he scree
Q: what are some of the best practices used to optimize networks, and what might be some of the securit...
A: TCP Window Measurement The purpose of TCP Window Scaling is to increase the size of the windows TCP ...
Q: How many layers are there in the OSI reference model? A. 5 B. 6 C. 7 D. 8
A: The OSI Model (Open Systems Interconnection Model) is a reasonable structure used to portray the ele...
Q: Create a python program called code.py. Write a function named pi_multiples() that takes an integer...
A: According to the provided information: We need to create a python function named pi_multiples() that...
Q: The computer and IT environment differs from a more conventional non-computer medium in what it allo...
A: The Answer:
Q: You are required to create the following tables in a database named SICKLEAVE: EMPLOYEES EMPLOYEE_ID...
A: Kindly Note: As per our company guidelines we are supposed to answer only first 3 sub-parts. Kindly ...
Q: Q.2.2 Write a query to generate a report indicating the total number of sick leave days for each emp...
A: Query to generate a report indicating the total number of sick leave days for each employee. Given: ...
Q: Which layer of the ISO/OSI Reference Model performs encryption or compression for a communications s...
A: The answer:
Q: umber by us
A: Step 1: To calculate the factorial of a given number, we usually multiply the numbers from 1 to that...
Q: Did you collaborate with customers to develop early use-cases for the unified process model? Describ...
A: Given: Did you collaborate with customers to develop early use-cases for the unified process model? ...
Q: Embedding binary tree on 2d-mesh: Prove that a binary tree of depth k > 4 does not have a load-1, di...
A: Answer: This question based on binary and their height. so we have discuss in next page.
Q: Could you enumerate a couple of the characteristics of a test case?
A: We are asked the characteristics of a test case. Test suite contain all possible test cases.
Q: (a) How to work with Structure in C? Show an example
A: This question comes from Programming Language in C which is a paper of Computer Science. Let's discu...
Q: Why is NonActionAttribute so important?
A: NonAction Attribute:- The NonAction Attribute is intended to make sure that a method isn't utilised ...
Q: In an MVC application, what does Model-View-Controller stand for?
A: The Answer is in given below steps
Q: Suppose we have the following student table in database. You have to write: Form load event to show ...
A: Answer :-
Q: You are given a line of n lowercase Latin letters, the word that Fischl recently expressed. You beli...
A: here have to determine about lowercase Latin letters problem statement.
Q: What do you mean by prims algorithm
A: The Answer is in Below Steps
Q: What are the difficulties associated with analyzing a system? What are some of the components that ...
A: What are some of the difficulties in evaluating a system? challenges: It is critical to work without...
Q: ) Convert the decimal numbers 73, 1906, -95, and -1630 into signed 12-bit n ne following representat...
A: Q.
Q: In your opinion, how important is it to include computer technology into your daily routine?
A: The answer :
Q: Write a program that calculates and prints the bill for a cellular telephone company. The company of...
A: code snippet:
Q: When comparing operating systems on a mainframe with a laptop, what is the primary distinction to be...
A: Here are the primary distinction on a mainframe with a laptop- The mainframe uses multiuser systems...
Q: This is the most effective file organization method in which one must handle all data records in a f...
A: The answer:
Q: Write a c# program to find current moment after 90 da
A: Code: using System;public class Example10{ public static void Main() { DateTime today ...
Q: Write a c# program to find the weekday from the current moment after 90 days
A: Here have to determine about weekdays from now to 90 days.
Q: 7. Write a program in C# Sharp to search the position of a substring within a string.
A: code : - // C# program to illustrate the// String.IndexOf(char x) methodusing System;namespace Cons...
Q: the advantages and disadvantages of client-side scripting languages?
A: The advantages and disadvantages of client-side scripting languages
Q: What are the stages involved in completing an MVC project?
A: MVC is an acronym for Model View Controller. The MVC pattern implements the Model, View, Controller ...
Q: Generate an (n x m) multiplication table. use a nested-loop. sample output if applicable typical out...
A: As no programming language is mentioned, it is solved using basic C++
Q: n c++ , write a program that gives the following output as mentioned in image . ( Give answer quickl...
A: Declare count=1,sp=1; for(int i=1;i<=4;i++) { for(int j=4;j>=i;j--) { Display ...
Q: to defin
A: Critical Bugs Critical bugs are ones that make a website unusable and for which there is no remedy...
Q: A 82-W incandescent lamp is connected to a 178-V source and is left burning continously in an otherw...
A: Formulas Used: Current, I = PowerVoltage Total Cost = Power * (total hours the bulb is used) * cost ...
Q: Which of the following statements is correct? Subscript notation in C# makes it possible to get at ...
A: Subscript notation in C# makes it possible to get at the individual characters in a string. (Corre...
Q: This course is crucial for understanding the history of computers, computer systems, viruses, and in...
A: WILL BE EXPLAINED:
Q: COMPUTERSCIENCE&IT Q52. Implement the following functions using a decoder. f,(x, y, z) = Em (0,1,3,7...
A: The Answer is in step2
Q: This is due to the fact that computers are very powerful nowadays. What factors have contributed to ...
A: Computers have been powerful since they were introduces but now they are everywhere, we can find com...
Q: Order of events in a text-based system such as a command line interface is determined by what?
A: The answer:
Q: [0] [1] [2] [3] myList "Bashful" "Awful" Jumpy" "Happy" The above "myList" is an ArrayList in Java p...
A: Use ArrayList.add(int index, E element) method to add element to specific index of ArrayList. To rep...
Q: 3. What is the advantage of using ArrayList over LinkedList? 4 How much time do you need to add an e...
A: 3- Advantage of using ArrayList- ArrayList is quick to select a particular element, although it is ...
Q: Identify three protocols that are weak or vulnerable to attack, presuming the organization's users h...
A: THE ANSWER:
Q: generate_number(pct_per_digit): Takes one float as input. Returns a random number that is constructe...
A: Python code : import random def generate_num_digits(pct_per_digit): x = 1 pct = 0 while...
Q: n Cache and Hash
A: Q. Difference between Cache and HashMap.
Q: Write a program for solving the system Ax = b by cholesky’s decomposition
A: The Cholesky decomposition or Cholesky factorization is a decomposition of a hermitian, positive de...
Q: Explain the purpose of “this” keyword. Give an example. d) What is composition and what is the purpo...
A: this keyword:- Within an instance method or a constructor, "this" is a reference to the current o...
Q: The OSI session layer controls and synchronizes dialog. Identify the Internet model layer in charge ...
A: Answer: The OSI session layer controls and the synchronized dialog are the two tasks of the session ...
Q: Which of the following statements is correct? Utilities include things like word processors, spreads...
A: The Answer:
Q: QUESTION 8 Mnemonic Code is used in O a. Machine Language Ob Assembly Language OC High Level Languag...
A: Given: We have to choose the language in which Mnemonic code is used. Options are: a. Machine Langua...
Q: Provide an example of how an engineer in charge of creating a system requirements specification coul...
A: Given: Provide an example of how an engineer in charge of creating a system requirements specifica...
Q: Which one is better, the standard binary tree or the advanced binary search tree?
A: Standard binary tree refers to binary tree. Because the BINARY TREE is unsorted, the insertion, dele...
Q: Is there a term for a software that is designed to do a certain job, such as a virus scanner or a fi...
A: Utility software is a type of system software that helps in the proper and efficient operation of a ...
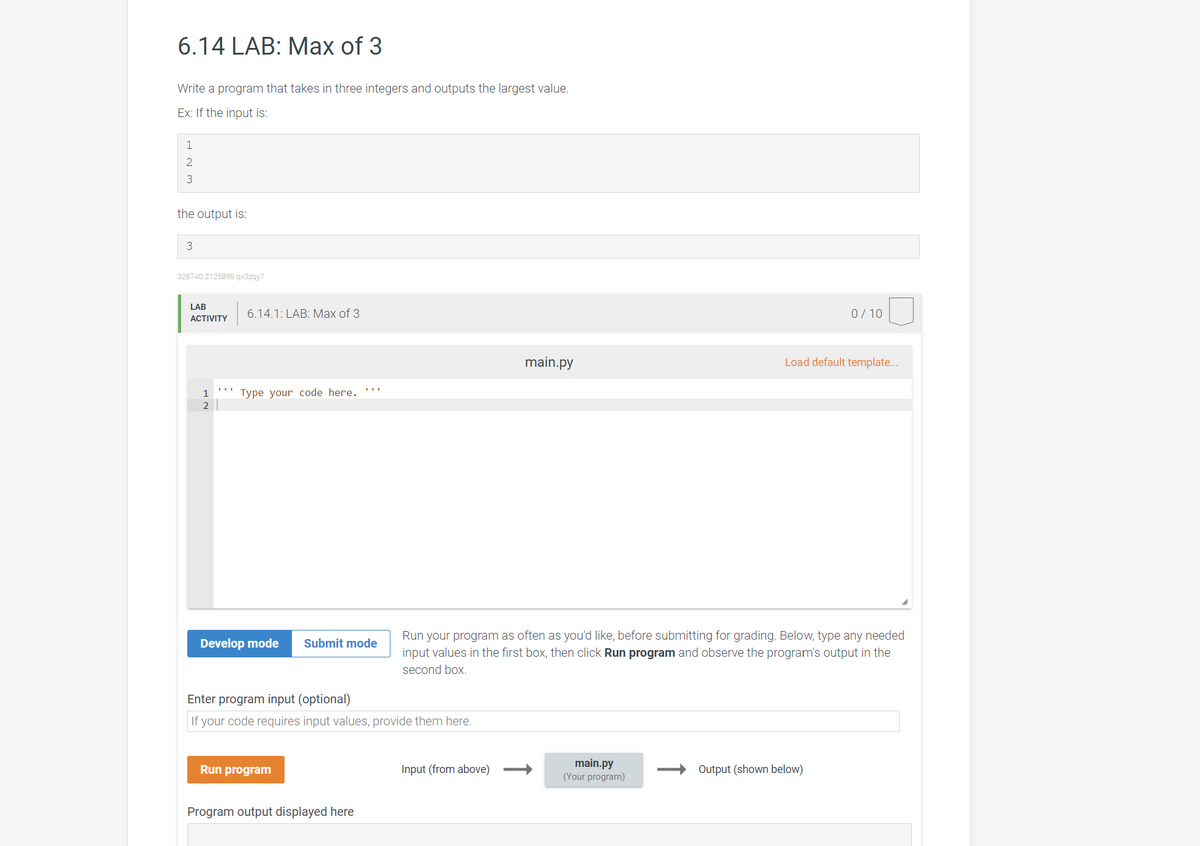
This is a python max of 3 exercises, the screenshot can explain more, please.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- 5.12.2: Switch statement to convert letters to Greek letters. Write a switch statement that checks origLetter. If 'a' or 'A', print "Alpha". If 'b' or 'B', print "Beta". For any other character, print "Unknown". Use fall-through as appropriate. End with newline. import java.util.Scanner; public class ConvertToGreek {public static void main (String [] args) {Scanner scnr = new Scanner(System.in);char origLetter; origLetter = scnr.next().charAt(0); /* Your solution goes here */ }}Computer Science Use only NumPy to create the Normalize Class: Image Normalization is a technique used to touch up images that are too dark or too light for the human viewing experience. Implement a version that outputs images with full dynamic range (0–255 pixel intensity). In other words, for each color channel (r, g, b), rescale the range of pixel values for that channel to include both 0 and 255. After normalizing, there should be at least one pixel with a red value of 0, at least one pixel with a red value of 255, at least one pixel with a green value of 0, etc. To normalize a list of numbers nums to the range 0–n, set nums[i] = (nums[i]−min(nums))/(max(nums)−min(nums))∗n for all i. Be careful! When max(nums) == min(nums), you should not touch that list (why?).● Create a Python file called amazon.py in this folder.● Write code to read the content of the text file input.txt.● For each line in input.txt, write a new line in the new text file output.txtthat computes the answer to some operation on a list of numbers.● If the input.txt has the following:o Min: 1,2,3,5,6o Max: 1,2,3,5,6o Avg: 1,2,3,5,6● Your program should generate output.txt as follows:o The min of [1, 2, 3, 5, 6] is 1.o The max of [1, 2, 3, 5, 6] is 6.o The avg of [1, 2, 3, 5, 6] is 3.4.● Assume that the only operations given in the input file are min, max andavg, and that the operation is always followed by a list ofcomma-separated integers.● You should define the functions min, max and avg that take in a list ofintegers and return the min, max or avg of the list.● Your program should handle any combination of operations and anylength of input numbers.● You can assume that the list of input numbers are always valid integersand that the list is never empty.● Hint: there is…
- 12. What is the output of the following program? (2, 3, 6, 8) #include #include #include #include using namespace std; int main() { double x, y; string str; x = 9.0; y = 3.2; cout (sqrt(pow (y, 4))) = " (sqrt(pow (y, 4))) << endl; str = "Predefined functions simplify programming code!"; cout << "Length of str = " << str.length() << endl; return 0; }6.28 In Python, Write a program that replaces words in a sentence. The input begins with word replacement pairs (original and replacement). The next line of input is the sentence where any word on the original list is replaced. Ex: If the input is: automobile car manufacturer maker children kids The automobile manufacturer recommends car seats for children if the automobile doesn't already have one. the output is: The car maker recommends car seats for kids if the car doesn't already have one. You can assume the original words are unique. END WITH A NEW LINE6.28 In Python, Write a program that replaces words in a sentence. The input begins with word replacement pairs (original and replacement). The next line of input is the sentence where any word on the original list is replaced. Ex: If the input is: automobile car manufacturer maker children kids The automobile manufacturer recommends car seats for children if the automobile doesn't already have one. the output is: The car maker recommends car seats for kids if the car doesn't already have one. You can assume the original words are unique.
- TODO 1 Obtain all the indexes with labels equal 2 with np.where and the label array y. Keep the results in two_class_idx also index np.where() at 0 # TODO 1.1 two_class_idx = print(f"two_class_idx output: \n {two_class_idx}") try: print(f"two_class_idx shape: {two_class_idx.shape}") except Exception: pass todo_check([ (isinstance(two_class_idx, np.ndarray),f'two_class_idx is not an NumPy array! two_class_idx is currently a {type(two_class_idx)}'), (np.all(two_class_idx == np.array([3,9,11,12,16])),'two_class_idx does not contain the correct location values') ])4.10.1: LAB: Exception handling to detect input string vs. integer The given program reads a list of single-word first names and ages (ending with -1), and outputs that list with the age incremented. The program fails and throws an exception if the second input on a line is a string rather than an integer. At FIXME in the code, add try and except blocks to catch the ValueError exception and output 0 for the age. Ex: If the input is: Lee 18 Lua 21 Mary Beth 19 Stu 33 -1 then the output is: Lee 19 Lua 22 Mary 0 Stu 34 # Split input into 2 parts: name and ageparts = input().split()name = parts[0]while name != '-1': # FIXME: The following line will throw ValueError exception. # Insert try/except blocks to catch the exception. age = int(parts[1]) + 1 print('{} {}'.format(name, age)) # Get next line parts = input().split() name = parts[0]5.18 C++ Write a program that reads a list of integers, and outputs those integers in reverse. The input begins with an integer indicating the number of integers that follow. For coding simplicity, follow each output integer by a comma, including the last one. Ex: If the input is: 5 2 4 6 8 10 the output is: 10,8,6,4,2,
- 4) Which of the following is/are valid ways to allocate memory for an integer by dynamic memory allocation in CPP? a. int *p = new int(100);b. int *p; p = new int; *p = 100;c. int *p = NULL; p = new int; *p=100;d. Only 1,2e. All of these 5) Choose the correct option?#include<iostream>using namespace std; class Base {}; class Derived: public Base {}; int main(){Base *bp = new Derived;Derived *dp = new Base;} a. No Compiler Errorb.Compiler Error in line “Base *bp = new Derived;”c. Compiler Error in line ” Derived *dp = new Base;”d. Runtime ErrorThis question concerns the use of a book cypher to encode a message.Write a program called ‘bookcypher.py’ that accepts:1. The file name for a Project Gutenberg book text.2. A message that is to be encoded.3. A file name for output of the encoded version of the message.The program will create an encoded version of the message by replacing its words with the locationsof words in the book.Say, for example, the message is ‘meet me at the usual time and place’, and the Gutenberg text is‘The Importance of Being Earnest’ by Oscar Wilde.• There is an occurrence of ‘meet’ as the 5th word on the 493rd line of the book text.• There is an occurrence of ‘me’ as the 9th word on the 190th line of the text.• There is an occurrence of ‘at’ as the 6th word on the 8th line of the text.• And so on.Representing a word position as a conjunction of the line number and the index of the word withinthe line, we can encode the message as 493-5, 190-9, 8-6, etc.Sample I/O (user input in bold):Enter the book…can you make it so it reads from the kongcrew.txt file instead of typing out the info? can you also make it where it lists all of the specifications with the information below like the bolded texted in the picture? example below Name Sit Walk Swing ....... and so on with the info below (make one print out before adding the second ss and after so it shows the updated info of how many bananas the monkeys have before and after) the txt file information is below. Donkey Kong Y Y Y N 3 3 1981 Donkey Cranky Kong Y Y N Y 1 0 1985 Donkey Dixie Kong Y Y N Y 2 2 2001 Dixie Kiddy Kong Y N Y N 1 1 2003 Dixie Wrinkly Kong N N Y Y 1 2 1985 Donkey Tiny Kong N N Y Y 2 1 2001 Dixie Diddy Kong Y Y Y N 3 2 1985 Donkey Uncle Kong Y N Y N 1 2 1990 Donkey Chunky Kong N Y Y Y 2 5 2007 Dixie

