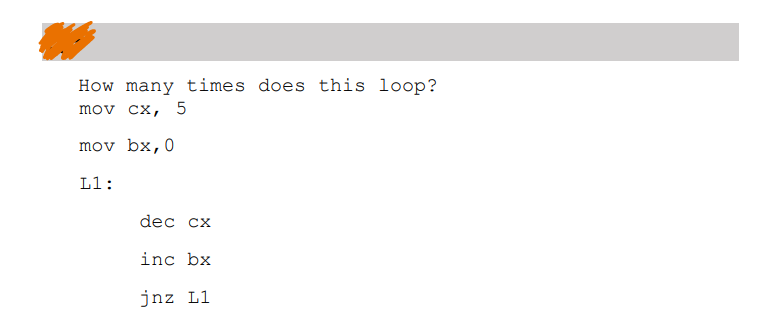
How many times does this loop? mov cx, 5 mov bx, 0 L1: dec cx inc bx jnz L1
Q: Subject: Industrial project Q): How results & finding analyze on software NVIVO after interview?
A: What is NVivo software: NVivo is a qualitative data analysis software developed by QSR…
Q: If you could customise a dashboard for your organisation, what data would you include?
A: When customizing a dashboard for an organization, the choice of data to include would depend on the…
Q: What methods are used now after decades of technical advancements?
A: The saying "appliance education" (ML) and "fake aptitude" (AI) are both contraction designed for the…
Q: The blue part of this diagram is filled with code, and the right side is the result of the run.just…
A: I have provided COMPLETE HTML CODE along with OUTPUT SCREENSHOT----------Note: I have explaine…
Q: Why does wifi age faster than cable?
A: Wireless relatives such as Wi-Fi operate via radio impression, which are innately at risk to…
Q: Consider the following class definitions: public class Thing { public void string_method(String…
A: Here is your solution -
Q: As an IT worker, is it possible to act legally without acting ethically?
A: What is IT worker: An IT worker refers to an individual who is employed in the field of Information…
Q: Why architecture matters? Try charting a project sans architecture. effect on product.
A: Architecture plays a crucial role in software development projects, and designing a project without…
Q: Please list the DBA's technical function's design and implementation duties.
A: As a Database Administrator (DBA), some of the technical function's design and implementation duties…
Q: Why does staggered use the idea of a disc to cut down on rotating delay?
A: In the realm of disc storage, staggered addressing emerges as a technique aimed at mitigating time…
Q: Why are people of all ages and from all walks of life so interested in computer science?
A: Among the rapid pace of technical progression, computer science comprise turn into more and more…
Q: programming is a term used for organizing programs by dividing them into smaller modules that…
A: The Boolean operator "&&" represents the logical AND operation. It returns true only if both…
Q: Write functional and non-functional requirements for any online shopping site you want
A: We need to write the both functional and non-functional, for any online store. so we will see in the…
Q: Define bounded summation and explain its significance in algorithm analysis.
A: Bounded summation is a concept used in algorithm analysis to describe the behavior and complexity of…
Q: Why would you upgrade a technological item?
A: There are several reasons why you might consider upgrading a technological item: 1. Improved…
Q: Make a multilayer sequence diagram for the use case put order object, including the view, data, alt,…
A: Sequence diagrams are the part of Merged Modeling Dialect (UML), broadly used in thing-oriented…
Q: What does the database management system driver actually do?
A: A database management system (DBMS) driver, also known as a database driver or database connector,…
Q: Conditions: 1. Water must be replaced when -Water level (T) 9) 2. Fish food (pellets): 1 x 4.5…
A: To create a proven simulation of an automatic aquarium care system using Arduino in Tinkercad,we can…
Q: VLANs may improve a company's compliance, scalability, pricing, and more.
A: Virtual Local Area Networks (VLANs) are vital in enforce fulfillment within an Organization network.…
Q: Talk about credit card protection and how to stay safe.
A: What is credit card: A credit card is a payment card issued by a financial institution that allows…
Q: Please specify weak entity type. Its secret? An example What is attribute specialisation?ER…
A: In the context of Entity-Relationship (ER) modeling, used to design and represent databases, there…
Q: What are some of the most important parts of an Android app?
A: Android apps have become an essential part of our daily lives, and they are used for a wide variety…
Q: Find a business chance in the current situation in Malaysia?
A: Potential business opportunities in the current situation in Malaysia. will identify areas where…
Q: Ethics advise on what is ethically good to retain, whereas laws impose security requirements.…
A: The balance between ethics and laws often raises questions about what is considered ethically good…
Q: What are the problems with putting internet trade into place?
A: Implementing Internet trade also known as e-commerce can present several challenges. Some of the…
Q: How exactly does a database management system get normalised?
A: Database normalization is a fundamental aspect of database design that aims to minimize data…
Q: e might look like and provide a SQL query to return a list of the honor roll students (top 10%),…
A: Designing a database for storing students' grades necessitates understanding fundamental concepts of…
Q: Create a Client class that interacts with an SQLDatabase Server (provided below). The Client sends a…
A: The Client class is initialized with a server parameter, which represents an instance of the…
Q: Explain why software developers prefer deep access over shallow access, not merely performance
A: Deep access refers to a high level of control and visibility into the underlying system components…
Q: Why would your company pick high-availability DHCP? What's best? Any drawbacks? What makes it…
A: The setup of several DHCP servers to continually offer network configuration and IP address…
Q: Consider this data sequence: "3 11555246673-8". Any value that is the same as the immediately…
A: 1. Import the java.util.Scanner class.2. Create a public class named ConsecutiveDuplicates.3. Define…
Q: Give an outline of the most important parts of electronic payment methods that make online and…
A: Electronic payment methods have revolutionized the way we conduct transactions, making online and…
Q: Please do not give solution in image format thanku Software Engineering: Project Description:…
A: A) Context Models:The Sentiment Analysis system for images consists of multiple components that work…
Q: Explain the DBA's technical duties, including service design and implementation.
A: What is DBA: DBA stands for Database Administrator. They are responsible for managing and…
Q: Why didn't Target hire a CISO before the breach?
A: In the aftermath of the notorious data breach that shook Target in the past, questions have been…
Q: Discuss business intelligence implementation challenges?
A: challenges associated with implementing business intelligence (BI) systems. BI implementation…
Q: Your network administrator must create a new file and print server for Windows, Linux, and Mac…
A: What is Server Services and Security Document: Server Services and Security Document is a concise…
Q: Improve Luby’s MIS algorithm coded in Python by selecting a vertex at random, finding its neighbors…
A: 1. Define the function luby_mis(graph) that takes a graph as input.2. Initialize an empty set mis to…
Q: Please do not give solution in image format thanku Giveexplanation short point to point and short…
A: Laravel is a popular and user-friendly framework for building web applications using PHP. It…
Q: Explain three technological controls that can be used to make the transport layer more safe.
A: To make the transport layer more secure, there are several technological controls that can be…
Q: I have a code (class Server). I need help to fix error in another class. These are 2 seperated…
A: The error you're encountering is occurring because the pickle.loads() function is expecting a…
Q: Write a JavaScript code with the following three different conditions: • Create the HTML document…
A: <!DOCTYPE html><html><head><title>Change Image…
Q: Operating System: Please In your own words, and clearly. A) How would you explain the concept of…
A: The critical section problem is a problem in computer science that arises when multiple processes…
Q: Defense in Depth is a security principle organizations use to preserve the CIA triad of their…
A: Security refers to the measures and practices put in place to protect assets, systems, and…
Q: Mobile app development: what should be considered?
A: Choosing the accurate platform for your app is crucial and often depends on your goal audience's…
Q: Taking into account the distribution method and the Model-View-Controller design, can the interface…
A: Yes,in the Model-View-Controller (MVC) design pattern,it is possible to change the interface of one…
Q: Two-factor verification would be using two passwords to get into a system, right? Why?
A: Two-factor verification does not involve using two passwords to access a system.It typically…
Q: What is the key sign on the computer for the Left Menus key?
A: In computer science, the left menus key, also known as the "Windows key" or "Start key," is a key…
Q: How can you figure out how well an ArrayList works?
A: What is ArrayList: ArrayList is a dynamic array-based data structure that provides resizable arrays,…
Q: How would you connect local area network endpoint and infrastructure devices? How would you…
A: Local Area Networks, frequently known as LANs, are comprise of a selection of endpoint approach…
Step by step
Solved in 3 steps

- Instructions: Use online editor for doing shell script Use JSLinux online tool to do practicals (Website address : https://bellard.org/jslinux) ===========================================================Write a shell script that reads the price for 6 mobile phones and counts the price of mobile phones whose price is more than 300 OMR. Note : · Use loop and conditional statements. · Display the appropriate output.How many times the loop will be repeated? LDI R20, 20 now: LDI R21, 10 DEC R21 DEC R20 BRNE now JMP now Select one: a. infinite number of times b. 20 c. 10 d. 200COUNT EQU 0x37 MOVLW d'30' MOVWF COUNT MOVLW 0AGAIN ADDLW 4 DECFSZ COUNT, F GOTO AGAIN MOVWF PORTB Questions: Find the value at PORTB. Find how many loops there are in total.
- What is the value saved after executing the following code? .data var1 WORD 1000h var2 WORD 2000h val byte 5 .code movzx ax, val ; ax= xchg ax,bx ; bx= xchg var1,bx ; bx= xchg eax,ebx ; eax=IMP PLEASE HELP, i will give like to all your Q, PLS ASAP , pls send a screen shot of your code Create a function that manipulates a string. Also can you write a code for mainfunction for both of them please allClear Clear string (makes it an empty string) eraseString Erase characters at specified position from string(python) Which command is used to exit out of a loop at any point? a. continue b. break c. exit d. end
- Sockets cannot send the bits. Question 10 options: True FalseWhat is the output of the given code below Dim num As Integernum = 11Do while num >= 5 num = num -2 ListBox1.Items.Add (num)Loop Select one: a. 975 b. 11975 c. 9753 d. none of the choices What is the standard prefix used for check box control? Select one: a. none of the choices b. chb c. chk d. ckbcan you please do it on dev c++ , it's C programming
- NUMBER 8 Code the following in DEV C++ Rules: 1. Kindly code it in a proper way 2. The symbols and values are posted here: r1 = outer radiusr2 = inner radiusC1 = outer circumferenceC2 = inner circumferenceA1 = area of circle of r1, area within outer circleA2 = area of circle of r2, area within inner circleA0 = shaded area, outer area minus inner areaA0 = A1 - A2π = pi = 3.1415926535898√ = square root 3. Example of the code is this Annalus Calculator https://www.calculatorsoup.com/calculators/geometry-plane/annulus.php 4.. Please don't reject CODE THE FOLLOWING (SEE ATTACHED PHOTO):New Jave code must be entered inbetween grey blocks of code as seen in photoThe code needs to be updated to have the streaming service be "Netflick" for Where to watch movie one...currently all Where to watch...results in none...how do I fix the error below, thanks for your help in advance! Test Failed: None != ['The Seventh Seal (1957)', 'Netflick'] : Expected value: ['The Seventh Seal (1957)', 'Netflick'] Value from your code: None





