the below step
Q: A compiler must take several things into consideration before it can generate stable and effective…
A: The programme written in a high-level language must first be compiled before it can be translated…
Q: Virtualization and its many manifestations are investigated in detail (Language, Operating System…
A: Virtualization isolates a computer's virtual instance from the hardware. Desktop users most often…
Q: Please complete questions (3), (4), and (5) in the screenshot provided into the code given in the…
A: The given code implements two algorithms for finding the shortest path in a weighted graph:…
Q: To what extent do certain ideas and patterns recur often in modern cybercrime? If you want a…
A: Introduction: Cybercrime is a growing concern in the modern era as technology continues to advance.…
Q: In terms of memory, how much space does a computer need?
A: The amount of memory (RAM) and storage space (hard drive or SSD) a computer needs depends on the…
Q: please add or fix any errors if needed for this assignement. I'm having troubles after running Gcc
A: After fixing the code, I have provided C CODE along with CODE SCREENSHOT and OUTPUT…
Q: In addition to the services that operating systems deliver, describe the three interfaces via which…
A: 1) An operating system (OS) is a software system that manages computer hardware and software…
Q: How did these current trends that are associated with cybercrime come to be? If you want me to give…
A: cybercrime, also known as PC misconduct, uses a computer to commit crimes like deception, dealing…
Q: Each proposed solution to the framework must include the difficulties that will arise during…
A: Answer is
Q: Provide a justification for deep access as opposed to shallow access from the viewpoint of a…
A: Introduction:- A Deep or Shallow binding variable access approach is typically used to implement…
Q: How do things like passwords and other forms of access control factor into rule enforcement?
A: Your unique key to a computer system is a password. Only authorized users can access computer…
Q: While it's not required by law, businesses should strongly consider encrypting all of their…
A: With increased data breaches, threats, and assaults, it's crucial to consider encryption's benefits.…
Q: ould you use arrays?
A: #include <stdio.h> int main() { float loanAmount, annualInterestRate, monthlypayment; int…
Q: Investigate whether or not your network is being subjected to penetration testing. Is data privacy a…
A: Introduction: In today's digital age, data privacy and cybersecurity have become major concerns for…
Q: Java Programming: Make AST Nodes: IfNode, WhileNode, RepeatNode. All will have BooleanCompare for…
A: Java is a programming language that is widely used for developing desktop, web, and mobile…
Q: For a variable to be correctly described, it is also necessary to describe its other…
A: Introduction: C programmes seldom specify storage classes because they contain default values. The…
Q: Using asymmetric encryption methods, like those used in public-key cryptography, is a good idea.…
A: What is an Encryption: Encryption is the process of converting plain text into a cipher text…
Q: How can information technology aid transportation planning, implementation, and research?
A: It could be argued that transportation networks are an integral component of SCM, impacting every…
Q: Explain in depth what each virtualization type entails (Language, Operating System and Hardware).
A: What is virtualization: Virtualization is the creation of a virtual version of an operating system,…
Q: How interconnected are science and technology, and how does this affect our daily lives? In the face…
A: Your answer is given below.
Q: please use c# below are requirements and i will post question after requirement PROCESSING LOGIC…
A: Design and implement a C# application that allows users to input strings into a textbox, and adds…
Q: How Linux may be utilized in space exploration.
A: The answer is given in the below step
Q: What exactly is meant by the term "metadata"? Which component of a database management system is…
A: Table summaries and field specifications are examples of the kinds of metadata that can be found in…
Q: Include a discussion of open innovation as a real-world use of cloud computing throughout your talk.
A: To properly explain Cloud Computing, I use open innovation: Cloud computing lets big companies and…
Q: Please mention two instances of the issue between readers and authors. I would appreciate if you…
A: Describe the issue facing viewers and authors using two real-world instances. I need a response to…
Q: please code in python, I really need to know this works.. kindly help me out... please use can use…
A: Below is the complete solution with explanation in detail for the given question about the…
Q: Q1 Strings from RES There are eight strings of length 4 which cannot be produced by the following…
A: The regular expression given is: (a+ba)*(ab+ba)(b+ab)* Breaking it down: (a+ba)* means zero or more…
Q: Describe the hurdles and restrictions that will need to be overcome throughout the framework's…
A: Introduction: Bottlenecks are setbacks or obstacles that cause a process to slow down or stop.…
Q: I want to find out more about multi-factor authentication just out of plain old curiosity. When…
A: Answer is
Q: Build a process flow diagram of the use case order placement layer by layer. View layer, data layer,…
A: The Answer is in given below steps
Q: A two dimensional array of red and green entries represents a maze. Green entries are passable and…
A: (1) Abstracting the problem as a graph: We can represent the maze as a graph where each passable…
Q: please code in python, I really need to know this works.. kindly help me out... please use can use…
A: import timeimport numpy as npimport pandas as pdfrom sklearn.neural_network import MLPClassifierfrom…
Q: Think about the challenges you'll face as you build the framework, and then examine the problems and…
A: Introduction: Building a framework for a new project can be challenging, as there are many factors…
Q: Complete the statement using the following code: words = ['Young', 'boy, 'GIRL","old"] words.sort()…
A: Answer: ['GIRL', 'Young', 'boy', 'old']
Q: Problem 1. Suppose you are given an array A[1 n] of integers that can be positive or negative. A…
A: The problem involves finding the smallest number of positive contiguous subarrays of an array of…
Q: When asked to complete a set of tasks, what does an automated decision-making tool (ADT) do, and how…
A: Here is your solution -
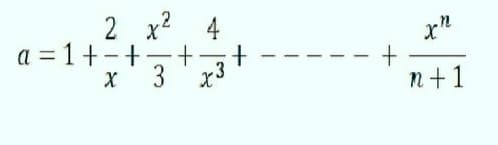
You have to take n-10 and X=100.. Matlab code.
Step by step
Solved in 2 steps with 2 images

- 2. Convert the following hexadecimal numbers into binary numbers:(a) 4E16(b) 3D716 (c) 3D7016Work out the following without using a calculator 111010102 + 21228 + ABC16 - 1238, Give your answer in decimal Given a binary number 11100101, find its equivalent in Decimal using Horner’s Rule Multiply the following binary numbers: 11011.101 by 101.111 Convert A74816 to octal equivalents Using Subtraction by 2’s Complement: 10100.01 – 11011.10Explain how to transform (integer) binary number to decimal number and to hexadecimal (for example 101111010001. (will leave a like)
- Obtain the 1’s and 2’s complements of the following binary numbers: (a) 00010000 (d) 10101010 (b) 00000000 (e) 10000101 (c) 11011010 (f) 11111111 Represent the unsigned decimal numbers 791 and 658 in BCD, and then show the steps necessary to form their sum. Express the following numbers in decimal: (a) (10110.0101) 2 (b) (16.5) 16 (c) (26.24) 8 (d) (DADA.B) 16 (e) (1010.1101) 2 Add and multiply the following numbers without converting them to decimal. (a)Binary numbers 1011 and 101. (b)Hexadecimal numbers 2E and 34.Show how the following floating-point additions are performed (where significands are truncated to 4 decimal digits). Show the results in normalized form. Know the solution but can explain more details about this question in words? a) 5.566 x 10² + 7.777 ×10² b) 3.344 x 10' + 8.877 x 10-2Show how the following floating-point additions are performed (where significands are truncated to 4 decimal digits). Show the results in normalized form. a) 5.566 x 10² + 7.777 ×10² b) 3.344 x 10' + 8.877 x 10-2 Can I know how to explain this type of question?
- Implement code convertor Y=(X+4) mod 8 using decoder and encoder. Y and X are 3-bit numbers.Answer the following 4 questions with step by step explanations :1. Convert 870678(9) = x(27)2. Convert ABF(16) =x(64)3. Subtract APG(32) - 7RK(32) =4. Multiply BF(16)* AA(16) =192.67.200.1 in Hexadecimal is: FF:23:C7:01 CA:D3:C8:01 C0:43:C8:01 C0:67:C8:01 C0:43:C8:10
- Convert the decimal number 431 to binary in two ways:(a) Convert directly to binary. (b) First convert it into hexadecimal and then from hexadecimal to binary. Which is faster in youropinion?The generating function for the sequence 1,0,1,0,1,0,1 is____ a)1 + x + x2 + x3+ x4+ x5 + x6+…. b)1 +x2 + x4+ x6+……. c)1 + x+ x2 + x3+ x4+ x5 + x6 d)1 + x2 + x4+ x6Suppose .3A42 base 16 is converted to base 10. What is contributed by the hex digit 3 if the value in decimal of .3A2 base 16 is computed? a. 0.1875 b. 0.0390625 c. 0.00048828125 d. 0.22705078125

