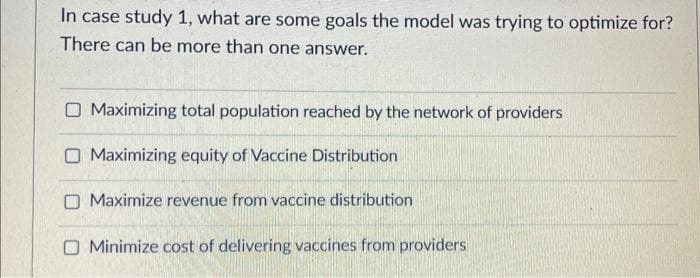
In case study 1, what are some goals the model was trying to optimize for? There can be more than one answer. O Maximizing total population reached by the network of providers O Maximizing equity of Vaccine Distribution O Maximize revenue from vaccine distribution Minimize cost of delivering vaccines from providers
Q: Understanding what computer science is and how it differs from other disciplines is crucial. Where…
A: The solution is given in the below step
Q: Can you explain the shmat system call to me? I need to know what a process is, what a shared memory…
A: The short () method binds the shared memory segment identified by the shared memory identification…
Q: Ubuntu is superior than other popular Linux distributions. In what ways do you believe your concept…
A: The main differences between Linux and Ubuntu are listed below: Linux kernel-based Ubuntu. Linux…
Q: How simple or complicated is it to add or delete users in Windows 10 and Linux?
A: In accordance with the inquiry, we must determine the difficulties associated with adding and…
Q: It's possible for anything to occur throughout the course of a software development project. How…
A: There are two primary software engineering approaches: the Waterfall model and the Agile technique.…
Q: To be successful in the role of system requirements engineer, one must show that they can…
A: Soln:— A functional requirement describes a system or one of its components. A nonfunctional…
Q: What are the most promising future options for a legacy system? When upgrading the hardware would be…
A: When considering future options for a legacy system, it's important to evaluate factors such as the…
Q: We take a look at these cutting-edge features of cloud computing and their implications for…
A: Cloud computing: Cloud computing, in its simplest form, is the delivery of computing services…
Q: What is the three-character identifier for button labels?
A: The three character ID used to name the buttons in Visual Basic is btn. It allows the user to modify…
Q: Which advantages does a compiled language have over an interpreted one? Tell me about any scenarios…
A: What benefits do compiled languages have over interpreted languages? Compilers convert compiled…
Q: Is there a difference between architecture and organization when it comes to computers?
A: The study of a computer system's internal operations, structure, and implementation is known as…
Q: Define the relationship between the words "reliability" and "availability" as it relates to a…
A: Computer Network:- Computer network refers to inter connection between two computer devices that…
Q: Python Programming You are given an array a of length N and Q queries. Each query is described by a…
A: Introduction Python Function: The function in Python is a set of related statements that perform out…
Q: #include #include using namespace std; void PrintVectors(vector numsList) { unsigned int i;…
A: In this question, it is asked to edit the code statements to pass all the test cases. One of the…
Q: Can you explain the shmat system call to me? I need to know what a process is, what a shared memory…
A: Introduction Shared memory is a method of inter-process communication that allows different…
Q: Is UDP just as shaky as IP, or is this not the case at all? I'm curious as to why you think this is…
A: Answer is
Q: When will it be possible to produce a user-defined identifier, and what conditions must be met?
A: In computer programming, an identifier is a name given to a variable, constant, function or any…
Q: Question 5 What is a "Secondary Dimension" in Google Analytics? A An additional report metric for…
A: In this question we have to answer for the following questions 1. What is a Secondary Dimension in…
Q: Is it complete that we have introduced and concluded the IOT temperature monitoring system?
A: Introduction: Io T is used to link electrical devices to the internet. The devices might include…
Q: Why is UDP useful? Perhaps it would have been preferable if IP packets could have been sent directly…
A: Introduction : UDP (User Datagram Protocol) is a communications protocol that is used primarily for…
Q: What are the three things you need to do when working with classes that include pointer variables as…
A: Introduction of object-oriented programming: Object-oriented programming is a programming…
Q: Specifically, it would be helpful to see an illustration of transition probabilities for a…
A: This review presents a non-homogeneous persistent time Markov regenerative interaction with forward…
Q: An organization's analysts should always present a concise executive summary of their results that…
A: Introduction: I'm drafting the answer to the above inquiry. Below is the written response. Strengths…
Q: What distinguishes a user-defined identifier from a reserved term, and how do you use one?
A: A user-defined identifier is a name created by the programmer for variables, functions, classes,…
Q: To clarify, what do you mean by the term "static semantics?" Please provide some examples of static…
A: Static Semantic Rules: These rules are more often linked with the syntax of programming languages…
Q: The algorithm for file deletion is the same across Symbian, Android, and iPhone.
A: The algorithm for file deletion can differ across different operating systems, including Symbian,…
Q: When someone says "Identifier attribute," what do they mean?
A: Answer is
Q: When and why does a newer version of the system get installed?
A: Introduction: Updating to a newer version of a system is a common practice in the world of…
Q: Many of cloud computing's disadvantages go unrecognized or are misunderstood.
A: Cloud computing may include a wide range of computer services, including servers, storage,…
Q: Describe, in your own words, the key distinctions between Linux and competing systems. This means…
A: INTRODUCTION: Linux is an operating system that was created in 1991 by Linus Torvalds. Linux derives…
Q: I have this code: def normalize_dictionary(self, d): """""" values =…
A: The given code is implementing a comparison between two dictionaries based on their normalized…
Q: How can data visualizations employ these five graphical data elements to highlight and contrast data…
A: Visualizing data It visually represents structured or unstructured data in order to convey…
Q: Using an Enigma Machine Simulator, solve the following code: Code:…
A: Introduction Enigma Machine Simulator: An Enigma machine simulator is a computer program that…
Q: The inner workings of an OS are beyond our ken.
A: A software programme known as an operating system serves as an administrator for other application…
Q: Is there a specific purpose for wireless networks in third world countries? This shift away from…
A: - We need to talk about wireless networks in third world countries.
Q: Describe the various semantic categories, including their applications, advantages, and…
A: Introduction There are actually two different definitions of semantics that apply to different…
Q: but there is no option of 23 msec there is only 7 , 16 and 2 msec
A: Given The total seek time = 13 milliseconds (msec) The total transfer time = 36 msec. Data size = 2…
Q: Where do other fields of study have similarities to computer science? Where do they stand in terms…
A: Start: The study of computers and algorithmic processes, including their underlying concepts,…
Q: It's possible that you may benefit from using cloud computing and social networking blogs in order…
A: Employing the Cloud The method of offering a service to a customer online is called cloud computing.…
Q: More companies are utilizing cloud computing to make their operations run more smoothly.
A: Introduction : The term "cloud computing" is used to describe a wide range of activities that…
Q: What measures must be taken to ensure the security of network "building blocks" such switches,…
A: Introduction:- A computer network is a system that connects two or more computers together for the…
Q: Are the following two IP addresses in the same subnet? Answer either 'yes' or 'no'.…
A: Given: Two IP addresses: 2001:69a0:75:60c9:6a10::1/64 2001:69A0:7500:60C9:632e:d456:3c95:72c2/64…
Q: The techniques used to enhance software quality are listed and explained.
A: Software product A software product is made to meet explicit client prerequisites, yet it regularly…
Q: 43. Which of these collections of subsets are partitions of the set of bit strings of length 8? a)…
A: In this question we have to answer which of these collections of subsets are partitions of the set…
Q: Please name and describe any eight of the sensors that are utilized in the Internet of Things (with…
A: 1) IoT sensors are pieces of hardware that detect changes in an environment and collect data. It may…
Q: : You will build a simplified, one-player version of the classic board game Battleship! In this…
A: Algorithm: The code implements the game as described in the prompt. It starts by initializing an…
Q: The word "Identifier attribute" seems to be thrown about a lot without a clear definition
A: Answer is
Q: In a script, the user is supposed to enter either a 'y' or 'n' in response to a prompt. The user's…
A: This provided code takes a letter input from the user and checks if it's 'y' or 'Y' and if it is, it…
Q: For FY20Q3, which Channel performed the worst?
A:
Q: Question 29 Which of the following metrics shows the number of times your ads were displayed? A…
A: According to Bartleby Guidelines we need to answer only one question so I have answered first…
Question Rk
Full explain this question very fast solution sent me step by step
Step by step
Solved in 2 steps

- Answer the following questions1. We have 3 data points for a model (1, 1), (2, 2), (3,3) and theta0, theta1 is consequently .5 and 1. What is the value of cost functions for the data (1.5, 1.8) and (2.3, 2.1)?2. What is confusion matrics? Why we use it?" data points denote (X, Y) values in question.Consider amodel of a drone to deliver the orders of the customerswithin the range of 20 km of the coverage area. a) Identified atleast 5 factors (inputs)required to experiment withthe above mention system model(e.g speed of the drone). b) Write down thelevels (range or setting)for each factor mentioned above.(e.g speed ranges from 10km/h to 30km/h). c) On what responses(results)will you analysethe experiment’s success orfailure(e.g drone failed to deliver the package on time), mention atleast 3 responses.Q.1: a. What is TFIDF? What is significance of IDF? Explain role of IDF in classification with one real life example. Give an example where IDF may not make sense while classifying. b. Explain how can you apply TFIDF to classify product reviews? (Here each post has 20 words). Give Pseudo code for the same. c. Discuss an algorithm to rank these reviews for different new customers based on their personalized parameters. (Make necessary assumptions) d. Can you combine CNN and TFIDF in this case? How? e. Discuss an algorithm where you combine different reviews to provide a single personalized review of the product for a particular customer.
- The scenarios below suggest what forecast method is suitable 3.1 A house evaluator estimates the house market value by comparing it to similar properties sold in thearea. The degree of similarity depends on the attributes considered. With house appraisals, featuressuch as land size, dwelling size, number of bedrooms and bathrooms, and garage space are usuallyconsidered. 3.2 The ministry of health construct consensus forecasts from a group of experts in a structured, iterativemanner for the COVID 19 vaccines. A preliminary round of information gathering from the expertsbefore setting the forecasting tasks was conducted. A facilitator was appointed to implement andmanage the process. 3.3 A company uses top managersto generate aggregate forecasts. Such forecasts are usually developedin a group meeting, where managers contribute information from their respective departments.Having top managers from different functional areas of the company promotes excellent skill andknowledge diversity…A coach is trying to choose the starting line-up for the basketball team. The team consists ofseven players who have been rated (on a scale of 1= poor to 3 = excellent) according to theirball-handling, shooting, rebounding, and defensive abilities. The positions that each playeris allowed to play (G = guard, C = center, F = forward) and the player’s abilities are:Player Position Defense Ability1 G 32 C 23 G-F 24 F-C 15 G-F 16 F-C 37 G-F 3Formulate an IP to choose the starting lineup such that the five-player starting line-up satisfiesthe following restrictions, then solve your IP using python (if you have not taken and are notcurrently taking python you may use the excel solver - be sure to document this in yourhomework submission). Submit your python file on canvas and include the optimal solutionin your written submission.(a)…Some manufacturing companies are hesitant to implement loT in their respective operations, give (3) specific situations based on economic, social, and ROl of the company.
- what machine learning model to estimate the duration of delivery time? there will be various features ex location, number of deliverer and etcQuestion 7In farming, given data on crop yields over the last50 years, learn to predict next year's crop yields. Is this regression or classification?Artificial Intelligence (For this scenario describe how you would develop an inteligent system to solve this problem) One of the challenging tasks of AI is to find the optimal path from one place to the destination place. I'ts is to find the optimal path for a vehicle to travel so that cost and time can be minimized. How can we solve this business problem using AI
- 19. What is the major advantage of using Incremental Model? a. Customer can respond to each increment b. Easier to test and debug c. It is used when there is a need to get a product to the market early d. Both b & cCurrently Techsoft has an exceptionally high customer service level of98%much high than any of its competiors. Customers showed positive response towards a possible lower but acceptable service level. Results of the surveyshowed 45 of the customers would be serviced at 908 (classified hereon as Category i) and the rest would have to serviced at95%(CategoryALast year, the retailer's weekly variance of demand was 100 units. The variance of orders was 250, 300, 400 and 600 units for the retailer, wholesalers, distributing and manufacturer. respectively (note that the variance of orders equals the variance of demand for that firm's supplier) A. calculate the bullwhip measures for the retailer, wholesales, distributor and manufacturer? B. what is the bullwhip effect for the entire supply chain? C. provide actionable guidelines (with anticipated bullwhip measures of each point on how to reduce bullwhip measures to 2 in the supply chain? All your calculations has to be done on paper and has to be done on excel sheets. Each question you must show the formula used to calculate the answer in excel sheet in order to use excel in exam. The excel sheet must be used as well and provide all the formulas used for each answer in order to use excel in the exam.



