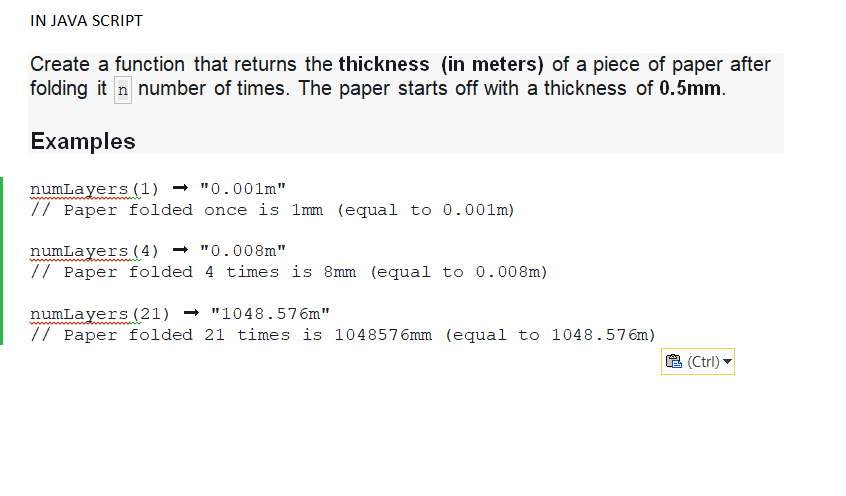
IN JAVA SCRIPT Create a function that returns the thickness (in meters) of a piece of paper after folding it n number of times. The paper starts off with a thickness of 0.5mm. Examples numLayers (1) "0.001m" // Paper folded once is 1mm (equal to 0.001m) numLayers (4) "0.008m" // Paper folded 4 times is 8mm (equal to 0.008m) numLayers (21) "1048.576m" // Paper folded 21 times is 1048576mm (equal to 1048.576m) (Ctrl)
Q: Skype offers a service that allows you to make a phone call from a PC to an ordinary phone. This…
A: Internet and telephone network interface: Customers of telecommunications companies can access the…
Q: Consider the relations Courses1, Courses2, _Enrollment and Students. Courses cid ename Al Calculus…
A: Write the following query in Relational Algebra. a) Find the sids of students who have enrolled in…
Q: Project 6: You have to create a program in C language in which the user enters the mass m and radius…
A: Algorithm: 1. Read mass, m. 2. Read radius, r. 3. moment_of_inertia = (m * r * r) / 2. 4. Print…
Q: Main memory is byte addressable? 2^20 bytes Main memory is word addressable( a word size is 32 bits)…
A: The answer is
Q: Assume class MyStack implements the following StackGen interface. For this question, make no…
A: public void interchange() { //declare a temp stack MyStack<T> temp = new MyStack<T>();…
Q: Developer / Salesforce How many triggers can be made on the same object? Show some best practices as…
A: You can have many triggers on a single object. Having multiple triggers for a single object is bad…
Q: . Consider a packet of length L that begins at end system A and travels over three links to a…
A:
Q: Skype offers a service that allows you to make a phone call from a PC to an ordinary phone. This…
A: The answer of the question is given below:
Q: Write a C++ program that contain a menu rto call user defined functions on a one dimendional array:…
A: Introduction: In this question, we are asked to write a C++ program to show the menu and do as per…
Q: b. How many bits are required to address a 16M x 8 memory
A: The answer is
Q: Create a simple text-based console game that implements at least three (3) interfaces. Below is a…
A: The java code is given in the below step with an output screen shot
Q: Project 6: You have to create a program in C language in which the user enters the mass m and radius…
A: The question has been answered in step2
Q: Solve problem by using PYTHON Program to remove the ith occurrence of the given word in ist where…
A: It is defined as a simple, general purpose, high level, and object-oriented programming language. It…
Q: Draw an entity-relationship diagram that describes the following business environment. Orlando…
A: The Entity-Relationship diagram is a data modelling diagramming technique. A relationship is the way…
Q: write c++ code for Design a class named Computer that holds the make, model, and amount of memory…
A: The class diagram and the runner code of the given program is provided in the next step.
Q: Apply your knowledge about arrays and functions and write a program, which takes a positive integer…
A: Algorithm: Read the value of n Run loop for i to n+1 and print the upper row element Run for loop…
Q: how to define turing machine in best possible and simple way?
A: A machine that accepts a recursive enumerable grammar, that is, type-0 grammar, is called as a…
Q: What are the basic interfaces of Java Collections Framework?
A: The answer of the question is given below
Q: Implement the following Racket functions: Symmetric-Closure Input: a list of pairs, L.…
A: The code is below, it uses Symm-helper function and opp function.
Q: O Cross entropy loss function for a logistic regression based model is given as: Cost = (Vactual) In…
A:
Q: Is a word for a system development approach that aims to reduce the time it takes to build and…
A: Information system is an organizational system which is used to distribute, process, store…
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position…
A: Introduction: IoT is a network of networked, internet-connected devices that can gather and transmit…
Q: Consider a processor with a 3.4 GHz clock rate and a CPI of 2.2. If the processor execute a program…
A: Introduction
Q: Obtain the cipher text for the plain text "mosque" using playfair cipher. All steps should be…
A: We need to encrypt the given string using playfair cipher.
Q: Current Situation of Computing Department Knowledge Management System (KMS)
A: An knowledge management system (KMS) is a stage that assists you with getting the right information…
Q: illustrate the execution of the in-place heap sort algorithm in the following input sequence: (2, 5,…
A: Solution:
Q: 4. Using the 16 bit (half precision) representation of floating-point numbers, with 5 bits for the…
A:
Q: Q2: Write a row-level trigger that executes before updating a project's location in the project…
A: The question is to write the SQL query for the given problem.
Q: simple conclusion in automated street light calculator using proteus ang assyembly language
A: simple conclusion is given below :
Q: (1) Write a python code to evaluate the following computations (i) exactly, (ii) using 3-decimals…
A: Import the required library. Compute the exact number. Compute the number chopped by 3-decimal…
Q: DHCP Discover -Fa0/0- .2 192.168.12.0/24 -Fa1/0- .2 192.168.23.0/24 .3
A: Introduction: An automatic distribution and assignment of IP addresses, default gateways, and other…
Q: Type the program's output my_list = [-3, -2, -1, 0, 1, 2, 3] new_list = = [ number for number in my…
A: Lists can also contain lists, they are called nested lists.
Q: Obtain the cipher text for the plain text "mosque" using playfair cipher. All steps should be…
A: Here we have given cipher text for the plain text "mosque" using playfair cipher. you find the…
Q: How can you aid in preventing internal and external threats?
A: External assaults are generally pernicious, with disturbing help, vandalism, and burglary as the…
Q: What is kernel in operating system.
A: The above question is solved in step 2 :-
Q: Consider an application that transmits data at a steady rate (for example, the sender generates an…
A: answer is
Q: IN JAVA SCRIPT Given an input string, reverse the string word by word, the first word will be the…
A: Algorithm - Create a method calculateScores with one string as argument. Now use the below logic…
Q: B={1,2,3,4,5,6,7,8,9,10} Using the n-bit binaries to which subset in the power set of the ordered…
A: The bit string 1100000011 represents the subset {1,2,9,10} in the power set of the ordered set B.…
Q: Let n be a positive integer and suppose we identify a collection of n people with numbers ranging…
A: The above question is solved in step 2 :-
Q: PYTHON!! Solve problem by using PYTHON Program to remove the ith occurrence of the given word in…
A: Python program steps to remove the ith occurrence of the given word list: To make it possible for…
Q: Write a python program to find unique elements in a list Input = [ 1,2,2,4,1,5] Output = [4, 5]
A: The above question is solved in step 2 :-
Q: Write a program that outputs the nodes of a graph in a depth-first traversal.
A: According to BartleBy Guidelines we need to answer only one question So I have answered first…
Q: 1. Create a Ladder logic using below instruction - Function: A start, and a stop button is used for…
A: Here's the solution:
Q: What is an abstract class?
A: Sometimes the developer or coder don't have all the needed requirement for the writing complete…
Q: Q1. 4X₁ + 3X₂ + 5X3 = 4 3X₁ + 2X₂ - 4X3 = 7 -2X₁₂ + 4X₂ + 3X3 = 5
A: “Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: Besides network-related considerations such as delay, loss, and bandwidth performance, there are…
A:
Q: write some info regarding to IT infrastructure and systems in place for Computing Department…
A: Answer : IT infrastructure should be design computing friendly environment so that it can be easily…
Q: 1 Question 1 A Deep Neural Network is shown in Figure 1. The aim of this network is to classify…
A: Since you have asked a question with multiple sub-parts, we will solve the first three sub-parts for…
Q: What is the difference between a host and an end system? List several different types of end…
A: The words "host" and "end device" are also used interchangeably. Between a host and an end device,…
Q: How does the NAT router differentiate two simultaneous connections which are initiated from PC1 to…
A: INTRODUCTION In this question we are asked how does the NAT router differentiate two simultaneous…
Step by step
Solved in 2 steps with 1 images

- In JAVA A function foo takes three integers as input arguments, i.e., foo(int a, int b, int c). The three inputs represent the three sides of a triangle in centimeter. The function is expected to return the type of a triangle: “equilateral”, “isosceles”, or “scalene”. Assume the domains of the three variables are 1 ≤ a ≤ 100, 50 ≤ b ≤ 150 and 100 ≤ c ≤ 200, respectively. A test case is in a tuple format <a, b, c, expected_output> with test inputs and the expected output. S1 is a set of test cases for the “Boundary Value Analysis” approach. S1 = S2 is a set of test cases for the “Robustness testing” approach. S2 – S1 = S3 is a set of tests cases for the “Robust Worst-Case testing” approach. Are there any types of triangles that S3 cannot reveal? If yes, what are they? If no, why?In java: Develop a void function that takes two parameters, an integer and a string. The function should print the string as many times as given by the integer. For example, with arguments 4 and “Hello” the function would print “Hello” four times. Call the function twice with different arguments. What happens when the argument is negative?This is a JAVA programming assignment. Program a GeneticAlgorithm to find an integer number between 0 and 31 that maximizes the function f (x) = x2.The initial procedure is given as below.• Population size: 6• Crossover probability: 100%• Mutation probability: 5%• Terminating criteria:o When your program produces an average of candidates is equal to or greater than29, then you can accept it as a terminating condition.• Fitness function:o You can use the function itself (f (x) = x2)as your fitness function.1. For the 1st generation, you need to print the process and result of selection, crossover, andmutation operation.you need to print the corresponding integer values and bits (binary values)of selection, crossover, and mutation operation. You also need to decide andprint the crossover point and the mutation point.2. From the 2nd generation, you do not have to print all results of selection, crossover,mutation operations. You can just print the result of each generation. Please provide…
- Write a Java program correctly that generates a report of proof of vaccination against COVID-19 for the peoplewho received their dose of vaccination. Write a program which:1. Display a welcome message.2. Then prompts the user to enter the following:• First name, with first letter uppercase, which is then stores in a variable of type String.• Last name, with first letter uppercase which is then stores in a variable of type String.• Day of birth, set as a number between 1 and 31, which is then stores in a variable of typeint.• Month of birth, set as a number between 1 and 12, which is then stores in a variable of typeint.• Year of birth, set as a number between 1920 and 2006, which is then stores in a variable oftype int.• Day of vaccination, set as a number between 1 and 31, which is then stores in a variable oftype int.• Month of vaccination. set as a number between 1 and 12, which is then stores in a variableof type int.• Year of vaccination, set as a number between 2020 and 2021,…In Java for zybooks ,Lab 3.27, Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first six letters of the first name, followed by the first letter of the last name, an underscore (_), and then the last digit of the number (use the % operator). If the first name has less than six letters, then use all letters of the first name.Write a JavaScript function that accepts a number from a user as input and checks if the number is prime, then print True if the number is not a prime, print False. Note: A prime number (or a prime) is a natural number greater than 1 that has no positive divisors other than 1 and itself.
- In JAVA ASSIGNMENT DESCRIPTION: A half-life is the amount of time it takes for a substance or entity to fall to half its original value. Caffeine has a half-life of about 6 hours in humans. Given caffeine amount (in mg) as input, output the caffeine level after 6, 12, and 24 hours. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:System.out.printf("After 6 hours: %.2f mg\n", yourValue); Ex: If the input is: 100 the output is: After 6 hours: 50.00 mg After 12 hours: 25.00 mg After 24 hours: 6.25 mg Note: A cup of coffee has about 100 mg. A soda has about 40 mg. An "energy" drink (a misnomer) has between 100 mg and 200 mg. THE CODE I HAVE SO FAR: import java.util.Scanner; public class LabProgram { public static void main(String[] args) { Scanner scnr = new Scanner(System.in); double caffeineMg; // "double" supports floating-point like 75.5, versus int for integers like 75. caffeineMg = scnr.nextDouble(); System.out.printf("After…in Java, Write a program that reads student scores, gets the best score, and then assigns grades based on the following scheme:• Grade is A if score is ≥ best − 10• Grade is B if score is ≥ best − 20;• Grade is C if score is ≥ best − 30;• Grade is D if score is ≥ best − 40;• Grade is F otherwise.The program prompts the user to enter the total number of students, then prompts the user to enter all of the scores, and concludes by displaying the grades. Here is a sample run: number of students: 4 scores are: 40.0, 55.0, 70.0, 58.0 Student 0 score is 40.0 and grade is C Student 1 score is 55.0 and grade is B Student 2 score is 70.0 and grade is A Student 3 score is 58.0 and grade is BWrite a console application in c++ that prints the next 20 leap years. A leap year is a year in which an extra day is added to the Gregorian calendar, which is used by most of the world. While an ordinary year has 365 days, a leap year has 366 days. ... A leap year comes once every four years. Because of this, a leap year can always be evenly divided by four.
- Use java Language Write the function parrotTrouble.** We have a loud talking parrot. The "hour" parameter* is the current hour time in the range 0..23. We are* in trouble if the parrot is talking and the hour* is before 7 or after 20. Return true if we are* in trouble.** Some Examples:* parrotTrouble(true, 6) returns true* parrotTrouble(true, 7) returns false* parrotTrouble(false, 6) returns false** @param isTalking true if the parrot is talking.* @param hour the time of day from 0..23.* @return true if you're in trouble with your neighbors.IN JAVA. Write a program that takes in an integer in the range 20-98 as input. The output is a countdown starting from the integer, and stopping when both output digits are identical. Ex: If the input is: 93 the output is: 93 92 91 90 89 88 Ex: If the input is: 77 the output is: 77 Ex: If the input is: 15 or any number not between 20 and 98 (inclusive), the output is: Input must be 20-98Solve in Python: Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first five letters of the last name, followed by the first letter of the first name, and then the last two digits of the number (use the % operator). If the last name has less than five letters, then use all letters of the last name. Ex: If the input is: Michael Jordan 1991 the output is: Your login name: JordaM91 Ex: If the input is: Kanye West 2024 the output is: Your login name: WestK24

