i) Detect the deadlock using wait for graph ii) Find out the solution to recover from this deadlock
Q: Explain If-Then Constraints.
A: A single simple trick (with suitable adjustments) can help usmodel a great variety of if-then…
Q: 1- Compare the required space for graph representation in terms of edges and vertices using a)…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: 7. Consider the following graph: B A •C D (a) Write the degree of each vertex (write it next to the…
A: 7 a) Degree of vertex: Degree of a vertex is denoted by the number of the edges that are connecting…
Q: 2. a) In the following graph, apply Depth First Search algorithm to find the Strongly Connected…
A: Answer as given below:
Q: 3. Apply Bellman-Ford algorithm on the following graph. Show all the steps. 2 3 -3 2.
A: Solution
Q: Problem: A Hamiltonian cycle, also called a Hamiltonian circuit, Hamilton cycle, or Hamilton…
A: Solution:: Lets see the above question from start to end and also by constructing space state tree.…
Q: 9. The relation with the directed graph shown below is an equivalence relation.
A:
Q: A graph without multiple edges and loops is called a ______ graph. (simple graph, mixed
A: the answer is an simple graph
Q: 3. Apply Bellman-Ford algorithm on the following graph. Show all the steps. -3 2. %24
A: Given graph contains 5 vertices that are s, r, x, y and z. Bellman ford algorithm is used to find…
Q: 19. Use the graph K; to answer the following questions. 6/6 9/11 3/4 6/6 3/3 3/3 2/2 8/8 1/1 b K2 a.…
A: According to the information given:- We have to identify a cycle in the graph and reduce flow in the…
Q: 1.1 Define a growth factor for the above difference equation (in the picture), also verify that your…
A: 1) A finite-difference economic model: A set of equations is used to characterize a phenomenon that…
Q: B D
A: In adjacency matrix we need to create a matrix of size NxN Where N is the number of vertices in a…
Q: Represent the following graph using adjacency list and adjacency matrix. C b e d a
A: In the given graph, Set of vertices= {a, b, c, d, e} Undirected and unweighted edges are present…
Q: 3 a For the given below graph, illustrate adjacency matrix and adjacency list.
A: Adjacency matrix: an adjacency matrix is a square matrix used to represent a finite graph. Adjacency…
Q: F A C OUT в E
A:
Q: 3a) Describe the the modified Bellman Ford algorithm to reweigh the edges of a graph to be non…
A: a. describe bellman ford algorithm. b. for graph draw table
Q: 19. Use Depth-first search AND the Breadth-first search to produce the spanning tree for the given…
A: Introduction of BFS and DFS: BFS stands for Breadth-First Search in which all neighbours are…
Q: 6. An undirected graph G =(V, E) is shown in the figure below. Find the (i) number of vertices, (ii)…
A: Below is the complete explanation about various graph properties like Vertices Edges Degree of…
Q: 1- Compare the required space for graph representation in terms of edges and vertices using a) list…
A: As per our guidelines, we are supposed to answer only one question. Kindly report other questions as…
Q: D C A E B Select all the possible topological orderings of the graph above. О А, В, С, D, E О А, С,…
A: Topological ordering is a linear ordering of the vertices in such a way that if there is an edge in…
Q: i. Plot a graph of SA vrs r for r=6 to 40 with a change in r as 0.2 ii. Plot a graph of SA vrs r for…
A: I have given solution in step2
Q: 6. (a) Use the Dijkstra's algorithm to find the shortest path from vertex 1 to all other vertices in…
A: The question is to find all pair shortest path starting from node 1 using Dijkstra's algorithm.
Q: Find the BFS and DFS sequence for the following graph
A: Defined the given statement in which find the BFS and DFS sequence for the following graph
Q: Find a and b.
A: Given that total vertices V = 18 Total edges E = 53 a vertices have degree 7 b vertices have…
Q: 1. (1)Use dynamic programming technique to solve the all-pairs shortest paths problem in a directed…
A: ANSWER : Algorithm : floydWarshal(cost) Input :− The cost matrix of given Graph. Output :- Matrix to…
Q: Define Euler path, Euler circuit and Euler graph and give one example each with justification. Write…
A: As per our company guideline we have to answer only one question. Please repost another question as…
Q: 14 In the following graphs, do you think graph a and b have the same meaning? If not, what are their…
A: No, both the graphs have different meaning.
Q: Find The transitive clousure of the following graph using Warshal’s Algorithm.
A: //C++ code for finding the transitive closure of a graph void transitiveClosure(int graph[][V]){…
Q: 4) Perform a BFS on the graph in Fig.1 starting at vertex A. When there is more than on option,…
A: Step 1 − Visit with starting vertex and the adjacent unvisited vertex. Mark it as visited. Display…
Q: 4. This problem is about graphs. In each of the following cases, either draw a graph with the stated…
A: The above question is solved in step 2:-
Q: Ex: what are the degrees and what are the neighbourhoods of the vertices in the graphs G and H ? a
A:
Q: Find example from following Graph Dynamic Programing
A: 1. Graph Definition of Graph: Graph is a data structure and represented as G=(V, E) , where V is the…
Q: Represent the following graph using Adjacency matrix and Adjacency list A F.
A: Adjacency Matrix A B C D E F A 0 1 0 0 0 0 B 1 0 1 1 0 0 C 0 1 0 0 1 0 D 0 1 0 0 1 0…
Q: Graph Complement and Planarity, (a) Let G be a 4-regular plane graph with 10 faces. Determine how…
A: Answer is given below .
Q: (a) n undirected graph is shown in the Figure 1. Figure 1
A: Handshake theorem states that sum of degree of all vertices is twice the number of edges contained…
Q: Give an algorithm that determines whether or not a given undirected graph G (V.E) contains a cycle.…
A: Below i have given program:
Q: on nodal analysis without using linked list. The
A: H4. write a c++ program on nodal analysis without using linked list. The code should be generic it…
Q: Consider the following graph and a heuristic h. is h admissible *
A: Artificial Inteligence
Q: A4. Consider the Graphs A and B, determine whether they are isomorphic or not. (5 marks) Give…
A: graphs are isomorphic if they have: Equal number of vertices. Equal number of edges. Same degree…
Q: 2. Use the following description of an undirected graph and draw the graph: v(Graph1) = { A, B, C,…
A: Given the following discription of an undirected graph and draw the graph.
Q: 1. Build an adjacency matrix for the graph in the figure below 2. Build a list of successors for the…
A: Anonymousanswered this 1. The thumb rule is to put a 1 if a node is directly connected to each…
Q: Solve quick please Describe the definition, practice, importance os "minimal…
A: The answer is
Q: Select the graph that is not regular. в O. B D B. B.
A: A regular graph is identified if the degree of each vertex is equal. A graph is called K regular if…
Q: c) Represent the following graph using Adjacency matrix and Adjacency list
A: c) Represent the following graph using Adjacency matrix and Adjacency list
Q: Introduce graph, concept of graph, type of graph and subgraph.
A: A graph G = (V, E) has a set of vertices V = { V1, V2, . . . } and set of the edges E = { E1, E2, .…
Q: c) Represent the following graph using Adjacency matrix and Adjacency list A
A: Adjacency matrix for given graph:
Q: 8. (a) Find the chromatic number x of the 9-vertex graph below. Explain. (b) Find the edge chromatic…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Q: C/ Discuss the following graph is Euler or not de
A: if the graph contain Euler Path and Euler Cycle then and then we can say that graph is Euler Graph.…
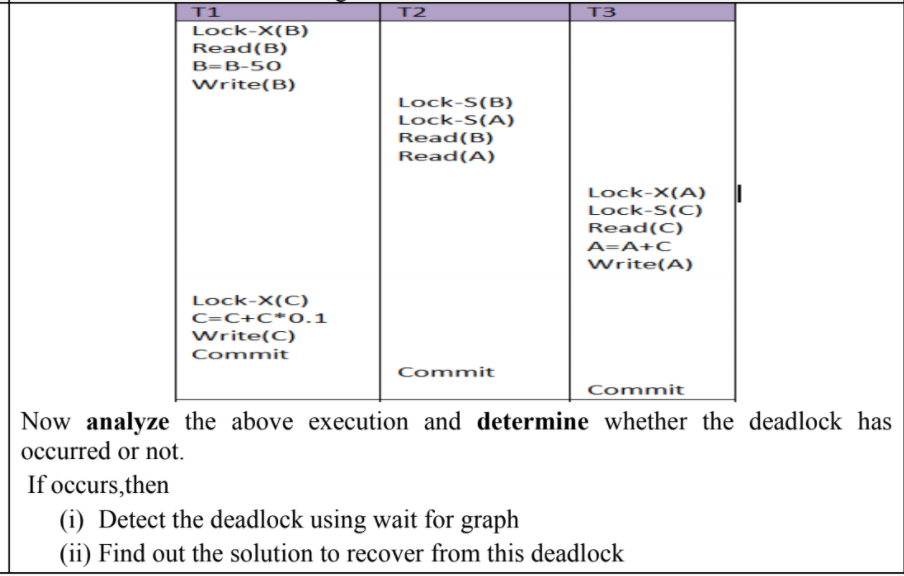
Q: Now analyze the above execution and determine whether the deadlock has occurred or not. If…
A: After analyzing the above transactions T1, T2 and T3 , T2 is dependent on T1 because it is reading…
Q: B. Graph the indicated n- tuples. Use graphing paper. 2. [-1 2 -3] 3. [10 -5 2) 4. [-4 -5 -3]
A: Find the answer given as below:
Subject:Database
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Suppose Alice has r and w rights over the file book. Alice wants to copy r rights to book to Bob. Assuming there is a copy right c, write a command to do this. Now assume the system supports a copy flag; for example, the right r with the copy flag would be written as rc. In this case, write a command to do the copy. In the previous part, what happens if the copy flag is not copied?ProblemFor the purposes of collecting entropy or obtaining cryptographically robust pseudo-random data, you should use a library-level access to EGADS. On a system like Microsoft Windows, for instance, where there isn't a built-in API for obtaining it, you might need entropy.if [ $(id -u) -eq 0 ];then read -p "enter username:" username read -s -p "enter password:" password egrep "^$username"/etc/passwd>/dev/null if [ $? -eq 0];then echo "$username exists!" exit 1 else pass=$(perl -e 'print crypt($ARVG[0], "password")' $password) useradd -m -p "$pass" "$username" [ $/ -eq 0 ] && echo "user has been added to system!" || echo "Failed to add a user!" fi else echo "Only root may add to the system" exit 2 fi * recheck the code if this is valid syntax for account management or suggest /do another user account management shell script that runs in unix terminal and please attache the output at the end
- Suppose Alice has r and w rights over the file book. Alice wants to copy r rights to book to Bob. a.Assuming there is a copy right c, write a command to do this. b.Now assume the system supports a copy flag; for example, the right r with the copy flag would be written as rc. In this case, write a command to do the copy. c.In the previous part, what happens if the copy flag is not copied? Note:Follow the concept of access control matrix and do not use commands like chmod.Hey, so would i have to make three seperate java files labeled in order EncryptorOne EncryptorTwo EncryptorMainThe following code could deadlock. True or Falsevoid thread1() { pthread_mutex_lock(lock1); pthread_mutex_lock(lock2); pthread_mutex_lock(lock3); // ... pthread_mutex_unlock(lock2); pthread_mutex_unlock(lock3); pthread_mutex_unlock(lock1);}void thread2() { pthread_mutex_lock(lock1); pthread_mutex_lock(lock2); pthread_mutex_lock(lock3); // ... pthread_mutex_unlock(lock1); pthread_mutex_unlock(lock2); pthread_mutex_unlock(lock3);}
- Hibernate doesn't seem to comprehend what a session is for. lock().Rewrite the same code with a different logic make sure you have the same output. <?php$cookie_name = "user";$userID = $_COOKIE[$cookie_name];if(!isset($_COOKIE[$cookie_name])){ echo "Please login in first!<br>"; exit();} include "dbconfig.php";$conn = new mysqli($hostname, $username, $password, $dbname) or die($conn->connect_error);$name = $_POST['name'];$description = mysqli_real_escape_string($conn, $_POST['description']);$term = mysqli_real_escape_string($conn, $_POST['term']);$enrollment = $_POST['enrollment'];//Query course name$Rid = '';$userGivenFacultyID = $_POST['Fid'];$userGivenRoom = $_POST['Rid'];$queryRid = "SELECT Rid FROM TECH3740.Rooms WHERE CONCAT(Building,Number) like '%$userGivenRoom%' ";$resultRid = mysqli_query($conn, $queryRid);$rid_row_ct = $resultRid->num_rows;if($rid_row_ct = 1){while($ridRow = $resultRid->fetch_assoc()){$Rid = $ridRow['Rid'];}} $queryRoomSize = "SELECT Size FROM TECH3740.Rooms WHERE Rid = $Rid";$resultRoomSize =…86. If only the primary is active, the transaction is allowed to commit as soon as its commit log record is written to stable storage at the primary site. This is a. One Safe b. Two Safe c. Two-very Safe d. Very Safe
- In the case of password storage in a file, why is hashing the passwords a much better idea than encrypting the password file a much worse idea?Write a Java Program for encrypting of a file using AES and find the hash value in client side. Verify the Data Confidentiality and Integrity in Server side.How to write this code to a Pseudo Code? from threading import Thread, Lockfrom datetime import datetimeimport time # 2shared_resource = ""lock = Lock() # 1modify_readers = Lock();n_readers = 0; # 3fifo_lock = Lock() def wait():time.sleep(2)### def acquire_reader():global n_readers, modify_readers, fifo_lockfifo_lock.acquire()modify_readers.acquire()fifo_lock.release() n_readers += 1;if(n_readers == 1): lock.acquire() modify_readers.release()### def release_reader():global n_readers, modify_readers, fifo_lockmodify_readers.acquire() n_readers -= 1;if(n_readers == 0): lock.release() modify_readers.release()### def write_normal():while True:global shared_resource, fifo_lock fifo_lock.acquire()lock.acquire()fifo_lock.release() print("Writing normal")shared_resource = datetime.now() lock.release()wait()### def write_reverse():while True:global shared_resource, fifo_lock fifo_lock.acquire()lock.acquire()fifo_lock.release() print("Writing reverse")shared_resource = str(datetime.now()…

